fisher
真正的验证逻辑在 main 函数的 catch 块里,不过走到需要满足输入的 sha1 的值等于 2e95a5c5f9643df668d3965a6cdf19541bc0496b, 后面发现没影响直接调进去就行。分析一下,加密流程如下:
table = 'ghijklpqrstuvwxyzABCabcDEFdef0123GHI4567JKL+/MNOmnoPQRSXYZ8TUVW9'
flag = input()
flag_a = ''
for c in flag:
if c in table:
flag_a += c
assert len(flag_a) > 0
flag_b = ''
i = j = 0
while True:
flag_b += flag_a[i]
i += 1
if i == len(flag_a):
flag_b += 'X'
break
if flag_a[i] == flag_b[j]:
flag_b += 'X'
else:
flag_b += flag_a[i]
i += 1
j += 2
if i >= len(flag_a):
break
i = 0
flag_c = ''
while i < len(flag_b):
group1 = 0
sub1 = 0
group2 = 0
sub2 = 0
for k in range(8):
for l in range(8):
if flag_b[i] == table[k * 8 + l]:
group1 = k
sub1 = l
break
if group1 != 0 and sub1 != 0:
break
i = i + 1
for k in range(8):
for l in range(8):
if flag_b[i] == table[k * 8 + l]:
group2 = k
sub2 = l
break
if group2 != 0 and sub2 != 0:
break
if group1 == group2:
flag_c += table[group1 * 8 + ((sub1 + 1) % 8)]
flag_c += table[group1 * 8 + ((sub2 + 1) % 8)]
else:
if sub1 == sub2:
flag_c += table[((group1 + 1) % 8) * 8 + sub1]
flag_c += table[((group2 + 1) % 8) * 8 + sub1]
else:
flag_c += table[group1 * 8 + sub2]
