1. 概述
接下来开始研究istio接入,今天已经成功接入kubernetes1.24,并且还注入deployment了,记录一下
环境:
kubernetes 1.24
istio 1.17.2
官方文档:
https://istio.io/latest/zh/docs/setup/install/istioctl/
2. istio安装
2.1.下载
https://github.com/istio/istio/releases/download/1.17.2/istio-1.17.2-linux-amd64.tar.gz
tar -zxvf istio-1.17.2-linux-amd64.tar.gz
2.2. 安装
sudo ./istioctl install
qiteck@logic:~/program/istio/istio-1.17.2/bin$ sudo ./istioctl install
This will install the Istio 1.17.2 default profile with ["Istio core" "Istiod" "Ingress gateways"] components into the cluster. Proceed? (y/N) y
✔ Istio core installed
✔ Istiod installed
✔ Ingress gateways installed
✔ Installation complete Making this installation the default for injection and validation.
Thank you for installing Istio 1.17. Please take a few minutes to tell us about your install/upgrade experience! https://forms.gle/hMHGiwZHPU7UQRWe92.3. 卸载
卸载也先给出来
istioctl uninstall --purge
2.4. 列出支持的profile
./istioctl profile list
qiteck@logic:~/program/istio/istio-1.17.2/bin$ ./istioctl profile list
Istio configuration profiles:
ambient
default
demo
empty
external
minimal
openshift
preview
remote不知道干啥的,先不管
2.5. 查看某个profile
./istioctl profile dump demo
qiteck@logic:~/program/istio/istio-1.17.2/bin$ ./istioctl profile dump demo
apiVersion: install.istio.io/v1alpha1
kind: IstioOperator
spec:
components:
base:
enabled: true
cni:
enabled: false
egressGateways:
- enabled: true
k8s:
resources:
requests:
cpu: 10m
memory: 40Mi
name: istio-egressgateway
ingressGateways:
- enabled: true
k8s:
resources:
