EasyRSA
(额。。这个题看错了不是挑战赛的。这里当做好题记录下来了)
题目信息:500 分 5 Polar币
from Crypto.Util.number import bytes_to_long, long_to_bytes, getPrime
import gmpy2, os
p = getPrime(512)
q = getPrime(512)
n = p*q
e = 65537
c = pow(flag1,e,n)
print(hex(n).strip("L"))
print(hex(c).strip("L"))
q = getPrime(512)
n = p*q
c = pow(flag2,e,n)
print(hex(n).strip("L"))
print(hex(c).strip("L"))
# 0x6364991c9ff97120fa450866ab1a3a0bd4e16bd71c8f7a0a4229b1307531fef6e2cb2410c3283db91e49476a8afcd590aedc3384b5045b2fb57208587a242e94e7528ea4998b66f3a57c7ac66b806d9631f8cff3e73557630a0e70467b5f6246ee3fbc6ed89d00af1e931cfabbc5f1deddb99a14dfac51820ffe48f2841bc1a1
# 0x17343966398f483e121de6c2515d630ebc31b0cbdbed5cdc2c09c2b253fc0bc9a055e222eac108e189b6bd6a705d2972c5ce435fa5a4469602bb7a0d0ee95c3f397a3fa4985e6cb7531eb1b5603be134d0dce2c47069d216063b5aea135681edebcfb20c86c3ab09c350901639ee5f74831b056b33c7c26fcef7a34fd39e9dab
# 0x4bf20122dc9f3fbd31bf4389d2a497392caa3de045fe217b692620874ce7a63146c6348c3f65a08bd3f9ec893236e904ceac4e54acdf04e198e7d2bb085c4d646be300158bafc27615875f65d2d1b196d14c024de581f511519631da1d727d6b4fd9c02298b6334938e5a6a7616389948fb9f35677fad6d596d95e5e67aa5549
# 0x2583826196498e3c4b5e1c9c967a74337e85f2b4f9827f2e0a164e3923644a3859c85bf8248ddfcb90f03c31f8704548d7dfd071581eee8a268ef715f93636485b56e559eef55ceee7a54706cf12717d035cc1f6fca838e8ce32fcbd413565ff78500c9810ff8c22ae09d3746b927b4768fc92e6d46a2dfb395cd14ae1321fd0n不互素问题,利用欧几里得求公约数
exp:
import gmpy2
import binascii
e = 65537
n1 = 0x6364991c9ff97120fa450866ab1a3a0bd4e16bd71c8f7a0a4229b1307531fef6e2cb2410c3283db91e49476a8afcd590aedc3384b5045b2fb57208587a242e94e7528ea4998b66f3a57c7ac66b806d9631f8cff3e73557630a0e70467b5f6246ee3fbc6ed89d00af1e931cfabbc5f1deddb99a14dfac51820ffe48f2841bc1a1
c1 = 0x17343966398f483e121de6c2515d630ebc31b0cbdbed5cdc2c09c2b253fc0bc9a055e222eac108e189b6bd6a705d2972c5ce435fa5a4469602bb7a0d0ee95c3f397a3fa4985e6cb7531eb1b5603be134d0dce2c47069d216063b5aea135681edebcfb20c86c3ab09c350901639ee5f74831b056b33c7c26fcef7a34fd39e9dab
