xx航空
已对敏感信息进行脱敏
1 清空配置+固件升级
WS-C3750交换机配置清除与固件版本更新
Catalyst 3750的软件下载中心包含两组Cisco IOS映像,分别用于每个功能集和版本。一组仅包含扩展名为.bin的Cisco IOS映像文件。另一组包含Cisco IOS映像以及扩展名为.tar的基于Web的设备管理器, 这里我使用的是.bin的IOS映像文件.
在Catalyst 3750交换机堆叠中, flash:代表主交换机的闪存文件系统, dir flash: 命令显示主交换机的内容
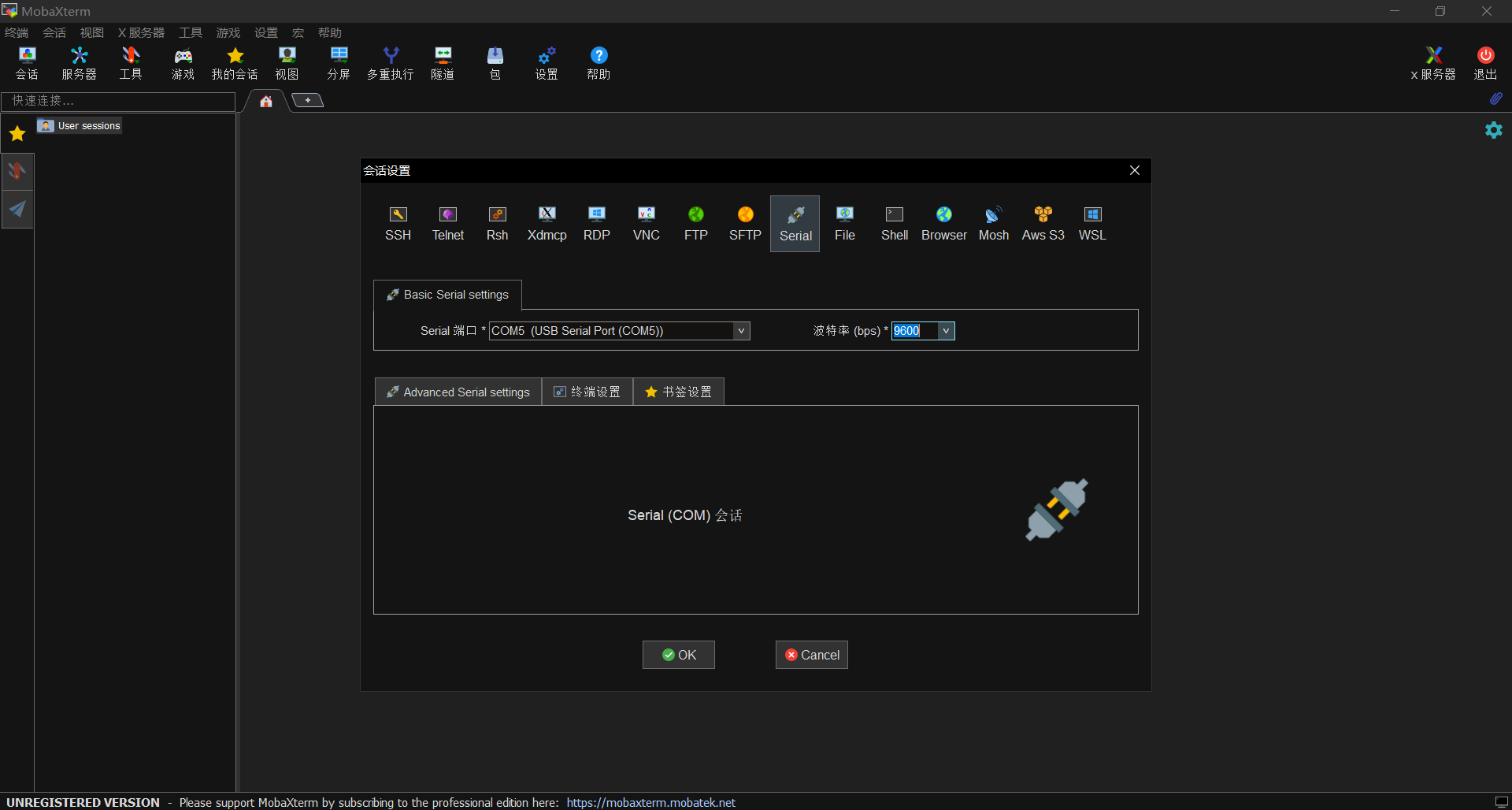
连接交换机, 这里最好使用console连接
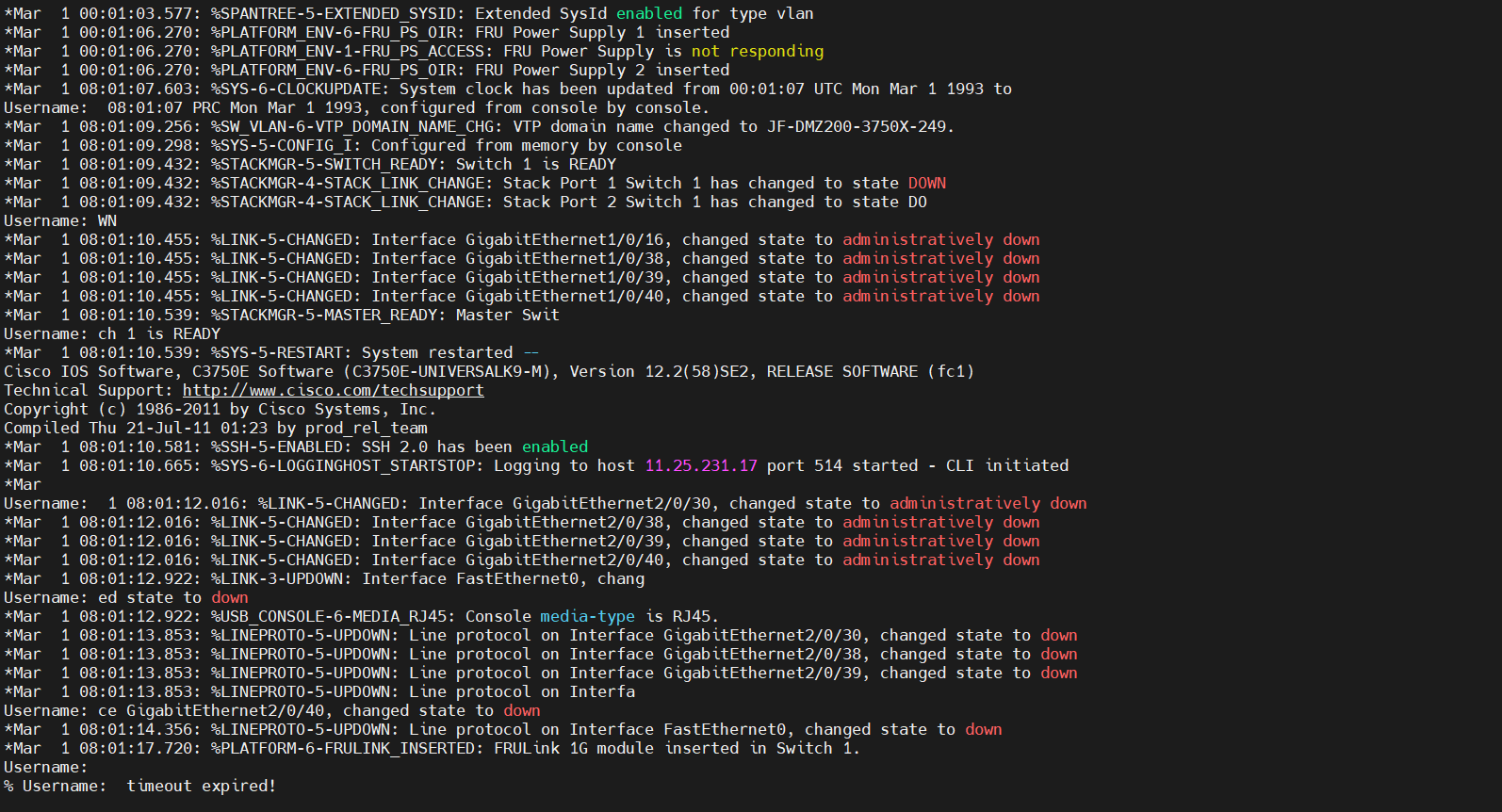
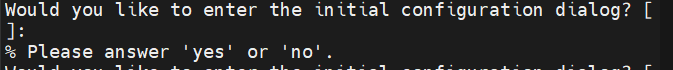
进来后旧配置有console密码, 不用惯着
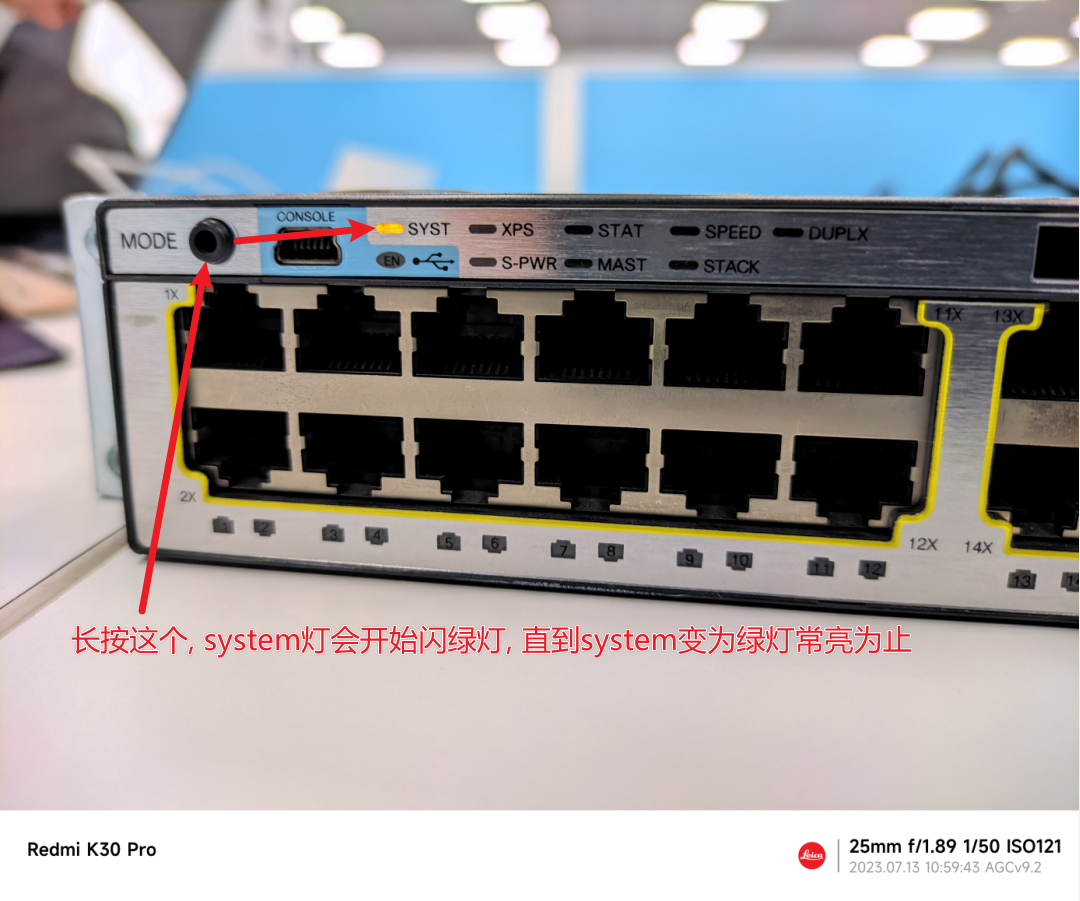
看到设备前面, 找到mode口, 长按直至sys灯常亮为止, 进入boot视图, 此视图下无法使用tab进行命令补全
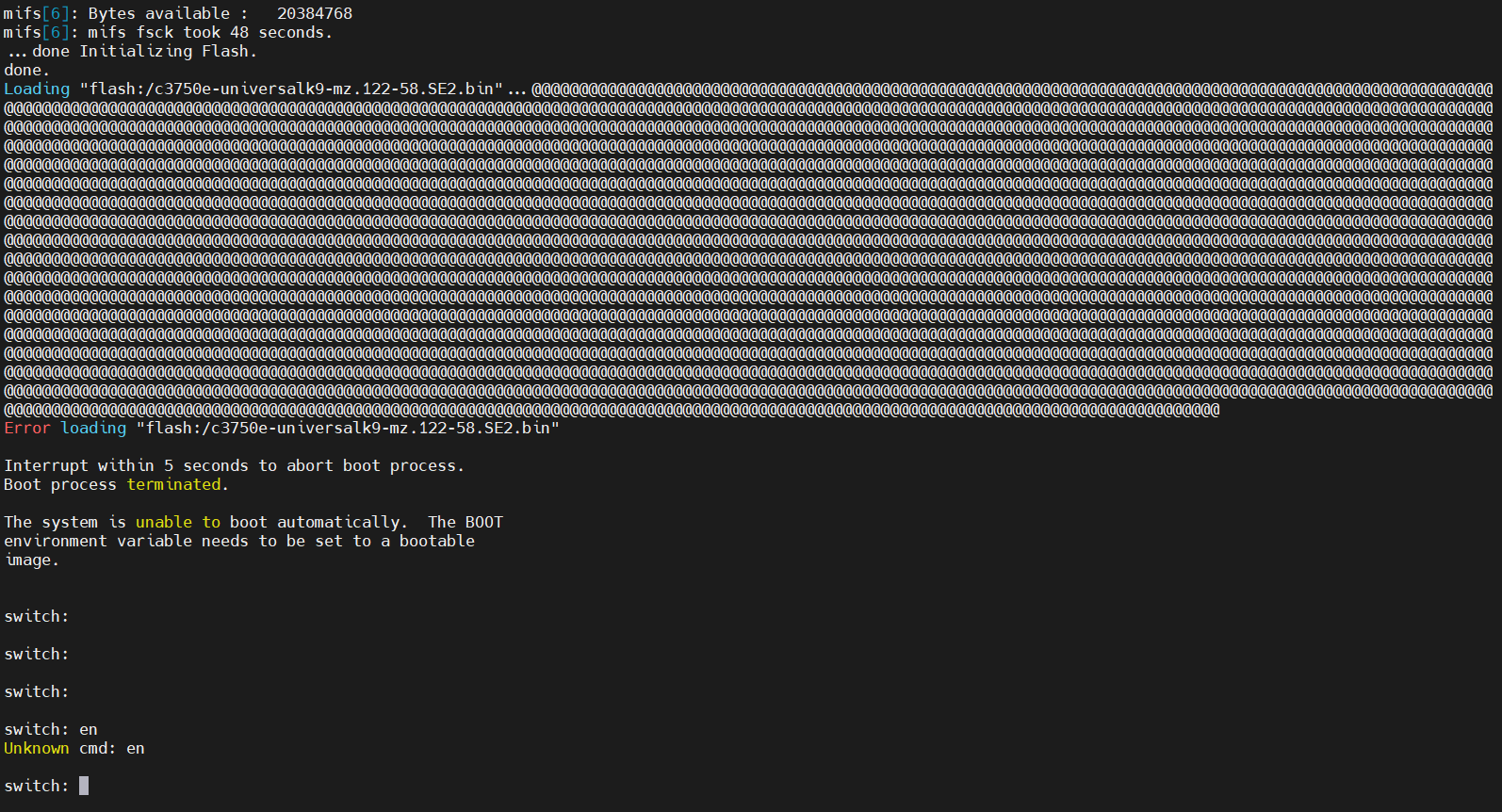
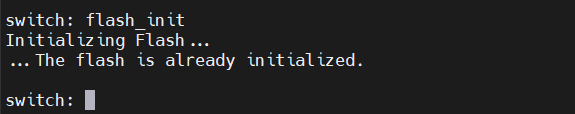
初始化flash
flash_init
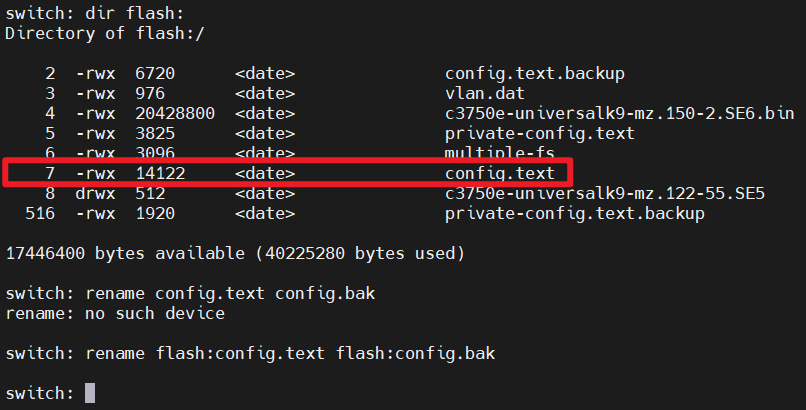
查看flash中的文件, 可以看到配置文件config.text(有的被删了就没有, 没有config.text在启动时也会自动创建)
dir flash:
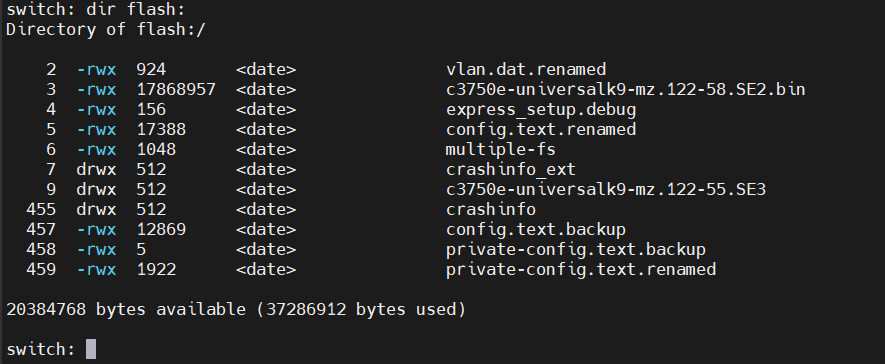
备份交换机原始配置文件, 没有就不用管
rename flash:config.text flash:config.bak