requests:
cpu: 10m
memory: 40Mi
service:
ports:
- name: status-port
port: 15021
。。。
好长省略了2.6. 查看deployment
sudo kubectl -n istio-system get deploy
qiteck@logic:~/program/istio/istio-1.17.2/bin$ sudo kubectl -n istio-system get deploy
NAME READY UP-TO-DATE AVAILABLE AGE
istio-ingressgateway 1/1 1 1 3m49s
istiod 1/1 1 1 3m58s部署了一个istiod和istio-ingressgateway deployment
2.7. 查看pods
sudo kubectl -n istio-system get pods
qiteck@server:~/program/k8s$ sudo kubectl -n istio-system get pods
NAME READY STATUS RESTARTS AGE
istio-ingressgateway-5555ccdc98-zx5nm 1/1 Running 0 23h
istiod-7fd9d6dd48-nn7sd 1/1 Running 0 23h2.8. 查看service
sudo kubectl -n istio-system get service
qiteck@server:~/program/k8s$ sudo kubectl -n istio-system get service
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
istio-ingressgateway LoadBalancer 10.96.134.112 <pending> 15021:49397/TCP,80:4713/TCP,443:33792/TCP 23h
istiod ClusterIP 10.96.194.4 <none> 15010/TCP,15012/TCP,443/TCP,15014/TCP 23h2.9. 验证是否安装成功
## 生成当前部署的manifest文件
qiteck@logic:~/program/istio/istio-1.17.2/bin$ ./istioctl manifest generate > $HOME/generated-manifest.yaml## 验证是否安装成功
sudo ./istioctl verify-install -f $HOME/generated-manifest.yaml
qiteck@logic:~/program/istio/istio-1.17.2/bin$ sudo ./istioctl verify-install -f $HOME/generated-manifest.yaml
✔ CustomResourceDefinition: authorizationpolicies.security.istio.io.istio-system checked successfully
✔ CustomResourceDefinition: destinationrules.networking.istio.io.istio-system checked successfully
