md cert;cd cert;md private
自签CA
1.生成CA的rsa密钥对
openssl genrsa -des3 -out ./private/cakey.pem 2048
#输入后弹出
Enter PEM pass phrase: 123456(输入)
Verifying - Enter PEM pass phrase: 123456(输入)
2.生成CA证书并自签发CA证书
#方法一 openssl req -new -days 365 -key ./private/cakey.pem -out careq.pem #生成CA证书请求
openssl ca -selfsign -in careq.pem -out ./crt/cacert.pem #自签发CA证书
#方法二(一条命令生成,利用-x509)
openssl req -new -x509 -days 365 -key ./private/cakey.pem -out ./crt/cacert.pem
Country Name (2 letter code) [AU]:cn
State or Province Name (full name) [Some-State]:cn
Locality Name (eg, city) []:cn
Organization Name (eg, company) [Internet Widgits Pty Ltd]:cn
Organizational Unit Name (eg, section) []:cn
Common Name (e.g. server FQDN or YOUR name) []:china
Email Address []:example@163.com
此时已经创建起来了CA可以进行证书的签发
生成用户证书
1.生成用户证书RSA密钥
openssl genrsa -des3 -out ./private/userkey.pem
2.生成用户证书请求体
openssl req -new -days 365 -key ./private/userkey.pem -out uesrreq.pem
3.使用CA签发用户证书
openssl ca -in userreq.pem -out usercert.pem
方法二
1.创建根目录
C:\Users\9A202-1>d:
#进入到d盘
md cert
D:\>cd cert
2.在根目录生成一个serial和index.txt文件
linux touch index.txt #空
linux touch "01" > serial
windows type nul > index.txt #空 windows `echo 01 > serial`
在创建自签证书的过程中,通过输入命令 touch "01" > serial,是为了创建一个包含设备序列号的文件。这个文件是必要的,因为该文件存储了证书颁发机构(CA)生成的每个设备的唯一标识。在为每个设备生成证书时需要使用这个唯一标识作为证书的一个字段,以确保每个设备的证书都是唯一的。通过这种方式可以防止在通讯过程中进行中人攻击。
3.修改配置文件
windows下的配置文件路径
C:\Program Files\Common Files\SSL/openssl.cnf
修改三个参数
[ CA_default ]
dir =./DemoCA --> dir = D:/cert #自己创建的根路径
new_certs_dir = $dir/newcerts --> new_certs_dir = $dir/
private_key = $dir/private/cakey.pem --> private_key = $dir/cakey.pem
创建CA证书
openssl req -new -x509 -days 365 -key ./cakey.pem -out cacert.pem
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [AU]:cn
State or Province Name (full name) [Some-State]:cn
Locality Name (eg, city) []:
Organization Name (eg, company) [Internet Widgits Pty Ltd]:
Organizational Unit Name (eg, section) []:
Common Name (e.g. server FQDN or YOUR name) []:www.ca.com
Email Address []:
4.创建apache的证书
D:\cert>openssl genrsa -out ./apache/apache.key 2048
5.创建apche的证书请求
D:\cert>openssl req -new -key ./apache/apache.key -out ./apache/apache.csr
#证书请求不需要时限 You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [AU]:cn #注意这里如果不改配置文件的话可能需要和ca的配置相同
State or Province Name (full name) [Some-State]:cn
Locality Name (eg, city) []:
Organization Name (eg, company) [Internet Widgits Pty Ltd]:
Organizational Unit Name (eg, section) []:
Common Name (e.g. server FQDN or YOUR name) []:www.skills.com
Email Address []:
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:
An optional company name []:
#如果和ca的配置不一样的话可能有个报错,报错了就不生成crt了
D:\cert>openssl ca -in ./apache/apache.csr -out ./apache/apache.crt -days 365
Using configuration from C:\Program Files\Common Files\SSL/openssl.cnf
Check that the request matches the signature
Signature ok
The countryName field is different between
CA certificate (cn) and the request (AU) ##这里报错了
解决方案:可以修改openssl.cnf文件
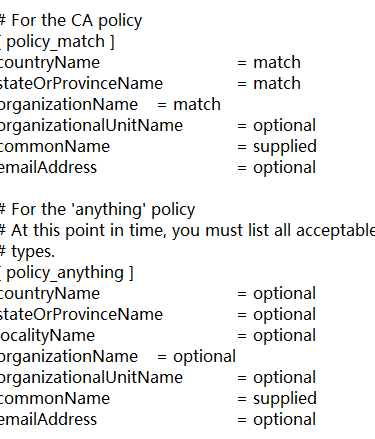
将countryName 改成optional
sataorprovincename改成 optional
organizationanme = option
前三个修改