flag_c += table[group2 * 8 + sub1]
i += 1
print(flag_c)
求解脚本:
real_flag_c = 'N17EHf1DWHD40DWH/f79E05EfIH1E179E1'
real_flag_b = ''
i = 0
for i in range(0, len(real_flag_c), 2):
c1, c2 = real_flag_c[i], real_flag_c[i + 1]
i1 = table.index(c1)
i2 = table.index(c2)
s1, g1 = i1 % 8, i1 // 8
s2, g2 = i2 % 8, i2 // 8
if g1 != g2 and s1 != s2:
s1, s2 = s2, s1 # 最后一种情况
elif g1 != g2 and s1 == s2:
g1, g2 = (g1 + 7) % 8, (g2 + 7) % 8
else:
s1, s2 = (s1 + 7) % 8, (s2 + 7) % 8
real_flag_b += table[g1 * 8 + s1]
real_flag_b += table[g2 * 8 + s2]
print(real_flag_b.replace('X', ''))
faalua
本来以为是 lua,看了好久最后搜索导出函数发现是 AngelScript,没找到asc的反编译程序,直接硬调了。程序主体刚好是官方示例给的 game 修改了一下,编译一个官方版本 bindiff 恢复一下符号表。
比原来的程序多注册了一些函数:
void send(const string &in)用来打印字符串string gift()用来接收输入,还做了个置换array<T>类型的一系列函数
调试发现,EndGame为 true 的情况下,会触发flag输入,然后加载了一个game.flua,dump 出来发现主要逻辑就在game.flua中,在下图这些函数的位置先下上断点,可能会用到。
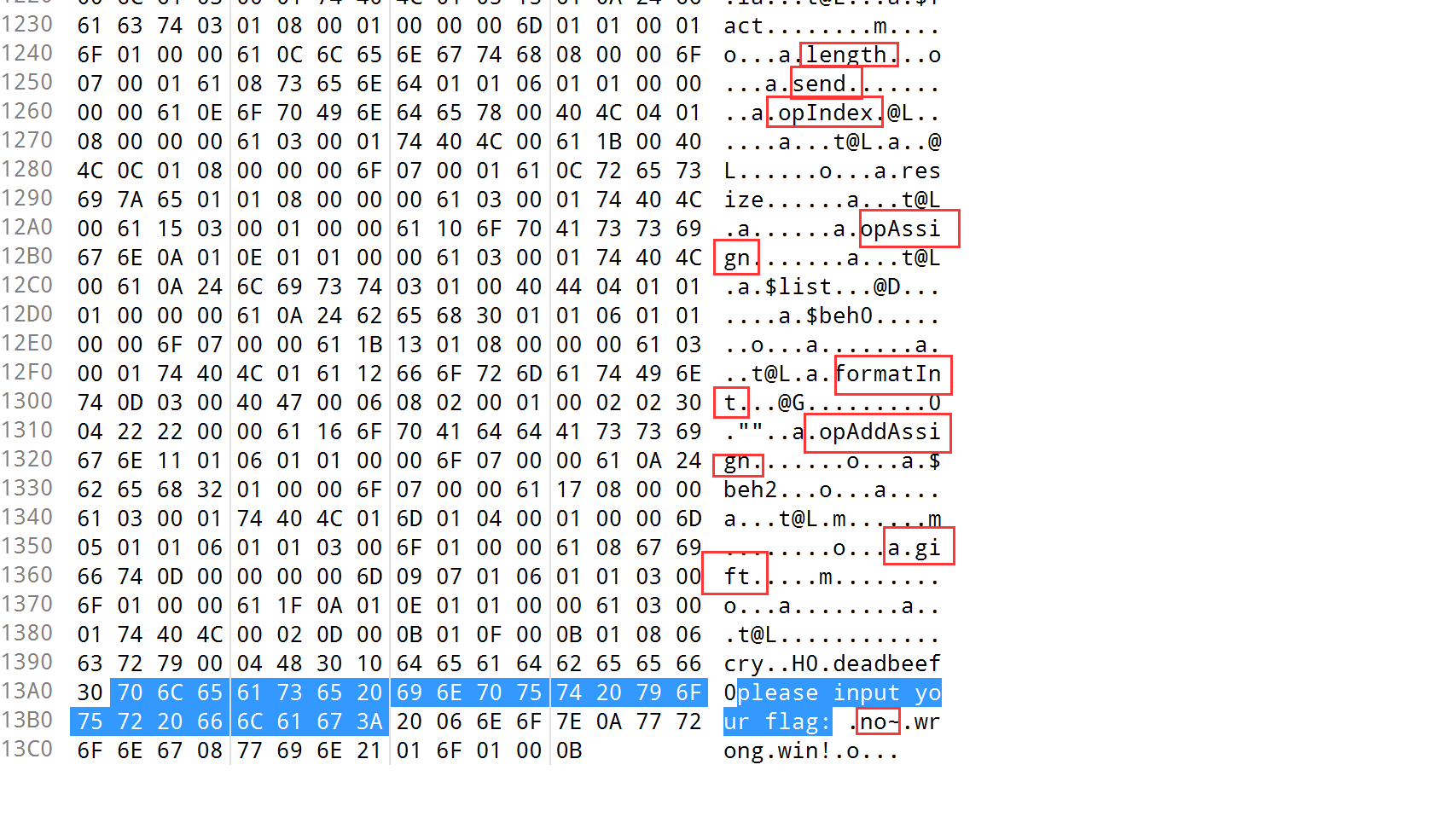
对gift返回的字符串下内存断点,断到 memmove 里了,然后继续断 memmove 后的新内存地址上的字符串。
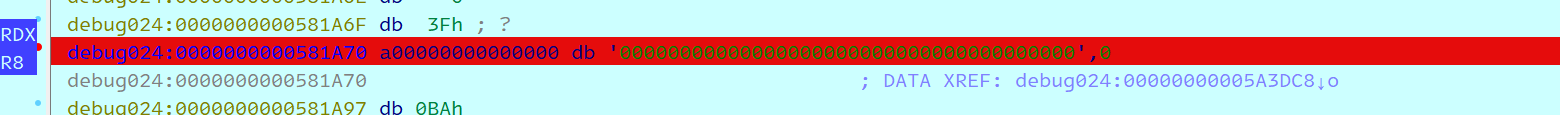
断到了 VM 的asBC_RDR1分支
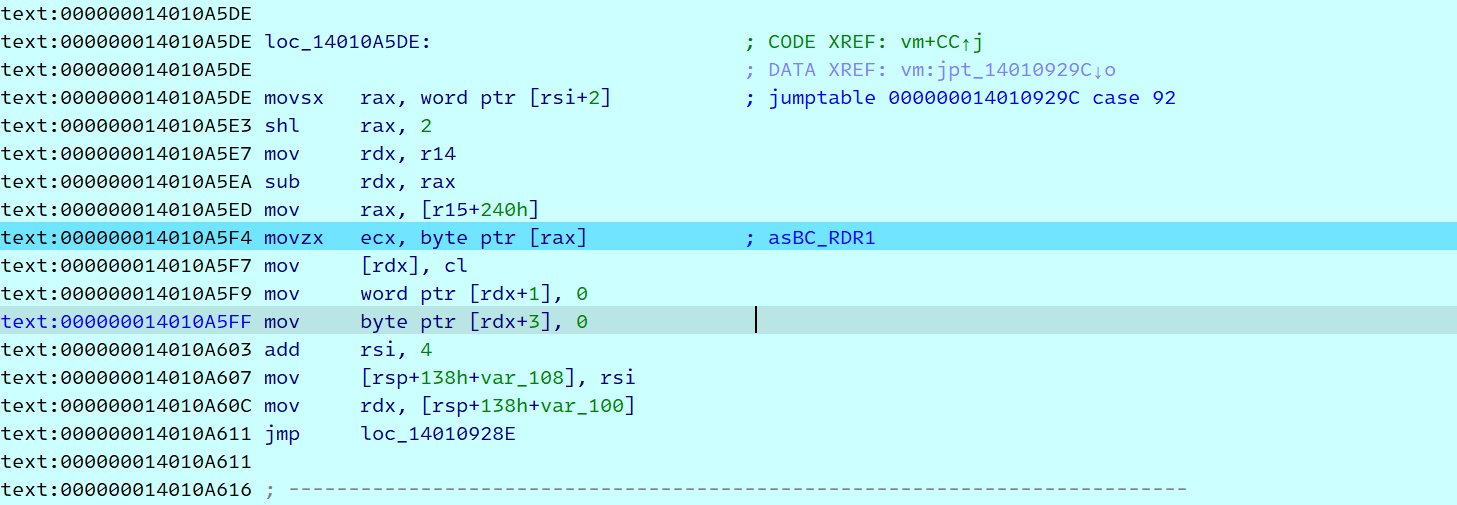
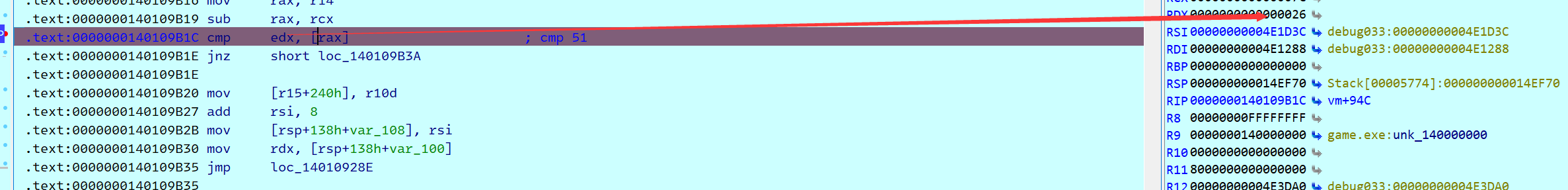