✔ CustomResourceDefinition: envoyfilters.networking.istio.io.istio-system checked successfully
✔ CustomResourceDefinition: gateways.networking.istio.io.istio-system checked successfully
✔ CustomResourceDefinition: istiooperators.install.istio.io.istio-system checked successfully
✔ CustomResourceDefinition: peerauthentications.security.istio.io.istio-system checked successfully
✔ CustomResourceDefinition: proxyconfigs.networking.istio.io.istio-system checked successfully
✔ CustomResourceDefinition: requestauthentications.security.istio.io.istio-system checked successfully
✔ CustomResourceDefinition: serviceentries.networking.istio.io.istio-system checked successfully
✔ CustomResourceDefinition: sidecars.networking.istio.io.istio-system checked successfully
✔ CustomResourceDefinition: telemetries.telemetry.istio.io.istio-system checked successfully
✔ CustomResourceDefinition: virtualservices.networking.istio.io.istio-system checked successfully
✔ CustomResourceDefinition: wasmplugins.extensions.istio.io.istio-system checked successfully
✔ CustomResourceDefinition: workloadentries.networking.istio.io.istio-system checked successfully
✔ CustomResourceDefinition: workloadgroups.networking.istio.io.istio-system checked successfully
✔ ServiceAccount: istio-ingressgateway-service-account.istio-system checked successfully
✔ ServiceAccount: istio-reader-service-account.istio-system checked successfully
✔ ServiceAccount: istiod.istio-system checked successfully
✔ ServiceAccount: istiod-service-account.istio-system checked successfully
