golang CVE-2016-2183漏洞,https需要添加tls设置加密算法白名单,将弱加密算法DES和3DES去掉。
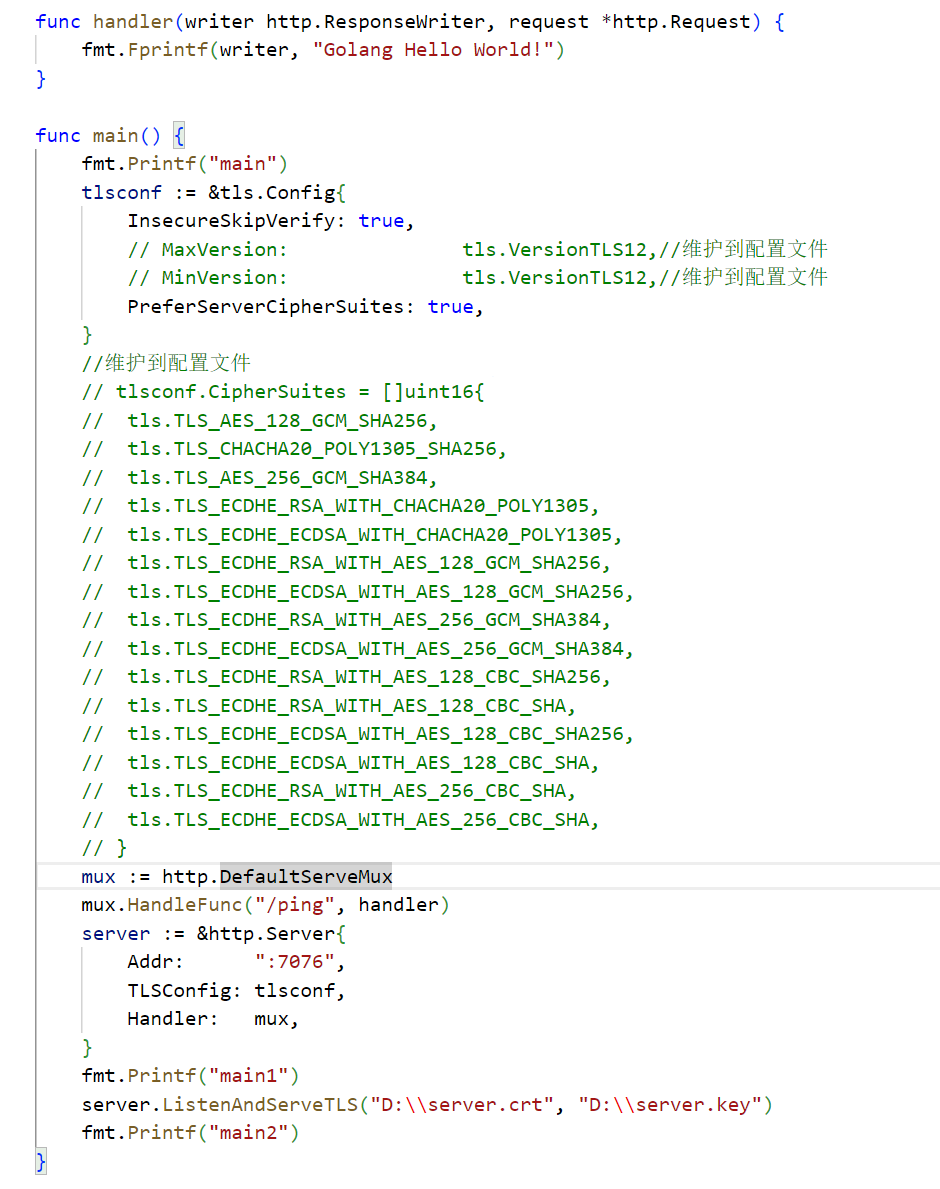
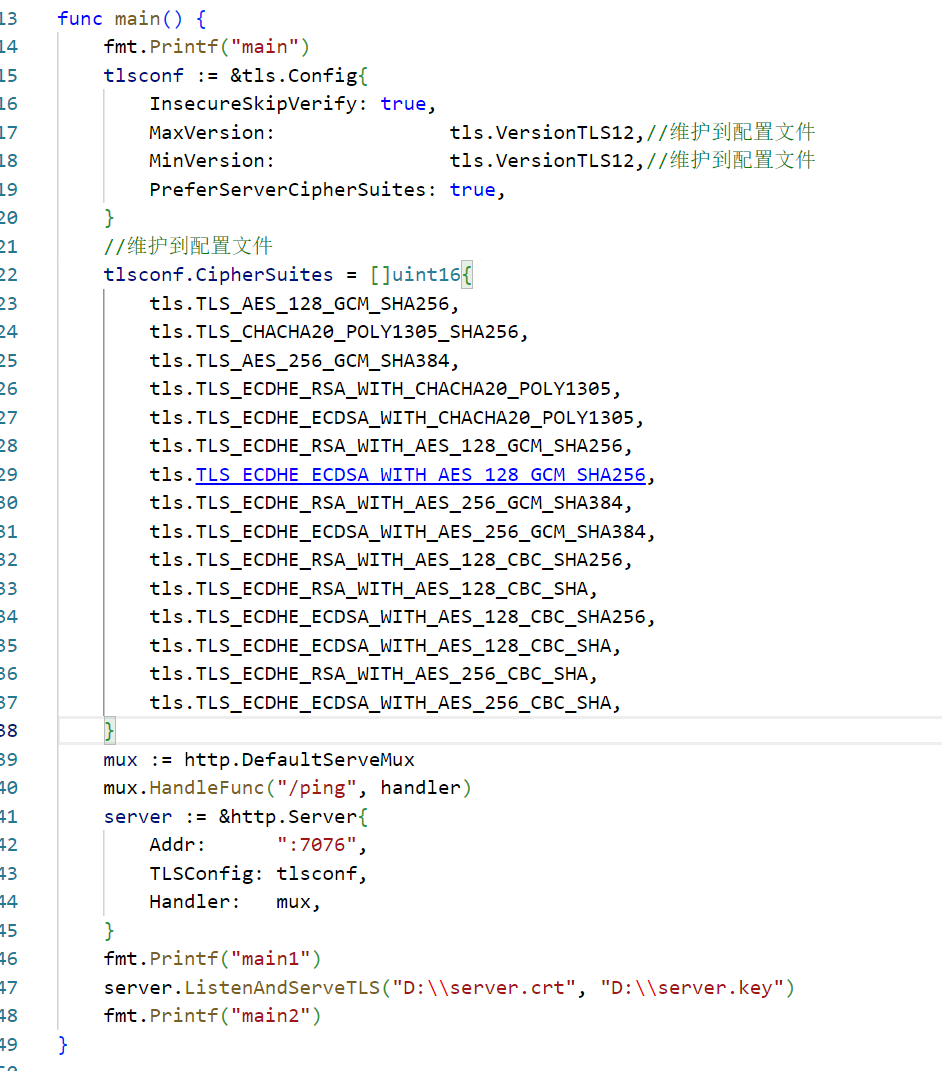
服务端样例代码
package main import ( "crypto/tls" "fmt" "net/http" ) func handler(writer http.ResponseWriter, request *http.Request) { fmt.Fprintf(writer, "Golang Hello World!") } func main() { fmt.Printf("main") tlsconf := &tls.Config{ InsecureSkipVerify: true, MaxVersion: tls.VersionTLS12,//维护到配置文件 MinVersion: tls.VersionTLS12,//维护到配置文件 