然后跟着调了一会发现就是对输入进行xor,还有 对一个数 mod 256这种操作,感觉就是 rc4,但是懒得分析密钥了,直接写个脚本把密钥流 dump 下来得了(脚本见后面),脚本跑的过程中发现 xor 的次数是输入长度的二倍,而且第二次 xor 的两个操作数都是输入决定的,trace 一下,如下图发现有一步查表置换操作
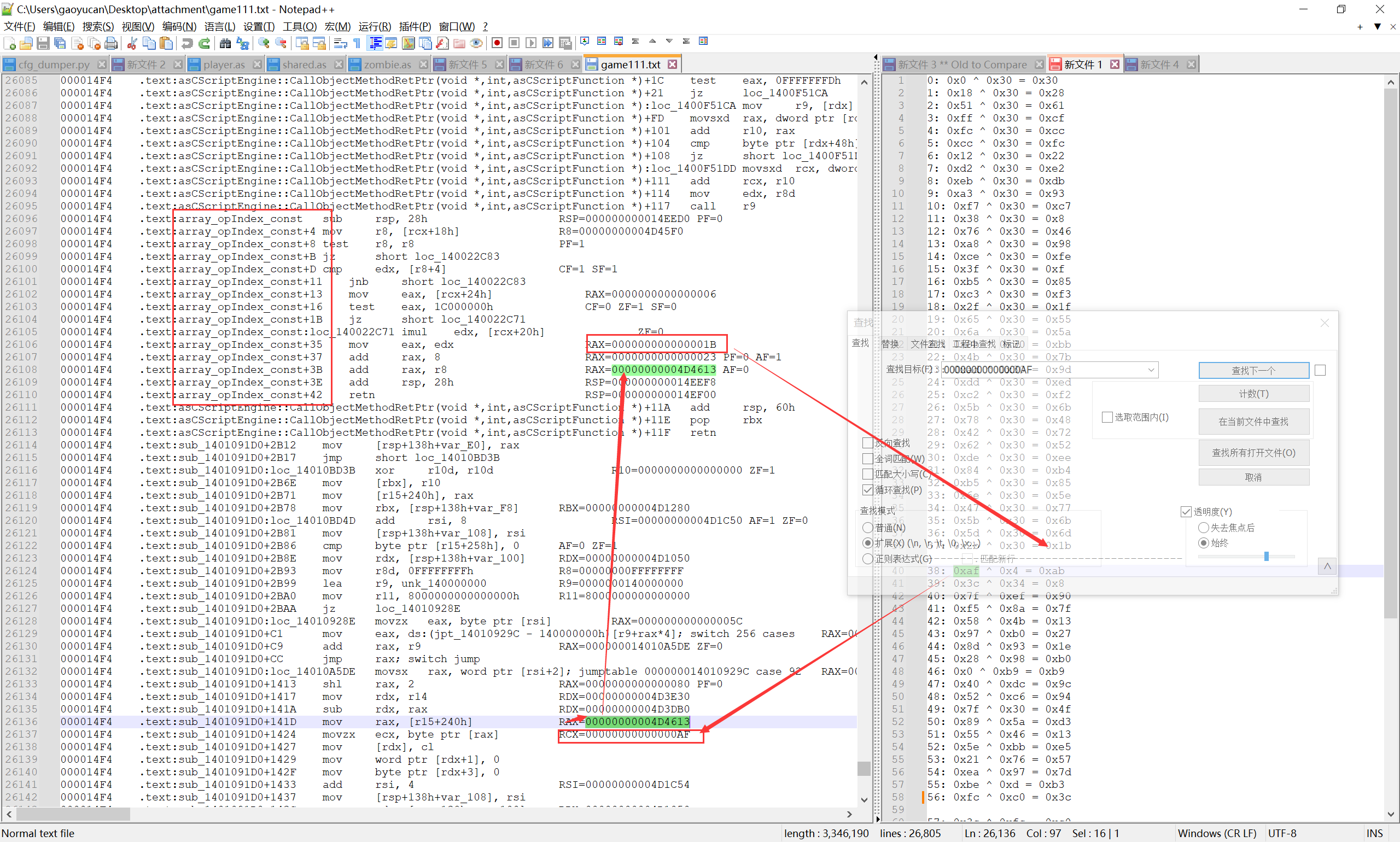
把表dump出来如下,
table = [0x63, 0x7C, 0x77, 0x7B, 0xF2, 0x6B, 0x6F, 0xC5, 0x30, 0x01, 0x67, 0x2B, 0xFE, 0xD7, 0xAB, 0x76, 0xCA, 0x82,
0xC9, 0x7D, 0xFA, 0x59, 0x47, 0xF0, 0xAD, 0xD4, 0xA2, 0xAF, 0x9C, 0xA4, 0x72, 0xC0, 0xB7, 0xFD, 0x93, 0x26,
0x36, 0x3F, 0xF7, 0xCC, 0x34, 0xA5, 0xE5, 0xF1, 0x71, 0xD8, 0x31, 0x15, 0x04, 0xC7, 0x23, 0xC3, 0x18, 0x96,
0x05, 0x9A, 0x07, 0x12, 0x80, 0xE2, 0xEB, 0x27, 0xB2, 0x75, 0x09, 0x83, 0x2C, 0x1A, 0x1B, 0x6E, 0x5A, 0xA0,
0x52, 0x3B, 0xD6, 0xB3, 0x29, 0xE3, 0x2F, 0x84, 0x53, 0xD1, 0x00, 0xED, 0x20, 0xFC, 0xB1, 0x5B, 0x6A, 0xCB,
0xBE, 0x39, 0x4A, 0x4C, 0x58, 0xCF, 0xD0, 0xEF, 0xAA, 0xFB, 0x43, 0x4D, 0x33, 0x85, 0x45, 0xF9, 0x02, 0x7F,
0x50, 0x3C, 0x9F, 0xA8, 0x51, 0xA3, 0x40, 0x8F, 0x92, 0x9D, 0x38, 0xF5, 0xBC, 0xB6, 0xDA, 0x21, 0x10, 0xFF,
0xF3, 0xD2, 0xCD, 0x0C, 0x13, 0xEC, 0x5F, 0x97, 0x44, 0x17, 0xC4, 0xA7, 0x7E, 0x3D, 0x64, 0x5D, 0x19, 0x73,
0x60, 0x81, 0x4F, 0xDC, 0x22, 0x2A, 0x90, 0x88, 0x46, 0xEE, 0xB8, 0x14, 0xDE, 0x5E, 0x0B, 0xDB, 0xE0, 0x32,