重启交换机
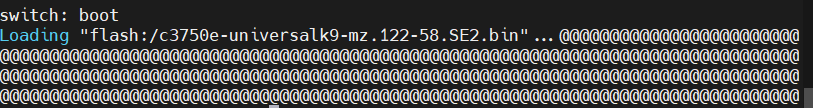
boot
no
密码清除, 进入交换机, 配个地址, 再拿根网线连接PC, 备份之前的固件到ftp服务器(我这里的是192.168.0.1)(交换机如果支持U盘可以省去这一步, 直接从U盘copy文件进来)
copy 固件名称 tftp://192.168.0.1
输入本地需要备份的文件名称
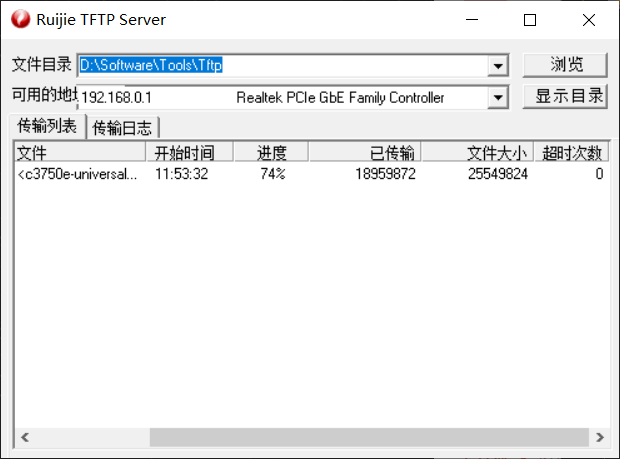
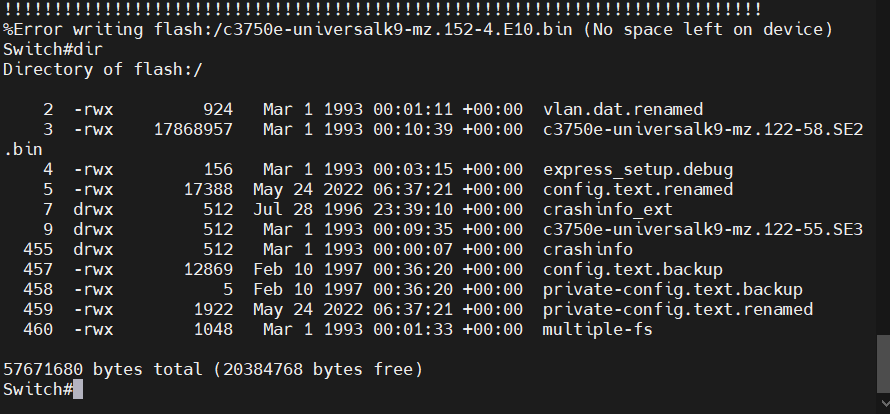
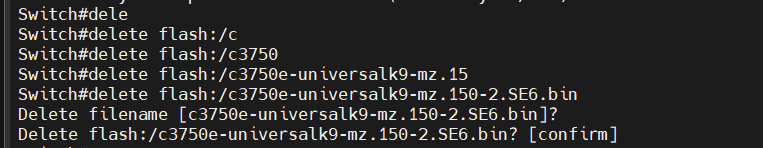
删除旧固件
delete 旧固件
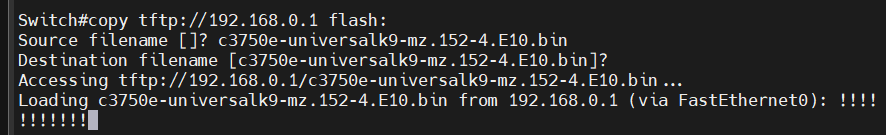
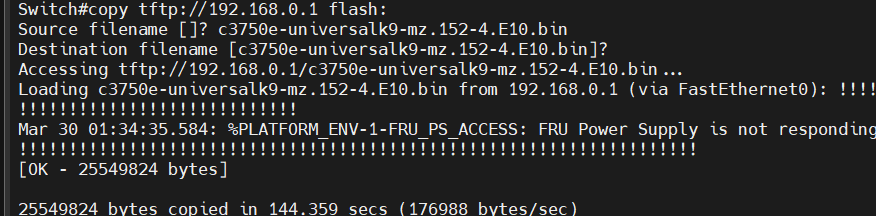
从ftp下载新固件到设备
copy tftp://192.168.0.1 flash:
输入下载文件名称
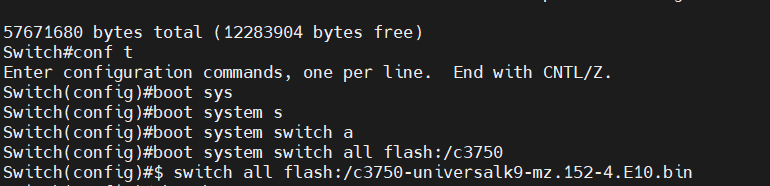
指定设备启动时加载的固件
boot system switch all 固件路径
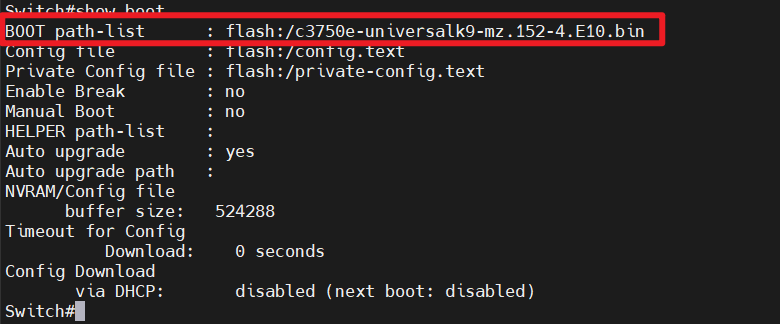
验证设备启动时固件引导
show boot
重启设备
reload
设备在一直@@@完后会进入一直passsss的状态, 这个状态会持续很长时间, 建议拔了console去整其他设备先
2 设备配置
共六台思科的C3750交换机, 其中两台做汇聚设备并进行堆叠, 其余四台做接入层设备
记得清除设备上的vlan, 思科设备的vlan位于flash上的vlan.dat中, 不随设备配置config.text一起清空, 需要删除文件或手动no掉
no vlan XXX