✔ ClusterRole: istio-reader-clusterrole-istio-system.istio-system checked successfully
✔ ClusterRole: istio-reader-istio-system.istio-system checked successfully
✔ ClusterRole: istiod-clusterrole-istio-system.istio-system checked successfully
✔ ClusterRole: istiod-gateway-controller-istio-system.istio-system checked successfully
✔ ClusterRole: istiod-istio-system.istio-system checked successfully
✔ClusterRoleBinding: istio-reader-clusterrole-istio-system.istio-system checked successfully
✔ ClusterRoleBinding: istio-reader-istio-system.istio-system checked successfully
✔ ClusterRoleBinding: istiod-clusterrole-istio-system.istio-system checked successfully
✔ ClusterRoleBinding: istiod-gateway-controller-istio-system.istio-system checked successfully
✔ ClusterRoleBinding: istiod-istio-system.istio-system checked successfully
✔ ValidatingWebhookConfiguration: istio-validator-istio-system.istio-system checked successfully
✔ EnvoyFilter: stats-filter-1.13.istio-system checked successfully
✔ EnvoyFilter: stats-filter-1.14.istio-system checked successfully
✔ EnvoyFilter: stats-filter-1.15.istio-system checked successfully
✔ EnvoyFilter: stats-filter-1.16.istio-system checked successfully
✔ EnvoyFilter: stats-filter-1.17.istio-system checked successfully
✔ EnvoyFilter: tcp-stats-filter-1.13.istio-system checked successfully
✔ EnvoyFilter: tcp-stats-filter-1.14.istio-system checked successfully
✔ EnvoyFilter: tcp-stats-filter-1.15.istio-system checked successfully
✔ EnvoyFilter: tcp-stats-filter-1.16.istio-system checked successfully