n2 = 0x4bf20122dc9f3fbd31bf4389d2a497392caa3de045fe217b692620874ce7a63146c6348c3f65a08bd3f9ec893236e904ceac4e54acdf04e198e7d2bb085c4d646be300158bafc27615875f65d2d1b196d14c024de581f511519631da1d727d6b4fd9c02298b6334938e5a6a7616389948fb9f35677fad6d596d95e5e67aa5549
c2 = 0x2583826196498e3c4b5e1c9c967a74337e85f2b4f9827f2e0a164e3923644a3859c85bf8248ddfcb90f03c31f8704548d7dfd071581eee8a268ef715f93636485b56e559eef55ceee7a54706cf12717d035cc1f6fca838e8ce32fcbd413565ff78500c9810ff8c22ae09d3746b927b4768fc92e6d46a2dfb395cd14ae1321fd0
e = 65537
p = gmpy2.gcd(n1, n2)
q = n1 // p # 这里用n1求第一部分,
phi = (p - 1) * (q - 1)
d = gmpy2.invert(e, phi)
m = gmpy2.powmod(c1, d, n1)
print(binascii.unhexlify(hex(m)[2:]))
#flag{c9bee33232dbbf
q = n2 // p # 这里用n2求第二部分,
phi = (p - 1) * (q - 1)
d = gmpy2.invert(e, phi)
m = gmpy2.powmod(c2, d, n2)
print(binascii.unhexlify(hex(m)[2:]))
#7872763d69d769c74d}天干地支
题目信息:100 分 1 Polar币
小李某一天收到一条微信,微信中写了几个不同的年份
丁丑 丙子 戊辰 壬午 丁丑 丙子 戊辰 壬午 壬辰 壬辰 辛未 丙戌
微信的后面还写有“+甲子”,请解出这段密文。
flag格式:flag{XXX}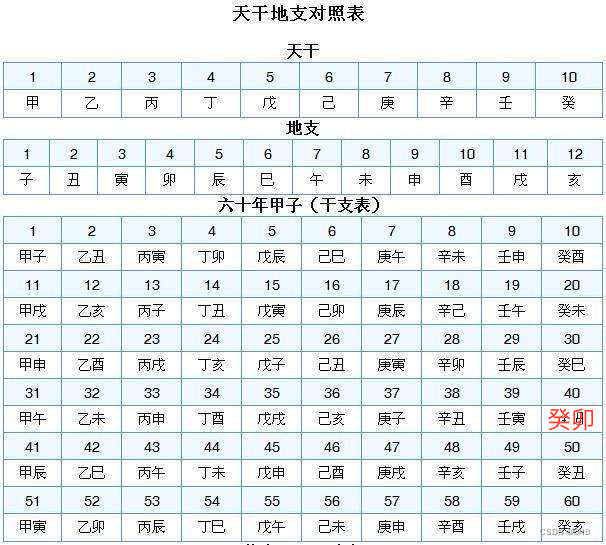
查表把附件里的年份转为数字,分别得到:14,13,5,19,14,13,5,19,29,29,8,23,提示加上甲子,就是加60
然后转ASCII码得到:JIAOJIAOYYDS,套上flag:flag{JIAOJIAOYYDS}
全世界都在说中国话
题目信息:100 分 1 Polar币
663867570008258541046114143248220132000152072143
时代在进步 中文也可以被翻译哦
得到flag用MD532位小写加密并套上flag{}中国电码转一下得到这都不会的话就给你一脑拍

md5加密后再套上壳:flag{679384ffaee1e8145a52408ac7ad6bfd}
小精灵来喽
题目信息:300 分 3 Polar币
压缩包有密码。。。但打开解压右边有提示哈哈,好好好

观察右边的密文eag'expxwxj,key=itsme,维吉尼亚解密得到who'stheelf
然后解压拿到里面文档

一种图形密码,结合题目名称可以想到是古精灵语
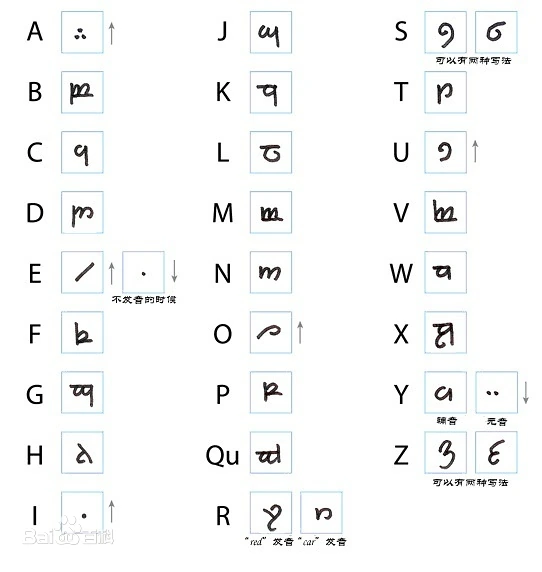

查表得到herec0mesthee1f,MD5大写得到flag{08460AE514ACCC54E5D8D4B690A75D29}
眼见非实
题目信息:300 分 3 Polar币
1111011111111011000110010101111111110010111011011110000110001101101110101110110111001100011000111100得出的结果用md5加密后套上flag{}二进制解码不行,题目名称眼见非实也就是说看到的不一定是真的,那么看到01我们可以想到培根的变型。
1 -> A,0 -> B,再培根密码解码
AAAABAAAAAAAABAABBBAABBABABAAAAAAAAABBABAAABAABAAAABBBBAABBBAABAABAAABABAAABAABAAABBAABBBAABBBAAAABBbaconiancipherisgoodMD5加密后:flag{68e5987347d955690d9782edc531ddf3}
Round
题目信息:500 分 5 Polar币
BRUEIFYRGBEUNVUICRHFU
FYURGUAROINNIEURYVYRU
E3BYUGDUWRNYUTFSRDE5W
FURYGRUTGUTUNAWGDUIEB
UYGIGNGIHFYBFYURGFURB
TFRUBYFUVOVNERTWINDUE