客户提供的拓扑规划:
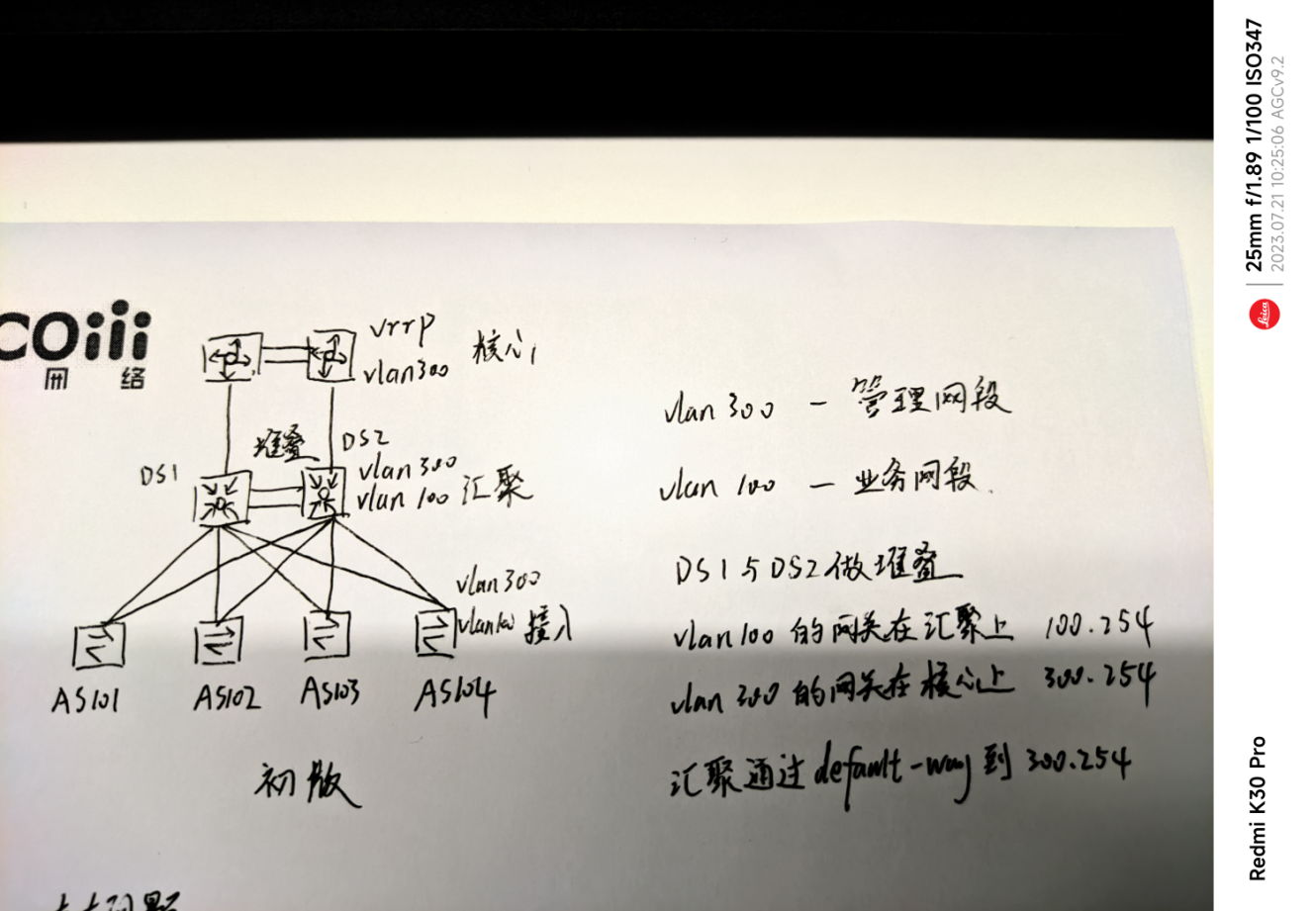
此版本存在的问题:
- 出方向流量: AS10X(vlan100)-->DSX(vlan100)-->核心(vlan300)-->路由器/防火墙
- 入方向流量: 路由器/防火墙-->核心(vlan300)-->DSX(vlan300)-->AS10X(vlan100)
在汇聚和核心之间, 出方向业务流量通过vlan100传递, 入方向业务流量通过vlan300传递, 业务流量在这条链路上杂糅了两个vlan
配置
接入
service tcp-keepalives-in
service tcp-keepalives-out
service timestamps debug datetime msec localtime show-timezone
service timestamps log datetime msec localtime show-timezone
service password-encryption
!
hostname XX-XX-XX-XX-AS101 //对应更改
!
boot-start-marker
boot-end-marker
!
logging buffered 8192!
username admin15 privilege 15 password Qurare
enable secret Qurare
aaa new-model
tacacs-server host 11.24.233.127 single-connection key Qurare2
tacacs-server host 11.24.233.128 single-connection key Qurare2
tacacs-server host 11.24.233.129 single-connection key Qurare2
!