0x3A, 0x0A, 0x49, 0x06, 0x24, 0x5C, 0xC2, 0xD3, 0xAC, 0x62, 0x91, 0x95, 0xE4, 0x79, 0xE7, 0xC8, 0x37, 0x6D,
0x8D, 0xD5, 0x4E, 0xA9, 0x6C, 0x56, 0xF4, 0xEA, 0x65, 0x7A, 0xAE, 0x08, 0xBA, 0x78, 0x25, 0x2E, 0x1C, 0xA6,
0xB4, 0xC6, 0xE8, 0xDD, 0x74, 0x1F, 0x4B, 0xBD, 0x8B, 0x8A, 0x70, 0x3E, 0xB5, 0x66, 0x48, 0x03, 0xF6, 0x0E,
0x61, 0x35, 0x57, 0xB9, 0x86, 0xC1, 0x1D, 0x9E, 0xE1, 0xF8, 0x98, 0x11, 0x69, 0xD9, 0x8E, 0x94, 0x9B, 0x1E,
0x87, 0xE9, 0xCE, 0x55, 0x28, 0xDF, 0x8C, 0xA1, 0x89, 0x0D, 0xBF, 0xE6, 0x42, 0x68, 0x41, 0x99, 0x2D, 0x0F,
0xB0, 0x54, 0xBB, 0x16]
看打印出来的 xor 数据,加密逻辑应该是
for b in e:
e_1.append(table[b])
for i in range(0x26):
e_1[i] ^= e_1[0x26 - i - 1]
在 send 下断点 trace 之后,往上找 cmp 指令然后找要对比的密文了,结果发现在 cmp 指令对比的一直是 0x26 和我输入的长度,不一致就 send no~
判断长度过了后,在所有可能的 cmp 分支下断点,发现对比的目标是 0, 看 trace 结果前面是个 xor,贴出最终的 调试脚本
from idaapi import *
import time
#
# 解密 game.flua
# # def decrypt(addr, len, flag_addr):
# # patch_byte(flag_addr, 1)
# # for i in range(len):
# # patch_byte(addr + i, get_byte(addr + i) ^ 0xdb)
# #
# # decrypt(0x140218020, 0x13CD, 0x14021B558)
#
i = 0
while True:
if get_reg_val('rip') == 0x140109908: # xor 分支中 xor 指令的地址