HUGRURBIGGNSUITIMTQEI
GBUTNGUIJTINGIEGFURYU
TYVCTYSAIBYEIFWIRHUGF
TRTUBGUYTRGSONIUONRRI
6YMUYTNYTIUWABRWBTESS
BRUHGUFGTJNUBAFDEGTEF
DHYEUBFYEYFTYUEBFIUBA
CTBRTNUKMIWGRBEHSDDVC
RUEBFUIRGFRBVXUAVTYEF
YUGRTFBUKCZUIWEIHUEFB
FRVRUIYUFRLNRUYGQEBYE这里有两串密码,来找找flag在哪吧
(听说阿拉伯数字全世界通用哦)
和谐民主和谐富强和谐民主和谐自由和谐富强和谐民主和谐自由和谐富强和谐文明和谐富强和谐民主和谐自由和谐富强和谐爱国和谐爱国和谐民主和谐富强和谐爱国
和谐爱国和谐自由和谐文明和谐民主和谐富强和谐民主和谐富强和谐爱国和谐爱国和谐自由和谐民主和谐富强和谐爱国和谐爱国和谐文明和谐富强和谐民主和谐富强和谐爱
国和谐爱国和谐自由和谐文明和谐富强和谐爱国和谐爱国和谐自由和谐文明和谐民主和谐富强和谐爱国和谐爱国和谐自由和谐文明和谐民主和谐富强和谐爱国和谐爱国和谐
自由和谐文明和谐民主和谐富强和谐爱国和谐爱国和谐自由和谐文明和谐民主和谐富强和谐爱国和谐爱国和谐自由和谐文明和谐民主
lqbehgfdajmopcikn
将找到的字符串进行md5加密后套上flag{}即可社会主义核心价值观解码
1014014020140881088421010884108820108842088421088421088421088421088421
发现只有01248,云影密码解码
AEEBEQWAURAVWWWWW再看第一个文件
托马斯杰斐逊 转轮密码
原理:给一个密码表,n行的26个字母,key是 1 - n 的数列, 密文是 n 个英文字母,根据 key 找对应行的密码表,然后在密码表上找密文字母,以这个字母为开头,重新排序。
先把lqbehgfdajmopcikn转成数字得到:12,17,2,5,8,7,6,4,1,10,13,15,16,3,9,11,14,密文是AEEBEQWAURAVWWWWW
比如第一个key是11,就要把第11行变为以A开头的串
6YMUYTNYTIUWABRWBTESS –> ABRWBTESS6YMUYTNYTIUW
以此类推
exp:
import re
text=""
code = [
"BRUEIFYRGBEUNVUICRHFU",
"FYURGUAROINNIEURYVYRU",
"E3BYUGDUWRNYUTFSRDE5W",
"FURYGRUTGUTUNAWGDUIEB",
"UYGIGNGIHFYBFYURGFURB",
"TFRUBYFUVOVNERTWINDUE",
"HUGRURBIGGNSUITIMTQEI",
"GBUTNGUIJTINGIEGFURYU",
"TYVCTYSAIBYEIFWIRHUGF",
"TRTUBGUYTRGSONIUONRRI",
"6YMUYTNYTIUWABRWBTESS",
"BRUHGUFGTJNUBAFDEGTEF",
"DHYEUBFYEYFTYUEBFIUBA",
"CTBRTNUKMIWGRBEHSDDVC",
"RUEBFUIRGFRBVXUAVTYEF",
"YUGRTFBUKCZUIWEIHUEFB",
"FRVRUIYUFRLNRUYGQEBYE"
]
print(code)
codetext="AEEBEQWAURAVWWWWW"
codenum = "12,17,2,5,8,7,6,4,1,10,13,15,16,3,9,11,14"
codenum=codenum.split(",")#把这些数字都弄到一个里面去
#print(codenum)
a=0
print("解密后的:")
for i in codenum:
index=code[int(i)-1].index(codetext[a])
a=a+1
code[int(i)-1]=code[int(i)-1][index:]+code[int(i)-1][:index]
print(code[int(i)-1])
#完成了变形了
print("下面是每一列的")
for i in range(len(code[0])):
str=""
print("第{}列的是:".format(i),end="")
for j in codenum:
str+=code[int(j)-1][i]
print(str.lower())flagisvucuuub3ayr
注意将flag转化为大写后再MD5加密,MD5加密后:flag{52c85c0bb38a8fc993d335401b56d9b6}
low encryption exponent RSA
题目信息:500 分 5 Polar币