!
aaa group server tacacs+ mfacs
server 11.24.233.127
server 11.24.233.128
server 11.24.233.129
!
aaa authentication login consolelogin line
aaa authentication login acslogin group mfacs local
aaa authorization exec acsexec group mfacs if-authenticated
aaa authorization commands 15 cmd15 group mfacs if-authenticated
aaa accounting exec default start-stop group mfacs
aaa accounting commands 1 default start-stop group mfacs
aaa accounting commands 15 default start-stop group mfacs
!
!
!
!
!
aaa session-id common
clock timezone PRC 8 0
system mtu routing 1500
vtp domain XX-XX-XX-XX-AS101 //对应更改
vtp mode transparent
udld aggressive
ip arp inspection vlan 100
ip arp inspection validate src-mac dst-mac ip
ip arp inspection log-buffer entries 1024
ip arp inspection log-buffer logs 1024 interval 300
!
!
ip dhcp snooping vlan 100
no ip dhcp snooping information option
ip dhcp snooping database flash:/dhcp-snooping.db
ip dhcp snooping database write-delay 3600
ip dhcp snooping database timeout 60
ip dhcp snooping
no ip domain-lookup
ip domain-name mf.com
!
!
crypto key generate rsa general-keys modulus 1024
!
!
errdisable recovery cause arp-inspection
errdisable recovery interval 60
!
spanning-tree mode rapid-pvst
spanning-tree portfast default
spanning-tree portfast bpduguard default
spanning-tree extend system-id
!
vlan internal allocation policy ascending
!
vlan 100
name PRIVATE-NET
!
vlan 300
!
ip ssh version 2
!
!
!
!
!
interface range GigabitEthernet1/0/1 -48
switchport access vlan 100
switchport mode access
ip arp inspection limit rate 300
ip dhcp snooping limit rate 300
interface GigabitEthernet1/1/1 //对应更改
description XXX-XXX-XXX-XXX-DS100_G1/0/1 //对应更改
switchport trunk allowed vlan all
switchport trunk encapsulation dot1q
switchport mode trunk
ip arp inspection trust
ip dhcp snooping trust
channel-group 1 mode active
interface GigabitEthernet1/1/2 //对应更改
description XX-XX-XX-XX-DS100_G2/0/1 //对应更改
switchport trunk allowed vlan all
switchport trunk encapsulation dot1q
switchport mode trunk
ip arp inspection trust
ip dhcp snooping trust
channel-group 1 mode active
interface Vlan1
no ip address
no ip route-cache
shutdown
!
interface Vlan300
ip address 10.155.254.101 255.255.255.0 //对应更改
no ip route-cache
no shutdown
!
ip default-gateway 10.155.254.254
no ip http server
no ip http secure-server
logging esm config
logging trap debugging
logging 11.25.231.17
logging facility local0
logging source-interfac vlan 300
ntp server 11.25.233.40
snmp-server community xhpublic RO
!