if i == 0x26 * 3:
break
right = get_byte(get_reg_val('rax'))
left = get_reg_val('rdx')
print(f'{i}: {hex(left)} ^ {hex(right)} = {hex(right ^ left)}')
if i / 0x26 > 1:
set_reg_val('rdx', right)
continue_process()
time.sleep(0.2)
i += 1
else:
break
wait_for_next_event(WFNE_SUSP, -1)
拿到第一步中的密钥流,以及最后一步判断的目标,最后解密脚本如下:
table = [0x63, 0x7C, 0x77, 0x7B, 0xF2, 0x6B, 0x6F, 0xC5, 0x30, 0x01, 0x67, 0x2B, 0xFE, 0xD7, 0xAB, 0x76, 0xCA, 0x82,
0xC9, 0x7D, 0xFA, 0x59, 0x47, 0xF0, 0xAD, 0xD4, 0xA2, 0xAF, 0x9C, 0xA4, 0x72, 0xC0, 0xB7, 0xFD, 0x93, 0x26,
0x36, 0x3F, 0xF7, 0xCC, 0x34, 0xA5, 0xE5, 0xF1, 0x71, 0xD8, 0x31, 0x15, 0x04, 0xC7, 0x23, 0xC3, 0x18, 0x96,
0x05, 0x9A, 0x07, 0x12, 0x80, 0xE2, 0xEB, 0x27, 0xB2, 0x75, 0x09, 0x83, 0x2C, 0x1A, 0x1B, 0x6E, 0x5A, 0xA0,
0x52, 0x3B, 0xD6, 0xB3, 0x29, 0xE3, 0x2F, 0x84, 0x53, 0xD1, 0x00, 0xED, 0x20, 0xFC, 0xB1, 0x5B, 0x6A, 0xCB,
0xBE, 0x39, 0x4A, 0x4C, 0x58, 0xCF, 0xD0, 0xEF, 0xAA, 0xFB, 0x43, 0x4D, 0x33, 0x85, 0x45, 0xF9, 0x02, 0x7F,
0x50, 0x3C, 0x9F, 0xA8, 0x51, 0xA3, 0x40, 0x8F, 0x92, 0x9D, 0x38, 0xF5, 0xBC, 0xB6, 0xDA, 0x21, 0x10, 0xFF,
0xF3, 0xD2, 0xCD, 0x0C, 0x13, 0xEC, 0x5F, 0x97, 0x44, 0x17, 0xC4, 0xA7, 0x7E, 0x3D, 0x64, 0x5D, 0x19, 0x73,