✔ EnvoyFilter: tcp-stats-filter-1.17.istio-system checked successfully
✔ ConfigMap: istio.istio-system checked successfully
✔ ConfigMap: istio-sidecar-injector.istio-system checked successfully
✔ MutatingWebhookConfiguration: istio-sidecar-injector.istio-system checked successfully
✔ Deployment: istio-ingressgateway.istio-system checked successfully
✔ Deployment: istiod.istio-system checked successfully
✔ PodDisruptionBudget: istio-ingressgateway.istio-system checked successfully
✔ PodDisruptionBudget: istiod.istio-system checked successfully
✔ Role: istio-ingressgateway-sds.istio-system checked successfully
✔ Role: istiod.istio-system checked successfully
✔ Role: istiod-istio-system.istio-system checked successfully
✔ RoleBinding: istio-ingressgateway-sds.istio-system checked successfully
✔ RoleBinding: istiod.istio-system checked successfully
✔ RoleBinding: istiod-istio-system.istio-system checked successfully
✔ HorizontalPodAutoscaler: istio-ingressgateway.istio-system checked successfully
✔ HorizontalPodAutoscaler: istiod.istio-system checked successfully
✔ Service: istio-ingressgateway.istio-system checked successfully
✔ Service: istiod.istio-system checked successfully
Checked 15 custom resource definitions
Checked 2 Istio Deployments
✔Istio is installed and verified successfully打勾就是安装完成了
2.10. 遇到问题
- Ingress gateways encountered an error: failed to wait for resource: resources not ready after 5m0s: timed out waiting for the condition
内存不足导致的:
istioctl install有一个最低内存要求,这是没有文档记录的,也是需要的。超时错误消息具有误导性。它应该显示内存不足。
安装在一个有5G内存的机器就可以了 :
- 搭建成功以后,k8s正常的deployment无法部署了
k8s controller报错: maximum cpu usage per Container is 900m, but limit is 2, maximum memory usage per Container is 1000Mi, but limit is 1Gi
先把limitrange删除再说。
3.注入 Sidecar
3.1.自动注入-注入namespace
还有自定义注入的方式,没有尝试
sudo kubectl label namespace default istio-injection=enabled
qiteck@logic:~/program/istio/istio-1.17.2/samples$ sudo kubectl label namespace default istio-injection=enabled
namespace/default labeled3.2.查看namespace注入情况
sudo kubectl get namespace -L istio-injection
qiteck@server:~/program/k8s$ sudo kubectl get namespace -L istio-injection
NAME STATUS AGE ISTIO-INJECTION
default Active 279d enabled
ingress-nginx Active 23d
istio-system Active 21h
kafka Active 42d
kube-node-lease Active 279d
kube-public Active 279d
kube-system Active 279d
rabbitmq Active 23h
zookeeper Active 43d可以看到只有default这个namespace注入了istio
注入以后,需要重启deployment才能看到注入容器
3.3.注入以后deployment的情况
注入以后,我把gamedeployment重启了:sudo kubectl rollout restart deployment game
然后可以看到game是2个容器了,其他是一个容器
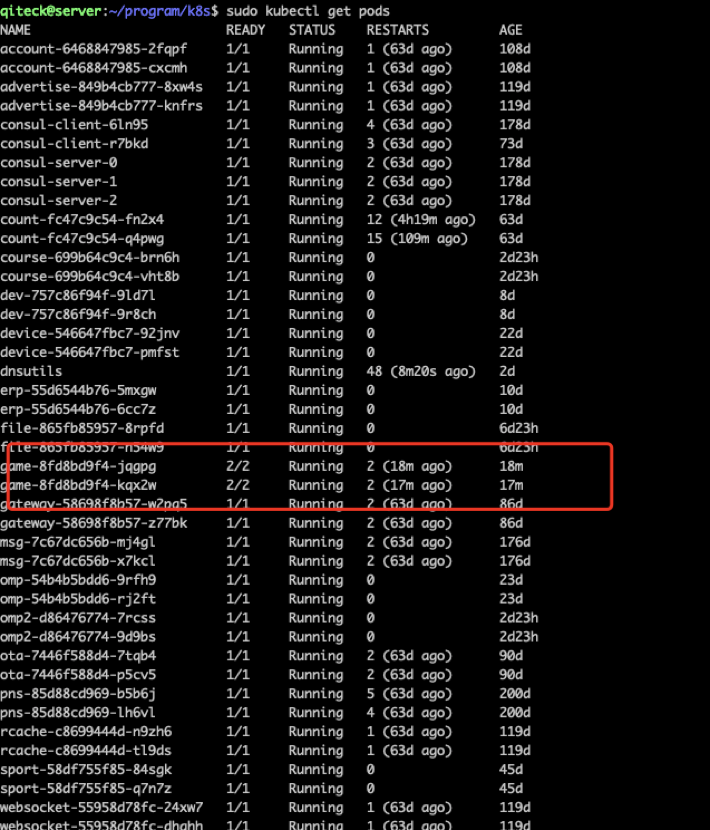
默认服务部署的时候是一个容器,game加了istio注入容器
3.4.注入以后pod的描述
Sudo kubectl describe pod game-8fd8bd9f4-jqpgg
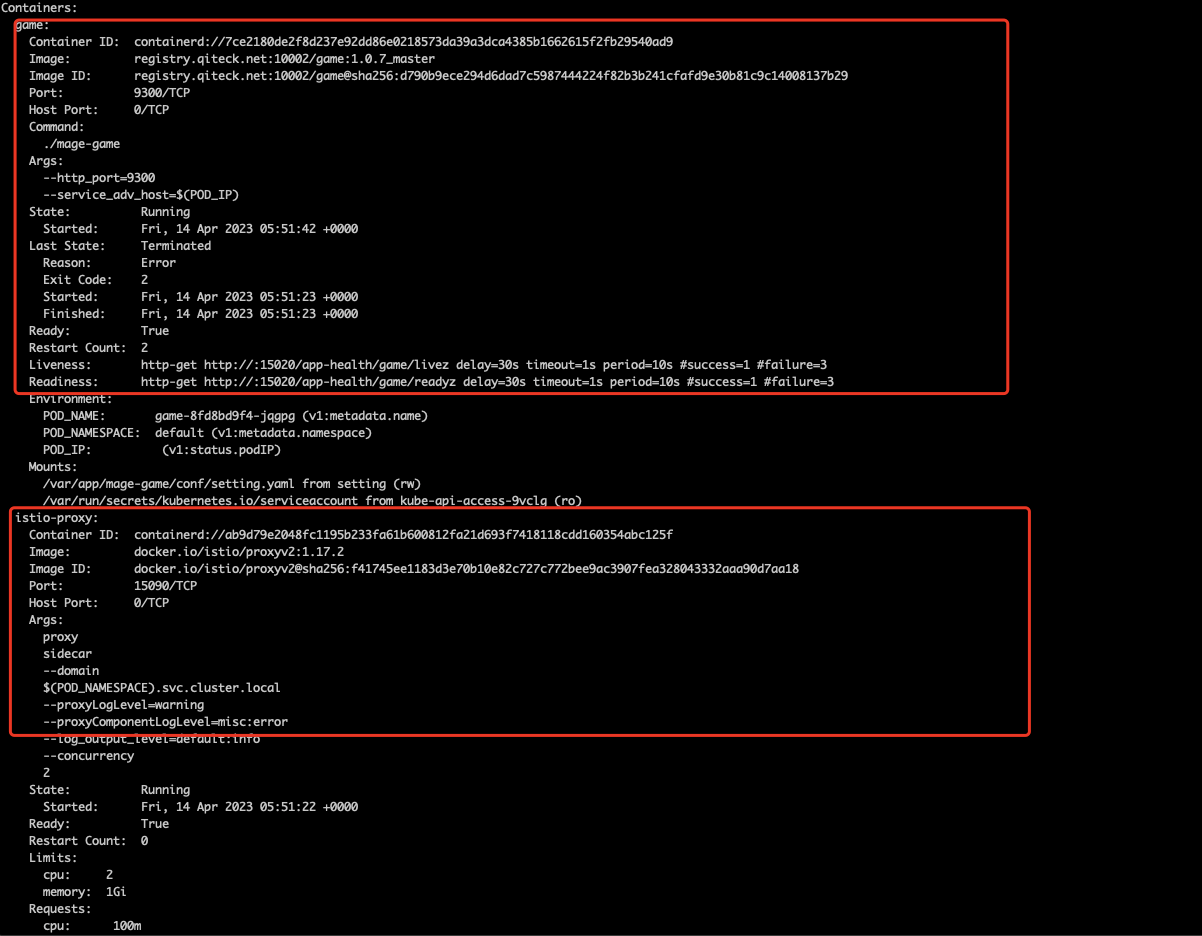
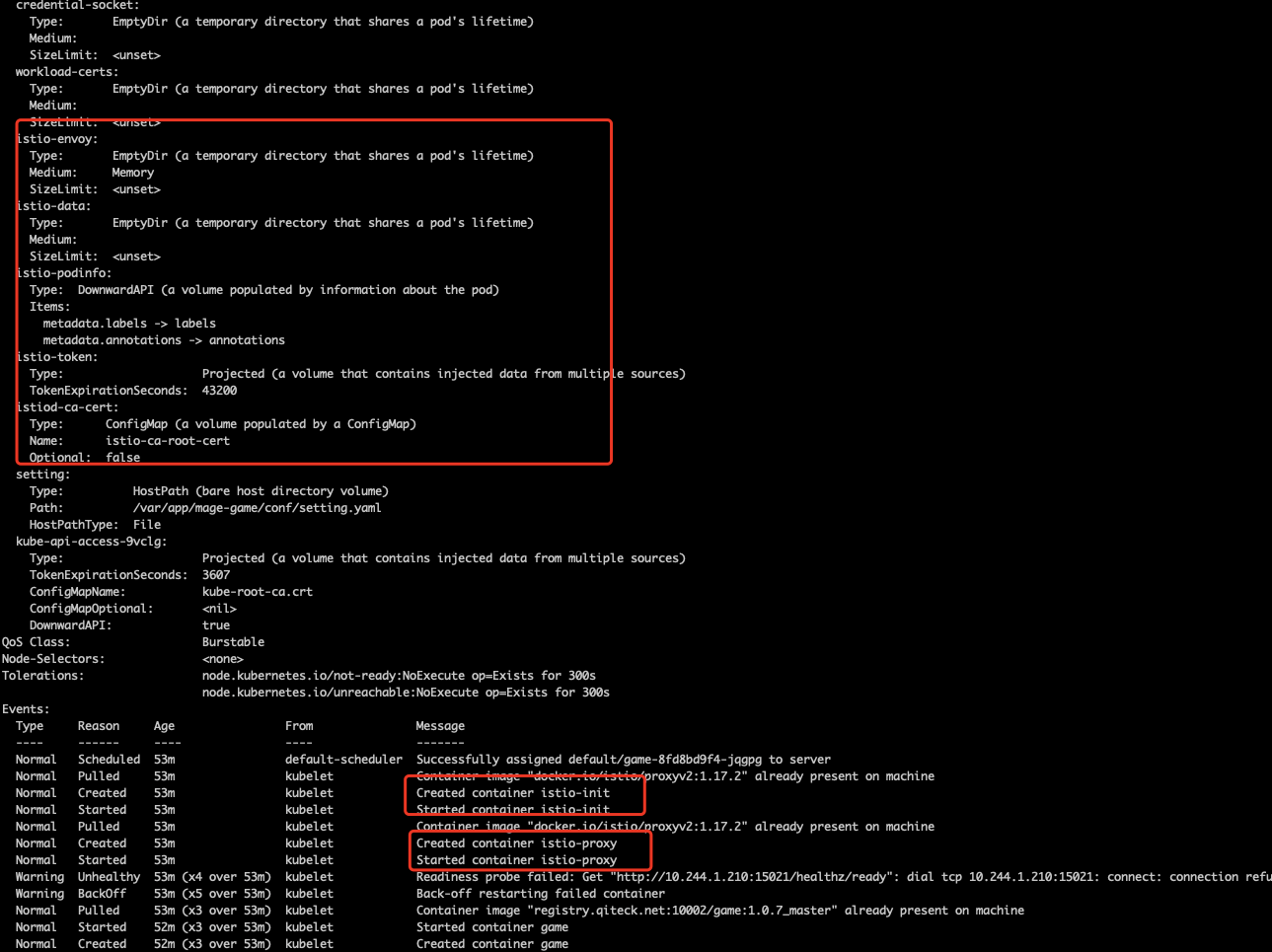
可以看到:
有两个containers:
- Game:原来的容器
- Istio-proxy: 注入的容器
很多其他istio的信息,这样就注入成功了。
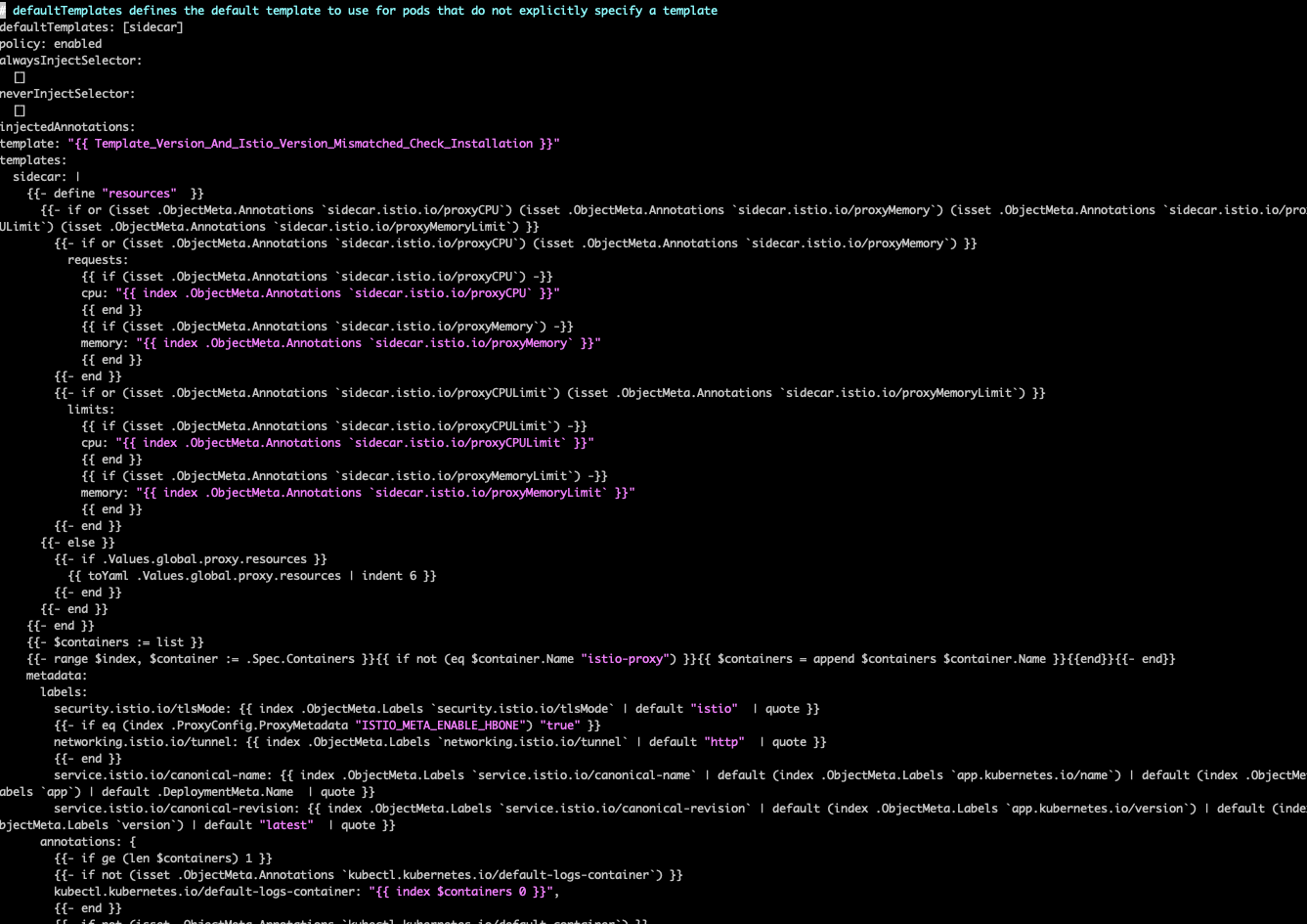
3.5.查看 istio-sidecar-injector Configmap 的配置
kubectl -n istio-system get configmap istio-sidecar-injector -o=jsonpath=‘{.data.config}'