!
line con 0
exec-timeout 5 0
password 0 Qurare
line vty 0 4
exec-timeout 5 0
authorization commands 15 cmd15
authorization exec acsexec
logging synchronous
login authentication acslogin
transport preferred ssh
transport input ssh
transport output ssh
line vty 5 15
exec-timeout 5 0
authorization commands 15 cmd15
authorization exec acsexec
logging synchronous
login authentication acslogin
transport preferred ssh
transport input ssh
transport output ssh
!
注: 思科有部分老型号的交换机trunk的封装并未使用dot1q, 而是使用思科私有的trunk封装协议, 如果未使用dot1q会导致mode trunk命令报错, 无法为接口配置trunk
汇聚暂时没有配置, 因为下面还需要更改, 汇聚会在下面给出变更后的脚本
3 客户需求变更
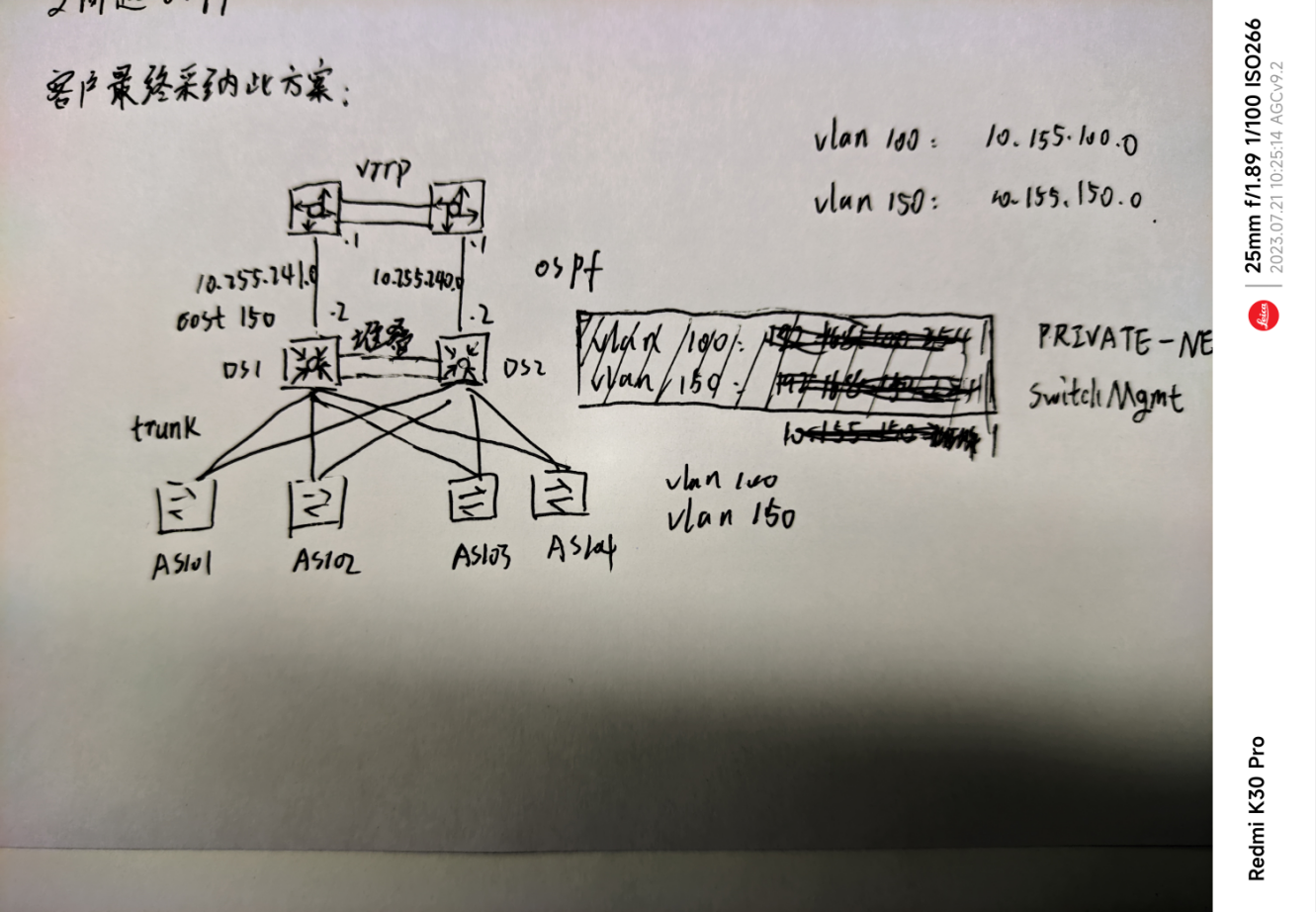
对于之前存在问题的拓扑, 我们给出如下两个方案:
-
在核心上添加vlan100和vlanif100, 并使汇聚的默认路由指向核心的vlanif100, 使得业务流量出入汇聚都是通过vlan100;
此方案被客户拒绝, 原因是不愿意动核心的配置
-
在汇聚上添加vlan150作为管理网段, 并指定vlan150的网关为汇聚交换机, 使得业务网段和管理网段的网关位于同一台设备(两台汇聚依旧是堆叠), 汇聚则起ospf与核心交换路由表项.