0x60, 0x81, 0x4F, 0xDC, 0x22, 0x2A, 0x90, 0x88, 0x46, 0xEE, 0xB8, 0x14, 0xDE, 0x5E, 0x0B, 0xDB, 0xE0, 0x32,
0x3A, 0x0A, 0x49, 0x06, 0x24, 0x5C, 0xC2, 0xD3, 0xAC, 0x62, 0x91, 0x95, 0xE4, 0x79, 0xE7, 0xC8, 0x37, 0x6D,
0x8D, 0xD5, 0x4E, 0xA9, 0x6C, 0x56, 0xF4, 0xEA, 0x65, 0x7A, 0xAE, 0x08, 0xBA, 0x78, 0x25, 0x2E, 0x1C, 0xA6,
0xB4, 0xC6, 0xE8, 0xDD, 0x74, 0x1F, 0x4B, 0xBD, 0x8B, 0x8A, 0x70, 0x3E, 0xB5, 0x66, 0x48, 0x03, 0xF6, 0x0E,
0x61, 0x35, 0x57, 0xB9, 0x86, 0xC1, 0x1D, 0x9E, 0xE1, 0xF8, 0x98, 0x11, 0x69, 0xD9, 0x8E, 0x94, 0x9B, 0x1E,
0x87, 0xE9, 0xCE, 0x55, 0x28, 0xDF, 0x8C, 0xA1, 0x89, 0x0D, 0xBF, 0xE6, 0x42, 0x68, 0x41, 0x99, 0x2D, 0x0F,
0xB0, 0x54, 0xBB, 0x16]
e_1 = [0x27, 0xfd, 0x94, 0x28, 0x97, 0x7d, 0xcb, 0xd3, 0x31, 0xdd, 0xe, 0xcc, 0x97, 0xc9, 0xa8, 0x5, 0xae, 0xaf, 0x61,
0xd0, 0x88, 0xf8, 0xd7, 0xee, 0x16, 0x36, 0x67, 0x3a, 0x8c, 0x35, 0x97, 0x2c, 0x22, 0x17, 0xdd, 0xef, 0x9a, 0x96]
for i in range(0x25, -1, -1):
e_1[i] ^= e_1[0x26 - i - 1]
e_0 = []
for b in e_1:
e_0.append(table.index(b))
xor_key = [0x0, 0x18, 0x51, 0xff, 0xfc, 0xcc, 0x12, 0xd2, 0xeb, 0xa3, 0xf7, 0x38, 0x76, 0xa8, 0xce, 0x3f, 0xb5, 0xc3, 0x2f,