【2023秋季个人挑战赛】 小王在学习了RSA加密后知道了,当n非常大时,将n拆分成两个素数相乘就变得十分困难,从而能够保证加密的安全性, 于是小王自以为是的使用了函数自动生成了很大的n,以为这样就很安全了,但他似乎没有考虑e对c的影响。
# -*- coding = utf-8 -*-
# @software:PyCharm
from Crypto.Util.number import *
import libnum
flag = b'***********************'
m = bytes_to_long(flag)
n = getRandomNBitInteger(2048)
e = 5
c = pow(m, e, n)
print(n)
print(c)
#n=18049146130359556157811138499355569967231668855528566823643376144155931993553424757354835027829037263429007310779886281743425186527415596058004878860570474866413182148724803537036078612785180550377667299555519230603647447077725080756322343538156406080031959768393145744701092093127752647143419553963316375696232038952573236311522683541862835602321038621904842874356522524316864553501304106884213097353522958546518042728628006318129608745487662533959888992223736595503203451378533217004433230837006796341055201266431153548000348148960250455415972226546646460918890401484239320725539304914347952245606818833495867312063
#c=377041108412334062897923100149371833160065752130578483588828849399791858197434981428466047315212724764223394695011882740933537996983126187094472520344493047769519118482187945467176598341785927269390299847888131061799861412055502165865052720513992259109503509827127768615772091500352075827289290029872935215672798059068944088543667111296361405639896493856695176145088430237388172420390881291650155157688737470414069130558367036786376549227175617218017578125哈哈哈,小明文
exp:
from Crypto.Util.number import long_to_bytes
from gmpy2 import iroot
c1 = 377041108412334062897923100149371833160065752130578483588828849399791858197434981428466047315212724764223394695011882740933537996983126187094472520344493047769519118482187945467176598341785927269390299847888131061799861412055502165865052720513992259109503509827127768615772091500352075827289290029872935215672798059068944088543667111296361405639896493856695176145088430237388172420390881291650155157688737470414069130558367036786376549227175617218017578125
m = iroot(c1,5)[0]
print(long_to_bytes(m).decode())
#flag{fea80b814dcb0ff0a17e36c1e72569e7}