此方案被客户采纳.
最终敲定的更改方案, 在之前的配置上做出如下更改
配置
接入(追加)
!
vlan 150
name SwitchMgmt
!
!
interface Vlan150
ip address 10.155.150.103 255.255.255.0 //对应更改
no ip route-cache
!
no ip default-gateway
ip default-gateway 10.155.150.1
no logging source-interface vlan 300
logging source-interface vlan 150
!
!
no vlan 300
no interface vlan 300
!
int port-channel 1
ip dhcp snooping trust //这个是之前忘记了, 在这里补上
!
汇聚(完整)
service tcp-keepalives-in
service tcp-keepalives-out
service timestamps debug datetime msec localtime show-timezone
service timestamps log datetime msec localtime show-timezone
service password-encryption
!
hostname XX-XX-XX-XX-DS1
!
boot-start-marker
boot-end-marker
!
logging buffered 8192!
username admin15 privilege 15 password Qurare
enable secret Qurare
aaa new-model
tacacs-server host 11.24.233.127 single-connection key Qurare2
tacacs-server host 11.24.233.128 single-connection key Qurare2
tacacs-server host 11.24.233.129 single-connection key Qurare2
!
!
aaa group server tacacs+ mfacs
server 11.24.233.127
server 11.24.233.128
server 11.24.233.129
!
aaa authentication login consolelogin line
aaa authentication login acslogin group mfacs local
aaa authorization exec acsexec group mfacs if-authenticated
aaa authorization commands 15 cmd15 group mfacs if-authenticated
aaa accounting exec default start-stop group mfacs
aaa accounting commands 1 default start-stop group mfacs
aaa accounting commands 15 default start-stop group mfacs
!
!
!
!
!
aaa session-id common
clock timezone PRC 8 0
system mtu routing 1500
vtp domain XX-XX-XX-XX-DS1
vtp mode transparent
udld aggressive
ip arp inspection vlan 100
ip arp inspection validate src-mac dst-mac ip
ip arp inspection log-buffer entries 1024
ip arp inspection log-buffer logs 1024 interval 300
!
!
ip dhcp snooping vlan 100
no ip dhcp snooping information option
ip dhcp snooping database flash:/dhcp-snooping.db
ip dhcp snooping database write-delay 3600
ip dhcp snooping database timeout 60
ip dhcp snooping
no ip domain-lookup
ip domain-name mf.com
!
!
crypto key generate rsa general-keys modulus 1024
!
!
errdisable recovery cause arp-inspection
errdisable recovery interval 60
!
spanning-tree mode rapid-pvst
spanning-tree portfast default
spanning-tree portfast bpduguard default
spanning-tree extend system-id
!
vlan internal allocation policy ascending
!
vlan 100
name PRIVATE-NET
!
vlan 150
name SwitchMgmt
!
ip ssh version 2
!
!
!
!
!
router ospf 110
router-id 10.155.150.1
max-metric router-lsa on-startup wait-for-bgp
log-adjacency-changes detail
auto-cost reference-bandwidth 100000
nsf ietf
area 100 stub
timers throttle spf 30 100 1000
timers lsa arrival 50
timers pacing flood 10
passive-interface default
no passive-interface GigabitEthernet2/1
no passive-interface GigabitEthernet1/1
network 10.155.150.1 0.0.0.0 area 100
network 10.155.100.1 0.0.0.0 area 100
network 10.155.240.2 0.0.0.0 area 100
network 10.155.241.2 0.0.0.0 area 100
!
interface GigabitEthernetX/XX
description XXXX
switchport trunk allowed vlan all
switchport mode trunk
ip arp inspection trust
ip dhcp snooping trust
interface GigabitEthernet1/1
description XXXX
no switchport
ip address 10.255.241.2 255.255.255.252
ip ospf authentication message-digest
ip ospf message-digest-key 1 md5 0 mf2ospf
ip ospf network point-to-point
ip ospf cost 150
ip ospf mtu-ignore
interface GigabitEthernet2/1
description XXXX
no switchport
ip address 10.255.240.2 255.255.255.252
ip ospf authentication message-digest
ip ospf message-digest-key 1 md5 0 mf2ospf
ip ospf network point-to-point
ip ospf mtu-ignore
interface Vlan1
no ip address
no ip route-cache
shutdown
!
interface Vlan150
description SwitchMgmt
ip address 10.155.150.1 255.255.255.0
no ip route-cache
!
interface Vlan100
description PRIVATE-NET
ip address 10.155.100.1 255.255.255.0
ip helper-address 11.24.239.26
ip helper-address 11.25.239.26
no ip route-cache
!
no ip http server
no ip http secure-server
logging esm config
logging trap debugging
logging 11.25.231.17
logging facility local0
logging source-interfac int vl 150
ntp server 11.25.233.40
snmp-server community xhpublic RO
!
!
line con 0
exec-timeout 5 0
password 0 Qurare
line vty 0 4
exec-timeout 5 0
authorization commands 15 cmd15
authorization exec acsexec
logging synchronous
login authentication acslogin
transport preferred ssh
transport input ssh
transport output ssh
line vty 5 15
exec-timeout 5 0
authorization commands 15 cmd15
authorization exec acsexec
logging synchronous
login authentication acslogin
transport preferred ssh
transport input ssh
transport output ssh
!