0x65, 0x6a, 0x8b, 0x4b, 0xad, 0xdd, 0xc2, 0x5b, 0x78, 0x42, 0x62, 0xde, 0x84, 0xb5, 0x6e, 0x47, 0x5b, 0x5d, 0x2b]
for i in range(0x26):
e_0[i] ^= xor_key[i]
table2 = b'abcdefghijklmnopqrstuvwxyz0123456789+/ABCDEFGHIJKLMNOPQRSTUVWXYZ'
table3 = [0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF,
0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF,
0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0x3E, 0xFF, 0xFF, 0xFF, 0x3F, 0x34, 0x35, 0x36, 0x37, 0x38, 0x39,
0x3A, 0x3B, 0x3C, 0x3D, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0x00, 0x01, 0x02, 0x03, 0x04, 0x05, 0x06,
0x07, 0x08, 0x09, 0x0A, 0x0B, 0x0C, 0x0D, 0x0E, 0x0F, 0x10, 0x11, 0x12, 0x13, 0x14, 0x15, 0x16, 0x17, 0x18,
0x19, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0x1A, 0x1B, 0x1C, 0x1D, 0x1E, 0x1F, 0x20, 0x21, 0x22, 0x23, 0x24,
0x25, 0x26, 0x27, 0x28, 0x29, 0x2A, 0x2B, 0x2C, 0x2D, 0x2E, 0x2F, 0x30, 0x31, 0x32, 0x33, 0xFF, 0xFF, 0xFF,
0xFF, 0xFF, 0xC0, 0xDF, 0x1E, 0x40, 0x01, 0x00, 0x00, 0x00]
flag = ''
for b in e_0:
if b in table2:
flag += chr(table3.index(table2.index(b)))
else:
flag += chr(b)
print(flag)