PreferServerCipherSuites: true, } //维护到配置文件 tlsconf.CipherSuites = []uint16{ tls.TLS_AES_128_GCM_SHA256, tls.TLS_CHACHA20_POLY1305_SHA256, tls.TLS_AES_256_GCM_SHA384, tls.TLS_ECDHE_RSA_WITH_CHACHA20_POLY1305, tls.TLS_ECDHE_ECDSA_WITH_CHACHA20_POLY1305, tls.TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256, tls.TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256, tls.TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384, tls.TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384, tls.TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256, tls.TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA, tls.TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256, tls.TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA, tls.TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA, tls.TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA, } mux := http.DefaultServeMux mux.HandleFunc("/ping", handler) server := &http.Server{ Addr: ":7076", TLSConfig: tlsconf, Handler: mux, } fmt.Printf("main1") server.ListenAndServeTLS("D:\\server.crt", "D:\\server.key") fmt.Printf("main2") }
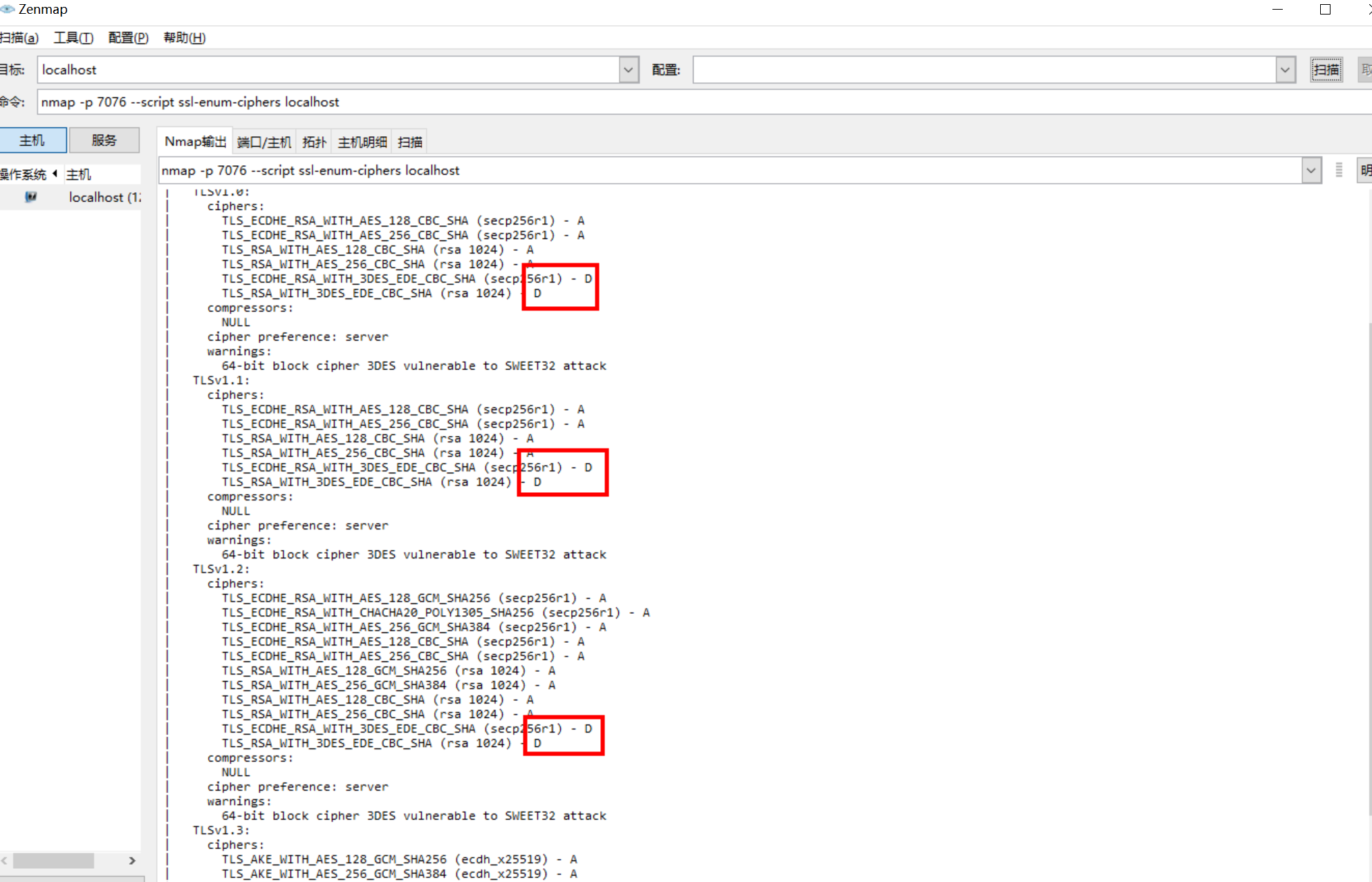
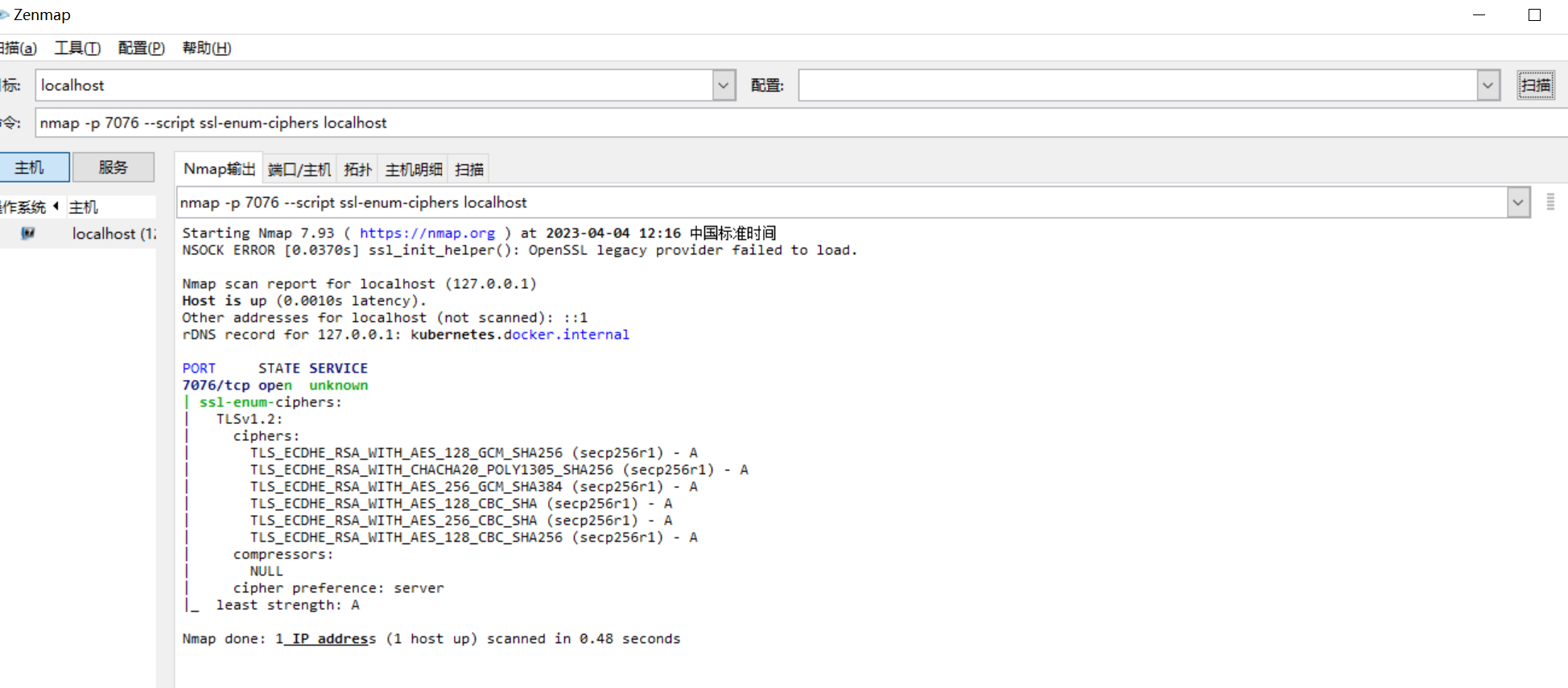
测试方法
当注释掉Cipher部分时验证效果,可以看到很多D级别的加密算法(扫描命令 nmap -sV -p 7076 --script ssl-enum-ciphers)
将CipherSuites配置生效后,看到已经扫描不到D级别的密码算法
参考网址
TLS完全指南(三):用Go语言写HTTPS程序 - 知乎 (zhihu.com)
(36条消息) 在 Windows 上安装 NMAP_nmap windows_allway2的博客-CSDN博客
HTTPS原理以及GOLANG指定HTTPS密码套件 - lvlooo - SegmentFault 思否